CDM-CYBER-DEFENSE-eMAGAZINE-March-2019
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
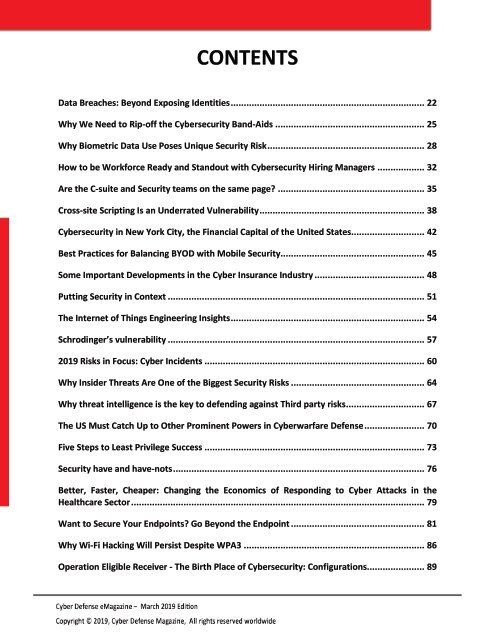
CONTENTS<br />
Data Breaches: Beyond Exposing Identities .......................................................................... 22<br />
Why We Need to Rip-off the Cybersecurity Band-Aids ......................................................... 25<br />
Why Biometric Data Use Poses Unique Security Risk ............................................................ 28<br />
How to be Workforce Ready and Standout with Cybersecurity Hiring Managers .................. 32<br />
Are the C-suite and Security teams on the same page? ........................................................ 35<br />
Cross-site Scripting Is an Underrated Vulnerability ............................................................... 38<br />
Cybersecurity in New York City, the Financial Capital of the United States ............................ 42<br />
Best Practices for Balancing BYOD with Mobile Security ....................................................... 45<br />
Some Important Developments in the Cyber Insurance Industry .......................................... 48<br />
Putting Security in Context .................................................................................................. 51<br />
The Internet of Things Engineering Insights .......................................................................... 54<br />
Schrodinger’s vulnerability .................................................................................................. 57<br />
<strong>2019</strong> Risks in Focus: Cyber Incidents .................................................................................... 60<br />
Why Insider Threats Are One of the Biggest Security Risks ................................................... 64<br />
Why threat intelligence is the key to defending against Third party risks .............................. 67<br />
The US Must Catch Up to Other Prominent Powers in Cyberwarfare Defense ....................... 70<br />
Five Steps to Least Privilege Success .................................................................................... 73<br />
Security have and have-nots ................................................................................................ 76<br />
Better, Faster, Cheaper: Changing the Economics of Responding to Cyber Attacks in the<br />
Healthcare Sector ................................................................................................................ 79<br />
Want to Secure Your Endpoints? Go Beyond the Endpoint ................................................... 81<br />
Why Wi-Fi Hacking Will Persist Despite WPA3 ..................................................................... 86<br />
Operation Eligible Receiver - The Birth Place of Cybersecurity: Configurations ...................... 89