Cyber Defense eMagazine July 2020 Edition
Cyber Defense eMagazine July Edition for 2020 #CDM #CYBERDEFENSEMAG @CyberDefenseMag by @Miliefsky a world-renowned cyber security expert and the Publisher of Cyber Defense Magazine as part of the Cyber Defense Media Group as well as Yan Ross, US Editor-in-Chief, Pieruligi Paganini, Co-founder & International Editor-in-Chief, Stevin Miliefsky, President and many more writers, partners and supporters who make this an awesome publication! Thank you all and to our readers! OSINT ROCKS! #CDM #CDMG #OSINT #CYBERSECURITY #INFOSEC #BEST #PRACTICES #TIPS #TECHNIQUES
Cyber Defense eMagazine July Edition for 2020 #CDM #CYBERDEFENSEMAG @CyberDefenseMag by @Miliefsky a world-renowned cyber security expert and the Publisher of Cyber Defense Magazine as part of the Cyber Defense Media Group as well as Yan Ross, US Editor-in-Chief, Pieruligi Paganini, Co-founder & International Editor-in-Chief, Stevin Miliefsky, President and many more writers, partners and supporters who make this an awesome publication! Thank you all and to our readers! OSINT ROCKS! #CDM #CDMG #OSINT #CYBERSECURITY #INFOSEC #BEST #PRACTICES #TIPS #TECHNIQUES
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Encode/Decode<br />
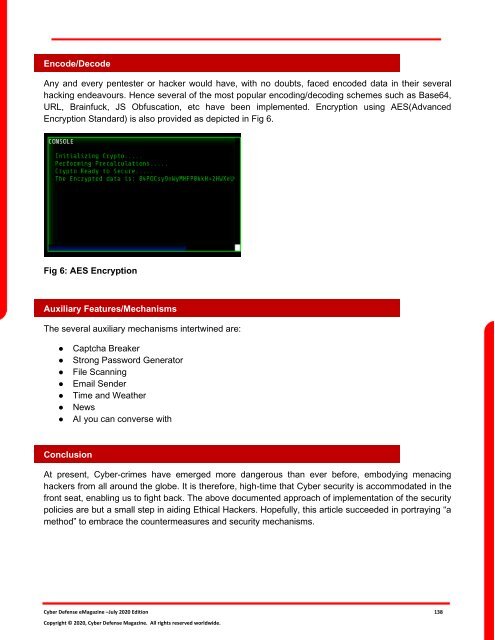
Any and every pentester or hacker would have, with no doubts, faced encoded data in their several<br />
hacking endeavours. Hence several of the most popular encoding/decoding schemes such as Base64,<br />
URL, Brainfuck, JS Obfuscation, etc have been implemented. Encryption using AES(Advanced<br />
Encryption Standard) is also provided as depicted in Fig 6.<br />
Fig 6: AES Encryption<br />
Auxiliary Features/Mechanisms<br />
The several auxiliary mechanisms intertwined are:<br />
●<br />
●<br />
●<br />
●<br />
●<br />
●<br />
●<br />
Captcha Breaker<br />
Strong Password Generator<br />
File Scanning<br />
Email Sender<br />
Time and Weather<br />
News<br />
AI you can converse with<br />
Conclusion<br />
At present, <strong>Cyber</strong>-crimes have emerged more dangerous than ever before, embodying menacing<br />
hackers from all around the globe. It is therefore, high-time that <strong>Cyber</strong> security is accommodated in the<br />
front seat, enabling us to fight back. The above documented approach of implementation of the security<br />
policies are but a small step in aiding Ethical Hackers. Hopefully, this article succeeded in portraying “a<br />
method” to embrace the countermeasures and security mechanisms.<br />
<strong>Cyber</strong> <strong>Defense</strong> <strong>eMagazine</strong> –<strong>July</strong> <strong>2020</strong> <strong>Edition</strong> 138<br />
Copyright © <strong>2020</strong>, <strong>Cyber</strong> <strong>Defense</strong> Magazine. All rights reserved worldwide.