Cyber Defense eMagazine September Edition for 2022 #CDM
#CYBERDEFENSEMAG @CyberDefenseMag by @Miliefsky a world-renowned cyber security expert and the Publisher of Cyber Defense Magazine as part of the Cyber Defense Media Group as well as Yan Ross, Editor-in-Chief and many more writers, partners and supporters who make this an awesome publication! Thank you all and to our readers! OSINT ROCKS! #CDM #CDMG #OSINT #CYBERSECURITY #INFOSEC #BEST #PRACTICES #TIPS #TECHNIQUES
#CYBERDEFENSEMAG @CyberDefenseMag by @Miliefsky a world-renowned cyber security expert and the Publisher of Cyber Defense Magazine as part of the Cyber Defense Media Group as well as Yan Ross, Editor-in-Chief and many more writers, partners and supporters who make this an awesome publication! Thank you all and to our readers! OSINT ROCKS! #CDM #CDMG #OSINT #CYBERSECURITY #INFOSEC #BEST #PRACTICES #TIPS #TECHNIQUES
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
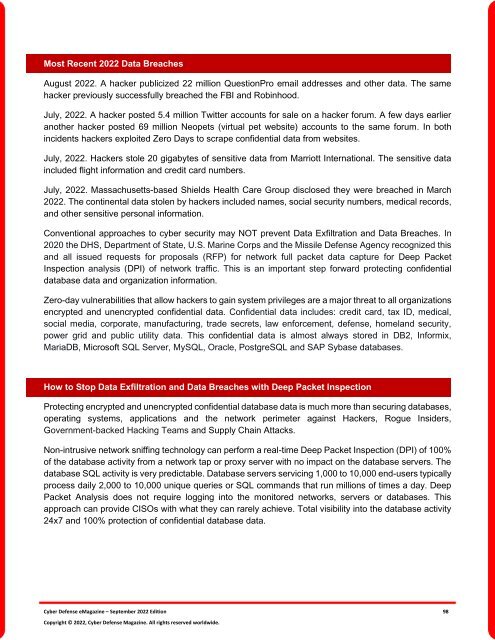
Most Recent <strong>2022</strong> Data Breaches<br />
August <strong>2022</strong>. A hacker publicized 22 million QuestionPro email addresses and other data. The same<br />
hacker previously successfully breached the FBI and Robinhood.<br />
July, <strong>2022</strong>. A hacker posted 5.4 million Twitter accounts <strong>for</strong> sale on a hacker <strong>for</strong>um. A few days earlier<br />
another hacker posted 69 million Neopets (virtual pet website) accounts to the same <strong>for</strong>um. In both<br />
incidents hackers exploited Zero Days to scrape confidential data from websites.<br />
July, <strong>2022</strong>. Hackers stole 20 gigabytes of sensitive data from Marriott International. The sensitive data<br />
included flight in<strong>for</strong>mation and credit card numbers.<br />
July, <strong>2022</strong>. Massachusetts-based Shields Health Care Group disclosed they were breached in March<br />
<strong>2022</strong>. The continental data stolen by hackers included names, social security numbers, medical records,<br />
and other sensitive personal in<strong>for</strong>mation.<br />
Conventional approaches to cyber security may NOT prevent Data Exfiltration and Data Breaches. In<br />
2020 the DHS, Department of State, U.S. Marine Corps and the Missile <strong>Defense</strong> Agency recognized this<br />
and all issued requests <strong>for</strong> proposals (RFP) <strong>for</strong> network full packet data capture <strong>for</strong> Deep Packet<br />
Inspection analysis (DPI) of network traffic. This is an important step <strong>for</strong>ward protecting confidential<br />
database data and organization in<strong>for</strong>mation.<br />
Zero-day vulnerabilities that allow hackers to gain system privileges are a major threat to all organizations<br />
encrypted and unencrypted confidential data. Confidential data includes: credit card, tax ID, medical,<br />
social media, corporate, manufacturing, trade secrets, law en<strong>for</strong>cement, defense, homeland security,<br />
power grid and public utility data. This confidential data is almost always stored in DB2, In<strong>for</strong>mix,<br />
MariaDB, Microsoft SQL Server, MySQL, Oracle, PostgreSQL and SAP Sybase databases.<br />
How to Stop Data Exfiltration and Data Breaches with Deep Packet Inspection<br />
Protecting encrypted and unencrypted confidential database data is much more than securing databases,<br />
operating systems, applications and the network perimeter against Hackers, Rogue Insiders,<br />
Government-backed Hacking Teams and Supply Chain Attacks.<br />
Non-intrusive network sniffing technology can per<strong>for</strong>m a real-time Deep Packet Inspection (DPI) of 100%<br />
of the database activity from a network tap or proxy server with no impact on the database servers. The<br />
database SQL activity is very predictable. Database servers servicing 1,000 to 10,000 end-users typically<br />
process daily 2,000 to 10,000 unique queries or SQL commands that run millions of times a day. Deep<br />
Packet Analysis does not require logging into the monitored networks, servers or databases. This<br />
approach can provide CISOs with what they can rarely achieve. Total visibility into the database activity<br />
24x7 and 100% protection of confidential database data.<br />
<strong>Cyber</strong> <strong>Defense</strong> <strong>eMagazine</strong> – <strong>September</strong> <strong>2022</strong> <strong>Edition</strong> 98<br />
Copyright © <strong>2022</strong>, <strong>Cyber</strong> <strong>Defense</strong> Magazine. All rights reserved worldwide.