Cyber Defense eMagazine August 2019
Cyber Defense eMagazine August Edition for 2019 #CDM #CYBERDEFENSEMAG @CyberDefenseMag by @Miliefsky a world-renowned cybersecurity expert and the Publisher of Cyber Defense Magazine as part of the Cyber Defense Media Group
Cyber Defense eMagazine August Edition for 2019 #CDM #CYBERDEFENSEMAG @CyberDefenseMag by @Miliefsky a world-renowned cybersecurity expert and the Publisher of Cyber Defense Magazine as part of the Cyber Defense Media Group
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
called ‘<strong>Defense</strong> in Depth’ product lines. However, ‘<strong>Defense</strong> in Depth’ approach is flawed and usually<br />
leads to much higher cost without solving the fundamental requirements of comprehensive cyber security.<br />
So, what is the primary goal of “Comprehensive <strong>Cyber</strong> Security for Digital Era”? It’s a) to protect the<br />
organization from all known and unknown cyber-attacks and b) if an attack happens, to proactively detect<br />
it at an early stage and contain or eliminate the attack to minimize the damage. In short “Stop the Data<br />
Breach from causing any damage to the organization” – whether that damage is legal, financial,<br />
competitive, and/or nation-state based.<br />
Let us look at what are the basic requirements of “Comprehensive <strong>Cyber</strong> Security”. The key requirements<br />
start with comprehensive visibility – if you can’t see the assets, the users, the traffic, and the<br />
vulnerabilities; you can’t protect the organization from attacks originating from them. Basic Security<br />
hygiene is important from protection from most common and known attacks perspective, but it’s not<br />
sufficient. Proactive detection based on behavioral science to detect anomalies has become the need of<br />
the hour. However, most machine learning and behavioral science-based solutions produce lot of false<br />
positives and create an alert fatigue. It’s very important to also have advance correlation engine, which<br />
correlates historical situational context along with machine learning anomalies to reduce the false<br />
positives and accurately find the real attacks rather than getting bogged down by least important issues.<br />
Once the attack is detected, the solution should also provide automated real-time response built in. The<br />
organization cannot rely on human intervention by Security Operations Center (SOC) analyst to analyze<br />
it before responding. The solution should respond automatically and stop the threat. The SOC analyst<br />
can analyze it and adjust later, but the attack needs to be stopped immediately in an automated manner.<br />
Furthermore, this solution and framework has to be continuously adjusted and adapted to changing<br />
posture of the organization in digital era where more content and applications are moving to the cloud<br />
and employees are preferring to work from anywhere, using any smart device to access the organization’s<br />
data which has to be omnipresent.<br />
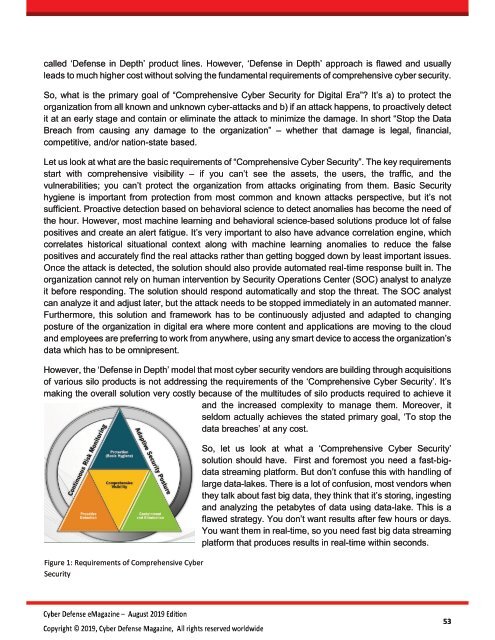
However, the ‘<strong>Defense</strong> in Depth’ model that most cyber security vendors are building through acquisitions<br />
of various silo products is not addressing the requirements of the ‘Comprehensive <strong>Cyber</strong> Security’. It’s<br />
making the overall solution very costly because of the multitudes of silo products required to achieve it<br />
and the increased complexity to manage them. Moreover, it<br />
seldom actually achieves the stated primary goal, ‘To stop the<br />
data breaches’ at any cost.<br />
Figure 1: Requirements of Comprehensive <strong>Cyber</strong><br />
Security<br />
So, let us look at what a ‘Comprehensive <strong>Cyber</strong> Security’<br />
solution should have. First and foremost you need a fast-bigdata<br />
streaming platform. But don’t confuse this with handling of<br />
large data-lakes. There is a lot of confusion, most vendors when<br />
they talk about fast big data, they think that it’s storing, ingesting<br />
and analyzing the petabytes of data using data-lake. This is a<br />
flawed strategy. You don’t want results after few hours or days.<br />
You want them in real-time, so you need fast big data streaming<br />
platform that produces results in real-time within seconds.<br />
53