NC1803
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
NETWORKcomputing<br />
I N F O R M A T I O N A N D C O M M U N I C A T I O N S – N E T W O R K E D www.networkcomputing.co.uk<br />
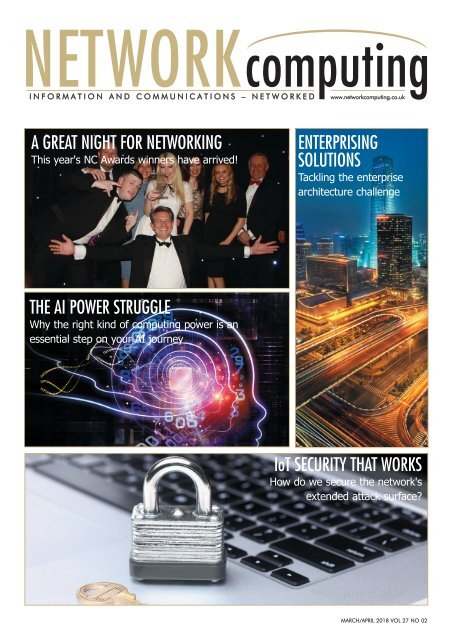
A GREAT NIGHT FOR NETWORKING<br />
This year's NC Awards winners have arrived!<br />
ENTERPRISING<br />
SOLUTIONS<br />
Tackling the enterprise<br />
architecture challenge<br />
THE AI POWER STRUGGLE<br />
Why the right kind of computing power is an<br />
essential step on your AI journey<br />
IoT SECURITY THAT WORKS<br />
How do we secure the network's<br />
extended attack surface?<br />
MARCH/APRIL 2018 VOL 27 NO 02
helping our customers do great things<br />
we help our customers do great things<br />
IPEXPO<br />
manchester<br />
25-26 April 2018,<br />
Manchester Central<br />
REGISTER FREE<br />
• 95+ World-class speakers<br />
• 100+ Industry leading vendors<br />
• 9 Theatres<br />
• Live Demos<br />
• Everything you need<br />
under ONE roof<br />
CLOUD & IOT<br />
CYBER SECURITY<br />
MANCHESTER<br />
NETWORKS &<br />
INFRASTRUCTURE<br />
DATA & ANALYTICS DEVOPS AI<br />
www.ipexpomanchester.com<br />
SPONSORED BY<br />
helping you do great things
COMMENT<br />
COMMENT<br />
THE BEST NETWORK POSSIBLE<br />
BY RAY SMYTH, EDITOR<br />
We live in an uncertain world: of that there can be no doubt. We are advised<br />
that the current skills shortage in IT and cybersecurity will get worse before it<br />
gets better, and yet I have noted that one response to the shortage is to<br />
increase salaries for some IT staff from that same, limited pool. While this will be welcomed<br />
by the beneficiaries, it's well known that the positive effect of a salary increase<br />
will be short-lived, and it is actually unlikely to prevent employees accepting a role<br />
with an even better salary offered by a competitor. But does any of this contribute to a<br />
better, more operationally aligned, secure networked estate?<br />
I have never held back in encouraging those working in IT and networking to get<br />
more involved in their organisation: involved so that they can spend more time and<br />
resources doing what the organisation really needs and dissuading it from embarking<br />
on a path of networked anarchy, where functional line managers do what they want,<br />
when they want, and connect it to the network - all too often with board approval,<br />
even if tacit.<br />
The essentials of a well-functioning, business-aligned, realistically secure network will<br />
never change. These values should always be paramount and enable the organisation's<br />
objectives, reviewed regularly and refined and adjusted, in order to at least be in<br />
step with organisational changes, and ideally to lead them. When combined with<br />
competent scrutiny and a shared and evolving understanding, the digitally transformed,<br />
digitally driven organisation will naturally attract and retain the best people. It<br />
might even help to create some.<br />
EDITOR: Ray Smyth<br />
(ray.smyth@btc.co.uk)<br />
REVIEWS:<br />
Dave Mitchell<br />
Ray Smyth<br />
SUB EDITOR: Mark Lyward<br />
(netcomputing@btc.co.uk)<br />
PRODUCTION: Abby Penn<br />
(abby.penn@btc.co.uk)<br />
DESIGN: Ian Collis<br />
(ian.collis@btc.co.uk<br />
SALES:<br />
David Bonner<br />
(david.bonner@btc.co.uk)<br />
SUBSCRIPTIONS: Christina Willis<br />
(christina.willis@btc.co.uk)<br />
PUBLISHER: John Jageurs<br />
(john.jageurs@btc.co.uk)<br />
Published by Barrow & Thompkins<br />
Connexion Ltd (BTC)<br />
35 Station Square,<br />
Petts Wood, Kent, BR5 1LZ<br />
Tel: +44 (0)1689 616 000<br />
Fax: +44 (0)1689 82 66 22<br />
SUBSCRIPTIONS:<br />
UK £35/year, £60/two years,<br />
£80/three years;<br />
Europe:<br />
£48/year, £85/two years £127/three years;<br />
ROW:<br />
£62/year, £115/two years, £168/three years;<br />
Subscribers get SPECIAL OFFERS — see subscriptions<br />
advertisement; Single copies of<br />
Network Computing can be bought for £8;<br />
(including postage & packing).<br />
© 2018 Barrow & Thompkins<br />
Connexion Ltd.<br />
All rights reserved.<br />
No part of the magazine may be<br />
reproduced without prior consent, in<br />
writing, from the publisher.<br />
So if you have got this far then why not send this to your CEO, to whom I say: if your<br />
organisation is digitally driven (and that should be all of you) then you must think hard<br />
about how you will truly integrate your IT operations with the organisation you seek to<br />
create. Yes, you will have to pay those you recruit the going rate at the very least, but<br />
this alone will be sufficient to satisfy the emerging breed of organisationally integrated<br />
IT and networking professionals. They should probably want your job and may ultimately<br />
be best suited. It's over to you...<br />
Ray Smyth - Editor, Network Computing.<br />
Ray.Smyth@BTC.CO.UK | https://twitter.com/ItsRay?<br />
GET FUTURE COPIES FREE<br />
BY REGISTERING ONLINE AT<br />
WWW.NETWORKCOMPUTING.CO.UK/REGISTER<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 3
CONTENTS<br />
CONTENTS<br />
M A R C H / A P R I L 2 0 1 8<br />
AI AND YOUR NETWORK.....10<br />
We continue our artificial intelligence focus this<br />
issue with insights on how to begin your AI<br />
journey and the computing power and<br />
capacity required to do so. We also look at<br />
how AI can augment network security, and<br />
consider the next decade of AI development<br />
EDITOR’S COMMENT......................3<br />
The best network possible<br />
COMPANY NEWS............................6<br />
Market Dynamics: making sense of the market<br />
NETWORK NEWS............................7<br />
Moves, adds and changes<br />
VERSION X......................................8<br />
The latest networking news<br />
ARTICLES<br />
THE AI SANITY CHECK..................10<br />
By Professor Peter Cochrane at the University<br />
of Suffolk<br />
THE REINFORCING BENEFITS OF AI..11<br />
By Derek Lin at Exabeam<br />
INTELLIGENCE THAT IS ARTIFICIAL..12<br />
By Ken Gilmour at invinsec<br />
ENTERPRISE ARCHITECTURE...20<br />
Is improvement a bigger goal than<br />
alignment in the enterprise? Terry Blevins at<br />
The Open Group and owner of Enterprise<br />
Wise LLC considers the enterprise<br />
architecture challenge<br />
WHEN STORAGE<br />
BECOMES DATA..................26<br />
Do we need to consider storage media or<br />
should we consider data holistically? Mark<br />
Peters and Scott Sinclair at the Enterprise<br />
Strategy Group share their views<br />
IoT SECURITY THAT WORKS...22<br />
IoT devices extend the attack surface of<br />
networks, but what can be done to combat<br />
this, and how should the risk be<br />
understood? Professor William Webb at<br />
Weightless SIG explains<br />
NETWORK COMPUTING<br />
AWARDS 2018.....................28<br />
The Radisson Blu Edwardian in London was<br />
the venue for this year's Network Computing<br />
Awards. Discover more about the 2018<br />
winners in our special round-up feature<br />
THE AI POWER STRUGGLE.............13<br />
By David Hogan at NVIDIA<br />
PACKET MINING: THE GIFT THAT<br />
KEEPS ON GIVING.......................17<br />
By Cary Wright at Endace<br />
TRUST THAT KNOWS<br />
NO BOUNDS................................18<br />
By Barry Scott at Centrify<br />
NETWORKED AUDIO....................19<br />
By John Ellis at Shure<br />
CONTAINING EXPECTATIONS.......21<br />
By Marco Ceppi at Canonical<br />
SMART CONNECTIVITY<br />
BY DESIGN...................................25<br />
By Oli Barrington at R&M<br />
TRANSPARENT I.T..........................27<br />
By James Cockroft at Coeus Consulting<br />
SHOW PREVIEWS<br />
IP EXPO MANCHESTER.................15<br />
25th-26th April at Manchester Central<br />
UC EXPO LONDON....................16<br />
16th-17th May at ExCel London<br />
PRODUCT REVIEWS<br />
ALTARO VM BACKUP - UNLIMITED<br />
PLUS EDITION...............................14<br />
NETSCOUT AIRCHECK G2...........23<br />
4 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
The first dedicated<br />
Recruitment EXPO<br />
for cyber security<br />
professionals<br />
Thursday 5th April 2018<br />
UWE Conference Centre, Bristol<br />
www.CyberSecurityExpo.co.uk<br />
The Bristol Expo<br />
is FREE to attend<br />
Come and meet the<br />
companies hiring within<br />
Cyber Security.<br />
Find out about<br />
the latest hot jobs<br />
100s of job vacancies<br />
available on the day.<br />
Free entry into<br />
the Security<br />
Cleared EXPO<br />
Industry Partners:
COMPANYNEWS<br />
MARKET DYNAMICS: MAKING SENSE OF THE MARKET<br />
IN A REGULAR LOOK AT RESULTS AND KEY BUSINESS ANNOUNCEMENTS FOR SUPPLIERS INTO THE<br />
NETWORKING AND IT MARKET, NETWORK COMPUTING SUMMARISES THE EDITORS SELECTIONS<br />
It's not just technology that has to<br />
evolve and change: organisations too<br />
must make sure they remain relevant<br />
and in tune with their market. Having<br />
launched the Riverbed Digital<br />
Performance Platform, Riverbed<br />
Technology has also unveiled a new<br />
brand identity, which they say is to<br />
accelerate their strategy to deliver<br />
industry-leading solutions to maximise<br />
digital performance and fuel new growth<br />
opportunities in a $30 billion plus market.<br />
Subbu Iyer, SVP and Chief Marketing<br />
Officer at Riverbed explains, "Digital<br />
business is now mainstream and digital<br />
performance defines business success.<br />
Riverbed has also evolved significantly in<br />
the last few years, with entirely new<br />
offerings that have enabled us to deliver a<br />
modern IT architecture for today's digital<br />
enterprise. The result of these efforts is the<br />
new Riverbed Digital Performance<br />
Platform, which helps maximise<br />
performance across every aspect of a<br />
customer's business, allowing<br />
organisations to fundamentally rethink."<br />
According to IDC, at least 50 per cent of<br />
global GDP will be digitised by 2021,<br />
with growth driven by digitally-enhanced<br />
offerings, operations and relationships.<br />
They expect digital transformation<br />
spending to reach $2.1 trillion in 2021.<br />
Cybersecurity company Webroot has<br />
announced double-digit year-on-year<br />
annual recurring revenue growth for the<br />
second quarter of fiscal 2018. This marks<br />
the sixteenth consecutive quarter of<br />
double-digit, year-on-year revenue<br />
growth. Their business segment grew by<br />
31 per cent, more than 5 times the 6 per<br />
cent growth analyst firm Radicati tracks as<br />
the annual growth rate for business<br />
endpoint security solutions worldwide.<br />
In the consumer segment, Webroot grew<br />
by 4 per cent year-on-year, which<br />
according to Webroot's calculations is 2.6<br />
times the pace of worldwide security<br />
spending in the consumer security<br />
software segment.<br />
Mike Potts, CEO of Webroot said, "[This]<br />
highlights the demand for our solutions as<br />
businesses and consumers face an<br />
increasingly complex landscape of<br />
cybersecurity threats. Our momentum<br />
further validates that Webroot has the<br />
most sophisticated threat intelligence<br />
engine in the industry, integrated with<br />
leading technology partners."<br />
As part of their ongoing strategy to<br />
expand across Canada, eStruxture Data<br />
Centers has acquired Kolotek from Gaz<br />
Métro Plus. This will allow both eStruxture's<br />
and Kolotek's existing customers to take<br />
advantage of multiple physical locations in<br />
the greater Montreal region, improving<br />
multi-site and disaster recovery options<br />
while adding to eStruxture's collective pool<br />
of network providers.<br />
The latest Tech Barometer from Moore<br />
Stephens, the accounting and advisory<br />
firm, has revealed that the average<br />
enterprise value of technology companies<br />
on the Alternative Investment Market<br />
(AIM) has reached £111m. This is a 24.9<br />
per cent increase from 30 June 2017 and<br />
a 50 per cent increase for the full year.<br />
The continued growth in value of these<br />
stocks has resulted in a resurgence of tech<br />
IPOs with seven in the second half of<br />
2017, raising £114m in total. This is a<br />
stark increase to just the one to take place<br />
in the previous half-year.<br />
Dougie Hunter, Director at Moore<br />
Stephens said, "Six months ago we<br />
predicted an increase in IPO activity and<br />
this has certainly been the case. In total,<br />
more than £1.2bn was raised by<br />
technology companies on AIM throughout<br />
2017 - it really is a booming market."<br />
UK headquartered Software Services<br />
Company Clearvision has reported<br />
another year of record growth. Turnover<br />
rose to more than £22m at the end of<br />
2017, from £17.3m, representing a 27<br />
per cent year-on-year increase. Founder<br />
and CEO Gerry Tombs attributes the<br />
phenomenal growth to the continued trend<br />
for digital transformation across all<br />
business types and size, as well as their<br />
innovations and expansion into new areas,<br />
in particular its capability to take teams<br />
and technology to the cloud. The<br />
independently owned business operates<br />
across five locations, with headquarters in<br />
Southampton and employs 90 people. NC<br />
Disclaimer - all information published in this article is based upon fuller submissions provided under general release. Any interested party is urged to verify<br />
any information printed here, prior to using it in any way. Neither Network Computing nor it publishers accepts any responsibility for the accuracy of the<br />
information contained in this article.<br />
6 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
NETWORKNEWS<br />
NETWORK NEWS - MOVES, ADDS AND CHANGES<br />
A REGULAR LOOK AT THE STORIES INVOLVING PEOPLE, COMPANIES AND SOLUTIONS<br />
The threat posed by networked IoT<br />
devices is significant, especially at<br />
this early developmental stage.<br />
Gartner, using survey data from recently<br />
acquired CEB, says that nearly 20 per<br />
cent of organisations observed at least<br />
one IoT-based attack in the past three<br />
years. Much will have to change if this<br />
attack surface is to be defended. To protect<br />
against these threats Gartner forecasts<br />
that worldwide spending on IoT<br />
security will reach $1.5 billion in 2018,<br />
a 28 per cent increase from 2017.<br />
Commenting, Ruggero Contu,<br />
Research Director at Gartner explains<br />
that "Organisations often don't have<br />
control over the source and nature of<br />
the software and hardware being<br />
utilised by smart connected devices. We<br />
expect to see demand for tools and<br />
services aimed at improving discovery<br />
and asset management, software and<br />
hardware security assessment, and penetration<br />
testing. In addition, organisations<br />
will look to increase their understanding<br />
of the implications of externalising<br />
network connectivity."<br />
With the number of IoT devices set to<br />
quadruple by 2024, has anyone considered<br />
the impact that these devices will<br />
have on the network operators? The<br />
huge number of devices and subscribers<br />
accessing the network will have consequences<br />
for operators, says Robin Kent,<br />
Director of European Operations at<br />
Adax. He explains that operators will<br />
need to prioritise traffic, asking "Can<br />
you imagine if the smart grid were to<br />
stop working to prioritise advertising?"<br />
As if to underline the future risk, Robin<br />
explains that, "If you think back 20+<br />
years, this can be likened to the advent<br />
of SMS, whose volume of messages<br />
caused problems for the voice network.<br />
The solution, to offload SMS messages<br />
and reroute them to give the priority to<br />
voice, highlighted a problem that wasn't<br />
anticipated."<br />
A 'wait and see' policy may have its<br />
merits, but not when it comes to digital<br />
transformation - and this is especially<br />
true in the retail sector. Mark Baker,<br />
Field Product Manager at Canonical<br />
says that, "In the digital age, technology<br />
is the differentiator, and ignoring the<br />
importance of innovation is akin to<br />
accepting failure. Those businesses<br />
which do so won't be around in five<br />
years' time."<br />
Continually evolving retail will be<br />
essential in order to compete in a world<br />
where traditional web shop solutions,<br />
which rely on templates, will no longer<br />
offer enough flexibility to consumers<br />
used to shopping with multiple devices.<br />
"The older systems are also difficult or<br />
impossible to adapt for the omni channel<br />
sales and logistics - these are musthaves<br />
for long term sales success and<br />
customer loyalty," says Baker, who concludes,<br />
"In the digital age, technology is<br />
the differentiator and ignoring the<br />
importance of innovation is akin to<br />
accepting failure."<br />
When faced with pressure on all sides,<br />
it is easy for network and IT staff to<br />
become unfamiliar with their network<br />
estate and in turn the nature of the<br />
security breaches taking place, including<br />
acknowledgment that a security<br />
breach could quite feasibly go unnoticed.<br />
This is reinforced from a recent<br />
survey by Balabit: The Unknown<br />
Network Survey.<br />
From the survey, 83 per cent of businesses<br />
agreed that technology can be<br />
effective in preventing breaches, but 73<br />
per cent believed that technology struggles<br />
to keep up with security threats.<br />
Csaba Krasznay, Security Evangelist at<br />
Balabit says, "Security is no longer<br />
about simply keeping the bad guys<br />
out... What's really alarming is that the<br />
majority of businesses know very little<br />
about the nature of the security breaches<br />
that are happening to them. Many<br />
even admit that a security breach could<br />
quite feasibly go unnoticed. That's how<br />
loose a grip we've got on them, or how<br />
little we really understand them. We<br />
know about breaches, sure - but we<br />
really don't know enough." NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 7
PRODUCTNEWS<br />
VERSION X<br />
VERSION X<br />
VERSION X<br />
VERSION X<br />
VER<br />
WITH PRODUCT ANNOUNCEMENTS RANGING FROM THE TRIVIAL TO THE BIZARRE, THE EDITOR<br />
DISTILS THE ESSENCE OF THOSE THAT ARE OF INTEREST TO THE NETWORKING COMMUNITY<br />
Full management visibility of the IT<br />
estate is progressively getting harder,<br />
and the benefits on offer from the use<br />
of virtual infrastructure increase this challenge.<br />
It is with this in mind that<br />
SolarWinds has added new functionality<br />
with a pair of product updates that offer<br />
broader and deeper performance monitoring<br />
capabilities across physical and virtual<br />
infrastructures, particularly in hybrid environments.<br />
The newest version of<br />
SolarWinds Storage Resource Monitor<br />
extends support to a wider range of leading<br />
all-flash arrays, while the latest update to<br />
Server & Application Monitor permits deeper<br />
visibility into interactions between a set<br />
of servers running business applications.<br />
Christoph Pfister, Executive Vice President<br />
of Products at SolarWinds said, "Finding<br />
clarity through the haze of complexity is<br />
vital to successfully keep today's heterogeneous<br />
and distributed IT environments running<br />
smoothly. With support for more leading-edge<br />
storage vendor solutions and<br />
deeper visibility into the connection<br />
between critical infrastructure resources, our<br />
system management updates give IT professionals<br />
more powerful tools to overcome<br />
complexity and optimise performance."<br />
Continuing the theme of growing complexity,<br />
fast effective testing of network<br />
operation is essential to keeping users<br />
working, and it seems there is a trend<br />
among tester providers to do this. The latest,<br />
from IDEAL software, is based on some<br />
free software updates for the SignalTEK NT<br />
network transmission tester, SignalTEK CT<br />
cable transmission tester and the NaviTEK<br />
NT Plus and Pro network trouble shooters.<br />
For significant enhancements, such as<br />
improved wire map and port discovery<br />
information, users can download the free<br />
updates from their website.<br />
There is a lot said about security and as<br />
each breach or compromise is disclosed,<br />
the task seems to get increasingly tougher.<br />
In the midst of this uncertainty there is however<br />
some comfort and hope offered in the<br />
form of encryption, which continues to be a<br />
significant tool for those wanting to protect<br />
their data. Interconnection and data centre<br />
company Equinix has launched its<br />
SmartKey. This global key management<br />
and encryption Software as a Service aims<br />
to simplify data protection across any cloud<br />
or destination. The service leverages their<br />
globally interconnected platform of more<br />
than 190 international Business Exchange<br />
data centres in 48 markets, to securely host<br />
encryption keys separate from, but in close<br />
proximity to, the data located across networks<br />
and hybrid multi-cloud environments.<br />
Commenting, Christina Richmond,<br />
Program Vice President, Worldwide Security<br />
Services, at IDC said, "Digital transformation<br />
efforts by enterprises and service<br />
providers are moving more data and systems<br />
to the cloud, pushing an ever-increasing<br />
amount of sensitive enterprise and customer<br />
data to be stored in multi-tenant,<br />
shared computing and storage environments.<br />
This trend is being driven by data<br />
sovereignty requirements like GDPR, creating<br />
demand for secure data localisation<br />
solutions like key management-as-a-service<br />
offerings, including Equinix SmartKey."<br />
Innovations such as 5g and IoT are<br />
responsible for increasing the complexity of<br />
the networks that they rely on to function.<br />
In response to this, Juniper Networks has<br />
been sharing its vision for simplifying service<br />
delivery in complex metro networks.<br />
Metro Fabric is designed to provide an<br />
adaptive, agile and secure network infrastructure<br />
for simplified service creation and<br />
delivery in the metro. The variety of services<br />
and the number of connected devices supported<br />
across metro networks - the layer of<br />
a service provider's infrastructure most<br />
commonly associated with connecting subscribers<br />
to the internet - has recently<br />
expanded exponentially.<br />
Ethernet business services, popular applications<br />
like Netflix and Skype, IaaS offerings<br />
like Amazon Web Services and a<br />
throng of IoT devices have proliferated,<br />
and this will only continue with emerging<br />
5G rollouts. The result is a complex web of<br />
legacy products, manual processes and<br />
divergent architectures and protocols that<br />
have hindered true innovation and rendered<br />
it difficult for service providers to<br />
keep up with bandwidth demands and cost<br />
constraints, explains Juniper.<br />
Juniper's Metro Fabric, they claim, comprises<br />
the industry's only disaggregated<br />
programmable photonic layer. Service<br />
providers building metro services for<br />
mobile, business, cable, fibre residential<br />
and direct public cloud use cases can now<br />
8 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
PRODUCTNEWS<br />
SION X<br />
leverage a modern service creation platform<br />
to quickly and efficiently deliver new<br />
revenue-generating services. Juniper says it<br />
is now introducing the initial building<br />
blocks of the refreshed metro: two new<br />
ACX Series Routers, as well as a new PTX<br />
Series Packet Transport Router. The company<br />
also intends to continue executing<br />
against its plan to deliver a Self-Driving<br />
Network across its networking portfolio,<br />
including the new Metro Fabric.<br />
Sally Bament, VP at Juniper Networks said,<br />
"In our commitment to engineer simplicity<br />
into all layers of the network, we are excited<br />
to deliver these new capabilities focused on<br />
transforming how service providers modernise<br />
service delivery in the metro. By combining<br />
adaptive and predictive software with<br />
new and existing network infrastructure<br />
offerings, we are evolving our solutions to<br />
enable service providers to deploy a metro<br />
network capable of faster service creation<br />
and time-to-revenue for a new generation<br />
of services and applications, including<br />
emerging 5G and IoT services."<br />
As if to prove that networking technology<br />
and deployment continues to progress and<br />
evolve, Cisco has announced an extension<br />
to its intent-based networking vision, bringing<br />
greater visibility to what they consider to<br />
be the biggest blind spot for IT: the widearea<br />
network (WAN). Made up of disparate<br />
networks outside of the control of IT, the<br />
WAN connects employees to applications,<br />
no matter where those employees might be.<br />
Its fragmented nature means that IT often<br />
has limited ability to specifically determine<br />
problems and get real-time information.<br />
Now, Cisco is helping by providing the<br />
capability to forecast WAN problems before<br />
they happen, while quickly isolating and fixing<br />
issues when they do occur. The rise of<br />
multi-cloud IT environments has exacerbated<br />
the traditional complexity of the WAN and<br />
magnified its challenges. IDC's 2017<br />
Worldwide SD-WAN Survey discovered that<br />
almost 3 out of 10 organisations considered<br />
network outages to be a top WAN concern,<br />
with the same number stating that they need<br />
better visibility and analytics to manage<br />
application and WAN performance.<br />
Building on their recent push toward<br />
intent-based networking, Cisco says it is<br />
driving this network revolution to the WAN<br />
and introducing innovations to provide IT<br />
with the vital visibility and insight into the<br />
WAN that will help keep businesses up and<br />
running. Cisco SD-WAN vAnalytics provides<br />
visibility, forecasting for applications and<br />
bandwidth planning, what-if scenarios and<br />
actionable recommendations. Cisco Meraki<br />
Insight, meanwhile, helps administrators to<br />
optimise the end-user experience by providing<br />
valuable insight into WAN and SaaS<br />
application performance, significantly<br />
reducing the time it takes to isolate and<br />
resolve issues.<br />
Scott Harrell, Senior VP and General<br />
Manager, Enterprise Networking at Cisco<br />
explains, "We have set an ambitious goal<br />
for ourselves of transforming the entire network,<br />
from campus to branch, data centre<br />
to edge. The WAN is a vital part of the network<br />
and is one of the toughest to manage.<br />
As we bring insight into the WAN with<br />
these new innovations, we get closer to<br />
delivering end-to-end intent-based networking<br />
to help our customers eliminate downtime<br />
and save money."<br />
Vikram Makhija, General Manager,<br />
Cloud Business Unit, at Cloudera has been<br />
speaking about what he describes as the<br />
industry's first machine learning and analytics<br />
Platform-as-a-Service built with a<br />
Shared Data Experience (SDX). "Cloudera<br />
Altus with SDX enables businesses to build<br />
and manage multi-function analytics use<br />
cases in the cloud, integrating data engineering,<br />
IoT, customer and operations analytics,<br />
with machine learning," said Makhija.<br />
"We offer a proven solution for businesses<br />
to capitalise on the value of their data,<br />
avoiding the analytics cloud sprawl problem<br />
through the simplicity and scale of our<br />
modern cloud platform for machine learning<br />
and analytics."<br />
Commenting on the Cloudera news, IDC<br />
says that "In 2017 and beyond, IT buyers,<br />
which include the various LOBs considering<br />
investing in big data and analytics and<br />
cognitive computing, would have to consider<br />
more than just a single use case within<br />
their respective business units. Big data<br />
analytics (BDA) has been well established<br />
on the ROIs and relative ease at which<br />
each individual business unit is able to<br />
adopt a BDA solution and rapidly apply it<br />
within their environment. The common<br />
challenge faced is when attempting to<br />
scale or replicate success achieved to more<br />
LOBs or function groups." NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 9
FEATUREAI<br />
THE AI SANITY CHECK<br />
ALL THE BALLYHOO IN THE MEDIA ABOUT<br />
ARTIFICIAL INTELLIGENCE HAS BEEN<br />
FOCUSED ON THE CRUDEST FORMS OF THE<br />
TECHNOLOGY. PETER COCHRANE,<br />
PROFESSOR OF SENTIENT SYSTEMS AT THE<br />
UNIVERSITY OF SUFFOLK, EXPLAINS WHAT<br />
HAPPENS AS WE STEP ONTO THE SECOND<br />
RUN OF THE AI LADDER<br />
All of the commercial AI available<br />
today is the simplest and crudest<br />
manifestation imaginable. At a<br />
fundamental level it does one thing and<br />
only one thing well; pattern recognition in<br />
the form of matching or classification.<br />
Intelligent search, speech, music and face<br />
recognition, cancer cell detection and<br />
identification, abnormal crowd and<br />
business or market behaviours are typical<br />
of the abilities found in today's<br />
applications space.<br />
The numerous techniques used on this<br />
first rung of the AI ladder embrace Neural<br />
Networks; Deep Learning; Heuristics;<br />
Vector Machines; Markov Decisions, et al.<br />
And all are basically advanced<br />
mathematical/probabilistic modelling and<br />
decision making techniques. But despite<br />
their essentially simple basis, they have,<br />
and continue to yield remarkable and<br />
powerful results. It might just be that we<br />
are seeing an 80 per cent of reward for a<br />
mere 20 per cent of effort and<br />
sophistication.<br />
An often posed question asks why it has<br />
taken so very long for AI to deliver on the<br />
promises of 50 years ago. The short<br />
answer is hardware technology density and<br />
complexity. Only in the last 5 years have<br />
we enjoyed computing hardware of<br />
sufficient transistor destiny and processing<br />
power to realise powerful AI at an<br />
affordable price. Exemplified by<br />
comparing the 1985 Cray 2 with the 2012<br />
iPhone 5, we all now have a much<br />
cheaper supercomputer in our pocket!<br />
The list of AI contributions to our<br />
civilisation is already formidable and in<br />
some niche areas AI now far exceeds<br />
human abilities. These include medical<br />
diagnosis; general knowledge; short term<br />
stock trading; wargaming; business<br />
modelling; every computer, board and<br />
card game; document reading and<br />
analysis; cellular and DNA analysis;<br />
autonomous robotics, and so on.<br />
So, what happens next? Very recently,<br />
one particular application lifted a foot<br />
onto the second rung of the AI ladder.<br />
After trying all of the known gaming,<br />
analytic, and predictive approaches to<br />
GO, the AlphaGO team remained<br />
confounded by failure. GO is the most<br />
complex game invented by man and<br />
presents more decision options than the<br />
number of atoms in the universe. And<br />
therein lies the problem - none of the<br />
standard techniques described above can<br />
deal with such complexity, and teaching a<br />
machine the rules and how to play like a<br />
human just results in mediocre humanlike<br />
results.<br />
How did they crack this problem?<br />
AlphaGo was programmed to watch and<br />
learn. After watching game after (human)<br />
game to learn the rules, it then played<br />
over 30 million games against itself.<br />
Having thus become a skilled player, with<br />
more game playing experience than all the<br />
GO Grandmasters that ever lived, it was<br />
ready to do battle against our best<br />
champion. No surprise; it won every game<br />
and AlphaGo is now the world champion.<br />
The next decade is going to see a raft of<br />
new AI entering the arena on this second<br />
rung. They will be will be big<br />
gamechangers in chip, circuit and network<br />
design, autonomous vehicles, surgical<br />
robots, robotics for the workspace and<br />
home, autonomous weapons of war,<br />
intelligent search and find, human intellect<br />
amplification - again, the list is endless.<br />
Just how and why this should be so is<br />
revealed by the nature of Intelligence as<br />
defined here: I ~ log2[1 + AS ( 1 + PM<br />
)], where I = Intelligence, A = Actuator<br />
(output), S= Sensors (input), P =<br />
Processing Power and M = Memory.<br />
Whilst it is possible to have intelligence<br />
without memory or processing power, it is<br />
impossible sans sensors and actuators.<br />
Connection and networking is essential for<br />
true cognition and self-awareness and we<br />
are affording AI this facility through our<br />
networked mobile devices, sensor nets and<br />
IoT. The ultimate outcome will be human<br />
empowerment and intellect amplification,<br />
plus of course, a few surprises in the form<br />
of emergent behaviours… NC<br />
10 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
FEATUREAI<br />
THE REINFORCING BENEFITS OF AI<br />
AI IS NOT A REPLACEMENT FOR TRADITIONAL<br />
NETWORK SECURITY BUT HAS THE POTENTIAL<br />
TO BOLSTER IT. DEREK LIN, CHIEF DATA<br />
SCIENTIST AT EXABEAM EXPLAINS HOW AI-<br />
BASED BEHAVIOUR MONITORING CAN<br />
AUGMENT NETWORK SECURITY USING A MORE<br />
DYNAMIC APPROACH TO THREAT DETECTION<br />
Whichever way you look at it, the<br />
task of keeping networks safe from<br />
security breaches is becoming<br />
harder, perhaps even impossible. The<br />
constantly growing threat landscape,<br />
combined with tighter headcounts and larger<br />
volumes of organisational data makes for a<br />
worrying outlook. Simply put, there aren't<br />
enough people in most IT security teams to<br />
cope with the number of potential threats.<br />
For this reason, many forward-thinking<br />
organisations are turning to technology in<br />
order to find effective solutions to some of<br />
today's most pressing network security issues.<br />
The growing popularity of AI-based<br />
behaviour monitoring is a prime example.<br />
WHAT IS AI-BASED BEHAVIOUR<br />
MONITORING?<br />
AI-based behaviour monitoring harnesses<br />
the power of data analytics and machine<br />
learning to mitigate one of the biggest<br />
network risk factors: the user. Machine<br />
learning algorithms analyse the behaviour<br />
trends of network users over time and<br />
create baselines on a per-user basis.<br />
Benchmarking routine (normal) behaviour<br />
in this way provides the context needed to<br />
establish abnormal user activity which can<br />
be quickly identified and flagged. By<br />
contrast, conventional network monitoring<br />
tools lack this context, increasing the<br />
chances of suspicious behaviour being<br />
missed, or conversely, normal behaviour<br />
being deemed suspicious and creating<br />
false positives.<br />
For example, an HR employee accessing<br />
financial information using the network may<br />
initially appear to be abnormal, but if they<br />
have a history of doing so, as the result of<br />
working with the accounts team on employee<br />
payroll, then this activity could in fact be<br />
normal. Machine learning engines can track<br />
and correlate this in line with established<br />
benchmarks, meaning that a false positive<br />
will not be thrown up each time it occurs.<br />
The concept of benchmarking user<br />
behaviour in this way isn't new, but to do it<br />
manually takes a significant amount of time<br />
and resources, both of which are usually in<br />
short supply for IT security teams. AI-based<br />
systems do it much more efficiently, meaning<br />
security personnel are free to focus their<br />
attention elsewhere. Furthermore, AI-based<br />
systems can adapt to new patterns of user<br />
behaviour and refine acceptable parameters<br />
over time, meaning that real threats are<br />
quickly spotted and false alarms minimised.<br />
AI IS REINFORCEMENT, NOT<br />
REPLACEMENT<br />
While the benefits of AI-based behaviour<br />
monitoring are numerous, it isn't a magical<br />
fit-and-forget solution to resolve user-centric<br />
network security issues. Misleading<br />
marketing from vendors, combined with poor<br />
audience understanding has led to some<br />
organisations getting carried away, thinking<br />
they can cut down their IT teams and entrust<br />
their network security to the new AI<br />
guardians instead. This is folly.<br />
While AI-based solutions can greatly<br />
improve the understanding of user behaviour<br />
across the network, careful management<br />
from skilled security experts remains critical.<br />
Rather than being viewed as a replacement,<br />
AI should instead be seen as a powerful<br />
reinforcement for existing security practices<br />
and personnel, adding intelligence and<br />
helping to reduce wasted time.<br />
An effective AI-based behaviour<br />
monitoring system can consume significant<br />
amounts of data, compile user activities into<br />
timelines, and analyse them against<br />
benchmarked behaviour in a matter of<br />
minutes. This same task would take an<br />
experienced incident response analyst days,<br />
weeks or even months. Freed from this<br />
manual task, the analyst can then spend<br />
more time reviewing the user sessions<br />
created for suspicious behaviour deviations,<br />
or verifying the alerts that the AI system has<br />
triggered, creating a win-win.<br />
The challenges faced by network security<br />
teams are both numerous and difficult.<br />
Adopting technology such as AI-based<br />
behavioural monitoring can significantly<br />
reduce the workload, removing many of the<br />
more time consuming manual tasks that<br />
effective network security requires. However,<br />
it shouldn't be seen as a magical<br />
replacement for skilful IT security personnel,<br />
rather a powerful reinforcement that can<br />
greatly improve any team's operational<br />
effectiveness. NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 11
FEATUREAI<br />
INTELLIGENCE THAT IS<br />
ARTIFICIAL<br />
AI-BASED CYBERSECURITY IS<br />
NOT AN 'INSTALL AND LEAVE'<br />
OPTION. KEN GILMOUR, CTO<br />
AT INVINSEC EXPLAINS WHY<br />
Forget everything you've seen in sci-fi<br />
movies or read in sci-fi books about<br />
Artificial Intelligence. Forget about<br />
all the amazing and scary things AI<br />
promises to do and the jobs it will replace.<br />
AI of any kind has some major and<br />
fundamental flaws.<br />
Firstly it has no common sense. As a<br />
human, you might bake a cake so that<br />
other people can eat it. Humans<br />
understand this as a part of being human,<br />
but AI is unable to rationalise the concept.<br />
Secondly, AI has no understanding of what<br />
it sees. AI doesn't yet know how to solve<br />
crimes. It may recognise a pattern when a<br />
crime is taking place, but is currently<br />
unable to solve a crime that has already<br />
happened. If you are considering an AIbased<br />
cybersecurity deployment for your<br />
organisation, remember these points.<br />
HOW CAN AI LEARN IF THERE IS<br />
NOTHING TO TEACH IT?<br />
Let's consider a simple pattern recognition<br />
example. Say that you sell gadgets online<br />
and you've just installed your new supercool<br />
AI cybersecurity system. Your new<br />
investment uses its brain to automatically<br />
block attacks, meaning that you can relax.<br />
You will probably want your new AI<br />
system to learn about your customers'<br />
browsing habits, and so you decide to<br />
install it months before your biggest<br />
annual event, Black Friday. It's doing<br />
great and learning what's normal and<br />
what isn't. It's looking at simple patterns,<br />
such as multiple failed logins and,<br />
realising that these are brute force<br />
attacks, blocks them accordingly.<br />
GOING LIVE<br />
After several months you are more<br />
confident that you can detect multiple<br />
variations of attacks that previously you<br />
had no signatures for. Confidence is high<br />
that your security AI solution understands<br />
your unique environment, and you're<br />
hopeful that when Black Friday comes,<br />
nothing will take you down.<br />
On the day before, everything is<br />
prepared. At exactly midnight, you're<br />
going to launch some amazing deals that<br />
will create significant revenue for you. At<br />
23:50 you see some attacks. The system<br />
detects them and successfully thwarts the<br />
attackers. At 23:59:59, all of your<br />
customers start refreshing their web page<br />
so they can reload their choices. They<br />
don't need to do that because your<br />
website will automatically update them.<br />
Maybe you expected it, maybe you didn't.<br />
Has your AI seen this before and does it<br />
know what to do?<br />
Your AI thinks it's detecting a DDoS<br />
attack because it sees thousands of IP<br />
addresses competing for the same<br />
resource at the same time and a<br />
significant bandwidth increase. Your AI<br />
security solution blocks prospective<br />
customers and you lose several minutes<br />
trying to switch it off so that customers can<br />
connect and transact. You lose some<br />
customers who gave up after a few<br />
minutes; they're not patient, and they look<br />
for the deals elsewhere.<br />
With no choice, you disable your sole<br />
security mechanism because it's blocking<br />
your customers. The attack you saw at<br />
23:50 was a real attack and now you<br />
can't detect it. The attacker gets in,<br />
hijacks accounts and steals money from<br />
your customers.<br />
WHAT JUST HAPPENED?<br />
This is not an unrealistic scenario. It<br />
becomes obvious that you need humans in<br />
a Security Operations Centre (SOC)<br />
watching the patterns that the AI is<br />
recognising to make common sense of the<br />
problems and understand the scenarios.<br />
You also need other patterns written by<br />
humans to help the AI recognise variations<br />
of those patterns so that you can optimise<br />
the work of the humans and make them<br />
more cost-effective.<br />
AI is not something which can be trusted<br />
on its own. The solution to your security is<br />
defence in depth. AI helps, but do remember<br />
that its intelligence is artificial. NC<br />
12 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
FEATUREAI<br />
THE AI POWER CHALLENGE<br />
COMPUTING POWER OF A SUITABLE TYPE AND CAPACITY IS AN<br />
ESSENTIAL FIRST STEP IN STARTING THE AI JOURNEY. DAVID<br />
HOGAN, SENIOR DIRECTOR ENTERPRISE AT NVIDIA EXPLAINS<br />
Fuelled by GPU (Graphics Processing<br />
Unit) deep learning, we're in the early<br />
stages of a new computing era: AI<br />
computing. We know that early investment<br />
in new technology can provide first mover<br />
advantage, but it's also natural to<br />
approach it with scepticism and caution.<br />
Additionally, figuring out how to get<br />
started with AI can be daunting. So what's<br />
the best way to get your head around AI<br />
and understand what it can do for your<br />
organisation? Consider the following as<br />
you start your journey.<br />
EMBRACE THE NEW AND LEARN<br />
FROM OTHERS<br />
AI was once the stuff of science fiction, but<br />
now autonomous racing cars take to the<br />
track, artificially intelligent chatbots answer<br />
customer queries, and deep learning helps<br />
to find new ways to battle diseases like<br />
cancer. Industries like automotive and<br />
healthcare have been quick to adopt AI<br />
and are already reaping the benefits,<br />
creating new products, services and<br />
solutions. Accordingly, others can learn<br />
from those that have gone before in other<br />
verticals and seize the opportunity to be a<br />
pioneer in their own.<br />
GOOD QUALITY DATA - AND<br />
LOTS OF IT<br />
The success of deep learning systems is<br />
measured by the level of accuracy they<br />
achieve. This requires a huge amount of<br />
training data, as well as sophisticated<br />
neural networks which can learn from<br />
these vast datasets without forgetting<br />
past experience.<br />
Cutting corners on data collection is<br />
unwise. If you want to get the best results,<br />
you need to ensure that your datasets<br />
incorporate high-quality, labelled data.<br />
Implementing a clear workflow is crucial<br />
for enterprises wanting to capture the type<br />
and volume of data that they will need.<br />
HIRE AND RETAIN<br />
The demand for skilled staff far outweighs<br />
supply; it's becoming an increasingly<br />
competitive job market for deep learning<br />
developers. But building the right team is<br />
critical to a successful long-term AI<br />
strategy. Investing in a balanced,<br />
experienced and talented team allows a<br />
business to stand out from the crowd, and<br />
attract still more talent.<br />
To retain talent, you'll also need to<br />
provide them with the right space to grow<br />
and develop, as well as cutting-edge<br />
computing tools to do their work. Your<br />
research team will have to execute<br />
thousands of training jobs as they build<br />
your systems, so ensure they have the<br />
compute power required.<br />
TESTING: CLOUD-BASED DEEP<br />
LEARNING DEVELOPMENT<br />
PLATFORMS<br />
The prospect of investing in and<br />
maintaining deep learning hardware and<br />
software can seem challenging. In the<br />
last six months alone one framework,<br />
TensorFlow, has gone through six<br />
different versions.<br />
You can make life easier by taking<br />
advantage of cloud-based tools that<br />
provide a managed deep learning<br />
environment that scales to your needs.<br />
Amazon Web Services, Microsoft Azure<br />
and Google Cloud all offer cloud-based<br />
GPU instances for deep learning, ideal for<br />
testing and proof of concept projects. The<br />
NVIDIA GPU Cloud (NGC) also simplifies<br />
software tools for GPU deep learning,<br />
providing ready-optimised containers,<br />
frameworks and libraries that are<br />
automatically updated.<br />
SUCCESS REQUIRES FLEXIBILITY<br />
AND STABILITY<br />
Creating a stable platform for developers<br />
in the midst of an extremely dynamic deep<br />
learning ecosystem is crucial. Developing<br />
an end-to-end production pipeline can<br />
help ensure you nurture innovation, while<br />
not losing sight of the aims of the project.<br />
Establishing a baseline performance<br />
model and useful metrics can provide<br />
insights into project performance and<br />
allow for easy comparisons between<br />
models. Testing against these metrics<br />
regularly will make it easier to measure<br />
progress and reveal where improvements<br />
can be made.<br />
Remember that AI algorithms rarely live in<br />
isolation. When deployed as products, they<br />
will have to meet a number of nonfunctional<br />
requirements. If your system is<br />
constrained by power consumption,<br />
latency, memory or something else, then<br />
you will need to understand, control and<br />
react to this requirement from day one. NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 13
PRODUCTREVIEW<br />
Altaro VM Backup -<br />
Unlimited Plus<br />
Edition<br />
PRODUCT REVIEW<br />
PRODUCT<br />
REVIEWPRODUCT RE<br />
Data backup has had a chequered past<br />
and has often been an afterthought. It<br />
is now a critical component of IT<br />
operations, digital transformation, security and<br />
compliance, with a definitive role and<br />
lifecycle. This is embraced and enabled by<br />
Altaro VM Backup version 7.6, available in<br />
four versions. Here we review the fully<br />
featured, Unlimited Plus edition.<br />
We downloaded the installer (less than<br />
150MB) ran install, and were quickly<br />
presented with a guided three-step set-up,<br />
which dealt with licensing, specifying a backup<br />
location and our backup targets. Using the<br />
default settings we had a credible<br />
configuration in less than fifteen minutes.<br />
Complexity of storage estate will naturally<br />
increase this, but it's very intuitive to get things<br />
working and advanced options can be<br />
considered using familiarity, understanding<br />
and evolving requirements.<br />
Five backup locations are offered: Physical<br />
Drive, Network Path (LAN), Cloud (Azure),<br />
Altaro Offsite Server and Drive rotation. How<br />
these are used depends on an organisation's<br />
policy and compliance, but each can be<br />
granularly adjusted to suit. The flexibility<br />
offered allows a Disaster Recovery (DR) site to<br />
be established.<br />
Using the sidebar we explored Advanced<br />
Settings. Application Consistent Backup (ACB),<br />
enabled by default, will truncate transaction logs<br />
and ensure the VM is aware a backup has been<br />
taken. A new feature in this version, Continuous<br />
Data Protection (CDP) can backup as frequently<br />
as every five minutes. It's a feature to use with<br />
caution, and ACB cycles will mostly be less<br />
frequent. It's worth understanding the<br />
connections, because if a backup doesn't<br />
complete in five minutes it will immediately start<br />
the next one, effectively reducing frequency.<br />
Backup Health Monitor runs in the<br />
background, except when CDP is enabled. It<br />
ensures that backups are viable and that any<br />
bad blocks are self-healed. Storage capacity is<br />
always an issue with backup, and Altaro<br />
manage this using standard and custom<br />
Backup Policy options. This is complemented<br />
by GFS (Grandfather, Father, Son) Archiving,<br />
also new to 7.6, forming an essential part of<br />
backup operations.<br />
Managing by exception is aided with optional<br />
failure notifications by email and 7.6<br />
Deduplication ensures that data is stored only<br />
once. Change Block Tracking allows fast<br />
backup by reducing scanning and<br />
incrementally backing up. Volume Snapshot<br />
Service (VSS) can be disabled for non-<br />
Microsoft sources. All remote backups are<br />
encrypted by default and cannot be turned off,<br />
as they can for local backups.<br />
Like all Altaro functions Restore is highly<br />
intuitive, and with a target and location<br />
selected it simply gets on with it, while the<br />
Dashboard keeps you briefed. There is an<br />
option to undertake a test restore and even to<br />
restore a complete VM instance: in this case<br />
there is an option to disable the network to<br />
avoid IP conflict. It is possible to restore a<br />
single file, email or complete Virtual Disk.<br />
Verification and Sandbox Restores can be<br />
scheduled and boot from backup is especially<br />
important when facing a Ransomware attack.<br />
If, for example, you were running CDP and<br />
had an idea when a compromise took place,<br />
you could select an appropriate restore point,<br />
boot, and safely run.<br />
Reports provide Dashboard insight to all<br />
operations. The ingenious Get Help feature<br />
provides Telephone, Email and Chat support<br />
and can generate error reports and even<br />
provide remote support.<br />
It's quite possible that some smaller<br />
organisations may not understand what they<br />
should backup, in which case the default steps<br />
will quickly get them to a secure, defendable<br />
backup status. From here, experience and<br />
backup experiments, combined with easy<br />
creation can produce an extremely tailored,<br />
highly effective data backup and disaster<br />
recovery solution.<br />
With Altaro, VM backup and DR is assured<br />
and no longer a worry or a chore. NC<br />
Product: Altaro VM Backup Unlimited Plus<br />
Edition<br />
Supplier: Altaro Software<br />
Telephone: +44 (0) 203 397 6280<br />
Web site: www.altaro.com<br />
Email: info@altaro.com<br />
Price: £650 per host<br />
14 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
SHOWPREVIEW<br />
IP EXPO<br />
MANCHESTER, 25TH<br />
TO 26TH APRIL<br />
IN NEED OF INSPIRATION,<br />
GUIDANCE OR HELP? CONFUSED<br />
BY CLOUD OPTIONS, NEEDING A<br />
CYBER SECURITY UPGRADE OR<br />
WONDERING HOW TO MAKE AI<br />
WORK FOR YOU? IP EXPO IS<br />
BACK IN MANCHESTER TO HELP<br />
IP EXPO, Europe's largest enterprise IT<br />
event series, returns to Manchester Central<br />
on 25th-26th April. The two day event will<br />
bring together experts and visionaries from<br />
across the technology industry to share their<br />
views on the hottest technology issues of the<br />
moment. The event is organised around six<br />
main themes as follows.<br />
CYBERSECURITY MANCHESTER<br />
With GDPR coming into force 29 days after<br />
IP EXPO Manchester and data breaches<br />
happening daily, IP EXPO Manchester has a<br />
significant focus on cybersecurity for 2018.<br />
Across the event, security gurus, white hat<br />
hackers and legal experts will be delivering<br />
cutting edge advice and insight into security<br />
issues. The opening keynote for the event will<br />
be delivered by former GCHQ Director<br />
Robert Hannigan, who will provide a<br />
reminder for everyone on cyber best practise<br />
and the new threats that organisations face.<br />
Bradley Maule-ffinch, EMEA Portfolio<br />
Director for the IP EXPO Event Series<br />
comments that, "In the era of GDPR we<br />
want visitors at IP EXPO Manchester 2018<br />
to walk away confident so that they can<br />
execute the cybersecurity strategy that is<br />
best suited for their business. To do this,<br />
we're bringing together experts from across<br />
industry and academia to share their vision<br />
and knowledge on cybersecurity in the<br />
year ahead."<br />
DATA & ANALYTICS<br />
Data is the fuel of the modern, digitally<br />
transformed organisation. But if you're still<br />
paddling through data lakes rather than deep<br />
diving for insights, IP EXPO Manchester<br />
keynote speaker Dr Hannah Fry, Lecturer in the<br />
Mathematics of Cities at the Centre for<br />
Advanced Spatial Analysis at UCL, will be able<br />
to give you some inspiration. Her opening<br />
keynote on 26th April, The Joy of Data, will<br />
have you think twice about how you apply<br />
analytics to get the most from your data.<br />
CLOUD & IoT<br />
Cloud and IoT have changed how<br />
organisations operate. At IP EXPO Manchester,<br />
speakers and exhibitors will be delving into the<br />
next evolution of cloud, looking at how to<br />
manage multi-cloud environments, how cloud<br />
improves collaboration and cost efficiency, and<br />
how IoT can operate at scale. Highlight<br />
speakers include Nick Martin, Head of<br />
Google Cloud, Retail & CPG at Google and<br />
Ian Massingham, Worldwide Lead, AWS<br />
Technical & Developer Evangelism at Amazon<br />
Web Services.<br />
ARTIFICIAL INTELLIGENCE<br />
AI is here to stay, but rather than the future<br />
depicted in films like Blade Runner, Deep<br />
Learning, Data Science and AI enterprise<br />
applications are headlining the AI track at IP<br />
EXPO Manchester. Visitors will be able to get<br />
the AI facts straight from the companies and<br />
people at the cutting edge of current AI<br />
development. Highlight speakers include Lorna<br />
Mitchell, Developer Advocate at IBM Watson<br />
Data Platform and Katie Gibbs, Head of<br />
Consulting and Delivery at Heron.<br />
DEVOPS<br />
If you want to make continuous delivery and<br />
agile architecture a reality in your organisation,<br />
then make sure to check out the DevOps track<br />
at IP EXPO Manchester. Speakers such as<br />
Adrian Daniels, Solutions Architect at CHEF,<br />
and Emily Freeman, Developer Advocate at<br />
Kickbox will be educating attendees on<br />
everything you need to know to help create a<br />
high performing DevOps team which forms a<br />
key part of your organisation.<br />
NETWORKS & INFRASTRUCTURE<br />
Networks and infrastructure is the backbone of<br />
modern IT. At IP EXPO Manchester, exhibitors<br />
and speakers, including George Tunnicliffe,<br />
Head of IT Operations at National Theatre<br />
and Tom Arbuthnot, Unified Comms Architect<br />
at Modality Systems, will dig into the solutions<br />
and strategies for building efficient<br />
infrastructure capable of meeting the growing<br />
demands of future technology trends. NC<br />
For further information and to register for<br />
free for IP EXPO Manchester 2018, please<br />
visit: www.ipexpomanchester.com. Get<br />
involved on Twitter using the<br />
#IPEXPOManchester hashtag.<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 15
SHOWPREVIEW<br />
UC EXPO | EXCEL LONDON | 16TH<br />
TO 17TH MAY 2018<br />
SMARTER COLLABORATIVE WORKING IS NOW<br />
THE NORM AS ORGANISATIONS TAKE<br />
ADVANTAGE OF NEW METHODS,<br />
TECHNOLOGY AND BEST PRACTICE. UC EXPO<br />
DIGS INTO COLLABORATION CONUNDRUMS<br />
FOR ITS 2018 EVENT<br />
Smarter collaboration is the backbone<br />
of modern working, but is the school<br />
curriculum doing enough to provide<br />
students with the collaboration skills they<br />
need? Workplace demand for<br />
collaboration skills is high and<br />
organisational leaders must ensure that<br />
they provide the collaboration tools that<br />
their employees need and expect.<br />
"Workplace habits are changing at an<br />
incredible pace. Generational changes<br />
mean that many employees now expect to<br />
have flexible working practices, cool<br />
benefits and the latest technology as<br />
standard. As a result, the demands of<br />
unified communications and collaboration<br />
technology evolves rapidly too," comments<br />
Bradley Maule-ffinch, EMEA Portfolio<br />
Director for UC EXPO. "We're bringing<br />
together the world's leading influencers<br />
and brands to discuss the next evolution in<br />
smarter collaboration technology."<br />
Over two days, presentations, seminars<br />
and panel debates from industry leaders,<br />
and over 100 exhibitors, will provide<br />
attendees with the opportunity to discuss<br />
the most advanced technical solutions<br />
available. This will equip them to address<br />
their communication and collaboration<br />
challenges and develop a plan for their<br />
future, unified capability.<br />
HIGHLIGHT SESSIONS<br />
Kim Wylie, Head of Customer Change and<br />
Transformation at Google Cloud, will<br />
share her insights for building a culture<br />
where knowledge is a shared resource and<br />
employees act like owners. She will also<br />
discuss the psychology of change, why so<br />
many employees struggle to adopt new<br />
technologies and processes, how leaders<br />
can effectively inspire new ways of working<br />
and the role of teamwork and culture in<br />
bringing collaboration to life.<br />
Dave Michels, Principal Analyst at<br />
TalkingPointz will look at what's driving<br />
the adoption of Workstream<br />
Collaboration, why the shift matters, and<br />
key considerations in selecting a strategy.<br />
He will be covering how messagingcentric<br />
solutions for enterprise<br />
communications are filling a gap that<br />
most enterprises didn't realise they had,<br />
bringing with it a new set of vocabulary,<br />
services and providers.<br />
Dr Nicola Millard, Head of Customer<br />
Insights & Futures at BT Global Services<br />
Innovation Team will explore how we can<br />
override our inner Neanderthal when it<br />
comes to virtual working and effectively<br />
collaborate with people we may never<br />
actually meet. She'll also be looking at<br />
questions such as do we need offices<br />
anymore as more business takes place in<br />
digital space? How do we ever turn off in<br />
a world of constant connection? How do<br />
we create common ground for<br />
collaboration as we bring together a<br />
diverse, disparate and dispersed set of<br />
people? Do digital employees need a<br />
different type of digital leadership?<br />
Michael Affronti, VP of Product at Fuze,<br />
will be sharing his view of future<br />
workplaces and how, when, and where<br />
people like to work; what makes work<br />
effective; the role of automation and AI,<br />
and to what extent we are unlocking<br />
human potential.<br />
PANEL DEBATE<br />
Some industry leaders will also be going<br />
head to head with a series of panel<br />
discussions to debate and challenge the<br />
topics of the moment. The panels are set<br />
to cover a range of topics, including the<br />
role of AI in the future of work, the pros<br />
and cons of collaboration tools,<br />
technology and techniques, what the<br />
workforce of the future will look like and<br />
their requirements. There will also be<br />
general discussion on the year ahead,<br />
revealing what the panellists believe could<br />
be game changing.<br />
UC EXPO will also provide attendees<br />
with access to over 100 exhibitors and the<br />
opportunity to get hands-on with the next<br />
wave of collaboration technology in the<br />
future tech demo zone, including cutting<br />
edge interactive whiteboards and<br />
augmented reality headsets. NC<br />
UC EXPO 2018 takes place 16th to 17th<br />
May 2018 at ExCeL London. Registration<br />
is free at www.ucexpo.co.uk and get<br />
involved on Twitter with #UCEXPO.<br />
16 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
OPINION<br />
PACKET MINING: THE GIFT THAT<br />
KEEPS ON GIVING<br />
MAKING ASSUMPTIONS WHEN NETWORK<br />
PROBLEMS OCCUR IS NOT A GOOD RESPONSE.<br />
CARY WRIGHT, VP PRODUCT MANAGEMENT AT<br />
ENDACE EXPLAINS WHY IT PAYS TO KEEP AN<br />
OPEN MIND WHEN TROUBLESHOOTING<br />
As IT professionals know all too well,<br />
not all outages and performance<br />
problems are created equal, and<br />
many just cannot be blamed on the<br />
network or Internet Service Providers.<br />
If the network driving your site isn't<br />
optimised or suffers performance<br />
problems then delays and outages can<br />
happen, which can cause huge losses in<br />
revenue. Shopify's global Black Friday<br />
trading results are a great example: with<br />
revenue take running at $130k a minute,<br />
even a short outage can be devastating.<br />
As businesses progress through their<br />
own unique digital transformation, their<br />
network can become their business. This<br />
is a reality that requires some attention,<br />
and here are a few things to consider.<br />
THE DEEPER CAUSE<br />
The fact is that the problem before you<br />
may not be the network or your ISP. All too<br />
often when performance takes a dive it's<br />
easiest to blame the ISP or the network,<br />
but quite often it's deeper than that. For<br />
example, for several months a remote<br />
branch of a leading Asian bank was<br />
experiencing a bank teller application<br />
issue at random intervals throughout the<br />
day, freezing customer transactions for up<br />
to 15 minutes each time.<br />
A packet capture appliance was<br />
deployed on the link into the data centre<br />
to record exactly what was happening.<br />
When the problem reoccurred, the<br />
Operations team was able to go back<br />
and look at the transactions in detail<br />
using the recorded network history.<br />
The packets were getting delivered<br />
correctly and the network layer was<br />
healthy, but the application was taking up<br />
to 15 minutes to respond. It turned out<br />
that a new version of the bank's teller<br />
application had been rolled out a few<br />
months previously, and it had a bug<br />
between the application and the database<br />
that caused the database to occasionally<br />
lockup and stop responding to queries.<br />
CONGESTED TRAFFIC<br />
Poor quality video conferences are also<br />
often blamed on the network, and quite<br />
often the network is actually the source of<br />
the issue, but often for different reasons<br />
than originally thought. For example, if<br />
someone's running a video conference<br />
and the video quality starts to degrade, it<br />
could be down to processes like a<br />
network backup taking place at the same<br />
time: your network may just be congested.<br />
A lot of backups happen over the WAN<br />
link to the cloud service provider. Your<br />
backup traffic should have low priority<br />
compared to your video traffic. If your<br />
video traffic is not getting preferential<br />
treatment, it may be that something has<br />
been set wrong in your backup<br />
application or your IP network and all<br />
services are getting equal treatment.<br />
STORMY PACKETS<br />
Misconfiguration in the network can also<br />
be an issue. It causes lots of garbage<br />
packets to be generated through the<br />
network and a misconfigured network can<br />
cause packet storms. It could be<br />
something as simple as a routing loop<br />
that's accidentally been set up because<br />
someone put a cable in the wrong port<br />
on a switch, sending out messages<br />
thousands of times per second, rather<br />
than once every 20 seconds.<br />
This example of a packet storm, a<br />
bunch of packets that overwhelm the<br />
network, taking up all available<br />
bandwidth, creates a critical situation.<br />
Once the fault occurs, the only thing<br />
businesses can do is dig into packets to<br />
see what is going on and resolve the<br />
responsible misconfiguration.<br />
It is becoming increasingly common for<br />
organisations to deploy dedicated<br />
network recording solutions to reduce the<br />
discovery time surrounding such network<br />
challenges. Having the ability to inspect<br />
packets enables those responsible to<br />
quickly determine if the problem source is<br />
the network itself, or if the problem is<br />
more deeply seated in an application<br />
issue such as overloading,<br />
misconfiguration or a bug. NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 17
SECURITYUPDATE<br />
TRUST THAT KNOWS<br />
NO BOUNDS<br />
BARRY SCOTT, EMEA CTO AT<br />
CENTRIFY SAYS THAT THE<br />
ONLY WAY TO BALANCE<br />
SECURITY AND AGILITY IN<br />
IAAS ENVIRONMENTS IS THE<br />
DETERMINED USE OF ZERO<br />
TRUST<br />
Infrastructure as a Service (IaaS) platforms<br />
offered by the likes of Amazon Web<br />
Services (AWS) support the innovation and<br />
app-driven business models that many<br />
organisations are migrating towards. But in<br />
their race to embrace digital transformation,<br />
some overlook that security in the cloud is a<br />
shared responsibility - the risks of which are<br />
potentially huge.<br />
The answer is Zero Trust security,<br />
delivered by focusing on identity and<br />
embracing the principle of 'never trust,<br />
always verify'. This allows organisations to<br />
manage their IaaS risk and secure their<br />
systems, data and users.<br />
IAAS AT RISK<br />
Estimates suggest that 89 per cent of<br />
organisations have adopted the public<br />
cloud, running 41 per cent of their<br />
workloads there. Yet it's a complex picture,<br />
with hybrid cloud being the preferred<br />
enterprise strategy as IT infrastructure is<br />
spread between multiple providers.<br />
Increased complexity increases threat<br />
opportunities both inside and outside the<br />
organisation. Trusted and untrusted users will<br />
access corporate resources from their own<br />
devices anywhere, anytime and can no<br />
longer be easily separated. Identity sprawl,<br />
silo-based systems, password-based logins<br />
and a spectacular rise in phishing attacks<br />
underlines the risk for IaaS environments.<br />
The stakes couldn't be higher yet the<br />
outcome of poor Identity and Access<br />
management (IAM) is ever present. For<br />
example, the infamous Uber breach when<br />
hackers obtained their AWS credentials. In<br />
fact, static passwords lay at the heart of<br />
many breach incidents. According to<br />
Verizon in its 2017 report, 81 per cent of<br />
hacking-related breaches used stolen<br />
and/or weak passwords.<br />
ZERO TRUST IN ACTION<br />
Given the risks, Zero Trust Security is the<br />
only sure way to secure IaaS systems and<br />
hosted applications. Zero Trust means<br />
verifying users using multi-factor<br />
authentication (MFA), regardless of user<br />
type, or the resource being accessed. Access<br />
decisions must be adaptive and dynamic. By<br />
ditching static passwords, phishing can<br />
virtually be eradicated, making it much<br />
harder for hackers to access cloud systems.<br />
Next you need to verify the device,<br />
meaning that identity-centric preventative<br />
controls must be extended to the endpoint,<br />
so that systems can appraise trust levels and<br />
on-device security and tie these to the user's<br />
identity to create an overall risk score. For<br />
example, a user requesting access on a<br />
device that they use every day establishes a<br />
certain level of trust when compared to that<br />
user logging-in via a shared workstation. As<br />
risk increases, the appropriate controls kick<br />
in, requiring additional factors of<br />
authentication, or restricting access.<br />
Limiting access and privilege is another vital<br />
component of the Zero Trust model, which<br />
must be tightly managed. That's why<br />
restricting access according to the well-worn<br />
principle of least-privilege provides just<br />
enough access inside each application for<br />
users to do their jobs. These applications<br />
often contain large amounts of critical data,<br />
and because they're accessed by more users<br />
within the organisation, they become easy<br />
targets. So the more critical the data, the less<br />
the privilege offered, which requires the<br />
increased use of MFA to ensure identity.<br />
Finally, for Zero Trust to work it must be able<br />
to learn and evolve over time. Platforms that<br />
gather information about the user, endpoint,<br />
application, server and policies are ideal<br />
because they can learn and baseline normal<br />
behaviour and spot unusual activity which<br />
might indicate a breach. Behaviour analytics<br />
are invaluable to administrators and can be<br />
used to ascertain the level of risk in real-time<br />
and provide key insights to determine when<br />
policies should be changed.<br />
The good news is that you don't need to<br />
spend big to extend best practice security to<br />
the cloud. With the right approach and<br />
guiding principles like MFA everywhere,<br />
least privilege and user accountability, your<br />
IaaS environment can be as secure as your<br />
data centre. NC<br />
18 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
OPINION<br />
NETWORKED AUDIO<br />
AS BUSINESS SERVICES<br />
CONVERGE ON THE<br />
NETWORK, THOSE INVOLVED<br />
MUST SPEAK THE SAME<br />
LANGUAGE. JOHN ELLIS,<br />
REGIONAL SALES MANAGER AT<br />
SHURE, EXPLAINS HOW TO<br />
APPROACH THE AV/IT<br />
CHALLENGE<br />
Video and audio conferencing has<br />
significantly evolved as it has moved<br />
from hardware to software based<br />
solutions. Google Hangouts and Skype for<br />
Business would both be examples. This<br />
approach offers savings and greater<br />
flexibility for organisations along with user<br />
experiences, which are good - but if the<br />
audio equipment isn't up to the job then it<br />
can all become a bit fraught.<br />
The need for both AV and IT teams to<br />
understand each other and collaborate<br />
effectively has never been so important, but<br />
can they talk the same language, and what<br />
are the challenges of integrating networked<br />
audio with an IT network?<br />
Most IT departments haven't really had to<br />
deal with networked audio until now, but if<br />
their audio service is to work efficiently, a<br />
successful integration will be essential. In<br />
achieving this, one of the biggest<br />
challenges is providing reassurance to the<br />
AV team that everything they require can be<br />
provisioned on the network, and that both<br />
groups can work together effectively.<br />
Network security is a substantial topic for<br />
the network team and it will be one of the<br />
first things that IT departments will want to<br />
address. But because audio operates in<br />
real-time, it needs to be afforded some<br />
network priority. Also, from a project<br />
perspective, when working with networked<br />
audio, a lot of the commissioning has to be<br />
completed onsite, which will always be<br />
more challenging than commissioning<br />
offsite. Typically, AV professionals will find<br />
themselves working with unfamiliar IT<br />
infrastructure, and this requires planning<br />
and disclosure.<br />
The apparently reasonable request for the<br />
definition and detail of the IT infrastructure<br />
may cause the IT department to be<br />
defensive, if only because of security<br />
concerns. With all of this in mind and as<br />
convergence between AV and IT continues,<br />
do we need a new breed of<br />
communications professional servicing<br />
both disciplines?<br />
It has been quite normal for specialists to<br />
focus on their chosen area and all too<br />
often working independently from the IT<br />
team. There is now so much being<br />
deployed across networks that AV<br />
integrators have begun to employ network<br />
architects who can take a holistic view of a<br />
customer's estate and successfully bring all<br />
of the disciplines together.<br />
In addition to the need for AV and IT to be<br />
well versed in each other's work there's also<br />
a need for standardisation - and this is now<br />
starting to happen. Shure has worked with<br />
QSC to deploy a global standard, but the<br />
continuing challenge is to keep deployment<br />
and standards consistent.<br />
IT convergence is not new, and there has<br />
been a growing number of independent<br />
technologies coexisting on the network for<br />
some time, but now these technologies<br />
need to start talking to each other in a<br />
way they haven't previously. As an<br />
industry, we must embrace this and<br />
change our approach.<br />
We are contributing to this by hosting<br />
regular seminars aimed at AV<br />
commissioning engineers, installers, AV<br />
designers and audio engineers. We aim to<br />
offer them a better understanding of the IT<br />
networking standards commonly used in<br />
today's audio transport protocols, along with<br />
practical, hands-on, demonstrations.<br />
The convergence of AV and IT departments<br />
is improving, but there are still probably<br />
more AV people learning about IT than IT<br />
learning about audio. AV manufacturers are<br />
working to produce IT standards-based<br />
equipment which will make it much easier<br />
for AV and IT departments to implement<br />
networked audio and to collaborate well.<br />
AV teams need to understand the<br />
challenges of running audio across the<br />
production network and educate<br />
accordingly. In turn, IT departments must<br />
understand that the AV industry is not<br />
going to be foolish enough to add<br />
products to a network that will compromise<br />
that network's security. NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 19
OPINION<br />
ENTERPRISE ARCHITECTS OR<br />
STRATEGIC ADVISORS?<br />
IS IMPROVEMENT A BIGGER GOAL THAN<br />
ALIGNMENT IN THE ENTERPRISE? TERRY<br />
BLEVINS, A FELLOW OF THE OPEN GROUP AND<br />
OWNER OF ENTERPRISE WISE LLC CONSIDERS<br />
THE ENTERPRISE ARCHITECTURE CHALLENGE<br />
How should Enterprise Architecture<br />
(EA) align with business operations?<br />
When I am asked this I wonder if it is<br />
the right question to start with. I'm not a fan<br />
of the concept of alignment outside of<br />
mechanics: outside of the physical space,<br />
alignment isn't strong enough and is<br />
typically too indirect for impact. Instead, I<br />
prefer to consider how EA can improve<br />
business operations. Besides, if EA efforts<br />
aren't driving business operation<br />
improvements, then perhaps it is time to<br />
reconsider the EA investment.<br />
Given my position is it reasonable to say that<br />
the answer is just an unequivocal yes, with an<br />
imperative to deliver good enterprise<br />
architecture? Well, sort of - but no<br />
architecture is a solution, it is part of a path<br />
towards a desired solution. EA is an essential<br />
element on the journey of driving<br />
transformation or enterprise-level changes.<br />
There is much to do to ensure that EA has the<br />
intended impact, and some of these things<br />
aren't adequately covered by EA methods<br />
alone.<br />
So, what is needed from enterprise architects<br />
beyond the fundamental goal to improve<br />
business operations?<br />
WORK WITH BUSINESS OPERATIONS<br />
AT THEIR TEMPO<br />
In its simplest form, an enterprise comprises<br />
three main areas; operations (business or<br />
mission), management (governance) and<br />
development. Operations are where the<br />
business or mission processes produce the<br />
enterprise's value proposition. Management<br />
provides the governance to see that the<br />
necessary things are done to ensure<br />
continuous delivery, and development is<br />
where improvements are made to people,<br />
process, policy and technology capability, to<br />
enable delivery.<br />
Typically, enterprise architects work in<br />
development. However, there is opportunity<br />
for them to work closely with operations<br />
(similar to the DevOps) to experience and<br />
understand operational issues. The enterprise<br />
architect could also use their extensive<br />
knowledge to solve problems. By working<br />
closely alongside them, they can gather realtime<br />
information about the enterprise that gets<br />
captured in the EA which will ultimately help<br />
solve future issues.<br />
ANSWERS AND GUIDANCE<br />
ON-DEMAND<br />
I have attended countless meetings where an<br />
enterprise architect stands in front of their<br />
leaders and explains the EA model. What<br />
really should be done is to demonstrate the<br />
questions that can be answered and the<br />
insights discovered relating to operations.<br />
More importantly, an enterprise architect<br />
needs to answer operations questions as they<br />
arise. The key is to talk less about architecture<br />
models and provide more operations-focused<br />
guidance. The enterprise architect can thereby<br />
build trust with the real decision-makers.<br />
Without this, they will not make an impact.<br />
ENABLE INFORMATION IN A<br />
SERVICE FASHION<br />
I am a big fan of service orientation. Not<br />
software, but human service orientation. I<br />
believe the best setup for EA organisations<br />
is a service-oriented model which provides<br />
services to the rest of the enterprise. These<br />
types of service would be divided within<br />
operations, management and<br />
development, where each division provides<br />
specific solutions designed to answer<br />
important questions for each division.<br />
These answers usually appear in the form<br />
of information or guidance.<br />
CONNECT THE EA BOXES TO<br />
OPERATION GOALS<br />
We've all seen the boxes-and-lines view of<br />
an EA where the boxes and lines are<br />
connected. To support and improve business<br />
operations, the goal must be to become first<br />
class citizens in the enterprise architecture.<br />
Certain elements of the model are necessary<br />
to deliver those goals: people, process,<br />
policy and technology, as well as computers<br />
and networks. These key elements must be<br />
connected to articulate all the necessary<br />
components of the solution, and those lines<br />
must possess real values that help to<br />
measure contribution towards the goals.<br />
In summary, there are clearly enterprise<br />
architects who are equipped for the task and<br />
these are the ones you'll want to seek out<br />
and leverage for the benefit of your<br />
20 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
OPINION<br />
CONTAINING<br />
EXPECTATIONS<br />
BEST PRACTICE IS THE MISSING<br />
PIECE OF THE CONTAINERS<br />
PUZZLE, SAYS MARCO CEPPI OF<br />
CANONICAL. CAN BEST<br />
PRACTICE DRIVE THE INDUSTRY<br />
FROM CHAOS TO ADOPTION?<br />
With its performance, cost efficiency<br />
and scalability benefits, the use of<br />
container technology for running<br />
applications in the cloud is fast becoming a<br />
hot topic in IT. A recent survey reported that 42<br />
per cent of organisations are already using<br />
containers and 451 Research predicts that this<br />
market will be worth $2.7 billion by 2020. The<br />
technology may still be in its relative infancy,<br />
but its many advantages are already<br />
prompting a wide variety of businesses to take<br />
the plunge.<br />
This growth has resulted in an explosion of<br />
start-ups appearing in the market, all focused<br />
on building, managing or providing container<br />
services and adding to the plethora of<br />
container-based solutions already released by<br />
virtually all the major cloud providers and<br />
vendors. However, there are some challenges<br />
that need to be overcome. While this thriving<br />
market has created an abundance of choice<br />
for customers, it has also made it difficult for<br />
businesses to understand exactly what the best<br />
choice is for them.<br />
A disconnect has also emerged between the<br />
interest being shown in containers and its<br />
adoption, with many enterprises hesitating due<br />
to security and implementation concerns.<br />
These are issues that the industry should be<br />
keen to solve.<br />
REMOVING THE RISKS<br />
Despite the promise of containerisation, many<br />
businesses are yet to be fully convinced.<br />
Certain industries, such as financial services,<br />
have been quick to embrace containers, but<br />
CIOs and IT managers in other sectors are<br />
still unsure if the technology is the right<br />
option for them.<br />
This hesitation is to be expected, as any new<br />
technology comes with risk. One way of<br />
calming these fears is for the industry to<br />
establish best practice guidelines that<br />
businesses of all sizes can follow. Currently<br />
missing from the world of containers, this is<br />
primarily because early adopters are<br />
attempting to figure out what best practices<br />
should look like as they go along, all in an<br />
effort to get ahead of their competition.<br />
By collaborating to provide<br />
recommendations for the creation,<br />
deployment and usage of containerised<br />
applications, vendors and customers can<br />
consolidate their experiences and help the<br />
industry to develop, offering adopters'<br />
confidence in their deployments.<br />
A CALL FOR STANDARDISATION<br />
Another way the industry can kick-start<br />
adoption is to foster greater levels of<br />
standardisation. Without common building<br />
blocks for everyone to adhere to,<br />
organisations can't be sure that the technology<br />
they adopt will work as expected. This has the<br />
potential to hinder the progression of<br />
technology, but once the industry agrees on a<br />
certain base standard, it's a different story.<br />
Organisations, once shown a clearer path<br />
along which to travel, can be sure that the<br />
fundamental aspects of the technology -<br />
regardless of their choice of vendor - will work<br />
in the same predictable way.<br />
The world of containers is no exception. By<br />
creating a standard way to build and manage<br />
container technology, all customers can be<br />
assured that their technical expectations will be<br />
met which will leave them free to pick the best<br />
solutions to suit their specific objectives.<br />
Various industry bodies are already in place<br />
to help shape the future of the industry. For<br />
example, the Open Container Initiative (OCI)<br />
which is focused on creating open industry<br />
standards around container formats and<br />
runtime. There's also the Cloud Native<br />
Computing Foundation (CNCF) which boasts<br />
138 members after less than two years of<br />
activity. These include the world's six largest<br />
public cloud providers, and its membership<br />
continues to grow at a significant rate.<br />
These changes will help the world of<br />
containers evolve from chaos to widespread<br />
adoption and realise the promise of a<br />
technology that will undoubtedly play a key<br />
role in the next evolution of IT for many<br />
years to come. NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 21
SECURITYUPDATE<br />
IoT SECURITY THAT<br />
WORKS<br />
IoT DEVICES EXTEND THE<br />
ATTACK SURFACE OF<br />
NETWORKS, BUT WHAT CAN BE<br />
DONE TO COMBAT THIS, AND<br />
HOW SHOULD THE RISK BE<br />
UNDERSTOOD? PROFESSOR<br />
WILLIAM WEBB, CEO OF THE<br />
WEIGHTLESS SIG EXPLAINS<br />
Recently, the IoT has been hit by a number<br />
of security attacks, including denial of<br />
service operations and the hacking of<br />
home networks - home networks that are all<br />
too often used by employees for their<br />
professional use. As the number of connected<br />
devices explodes and their importance<br />
inevitably increases, the effort that hackers put<br />
into breaking systems will only grow, as may<br />
their gains.<br />
Overcoming threats of this sort is businessas-usual<br />
for the conventional Internet, mobile<br />
telephony firms and other IT systems. Defences<br />
comprise two elements: firstly as good a level<br />
of protection as possible using encryption,<br />
authentication and AI analysis, and secondly<br />
the ability to rapidly react to threats that<br />
breach these defences with software updates.<br />
The same approach will be needed to secure<br />
IoT deployments.<br />
The challenge however for IoT is not so much<br />
in knowing how to deliver secure systems in<br />
principle, it is implementing it in practice on<br />
devices with very small amounts of memory<br />
and processing power, connected across<br />
wireless connections with limited capabilities,<br />
and where preserving battery power is<br />
operationally essential.<br />
Unfortunately, many early IoT<br />
implementations have compromised on<br />
security, and this has enabled a growing<br />
number of hacks and breaches. While many<br />
different approaches to security are possible,<br />
it seems likely that the optimal design for IoT<br />
will comprise:<br />
A shared secure key embedded within the<br />
IoT chipset, in much the same way that a<br />
secure key is embedded in cellular SIM<br />
cards. This has proven to be the best way<br />
to deliver authentication and encryption.<br />
An update capability that can broadcast<br />
and allow millions of devices to listen to<br />
and receive a downlink software update.<br />
Without this, sending the update to<br />
individual devices one-at-a-time can take<br />
days or months and consume most of the<br />
available network capacity. This will<br />
result in a massive number of lost data<br />
packets using a non-managed uplink<br />
network protocol.<br />
The ability to update the entire security<br />
suite should algorithms be shown to be<br />
compromised. This is important in IoT,<br />
where some devices can be in the field<br />
for 10 or more years, during which<br />
time security algorithm design will<br />
inevitably evolve.<br />
Enabling a system design of this sort requires<br />
a standards body that can oversee the<br />
allocation and distribution of shared keys and<br />
where the world's best security experts can<br />
provide their input. It requires a radio design<br />
with significant downlink capability, ideally in a<br />
flexible manner, so that the downlink/uplink<br />
ratio can be varied dynamically, providing<br />
more downlink capacity when a broadcast<br />
update is required. And it requires a standard<br />
where best practice security is embedded deep<br />
into all of the layers.<br />
This is exactly what we have achieved. We<br />
employ shared secret keys with mutual EAP-<br />
GPSK authentication with a trusted third party<br />
in a similar manner to the cellular industry and<br />
use best-practice algorithms such as AES-128<br />
from US security bodies. Additionally, we have<br />
a flexible broadcast mode that can deliver<br />
software updates to all devices, or to selected<br />
subsets, such as those belonging to a<br />
particular user group. We can deliver<br />
completely new cypher suites over the air if<br />
needed and traffic analysis within the network.<br />
Using AI and big data analytics we can detect<br />
unusual behaviour such as devices sending<br />
more messages than expected, so that those<br />
devices can be quickly disabled until the<br />
problem is resolved.<br />
Even the most innocuous IoT device can<br />
become the source of a security-breach.<br />
Unlike traditional IT, recalling all devices is<br />
logistically impossible, and would probably be<br />
financially disastrous. Clearly, security is an<br />
area where absolutely no risks can be taken,<br />
and weightless technology embodies the best<br />
possible security principles to address known<br />
and unattended risks. NC<br />
22 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
PRODUCTREVIEW<br />
AirCheck G2 from<br />
NETSCOUT<br />
PRODUCT REVIEW<br />
PRODUCT<br />
REVIEWPRODUCT RE<br />
Evolving from home user self-sufficiency,<br />
Wi-Fi - more accurately Wireless LAN - is<br />
often misperceived as simple, plug and<br />
play technology. But wireless networking is<br />
mission critical, complex and challenging to<br />
support - especially without infrastructure insight.<br />
Driven by convenience, wireless networks are<br />
everywhere, and while most require credentials<br />
for access, they can also adversely impact one<br />
another. Despite the fact that your laptop<br />
confirms internet connectivity and good line<br />
speed, the user experience may be<br />
characterised by slow throughput, intermittent<br />
connectivity, application error and downtime.<br />
Multiple factors can coalesce to create a<br />
fractious wireless experience. Most are easy to<br />
address once they are identified, quantified<br />
and understood. The AirCheck G2 from<br />
NETSCOUT, updated in November 2017, is a<br />
convenient handheld tester that puts the<br />
network technician in firm control.<br />
Powered on, a top-level screen with 7 options<br />
conveniently outlines capability: Networks,<br />
Channels, Access Points, Clients, Interferers,<br />
Auto Test and Ethernet Test. To establish our<br />
base line, we ran Auto Test and were greeted<br />
with an easy to understand assessment of Air<br />
Quality which showed the in-range channels<br />
and any interference. From here we examined<br />
individual Access Points (APs) in great detail<br />
and tested them.<br />
Using the touchscreen we selected Networks<br />
which displayed those available. For each, we<br />
could determine the number of APs, signal and<br />
noise level, connected clients, security, and<br />
when it was last seen.<br />
Selecting the WLAN channel with the greatest<br />
signal strength is rarely the best option. To this<br />
end Channels informs decision-making by<br />
displaying Channel usage, 802.11 and non<br />
802.11 devices, AP's using that channel, and a<br />
visual indication of noise level. Selecting a<br />
Channel provides further insight, including<br />
applications in use, and utilisation over time.<br />
APs, the last physical point of a WLAN, can<br />
only be assessed by understanding signal<br />
strength, noise, and security. Using Access<br />
Points, we examined this and insight included<br />
the BSSID (MAC address), Signal to Noise<br />
Ratio and frequency.<br />
Visualisation throughout is excellent and<br />
everything is colour coded for rapid triage:<br />
green is good, orange potentially a problem<br />
and red requires attention. However far you<br />
drill into detail, the home button on the status<br />
bar does just that, while another icon saves<br />
results to a PDF. A free Link-Live account stores<br />
results and creates timeline profiles.<br />
Clients revealed all in-range associated and<br />
unassociated devices - including another<br />
AirCheck G2! Because the WLAN radio<br />
spectrum is unlicensed, it is heavily congested<br />
with energy from a range of devices or<br />
Interferers. Interferers can be wireless and nonwireless<br />
devices as innocent as a neighbour's<br />
AP, a microwave oven, a forgotten AP, or an AP<br />
covertly installed for illegal network access.<br />
Interferers will list candidate details including<br />
the affected channels, device type (we<br />
observed a microwave oven), average and<br />
peak power, and when its effects were last<br />
seen. It's not possible to eradicate all problem<br />
sources, but the AirCheck G2 provides<br />
everything needed to configure a WLAN<br />
around them.<br />
Whether using a Tablet or a Wi-Fi telephone,<br />
people expect to move around and stay<br />
connected. Using the Roaming test facility it's<br />
possible to understand dynamic network quality<br />
by repeating a PING as you move. This helps<br />
to ensure a seamless network experience.<br />
Throughput is the best way to understand user<br />
experience and the AirCheck G2 can run an<br />
iPerf test. The Kit option provides a small tester<br />
that acts as an iPerf server and a directional<br />
antenna to locate unknown RF sources.<br />
Wireless networking needn't be a dark art,<br />
and with decent insight it is logical and easy to<br />
manage. The capability provided by AirCheck<br />
G2 is as essential to WLAN provision as fuel is<br />
to an engine. Without insight, the best you can<br />
hope for is to coast unguided, downhill… NC<br />
Product: AirCheck G2<br />
Supplier: NETSCOUT<br />
Web site:<br />
http://enterprise.netscout.com/aircheck<br />
Email: kim.kingsbury@netscout.com<br />
Price: £1,848 pounds excluding VAT<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 23
OPINION<br />
SMART CONNECTIVITY<br />
BY DESIGN<br />
CONNECTIVTY REQUIREMENTS<br />
ARE CHANGING BEFORE OUR<br />
EYES. OLI BARRINGTON,<br />
MANAGING DIRECTOR UNITED<br />
KINGDOM & IRELAND AT R&M<br />
EXPLAINS HOW TO BEAR<br />
DOWN ON THE CHALLENGE<br />
According to Cisco, global mobile data<br />
traffic will approach 50 exabytes per<br />
month by 2021. But before we<br />
consider how to ensure that the appropriate<br />
networks are in place, let's understand the<br />
trends driving this bandwidth demand.<br />
Mobile device users expect uninterrupted HD<br />
video and access to cloud-based applications<br />
from any location. 5G will boost demand for<br />
highly reliable connectivity, placing huge<br />
demand on the transfer capacity of cellular<br />
phone antennas. In order to allow providers to<br />
develop and deliver the services that users<br />
want, fibre optic cables to base stations will be<br />
required for backhaul.<br />
Cloud is another vital driver. IDC claims that<br />
half of all global value creation will be<br />
digitised by 2021. The increase of digital<br />
decentralised business and production<br />
processes will further boost data volumes.<br />
Billions of sensors, cameras and other devices<br />
connecting in coming years to support Internet<br />
of Things (IoT) applications will increase data<br />
volumes to allow continuous data analysis.<br />
Edge data centres are used to avoid latency<br />
and ensure local data availability, while cost<br />
benefits, consolidation and cloud requirements<br />
are driving the rise of hyperscale data centres<br />
and advanced (autonomous) mobility solutions<br />
that require networks with blanket availability<br />
and high-performance connectivity. Functions<br />
for smart buildings are also being<br />
incorporated into data networks. This enables<br />
more efficient use of resources, increases<br />
flexibility and helps organisations to realise<br />
sustainability goals.<br />
MAKING IT WORK: ESSENTIAL<br />
CONSIDERATIONS<br />
Connectivity will need to be ubiquitous: LANs,<br />
WLANs or mobile solutions with limited reach<br />
won't suffice. Cabling digitisation has to be a<br />
fundamental component of all planning, from<br />
office buildings, factories and homes, to<br />
transportation systems, public infrastructures<br />
and smart cities. How to determine and<br />
implement a solution and ensure it remains<br />
effective is a challenge.<br />
Ultra-high density cabling and network<br />
infrastructure will be essential to meeting the<br />
challenges brought by the data explosion and<br />
particularly by hyperscale or edge data<br />
centres. This need for higher density is driving<br />
changes to enclosures, cabinets and racks.<br />
Planning must anticipate this imminent<br />
increase and the need for more ports and fibre<br />
optic cables between and within data centres,<br />
as well as at access points.<br />
The next bandwidth evolution might happen<br />
quicker than you think, so looking beyond<br />
today's specifications, you may want to go<br />
further than 10G or 100G and focus on<br />
ensuring connectivity for the next 50 years or<br />
so. Also, it's essential to ensure the availability<br />
of skilled workers, as apps are no substitute for<br />
installers and experts that can care for millions<br />
of ports, antennas, cables and so on.<br />
Automation and documentation will become<br />
a challenge. No human can document and<br />
manage hundreds of thousands of ports and<br />
links without some automation. Complete<br />
automation of infrastructure and asset<br />
management is absolutely critical.<br />
Finally, and to increase the likelihood of<br />
success, you'll need to examine the three<br />
variables involved in achieving higher data<br />
rates - more fibres, more wavelength and<br />
higher modulation - before deciding to invest<br />
in the latest optical connectivity. These need to<br />
be weighed according to requirements.<br />
Balancing cost-effectiveness with performance<br />
in each part of the network is essential.<br />
REALISING A LASTING SOLUTION<br />
Integrating cabling design into building<br />
information systems to evaluate effectiveness<br />
upfront and on an ongoing basis is one<br />
method of realising smart connectivity. Another<br />
tactic would be to try looking at every building<br />
project as a data centre and applying widely<br />
available and understood best practices.<br />
It is vital to choose components that are<br />
robust, reliable and repairable and that<br />
require little maintenance. Include connectivity<br />
engineering as a standard component of<br />
design, building and maintenance plans,<br />
along with structural engineering and electrical<br />
cabling. The processes, evaluations and<br />
maintenance schedules commonly used in<br />
these areas can simply be extended to<br />
structured cabling. NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 25
OPINION<br />
WHEN STORAGE<br />
BECOMES DATA<br />
DO WE NEED TO CONSIDER<br />
STORAGE MEDIA OR SHOULD<br />
WE CONSIDER DATA<br />
HOLISTICALLY? MARK PETERS,<br />
PRACTICE DIRECTOR & SENIOR<br />
ANALYST AND SCOTT SINCLAIR,<br />
SENIOR ANALYST AT THE<br />
ENTERPRISE STRATEGY GROUP,<br />
COMBINE THEIR VIEWS<br />
The terms legacy and emerging when<br />
combined with the word storage can<br />
seem either obvious or innocuous -<br />
perhaps both. They're probably things that<br />
you simply accept as givens or maybe dismiss<br />
as marketing speak. In much the same way,<br />
you might not pay attention to phrases like<br />
'tomorrow's performance today', or 'futureproof<br />
your system'. They are catch-all's that<br />
probably don't get given that much thought.<br />
Indeed, if you were to stop and consider<br />
this topic, you might get stumped, or at least<br />
frustrated, quite quickly. Is the distinction<br />
between the terms legacy storage and<br />
emerging storage simply the age of an<br />
installation, or perhaps the market longevity<br />
of a particular type of device? Maybe legacy<br />
just means any standalone system that<br />
doesn't fit neatly into a cloud, converged or<br />
software-defined world? Perhaps anything<br />
without flash is just old-hat? And how would<br />
we begin to layer the terms meaningfully<br />
upon the real world, given how mixed,<br />
muddled, and granularly-constructed most<br />
data centre, private or public storage<br />
ecosystems are?<br />
The truth is that neither of these distinctions<br />
are the crux of the issue. The distinction<br />
between legacy and emerging storage is not<br />
a given media or a particular system. The<br />
difference is not a particular physical<br />
storage thing, but is about an overall<br />
approach to data.<br />
At the risk of being obvious, storage is part<br />
of infrastructure, which in turn is part of an<br />
overall system, which in turn is designed to<br />
get stuff done. Stuff in this case means, of<br />
course, to provide the data to run<br />
applications, which in turn supports<br />
organisations and their objectives. Stuff<br />
matters. Indeed, the magic and value of<br />
what IT can do is increasingly obvious<br />
across our entire lives. But IT carries this<br />
out, increasingly, out of view, and perhaps<br />
that is how it should be. People and<br />
businesses used to be focused on, and often<br />
consumed by, the minutiae of how IT<br />
outcomes get delivered; these days, we just<br />
want the outcomes.<br />
This is categorically not to say that the<br />
emerging storage approach matters less<br />
than the legacy storage systems did - in<br />
fact it's probably the exact opposite. This<br />
is because achieving the kind of<br />
integrated, automated, app-aware and<br />
self-optimising storage (we really should<br />
start saying data) ecosystem we want, will<br />
demand exceedingly sophisticated<br />
engineering and support.<br />
Whereas the legacy storage arena proudly<br />
paraded its speeds-and-feeds, with new<br />
hardware releases as the cause for<br />
celebration and specialised tools and<br />
people to tweak all the literal and figurative<br />
knobs, the emerging data approach<br />
automatically subsumes whatever hardware<br />
it is given and dynamically and optimally<br />
orchestrates the resources across any given<br />
set of workloads. Moreover, the emerging<br />
approach invariably also wraps in analytics<br />
and security, and these are integral to the<br />
data system, and not applications layered<br />
onto heterogeneous storage systems as an<br />
afterthought.<br />
There's one last important point to make.<br />
The term emerging should not be interpreted<br />
as suggesting that all these new and<br />
desirable storage/data abilities for<br />
contemporary IT are only nascent or<br />
imminent. You can do this today. The term<br />
emerging is simply pointing out that<br />
adoption is only just beginning. The<br />
potential rewards for doing so are significant<br />
in terms of ease, efficiency, TCO, and<br />
security, and as with so much in IT, all it<br />
requires - and we know this is nothing like<br />
as easy to do as it is to write - is to figure out<br />
and focus on what you need to achieve.<br />
Moving from legacy to emerging requires<br />
you to stop thinking of storage as a list of<br />
disparate needs and items, and to start<br />
thinking instead of data, holistically. NC<br />
26 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
OPINION<br />
TRANSPARENT I.T.<br />
ENTERPRISES ARE STRUGGLING<br />
TO ADAPT TO DIGITAL WORLD<br />
DYNAMICS. IN AN EVOLVING<br />
ROLE, IT LEADERS MUST<br />
DEMONSTRATE VALUE AND<br />
PROVIDE COST TRANSPARENCY,<br />
EXPLAINS JAMES COCKROFT,<br />
DIRECTOR AT COEUS<br />
CONSULTING<br />
Once upon a time, IT existed to<br />
simply provision robust and<br />
reliable computing resources to the<br />
business. Today, information technology<br />
represents the heart of the enterprise. That's<br />
quite a change.<br />
The process of bringing the IT department's<br />
capabilities to the forefront of the enterprise<br />
requires IT to deliver value to the<br />
organisation, and IT leaders now find<br />
themselves under mounting pressure, not<br />
simply to justify their costs, but to<br />
demonstrate that they are actively<br />
contributing towards business growth. Yet IT<br />
departments are not as efficient at enabling<br />
transformation in the enterprise as they may<br />
believe; rarely do they adapt internal<br />
processes so that they can report<br />
transparently on the IT cost and benefit.<br />
FRONT OF MIND COSTS<br />
If IT is to take a leading role then cost<br />
transparency must be at the forefront of the<br />
CIO's mind, as it forms the very foundations<br />
of the department's relationship with the rest<br />
of the organisation. If the business can't<br />
understand what value IT is contributing,<br />
then there is no way of evaluating how it can<br />
inform business decisions.<br />
In a recent survey we carried out, this very<br />
point was highlighted by separating<br />
enterprises that are fully cost transparent<br />
from those that are partially or not cost<br />
transparent. The report found that these cost<br />
transparency leaders are far more likely to<br />
be trusted by the board as true partners. This<br />
leading group represents just 12 per cent of<br />
respondents, indicating that the<br />
overwhelming majority of IT departments<br />
have some way to go before they are fully<br />
cost transparent.<br />
But why does cost transparency matter?<br />
When compared to their less transparent<br />
counterparts, cost transparency leaders are<br />
twice as likely to be represented at board<br />
level and much more likely to link the<br />
performance of the IT operations and its<br />
employees to recognisable, measureable<br />
and genuine business outcomess.<br />
BOARD IT<br />
So what steps can IT take to win the trust of<br />
the board and provide their departments<br />
with the agility required to succeed in the<br />
digital age? The first step to ensuring<br />
transparency across IT is to align the<br />
department's objectives with those of the<br />
wider business. From the outset, there should<br />
be a clear case for cost transparency which<br />
lays out what exactly needs to be<br />
documented, for example, improved cost<br />
information, benchmarking or improved<br />
pricing. The next step is to prioritise where to<br />
focus first, as cost transparency cannot be<br />
achieved overnight. Should it be<br />
infrastructure, specific projects, or perhaps<br />
business-critical applications? Again, the<br />
priorities should be formulated to align<br />
and support the business' overarching<br />
strategic goals.<br />
A NEW APPROACH<br />
Another consideration for IT leaders<br />
embarking on the cost transparency journey<br />
is to address the structure of their data and<br />
the way that costs flow through the<br />
organisation. Exploiting cost transparency<br />
needs new processes, new behaviours, and<br />
a significant amount of communications and<br />
training. There may even need to be new<br />
roles and capabilities within the<br />
organisation. And with Brexit and GDPR<br />
around the corner, this is an opportune<br />
moment to address these points.<br />
If IT is able to explain its value to the<br />
business, it is more likely to be regarded as<br />
a trusted partner by the rest of the business.<br />
Cost transparency frames discussions<br />
around service, performance and risk. It also<br />
provides the justification for further<br />
investment in IT services. It is therefore a<br />
critical step to building a trusting partnership<br />
within the business. Those organisations that<br />
have built cost transparency are better able<br />
to demonstrate full value to the business,<br />
and this in turn enables the partnership to<br />
develop, with IT viewed increasingly as an<br />
integral part of the business. NC<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 27
AWARDS2018<br />
SPONSORED BY<br />
A BIG NIGHT FOR NETWORKING<br />
THE 2018 NETWORK COMPUTING AWARDS WINNERS ARE HERE!<br />
The Network Computing Awards ceremony took place in London on 22nd Match. Former<br />
cricketer, Graham Cowdrey, was Master of ceremonies for the night. He was assisted in<br />
presenting the Awards by comedian Patrick Monahan as well as Ray Smyth and Dave<br />
Bonner of Network Computing. All the of results can be seen in the following pages along with<br />
information on the winning product, company, project or individual. Please note, the awardwinning<br />
products will not necessarily be the only solutions or the newest solutions available from<br />
the respective vendors. We recommend that you contact these vendors to learn more.<br />
NETWORK INFRASTRUCTURE PRODUCT OF THE YEAR<br />
WINNER: Dell EMC - N4000 Series<br />
RUNNER UP: Allied Telesis - Secure Enterprise SDN (SES)<br />
The N4000 switch series offers a power-efficient and resilient 10 Gigabit Ethernet (10GbE)<br />
switching solution with support for 40GbE uplinks for advanced Layer 3 distribution for offices<br />
and campus networks.<br />
The N4000 switch series has high-performance capabilities and wire-speed performance<br />
utilizing a non-blocking architecture to easily handle unexpected traffic loads. The N4000 series<br />
includes dual internal hot-swappable 80PLUS-certified power supplies for high availability and<br />
power efficiency. The switches offer simple management and scalability via flexible user port<br />
stacking at 10Gbps or 40Gbps.<br />
28 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
AWARDS2018<br />
DATA CENTRE PRODUCT OF THE YEAR<br />
WINNER: Sudlows - A:LIST<br />
With the increasing reliance on data centre systems to support day to day businesses, Sudlows<br />
knows the importance of the design and build of reliable, resilient and efficient data centres.<br />
The latest offering from Sudlows' Data Centre Testing and Commissioning Team is the<br />
Advanced Load Integrated Systems Test, known as 'A:LIST'.<br />
Designed specifically for testing critical data environments by replicating the power and<br />
heatloads which will be installed, the A:LIST can provide a detailed analysis of your facility. The<br />
multi-award winning A:LIST has the ability to match the planned load closely, providing data<br />
centre operators the peace of mind that their data centres are running efficiently and<br />
effectively.<br />
RUNNER UP: Allied Telesis - X550 10 gig switch<br />
IT OPTIMISATION PRODUCT OF THE YEAR<br />
WINNER: KEMP Technologies - KEMP 360 Central<br />
KEMP 360 Central provides centralised management and control of application delivery assets,<br />
enabling reduced operational overheads and improved application uptime. From a single<br />
interface, KEMP 360 Central provides application owners and network managers with a unified<br />
view of the status and performance of their application delivery infrastructure, enabling rapid<br />
detection of issues and reduced management effort. A single KEMP 360 Central instance can<br />
manage multiple ADC instances across multiple environments including on-premises and cloud.<br />
With support for third party ADCs and integrated cloud load balancers, KEMP 360 Central is<br />
invaluable in hybrid cloud or cloud migration scenarios.<br />
RUNNER UP: F5 Networks - BIG-IP Local Traffic Manager<br />
TESTING / MONITORING PRODUCT OF THE YEAR<br />
WINNER: Netreo - OmniCenter<br />
Netreo's OmniCenter provides single-pane-of-glass dashboard views into the entire IT enterprise.<br />
Infrastructure, telephony, applications, email, virtualisation and cloud services - all on one<br />
beautifully crafted screen, along with powerful incident management functions and automated<br />
reporting. OmniCenter is appliance-based (hardware, virtual or cloud-based) with no clients,<br />
agents, or probes - so implementation is a breeze. We use a simple, consumption-based<br />
subscription model in which all modules, functionality, and support are embedded into one low<br />
fee. No surprises. No terms. No hassles. We make enterprise-class monitoring tools available in<br />
a way that no one else can compete with.<br />
RUNNER UP: iTrinegy - NE ONE Desktop Network Emulator<br />
CLOUD TELEPHONY PRODUCT OF THE YEAR<br />
WINNER: Natterbox - AVS<br />
Natterbox delivers a global Cloud Telephony Platform. Unique as the world's first and only end<br />
to end telephony service to be 100% embedded and managed within the Salesforce platform.<br />
Natterbox empowers businesses to use live CRM data to deliver concise personalised, phone<br />
journeys, with high call quality, around the globe. Natterbox is fully downloadable through the<br />
Salesforce AppExchange including a Cloud PBX, Contact Centre and call recording, offering a<br />
true no hardware, no software cloud based solution.<br />
With Natterbox you can increase efficiency, improve productivity and enhance your overall<br />
customer experience. It's time to prioritise your phone!<br />
www.Natterbox.com.<br />
RUNNER UP: Cisco - Cisco Unified Communications Manager<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 29
AWARDS2018<br />
CRM PRODUCT OF THE YEAR<br />
WINNER: webCRM - webCRM<br />
RUNNER UP: Smarty Software - Smarty CRM<br />
WebCRM is a cloud based, sophisticated CRM system for Small to Medium Enterprises, that is<br />
relatively quick to implement and straightforward to evolve. The system enables managers and<br />
users to more effectively manage leads and activities, opportunities and quotes, orders and a<br />
ticketing system for customer service. The marketing module provides detailed profiling on any<br />
aspect of the system information facilitating highly targeted email marketing. These processes<br />
are supported with an easy to use reporting and dashboard system.<br />
WebCRM can be integrated with a large number of popular systems including Office 365,<br />
Sage, Xero and QuickBooks plus most telephony systems.<br />
STORAGE PRODUCT OF THE YEAR<br />
WINNER: Buffalo EU B.V. - TeraStation TS51210RH<br />
RUNNER UP: Lenovo - Storage DX8200D<br />
BUFFALO's TeraStation 51210RH is a high performance 12-bay network storage solution ideal<br />
for businesses requiring a reliable RAID-based network storage solution for business critical<br />
applications. Increased speed and reliability is achieved with a 10GbE connection and enterprise<br />
class hard drives.<br />
With the powerful Annapurna Labs Alpine AL314 1.7Ghz Quad-Core processor and 8GB of<br />
fast DDR3 ECC memory, TeraStation 51210RH provides exceptional performance during file<br />
transfers and everyday NAS functions. It is available partially-populated with 8 or 16 TB, and<br />
fully-populated with 24, 48 or 96 TB. Partially populated models are ideal for users needing a<br />
small start with less initial investment.<br />
SECURITY PRODUCT OF THE YEAR<br />
WINNER: Rohde and Schwarz CyberSecurity - TrustedGate<br />
RUNNER UP: Arbor Networks - Arbor Cloud<br />
The cloud security solution TrustedGate enables companies to work securely in cloud computing<br />
environments (e.g. Google Drive, Magenta, Box.com) and collaboration tools such as SharePoint<br />
and Office 365. It combines encryption, virtualisation and fragmentation of sensitive documents<br />
for maximum protection of critical information. Users are able to distribute data on multiple<br />
clouds and servers in order to manage governance, risk management and compliance demands<br />
that require data to be protected according to the current state of the art or saved in a given<br />
region (e.g. GDPR). Document-centric encryption and role-based access control ensure that data<br />
is shielded against cyberattacks.<br />
NETWORK MANAGEMENT PRODUCT OF THE YEAR<br />
WINNER: SolarWinds - NPM<br />
RUNNER UP: Allied Telesis - Vista Manager EX<br />
SolarWinds Network Performance Monitor (NPM) is a powerful and affordable network<br />
monitoring software that enables you to quickly detect, diagnose, and resolve network<br />
performance problems and outages.<br />
SolarWinds develops its network management software upon the Orion Platform, which is<br />
highly scalable and unifies data from multiple parts of the stack into an application-centric<br />
view. This powerful platform gives IT departments the flexibility to add modules as their needs<br />
grow, deepening visibility into their environments. It can monitor, visualise, and analyse the<br />
performance of networks, applications, systems, storage, and databases.<br />
30 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
AWARDS2018<br />
SD-WAN VENDOR OF THE YEAR<br />
WINNER: Citrix<br />
Citrix aims to power a world where people, organisations and things are securely connected and<br />
accessible to make the extraordinary possible. We help customers reimagine the future of work by<br />
providing the most comprehensive secure digital workspace that unifies the apps, data and<br />
services people need to be productive, and simplifies IT's ability to adopt and manage complex<br />
cloud environments. Citrix solutions are in use by more than 400,000 organisations including 99<br />
percent of the Fortune 100 and 98 percent of the Fortune 500.<br />
RUNNER UP: Silver Peak<br />
HARDWARE PRODUCT OF THE YEAR<br />
WINNER: Opengear - IM7200<br />
The IM7200 streamlines remote management of network, server and power infrastructure in<br />
data centre and remote environments, ensuring business continuity, secure and reliable access.<br />
Available in range of models offering between 8 and 48 ports, the next generation IM7200<br />
combines Smart OOB out-of-band management with Failover to Cellular and delivers<br />
proactive monitoring and remediation.<br />
RUNNER UP: WatchGuard - Firebox M5600<br />
SOFTWARE PRODUCT OF THE YEAR<br />
WINNER: Natterbox - AVS RUNNER UP: Rohde & Schwarz Cybersecurity - R&S PACE 2<br />
Natterbox AVS offers the complete telephony solution, including Cloud PBX, CTI, Contact Centre<br />
and Call Recording within Salesforce. It enables transparency, flexibility and support, without<br />
needing to escalate to third party telephony suppliers. Natterbox is available worldwide; serviced<br />
by our 8 global data centres, providing quality of service, reliability and reduced complexity.<br />
You can either replace your existing phone system, with one that is 100% embedded in<br />
Salesforce. Or alternatively, integrate and enhance your existing phone system with our OTT<br />
solution, benefitting from the full contact centre integration.<br />
Accelerate productivity, transform customer experience and improve your data integrity - all<br />
within Salesforce.<br />
BENCH TESTED PRODUCT OF THE YEAR<br />
WINNER: NetScout - LinkRunner G2 NetScout – AirCheck G2 RUNNER UP: SolarWinds - NPM 12.1<br />
"We're honoured to have not one but two products distinguished by such an esteemed industry<br />
leader," commented Stefan Pracht, General Manager for Handheld Network Tools, NETSCOUT.<br />
"Both products dramatically improve efficiencies for IT professionals, and we're thrilled that the<br />
benefits they bring have been recognised at this high level."<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 31
AWARDS2018<br />
NETWORK PROJECT OF YEAR<br />
WINNER: Nuffield Health / Silver Peak<br />
- PUBLIC / NOT FOR PROFIT SECTOR<br />
Nuffield Health, a leading not-for-profit healthcare organisation, chose Silver Peak to transition<br />
its legacy MPLS networks to an SD-WAN and embark upon a cloud-first IT strategy. Since the<br />
deployment, Nuffield Health has reduced WAN traffic by up to 75 percent and realised a 4-6x<br />
increase in available bandwidth, enabling its users to use data-critical applications for patient<br />
care and customer needs<br />
NETWORK PROJECT OF THE YEAR - PRIVATE SECTOR<br />
WINNER: iMarket / iTrinegy<br />
iMarket Communications specialises in VoIP TDM over Ethernet trader voice and data solutions<br />
for the financial, banking and energy industries. When a client purchases an iMarket Private Line,<br />
iMarket assumes full responsibility for buying the required links from the carrier.<br />
To minimise its risk, iMarket selected iTrinegy's NE-ONE network emulator to verify, prior to<br />
signing any contract, that its equipment was going to work properly and not be adversely<br />
impacted by any latency or jitter. Testing with NE-ONE confirmed that its devices were well able<br />
to perform in such environments. Since then, the NE-ONE has been used to identify the<br />
tolerance limits of iMarket's systems.<br />
THE RETURN ON INVESTMENT AWARD<br />
WINNER: VoiceSage - Interactive Voice Messaging<br />
RUNNER UP: Natterbox - AVS<br />
VoiceSage is delighted to announce it has won the title of 'Return On Investment' - a win that<br />
marks an unprecedented sixth year of success at the Awards. The fact that VoiceSage's solutions<br />
allow brands to deliver a consistent and rich customer experience and realise tangible business<br />
improvements is believed to be the main factor behind the win.<br />
"Our win this year is especially important to us, as proven customer ROI is testament to the<br />
contribution our solution makes to enabling brands to proactively engage with customers in<br />
ways that are simple, immediate, and offer great choice across channels," commented CEO<br />
James J Kett.<br />
THE CUSTOMER SERVICE AWARD<br />
WINNER: Brookcourt Solutions<br />
RUNNER UP: NBM Technology Solutions<br />
Commenting on thei win, Brookcourt CEO Phil Higgins said "As a true testament of customer<br />
service and value to our clients, Brookcourt are delighted to have won The Customer Service<br />
Award of the Year 2018. Great achievements are nurtured with the cooperation of many<br />
minds with a common vision working toward a common goal. Brookcourt's award winning,<br />
customer centric approach ensures we continuously keep ahead, we are honoured to have<br />
won this award."<br />
32 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
AWARDS2018<br />
NEW PRODUCT OF THE YEAR – HARDWARE CATEGORY<br />
WINNER: Allied Telesis - SwitchBlade x908 Generation 2<br />
The Allied Telesis SBx908 GEN2 is the ideal solution for the modern enterprise network core. This<br />
stackable modular switch also has the capacity to support Smart City and IoT networks. The<br />
SBx908 GEN2 delivers a future-proof network with superior flexibility, coupled with the ability to<br />
stack multiple units.<br />
The high-capacity 2.6 Terabit fabric eliminates bottlenecks, effortlessly streams video and<br />
ensures all traffic in large networks is delivered reliably. Flexible hot-swappable expansion<br />
modules (XEMs) support 10 Gigabit, 40 Gigabitand 100 Gigabit in the future to easily expand<br />
the SBx908 GEN2 to meet network traffic demands, both now and well into the future.<br />
RUNNER UP: Dell EMC - PowerEdge T640<br />
NEW PRODUCT OF THE YEAR – SOFTWARE AND SERVICES CATEGORY<br />
WINNER: Check Point Software Technologies – Check Point Infinity<br />
Check Point Infinity is the first consolidated security across networks, cloud and mobile, providing<br />
the highest level of threat prevention against both known and unknown targeted attacks to keep<br />
you protected now and in the future. Infinity leverages unified threat intelligence and open<br />
interfaces, enabling all environments to stay protected against targeted attacks.<br />
By focusing on prevention rather than detection only, Infinity blocks the most sophisticated<br />
attacks before they occur. Check Point Infinity architecture consolidates management of multiple<br />
security layers, providing superior policy efficiency and enabling to manage security through a<br />
single pane of glass.<br />
RUNNER UP: Natterbox - AVS<br />
THE INSPIRATION AWARD<br />
WINNER: Andy Hirst IEng, MIET, CDCDP, ATD - Technical Director, Sudlows<br />
Andy Hirst IEng, MIET, CDCDP, ATD - Technical Director, Sudlows<br />
With over 25 years' design and management experience in the electrical industry, Andy has been<br />
instrumental in leading the transformation of Sudlows from a £2million data cabling company to<br />
an award winning £48million critical infrastructure provider. Andy is often in demand by both<br />
press and industry conferences to offer his opinion and views on Key critical infrastructure topics.<br />
After initially joining Sudlows to relaunch the electrical division, Andy become a Board Director<br />
and works closely with his fellow directors to define the growth strategy and commercial direction<br />
of the business. Andy's critical contribution has ensured that strategic growth is planned and<br />
controlled with significant investment in sourcing a high standard of engineers and designers in<br />
all disciplines around the data centre environment. Andy is a key figure within the critical<br />
infrastructure industry and has collected several awards for his technical work.<br />
RUNNER UP: Ian Moyse<br />
THE "ONE TO WATCH" COMPANY<br />
WINNER: Endace<br />
Endace provides high performance platforms for network performance and security analytics<br />
tools, providing agile functionality whilst saving both capex and opex and meeting the business<br />
need for long hardware depreciation cycles.<br />
The Endace Fusion Programme brings together best of breed functionality to ensure that<br />
analysts always have access to the tools they need in an ever-changing network and security<br />
landscape. The scalability and interoperability of EndaceProbes simplify incident response<br />
workflows, ensuring that problems are solved quickly and conclusively, the first time they occur.<br />
RUNNER UP: Algosec<br />
WWW.NETWORKCOMPUTING.CO.UK @NCMagAndAwards<br />
MARCH/APRIL 2018 NETWORKcomputing 33
AWARDS2018<br />
DISTRIBUTOR OF THE YEAR<br />
WINNER: Nuvias<br />
RUNNER UP: NBM Distribution<br />
Nuvias is a fast-growing high value, solutions-defined EMEA distributor with a portfolio covering<br />
a comprehensive range of IT solutions. The focus is currently on three areas - Cyber Security<br />
(based on the former Wick Hill); Advanced Networking (based on the former Zycko) and Unified<br />
Communications (based on the former SIPHON). In July 2017, Nuvias added Benelux value<br />
added distributor and security specialist DCB to the Group. All four award-winning companies<br />
had previously demonstrated their ability to provide innovative technology solutions from worldclass<br />
vendors, and deliver market growth for vendor partners and customers.<br />
RESELLER OF THE YEAR<br />
WINNER: Q Associates<br />
RUNNER UP: Brookcourt Solutions<br />
As an award-winning platform, data and services specialist, Q Associates are helping<br />
organisations across the commercial and public-sector drive innovation and leverage the best<br />
services and technologies. including:<br />
Expert IT consultation and advisory services<br />
Converged, hyper-converged and cloud-based solutions<br />
Data protection, compliance and information security<br />
Our people make us different. Our technical experts are there to remove your IT complexity,<br />
enable digital transformation and help you meet the changing demands of your business through<br />
a number of IT solutions.<br />
PRODUCT OF THE YEAR<br />
WINNER: Silver Peak - Unity EdgeConnect<br />
RUNNER UP: Netreo - OmniCenter<br />
Silver Peak’s Unity EdgeConnect SD-WAN solution<br />
Delivered in both virtual and physical appliances, the Silver Peak Unity EdgeConnect softwaredefined<br />
WAN (SD-WAN) solution dramatically reduces the cost and complexity of building a<br />
WAN by providing the flexibility to use any combination of transport technologies – including<br />
broadband – to connect users to applications. EdgeConnect is the industry's leading SD-WAN<br />
solution that frees businesses from their dependency on routers. In addition, EdgeConnect is<br />
application-driven, so it automatically learns and adapts to constantly changing network<br />
conditions. Fully compatible with existing WAN infrastructure, EdgeConnect provides a graceful<br />
migration to an SD-WAN and, ultimately, to the thin branch by simplifying the WAN architecture.<br />
COMPANY OF THE YEAR<br />
WINNER: Nuvias<br />
RUNNER UP: Brookcourt Solutions<br />
Nuvias Group is the pan-EMEA, high value distribution business, which is redefining<br />
international, specialist distribution in IT. The company has created a platform to deliver a<br />
consistent, high value, service-led and solution-rich proposition across EMEA. This allows partner<br />
and vendor communities to provide exceptional business support to customers and enables new<br />
standards of channel success. Nuvias currently has three main practice areas - cyber security,<br />
advanced networking and unified communications. Nuvias has 21 regional offices across EMEA,<br />
as well as serving additional countries through those offices. Turnover is around US$ 500 million.<br />
34 NETWORKcomputing MARCH/APRIL 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
EUROPE’S LARGEST UNIFIED COMMUNICATIONS AND COLLABORATION EVENT<br />
SMARTER COLLABORATION<br />
16 -17 May 2018, ExCeL London<br />
COLLABORATION CLOUD NETWORKS A.I.<br />
SECURITY CUSTOMER<br />
CONTACT<br />
Seamless Communications<br />
Flexible working<br />
True mobility<br />
Easy collaboration<br />
Increased workforce productivity<br />
Smarter collaboration<br />
Register FREE today and save £35<br />
*Visitors not registered by 7pm on Tuesday 15th May 2018 will be charged a fee of £35.<br />
Find out more at www.ucexpo.co.uk<br />
2017<br />
SPONSORS: