Viber Communication Security - Bad Request
Viber Communication Security - Bad Request
Viber Communication Security - Bad Request
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Experiments Chapter 3<br />
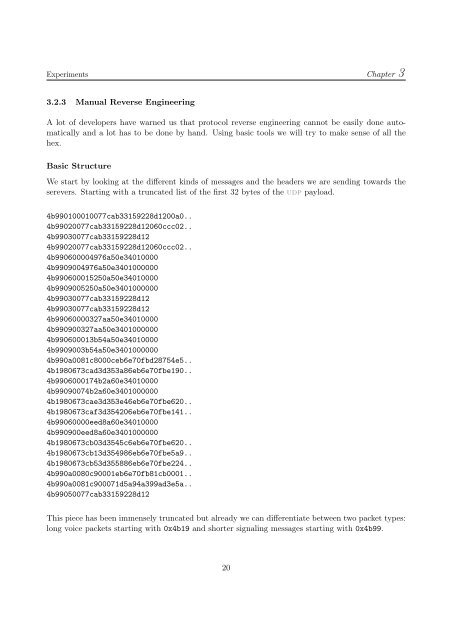
3.2.3 Manual Reverse Engineering<br />
A lot of developers have warned us that protocol reverse engineering cannot be easily done automatically<br />
and a lot has to be done by hand. Using basic tools we will try to make sense of all the<br />
hex.<br />
Basic Structure<br />
We start by looking at the different kinds of messages and the headers we are sending towards the<br />
serevers. Starting with a truncated list of the first 32 bytes of the udp payload.<br />
4b990100010077cab33159228d1200a0..<br />
4b99020077cab33159228d12060ccc02..<br />
4b99030077cab33159228d12<br />
4b99020077cab33159228d12060ccc02..<br />
4b990600004976a50e34010000<br />
4b9909004976a50e3401000000<br />
4b990600015250a50e34010000<br />
4b9909005250a50e3401000000<br />
4b99030077cab33159228d12<br />
4b99030077cab33159228d12<br />
4b99060000327aa50e34010000<br />
4b990900327aa50e3401000000<br />
4b990600013b54a50e34010000<br />
4b9909003b54a50e3401000000<br />
4b990a0081c8000ceb6e70fbd28754e5..<br />
4b1980673cad3d353a86eb6e70fbe190..<br />
4b9906000174b2a60e34010000<br />
4b99090074b2a60e3401000000<br />
4b1980673cae3d353e46eb6e70fbe620..<br />
4b1980673caf3d354206eb6e70fbe141..<br />
4b99060000eed8a60e34010000<br />
4b990900eed8a60e3401000000<br />
4b1980673cb03d3545c6eb6e70fbe620..<br />
4b1980673cb13d354986eb6e70fbe5a9..<br />
4b1980673cb53d355886eb6e70fbe224..<br />
4b990a0080c90001eb6e70fb81cb0001..<br />
4b990a0081c900071d5a94a399ad3e5a..<br />
4b99050077cab33159228d12<br />
This piece has been immensely truncated but already we can differentiate between two packet types:<br />
long voice packets starting with 0x4b19 and shorter signaling messages starting with 0x4b99.<br />
20