enlisted distribution and assignment system (edas) - Soldier Support ...
enlisted distribution and assignment system (edas) - Soldier Support ...
enlisted distribution and assignment system (edas) - Soldier Support ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
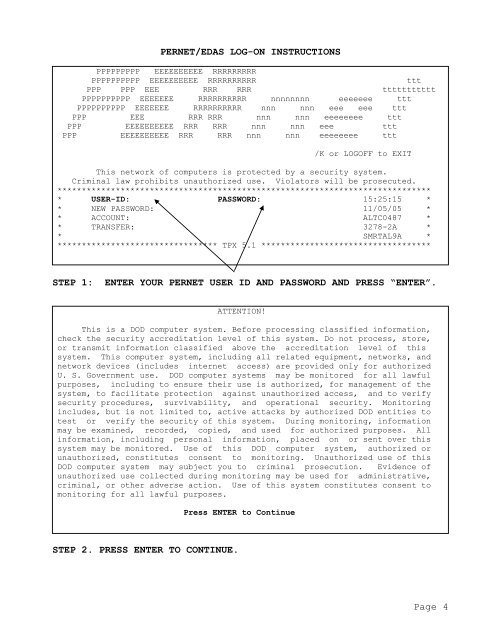
PERNET/EDAS LOG-ON INSTRUCTIONS<br />
PPPPPPPPP EEEEEEEEEE RRRRRRRRR<br />
PPPPPPPPPP EEEEEEEEEE RRRRRRRRRR ttt<br />
PPP PPP EEE RRR RRR ttttttttttt<br />
PPPPPPPPPP EEEEEEE RRRRRRRRRR nnnnnnnn eeeeeee ttt<br />
PPPPPPPPPP EEEEEEE RRRRRRRRRR nnn nnn eee eee ttt<br />
PPP EEE RRR RRR nnn nnn eeeeeeee ttt<br />
PPP EEEEEEEEEE RRR RRR nnn nnn eee ttt<br />
PPP EEEEEEEEEE RRR RRR nnn nnn eeeeeeee ttt<br />
/K or LOGOFF to EXIT<br />
This network of computers is protected by a security <strong>system</strong>.<br />
Criminal law prohibits unauthorized use. Violators will be prosecuted.<br />
*****************************************************************************<br />
* USER-ID: PASSWORD: 15:25:15 *<br />
* NEW PASSWORD: 11/05/05 *<br />
* ACCOUNT: ALTC0487 *<br />
* TRANSFER: 3278-2A *<br />
* SMRTAL9A *<br />
********************************* TPX 5.1 ***********************************<br />
STEP 1: ENTER YOUR PERNET USER ID AND PASSWORD AND PRESS “ENTER”.<br />
ATTENTION!<br />
This is a DOD computer <strong>system</strong>. Before processing classified information,<br />
check the security accreditation level of this <strong>system</strong>. Do not process, store,<br />
or transmit information classified above the accreditation level of this<br />
<strong>system</strong>. This computer <strong>system</strong>, including all related equipment, networks, <strong>and</strong><br />
network devices (includes internet access) are provided only for authorized<br />
U. S. Government use. DOD computer <strong>system</strong>s may be monitored for all lawful<br />
purposes, including to ensure their use is authorized, for management of the<br />
<strong>system</strong>, to facilitate protection against unauthorized access, <strong>and</strong> to verify<br />
security procedures, survivability, <strong>and</strong> operational security. Monitoring<br />
includes, but is not limited to, active attacks by authorized DOD entities to<br />
test or verify the security of this <strong>system</strong>. During monitoring, information<br />
may be examined, recorded, copied, <strong>and</strong> used for authorized purposes. All<br />
information, including personal information, placed on or sent over this<br />
<strong>system</strong> may be monitored. Use of this DOD computer <strong>system</strong>, authorized or<br />
unauthorized, constitutes consent to monitoring. Unauthorized use of this<br />
DOD computer <strong>system</strong> may subject you to criminal prosecution. Evidence of<br />
unauthorized use collected during monitoring may be used for administrative,<br />
criminal, or other adverse action. Use of this <strong>system</strong> constitutes consent to<br />
monitoring for all lawful purposes.<br />
Press ENTER to Continue<br />
STEP 2. PRESS ENTER TO CONTINUE.<br />
Page 4