Viber Communication Security - Bad Request
Viber Communication Security - Bad Request
Viber Communication Security - Bad Request
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Experiments Chapter 3<br />
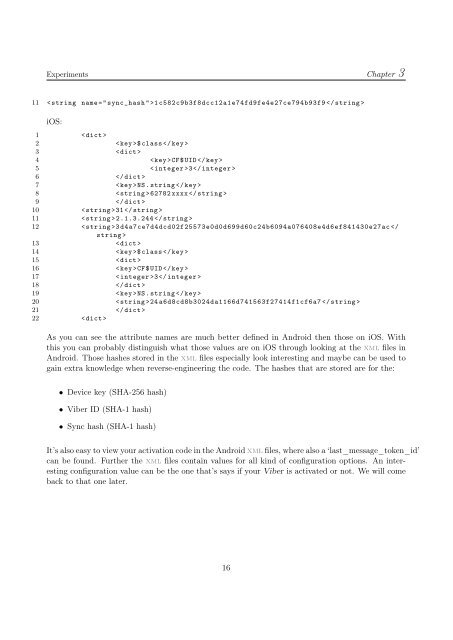
11 < string name =" sync_hash ">1 c582c9b3f8dcc12a1e74fd9fe4e27ce794b93f9 <br />
iOS:<br />
1 <br />
2 $ class <br />
3 <br />
4 CF$UID <br />
5 < integer >3<br />
6 <br />
7 NS. string <br />
8 < string >62782 xxxx <br />
9 <br />
10 < string >31 <br />
11 < string > 2.1.3.244 <br />
12 < string >3 d4a7ce7d4dcd02f25573e0d0d699d60c24b6094a076408e4d6ef841430e27ac <br />
13 <br />
14 $ class <br />
15 <br />
16 CF$UID <br />
17 < integer >3<br />
18 <br />
19 NS. string <br />
20 < string >24 a6d8cd8b3024da1166d741563f27414f1cf6a7 <br />
21 <br />
22 <br />
As you can see the attribute names are much better defined in Android then those on iOS. With<br />
this you can probably distinguish what those values are on iOS through looking at the xml files in<br />
Android. Those hashes stored in the xml files especially look interesting and maybe can be used to<br />
gain extra knowledge when reverse-engineering the code. The hashes that are stored are for the:<br />
• Device key (SHA-256 hash)<br />
• <strong>Viber</strong> ID (SHA-1 hash)<br />
• Sync hash (SHA-1 hash)<br />
It’s also easy to view your activation code in the Android xml files, where also a ‘last_message_token_id’<br />
can be found. Further the xml files contain values for all kind of configuration options. An interesting<br />
configuration value can be the one that’s says if your <strong>Viber</strong> is activated or not. We will come<br />
back to that one later.<br />
16