NTCA Conference Program
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>NTCA</strong> 2021 CYBERSECURITY SUMMIT<br />
at a<br />
GLANCE<br />
WEDNESDAY<br />
OCTOBER 13<br />
1:30 p.m.–4:00 p.m.<br />
Preconference Workshops<br />
2:00 p.m.–4:00 p.m.<br />
Cybersecurity: The Real World<br />
Brought to you by CyberESI,<br />
Telcom Insurance Group<br />
and Womble Bond Dickinson<br />
5:00 p.m.–6:00 p.m.<br />
CyberShare Member Reception<br />
THURSDAY<br />
OCTOBER 14<br />
7:00 a.m.–8:00 a.m.<br />
Continental Breakfast<br />
8:00 a.m.–Noon<br />
Opening General Session<br />
8:00 a.m.–9:00 a.m.<br />
The Isle of Tortuga —<br />
but on the Internet<br />
Dan Tentler, Founder and Chief<br />
Technical Officer, Phobos Group<br />
9:00 a.m.–9:45 a.m.<br />
State of Ransomware 2021<br />
9:45 a.m.–10:15 a.m.<br />
Break<br />
10:15 a.m.–11:00 a.m.<br />
Ransomware Incident Response and<br />
Restoration<br />
THURSDAY<br />
OCTOBER 14 CONT.<br />
11:00 a.m.–Noon<br />
Ransomware Cyber Insurance<br />
Noon–1:30 p.m.<br />
Lunch<br />
1:30 p.m.–2:10 p.m.<br />
Breakout Sessions<br />
Level 1: A Beginner’s Guide to<br />
Comprehensive Cybersecurity<br />
Planning<br />
Level 2: Keeping the Cloud<br />
Protected from the Storm<br />
2:20 p.m.–3:00 p.m.<br />
Breakout Sessions<br />
Level 1: Cybersecurity for the<br />
Non-Technical Team Member<br />
Level 2: Making an Effective<br />
Security Operation Center<br />
3:00 p.m.–3:30 p.m.<br />
Break<br />
3:30 p.m.–4:10 p.m.<br />
Breakout Sessions<br />
Level 1: The GM Perspective<br />
on Cybersecurity<br />
Level 2: Implementing Zero<br />
Trust Networking<br />
THURSDAY<br />
OCTOBER 14 CONT.<br />
4:15 p.m.–5:00 p.m.<br />
<strong>NTCA</strong> CyberShare<br />
Networking Discussion<br />
5:15 p.m.–6:15 p.m.<br />
Networking Reception<br />
FRIDAY<br />
OCTOBER 15<br />
7:30 a.m.–8:30 a.m.<br />
Continental Breakfast<br />
8:30 a.m.–9:00 a.m.<br />
Agency Update—What Is on<br />
CISA’s Radar?<br />
9:00 a.m.–9:45 a.m.<br />
How to Create an<br />
Organizational Defense<br />
10:00 a.m.–10:30 a.m.<br />
Break<br />
10:30 a.m.–11:15 a.m.<br />
Supply Chain Assessment<br />
and Vulnerabilities<br />
11:15 a.m.–Noon<br />
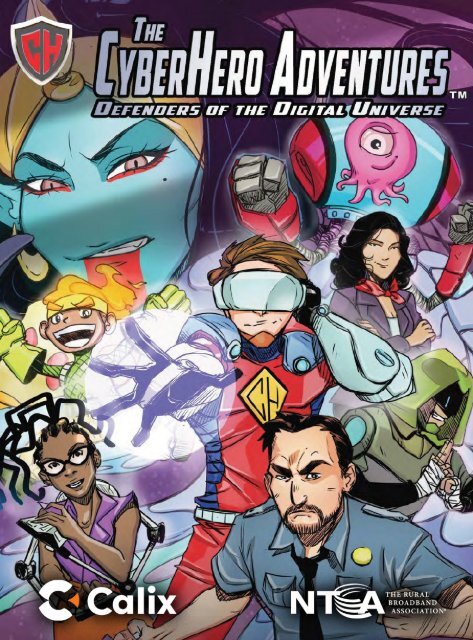
Adventures of a Cyber Hero —<br />
A CTO’s Survival Guide<br />
Gary Berman<br />
Details are subject to change.
www.calix.com<br />
BE A WORK FROM HOME<br />
WIZARD<br />
with gigaspire blast!<br />
The superior<br />
solution that gives<br />
you WiFi that works!
"Gary has put together a great show with some<br />
great talent from the cybersecurity space. From<br />
newbies to executives, everyone can stand to<br />
learn from Gary's fun and often funny (but<br />
serious) show highlighting the unsung heroes in<br />
cybersecurity".<br />
Join our mission to shine the light on<br />
the UNSUNG CYBER HEROES who<br />
toil in anonymity to keep us safe and<br />
Defend the Digital Universe!<br />
Meet members of The Cyber Hero<br />
Network who participate in highlevel,<br />
thought leadership Cyber Hero<br />
Adventures Shows, Micro Think<br />
Tanks and other B2B activities...<br />
"What a pleasure professionally to work with Gary<br />
Berman and Cyber Heroes! I've participated in<br />
several sessions he's hosted and produced and am<br />
pleased with the high caliber of the discussion he<br />
stimulates and end product he creates. Gary invites<br />
(and gets) some pretty high-powered people".<br />
"Gary‛s show is highly relevant, informative<br />
and entertaining. His questions are always on<br />
point and his guests offer helpful insights to<br />
those of us in critical infrastructure. (You‛re<br />
a great host, Gary.)".<br />
"Gary Berman is a marketing genius. With humor<br />
and aplomb he takes complex subjects and makes<br />
them accessible to everyone. He has been the<br />
pied piper for cyber security for several years<br />
now and his show is followed by thousands. I was<br />
honored to be featured myself and encouraged<br />
anyone who is invited to participate".<br />
www.cyberheroescomics.com
AFTE:R BUILDING Hl5 COMPANY THROUGH TE:N Yl':AR5 OF BLOOD, 5WE:AT ANO TE:AR5,<br />
1,-NTRl':PRl':Nl':UR L.ARRY JON!,-5 51GN5 A 01':AL WITH A LARGE: GLOBAL 5TRATl':GIC PARTNl':R.
PP!oNE:DWIT<br />
PORT OF MY Q<br />
TH!o LOV!o OF<br />
MUNCHKINS/<br />
lo HARD WO<br />
D D!oDICATION<br />
lo IN THIS R<br />
AST T!oN YioA<br />
!oM8ARKING
RE:VE:NUE: WAS UP AND THINGS<br />
WE:RE: GOING GRE:AT UNTIL ONf;.<br />
DAY ON THf:. BASKf:.TBAL.L. COURT...<br />
UNFORTUNATE:LY,<br />
THAT'S NOT THE:<br />
BAD NE:WS.<br />
THE: SCAN ALSO<br />
TURNE:D-UP SE:VE:RAL<br />
BLOOD CLOTS THAT COULD<br />
BE: LIFE:-THRE:ATE:NING IF<br />
WE: DON'T Sf;!, TO THE:M<br />
RIGHT AWAY.
OON'T WORRY<br />
ABOUT ANYTHING L.ARRY •<br />
.JUST GE:T BE:TTE:R 500N.<br />
I'LL. LOOK AFTE:R THE:<br />
COMPANY AS IF IT<br />
WE:RE: MINE:.<br />
THl5 15 .JAY AT<br />
HE:LIX ME:OIA. I GOT<br />
AN ANONYMOUS CALL<br />
ALLE:GING FRAUD IN<br />
YOUR COMPANY.<br />
PLE:A5E: RE:FUNO MY<br />
RE:TAINE:R UNTIL YOU<br />
5E:TTLE: ALL THIS.<br />
2]<br />
LAvV Fl RM<br />
This letter serves to inform you that my firm has been<br />
----ietained by Lighthouse Imaging in a matter that is of grave<br />
rn to your company. Please call m<br />
· est<br />
WHY ARE, THE,<br />
PHONE,5 5UDDE,NL Y 51Lf;NT<br />
f;XCE,PT FOR ALL THE,51,<br />
COMPLAINTS?<br />
WJ,10 MADE, THE,51,<br />
CALL5 ALLE,GING<br />
FRAUD?
C ftorl o new romponY,<br />
wnile still on poyroll<br />
C {opy inte!lertuol roperty files<br />
(indurling presentot1ons/<br />
g !Jownloorl rlient list<br />
C {o/1 clients ononymous/y,<br />
o//eging frourl<br />
!! Reseorrl otl,er woys to /Juilt!<br />
new rompony on tneir dime
Y LAWYE:R IN515<br />
5HE: RE:AD ANY AG<br />
BE:FORE: I 51GN IT<br />
IT WITH ME:<br />
OH MR J<br />
WHAT WOULD<br />
ABOUT ANY OF<br />
HAVE: MY D
... CLOSE; THE; DOORS<br />
TO HIS CORPORATE;<br />
OFFICE;S AND ...<br />
FROM SPORT<br />
UST CONFIRME;D TH<br />
f; THE; CONTRACTS<br />
IPLE: TIME:S ...<br />
1vlarket C<br />
es 2<br />
onsultants<br />
R SE:VE:RAL YE:ARS WHILE: 1-ARRY ATTE:MPTS TO RE:BUILD<br />
1-E;PHONf; CAl-1-S ARE; RE;DIRE;CTf;D, FILf;S Rf;GULARLY<br />
COMPLE:TE:LY FROM HIS COMPUTE:RS. INTRUSIONS INTO
! HOPE, THAT<br />
AND YOUR FAMI<br />
5<br />
-EoNTEoR THEo MARKEoTING FIEoLD ...<br />
[fl[jJ<br />
Rachael Stephen Darra Max<br />
Rich Barnes Argente Burgess<br />
Shannon<br />
Chen<br />
Dr Logan<br />
Kingston<br />
T 5EoVEoRAL. OF Hl5 FORMEoR Eo<br />
T 15 l-lN -
AFTE:R ANALYZING THE:<br />
DE:TAIL5 OF THE:5E: COMPUTE:R AND<br />
PHONE: 5CRE:E:N 5HOT5, IT LOOKS LIKE:<br />
OH, WOW!<br />
YOU ARE: UNDE:R A HE:AVILY ORCHE:5- FE:E:L5 GRE:AT TO HAVE:<br />
TRATE:D CYBE:R ATTACK.<br />
50MWNE: IN YOUR 5HOE:5<br />
----E::=:::\ THINK THAT IT MAKE:5 5E:N5E:.<br />
WHAT 00 WE: 00 NE:XT?<br />
Hae<br />
HE: ATTE:ND5 CONHRE:NCE:5, Ll5-<br />
TE:N5 TO COUNTLE:55 PODCA5T5,<br />
RE:AD5 RE:5E:ARCH RE:PORT5 AND ...<br />
! SPOKE:<br />
E: DISTRICT A<br />
E:Y, BUT HE:R 0<br />
WILLING<br />
LE:ARN E:VE:RYTHING HE: COU<br />
WORLD OF HACKING TO HE:LP<br />
N ONION, BE:GIN5 TO<br />
WHAT 15 HAPPE:NING.<br />
! SURE: HAD<br />
TO WIPE: A LOT OF<br />
EGG OFF MY FACE<br />
TO STAND UP AT<br />
THE: MIC .•.<br />
HE: ALSO RE:CE:IVE:5 INCRE:DIBLE: ADVICE: AND SUPPORT<br />
FROM THE: GOOD FOLKS IN CYBE:R5E:CURITY.
5UP!:R AG!:NT K HAS ALWAYS HAD A<br />
PASSION FOR LAW l:NFORC!:Ml:NT.<br />
HIS GRANDFATH!:R AND FATH!:R W!:Rl: HIGHLY Rl:SP!:CT!:D<br />
Sl:NIOR LAW !:NFORC!:Ml:NT OFFICIALS. 5UP!:R AG!:NT K<br />
Al.WAYS WANTE:O TO FOLLOW IN TH!:IR FOOTST!:PS.<br />
AN<br />
BU<br />
LARRY ANO 5UP!:R AG!:NT K Bl:COM!:<br />
FAST FRl!:NDS WITH A UNIFl!:D MISSION:<br />
TO PROT!:CT AND Dl:Fl:ND OTH!:RS<br />
FROM TH!: l:)(Pl:Rll:NC!:5 TH!:Y HAD/
SUPER AGENT K AND I..ARRY ARE INVITED<br />
TO A CYBERSECURl1Y CONFERENCE<br />
HOSTED AT THE NEXT GEN INSTITUTE.<br />
----<br />
LOWS YOU TO SEE V<br />
55ES OF HACKERS AN<br />
IMINALS AS THEY ARE<br />
"REAL" WORLD.
0<br />
0 0<br />
0
'<br />
MMON CLA55 Of HACK, AND THE:<br />
D WORK TIRE:LE:55LY TO PROTE:CT<br />
BRING DOWN THE: PE:RPE:TRATOR5.<br />
0<br />
---<br />
Re: Donation to Love Your Heart Foundation<br />
CEO Jeremy Diamond<br />
CFO Harald Jonah<br />
SUBJECT: Good Morning!<br />
WATCH OUT fOR<br />
fAKE:/5POOfE:D<br />
E:MAIL ADDRE:55E:5!<br />
E:!lt<br />
Yes, I am.<br />
Hello Harry, are you in the office right now?<br />
0<br />
I'm at an event playing golf with some other<br />
CEOs and need you to wire $SOK right away for<br />
this fundraiser.<br />
www.hartfoundation.org
LE; Of OTHE;<br />
IVE;S KNOW A<br />
AMOND'S HEcA<br />
DITION, RIGH<br />
Mark De l ete Compose Inspector<br />
WIRE TRANSFER INSTRUCTIONS<br />
Personal • Leads<br />
art Foundat on<br />
'og•<br />
Folders<br />
CEO Jeremy Diamond<br />
CFO Harald Jonah<br />
Fill out and transfer the funds as soon as possible. I want to announce my<br />
contribution during lunch. Very important to do it before lunch.<br />
CFO Harald Jonah<br />
CEO Jeremy Diamond<br />
What's the nature of this fundraiser?<br />
CEO Jeremy Diamond<br />
CFO Harald Jonah<br />
All the information is included in my previous message. I need you to transfer<br />
the funds as soon as possible.<br />
BE; CAREcfUL WHAT YOU PUT ONLINE;<br />
BEcCAUSE; IT MAY BE; USE;D AGAINST<br />
YOU AND IT WILL BE; "PUBLIC AND PE;R• ,<br />
MANEcNT" ACCORDING TO RICHARD<br />
GUE;RRY, FOUNDEcR Of THE; INSTITUTE;<br />
FOR REcSPONSIBLE; ONLINE; AND CE;LL·<br />
PHONE; COMMUNICATIONS.<br />
n. CFO Harald Jonah<br />
o CEO Jeremy Diamond<br />
I'm on it!
5T E:MAILE:D M<br />
CTING ME: TO<br />
IF1Y-THOU5AND<br />
TO THl5 FUND<br />
OUR HE:ART, NO<br />
T5 OR PACE:
Yf;S, I'VE:<br />
CHE:CKE:D THE:M OUT.<br />
THE:Y HAVE: A SOCIAL<br />
ME:DIA PRE:SE:NCf; AND<br />
SUCH, ALL GOOD/<br />
I COMPLE:TE:D THE:<br />
FORM AND SIGNW THE:<br />
PAPE:RWORK. I AUTHO·<br />
RIZE: YOU TO E:XE:CUTf;<br />
THIS RIGHT AWAY!<br />
WE:LL, THE:<br />
YOUR SIGN<br />
LL SE:E:MS
,,.<br />
Compost"<br />
Re: Donation to Love Your Heart Foundation<br />
rom: Abigail Arnold, Accounting<br />
C§!JIJ CFO Harald Jonah, CEO Jeremy Diamond<br />
0<br />
Subject: Task Completed<br />
Per your instructions and<br />
authorization in regards to Mr<br />
Diamond's request. Herc ,••...-,.,....<br />
confirmation number.<br />
.,,n,<br />
M•Tofoldff .•<br />
TO Ameritrade Wire Tram ,.<br />
,.,,,<br />
From: account no: ********<br />
To: account: **********7521 ,....<br />
RONmo<br />
CrutoO
AFTE:R 5WAL<br />
CFO HARAL<br />
"
DR G IMME:DIATE:LY FINDS THE: RE:D FLAG:<br />
A WE:LL-Dl5GUl5E:D FAKE: E:MAIL ADDRE:55. 50<br />
APPARE:NT TO THOSE: IN·THE:·KNOW, WHO LOOK A<br />
1-ITTLE: DE:E:PE:R, AT THE: ACTUAL E:MAIL ADDRE:55.<br />
/<br />
Compose<br />
Re: Donation to Love Your Heart Foundation<br />
<br />
F,om, EOJo,omy Di•mo,_<br />
SUBJE l<br />
Jeremy Diaffi"ond<br />
jeremydiamond8298@aol.com<br />
Hello ,<br />
FAKE: l>MAIL ADDRE:55!<br />
I Add to contacts<br />
Emails<br />
'<br />
THING HE:'LL<br />
0 VO RIGHT N<br />
CONTACT TH<br />
N BANK AND<br />
E:ZE: ON THO<br />
HE:IVE:5 WO<br />
E: TO WITHDRA<br />
ONE:Y BUT THE: CO<br />
50 WON'T BE: ABLE:<br />
E:R THE: FUNDS UNT<br />
15 50LVE:D, MAYBE: I<br />
AR5 OR MANY YE:AR<br />
UNLE:55 ...
!oMAIL<br />
5T ABOUT<br />
L 5!o!o If W!o<br />
IT!o5 BAC
CEO Jeremy Diamond<br />
Abigail Arnold<br />
Additional Funds for Love Your Heart Foundation<br />
A<br />
□<br />
Hello Mr. Diamond,<br />
I hope your morning on the links has refilled your tanks. Jane showed up this morning with a<br />
new perfume, whew! My allergies are on code red! But I digress ...<br />
Per your request, I wire-transferred $50,000 to account number 92-6937739. As I was doing<br />
that, I stumbled on your memorandum regarding doubling the amount of donations to heart<br />
disease research charities as a company policy for the new year.<br />
Our protocol dictates that you "sign off" on our secure website by entering pin [xz19I0] to<br />
authorize the extra $SOK. I'm providing the details here for your convenience, since I know<br />
you're at the event and might not have it handy.<br />
Arrow Bank<br />
Acct No: 6070255747179<br />
Routing: 092707912<br />
u/n: TheSquarePointGroup (case sensitive)<br />
p/w: playsD3ADtH3Pr1 nt3rD03S<br />
If you have any trouble entering the code, try lower case first then all caps. If you still have<br />
trouble, email or call me and I will assist you. Once that's done, Abigail will wire-transfer the<br />
extra funds.<br />
Let me know if you need anything else. See you bright and early.<br />
-Harald<br />
WE:!.!., I'VE: P<br />
THE: CYBE:R 8<br />
15Tl.f;5 TO 8!:<br />
CK THE: PE:<br />
ME:ANWHII.E: ... DR G 15<br />
5HING TOUCHE:5 ON A<br />
Y-RE:Al.15TIC-I.OOKING f
PH!5H!NG !5 THE: MOST COMMON TYPE: OF ONl.!NI:- SCAM. !T RE:FE:RS<br />
TO ANY ATTACK BY WHICH FRAUDSTERS IMPE:R50NATE: A I.E:GITIMATE:<br />
COMPANY ANO ATTEMPT TO STE:At. PE:R50NAI. INFORMATION OR I.OGIN<br />
CRWE:NTIAI.S. THOSE: E:MAII.S FRE:QUE:NTI.Y USE: THRE:ATS ANO A SE:NSE:<br />
OF URGE:NCY TO SCARE: USE:RS INTO DOING THE: ATTACKE:RS' BIDDING.<br />
!N SPE:AR PHISHING SCAMS, FRAUDSTE:RS CUSTOMIZE:<br />
THE:IR ATTACK E:MAII.S WITH THE: TARGE:T'S NAME:, POSITION,<br />
COMPANY, WORK PHONE: NUMBE:R AND OTHER INFORMATION<br />
IN AN ATTE:MPT TO TRICK THE: RE:CIPIE:NT INTO BE:I.IE:VING<br />
THAT THE:Y HAVE: A CONNECTION WITH THE: SE:NDE:R.
_:_::.<br />
THf:. CYBf:.RHf:.RO "UNMA5K5" THf:. PHl5Hf:.R BY DRAINING<br />
Hf:.R Mf:.MORY 8ANK5 AND COl.t.f:.CTING DATA THAT Wit.I.<br />
PO51TIVf:.t.Y IDf:.NTIFY Hf:.R IN THf:. Rf:.At. WORLD/<br />
CYBf:.RHf:.ROf:.5 ARf:. A8t.f:.<br />
f:.CT AND MAKf:. AN ARRf:.5T/<br />
THf:. CYBf:.RHf:.ROf:.5' WORK Nf:.Vf:.R 5TOP5/<br />
TUNf:. IN FOR THf:. Nf:.XT 155Uf:. OF THf:.<br />
CY8ERHERO A0VENTUREG!
IVAN STEALS '!'OUR NAME, DATE<br />
OF BIRTH, SOCIAL SECURIH<br />
NUMBER, DRIVER 1 S LICENSE<br />
NUMBER, BAN1' ACCOUNT AND<br />
CREDIT CARD NUMBERS, PIN<br />
NUMBERS, ELECTRONIC<br />
SIGNATURES, FINGERPRINTS,<br />
AND PASSWORDS... ALL IN AN<br />
EFFORT TO BECOME '(OU!<br />
Ar LEAST FOR THE<br />
PURPOSES OF STEALING<br />
'!'OUR MONE'!' AND<br />
APPL 'l'ING FOR LOANS<br />
CREDIT CARDS IN<br />
'(ou'LL HPICALL'I'<br />
A VARIEH OF<br />
• RUMMAGING<br />
GARBAGE FOR<br />
PERSONAL DOCUMENTS<br />
AND PHONES.<br />
• STEALING '!'OUR<br />
CREDIT CARDS,<br />
CARDS, PASSPORTS AND<br />
TO1'ENS.<br />
• UUESSING COMMON<br />
QUESTIONS SUCH AS:<br />
MAIL TO OBTAIN<br />
IDENTIFICATION<br />
AUTHENTICATION<br />
11:NOWLEDGE<br />
1 1 MOTHER 1 S MAIDEN<br />
NAME?", 11 FIRST CAR<br />
MODEL?" OR<br />
1 1<br />
1FIRST PET S NAME?"<br />
• S1'IMMING<br />
INFORMATION FROM<br />
CREDIT CARDS USING HAND-HELD CARD READERS.<br />
• I-IAC1'ING CO<br />
BASES TO OBTAIN<br />
LARGE QUANTITIES.<br />
• BRUTE-FORCE<br />
WORDS.<br />
• BROWSING<br />
SITES FOR PER-<br />
8'1' USERS.<br />
• DIVERTING<br />
IN ORDER TO<br />
TION AND CRE<br />
CARDS, BILLING<br />
STATEMENTS, OR<br />
NEW ACCOUNTS<br />
MENTS OPENED<br />
THIEVES IN THE<br />
•USING 1 CONTACTLESS 1<br />
CREDIT CARD READERS TO<br />
ACQUIRE DATA WIRELESSL 'I'.<br />
• DISCREETL 'I' WATCHING OR<br />
HEARING OTHERS PROVIDING VALU<br />
ABLE PERSONAL INFORMATION<br />
(SHOULDER-SURFING).<br />
• STEALING PERSONAL INFORMA<br />
TION FROM COMPUTERS USING<br />
BREACHES IN BROWSER SECURI<br />
MALWARE SUCH ASTRO.JAN<br />
1'E'l'STRO1'E LOGGING PRO-<br />
PUTER NETWOR1'S AND DATA<br />
PERSONAL DATA, OFTEN IN<br />
ATTAC1'ING WEAi( PASS<br />
SOCIAL NETWOR1'ING<br />
SONAL DETAILS PUBLISHED<br />
VICTIMS 1<br />
EMAIL OR MAIL<br />
OBTAIN PERSONAL INFORMA<br />
DENTIALS SUCH AS CREDIT<br />
AND BANl
0<br />
0<br />
0<br />
1Ji1o<br />
<br />
o<br />
I)<br />
0<br />
@]
LAl212'( IS A "12E
The small broadband provider ISAC<br />
EFFICIENT. AFFORDABLE. EFFECTIVE.<br />
CyberShare provides education and awareness of cybersecurity risk<br />
management practices and empowers you to take action.<br />
Relevant information<br />
The alerts and news are<br />
compiled specifically for<br />
small broadband providers.<br />
Access to experts<br />
Hear from government and<br />
industry experts you may not<br />
have access to otherwise.<br />
Efficient and time saving<br />
Access critical information<br />
compiled from public and<br />
nonpublic sources and tailored<br />
to your needs. Participants<br />
avoid spending hours each day<br />
combing sources.<br />
Peer-to-peer sharing and<br />
networking<br />
Develop relationships across<br />
the country and securely<br />
share information.<br />
Affordable<br />
CyberShare costs a fraction<br />
of what you would spend for<br />
larger cyberthreat products<br />
but offers more targeted<br />
information. Members also may<br />
earn a discount on their cyber<br />
insurance policy.<br />
Illustrates commitment to<br />
cybersecurity<br />
Show your customers and<br />
policymakers that you prioritize<br />
cybersecurity.<br />
Training tools<br />
Access the SecurityScorecard<br />
Cybersecurity Risk Ratings and<br />
CyberESI training module to use<br />
for companywide cybersecurity<br />
training.<br />
CyberShare, launched in 2019, was recently recognized as an Information<br />
Sharing and Analysis Center (ISAC), which establishes the program as<br />
THE ISAC for the small broadband community.<br />
90%<br />
of participants say the program<br />
adds value for their company<br />
86%<br />
would recommend the program<br />
to peers and other small<br />
network operators<br />
I was extremely happy with CyberShare —<br />
The Small Broadband Provider ISAC<br />
program’s communications regarding<br />
the exploitation of SolarWinds Orion<br />
Platform. Their operations manager<br />
provided timely, relevant and actionable<br />
information throughout the day, including<br />
an invitation to a Cybersecurity and<br />
Infrastructure Security Agency (CISA)<br />
meeting, which I attended. Solid return<br />
on investment for joining CyberShare.<br />
93%<br />
KURT FILES<br />
of participants say the program<br />
enhances their situational<br />
awareness about cyberthreats<br />
Director of IT, Home Telecom<br />
(Moncks Corner, SC)<br />
Learn more about how CyberShare can benefit your business by visiting www.cyber-share.org.