CS Nov-Dec 2022
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Computing<br />
Security<br />
Secure systems, secure data, secure people, secure business<br />
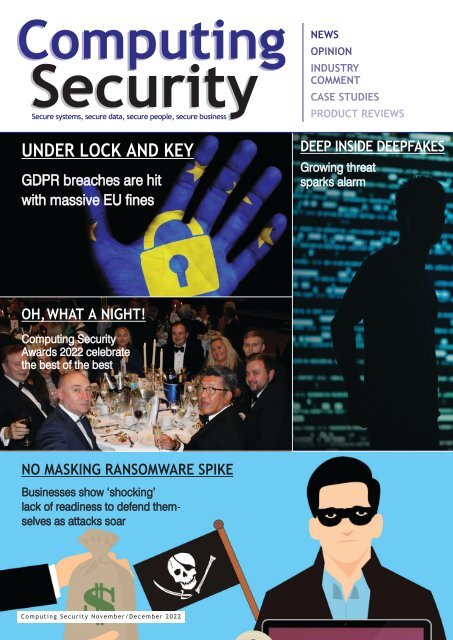
UNDER LOCK AND KEY<br />
GDPR breaches are hit<br />
with massive EU fines<br />
NEWS<br />
OPINION<br />
INDUSTRY<br />
COMMENT<br />
CASE STUDIES<br />
PRODUCT REVIEWS<br />
DEEP INSIDE DEEPFAKES<br />
Growing threat<br />
sparks alarm<br />
OH,WHAT A NIGHT!<br />
Computing Security<br />
Awards <strong>2022</strong> celebrate<br />
the best of the best<br />
NO MASKING RANSOMWARE SPIKE<br />
Businesses show ‘shocking’<br />
lack of readiness to defend themselves<br />
as attacks soar<br />
Computing Security <strong>Nov</strong>ember/<strong>Dec</strong>ember <strong>2022</strong>
Nobody likes feeling<br />
vulnerable.<br />
It’s the same when it comes<br />
to information security.<br />
That’s why our services have been designed<br />
to provide you with the information security<br />
assurances you, and your clients, require.<br />
Penetration Testing<br />
Red Teaming<br />
Information Security Consultancy<br />
www.pentest.co.uk<br />
contact@pentest.co.uk<br />
0161 233 0100<br />
pentest<br />
INFORMATION SECURITY ASSURANCE
comment<br />
WHY DATA ETHI<strong>CS</strong> MATTER<br />
Data ethics is no longer an academic or niche geek issue, as it has been since the<br />
inception of the internet and the world wide web. It has never been more<br />
urgent.<br />
That is the timely warning from Annie Machon in her newly released book, ‘The<br />
Privacy Mission: Achieving Ethical Data for Our Lives Online’. And Machon should know.<br />
After all, she began her career working as an intelligence officer for MI5, has extensive<br />
experience as an international public speaker, writer, media commentator and political<br />
campaigner, and is now the director of the World Ethical Data Foundation.<br />
As she points out: "Data ethics is an issue that affects all of us now, as<br />
our personal and professional lives increasingly take place online. Who controls access<br />
to the hardware, who runs the software, who can spy on us, hack us, data farm us?<br />
What are the threats that we need to mitigate against democratically, societally and<br />
personally? How can corporations protect us and how can that help their bottom line?"<br />
'The Privacy Mission' aims to answer these questions, and summarise both the<br />
overarching concepts and principles about why data ethics is important. It offers<br />
practical solutions for companies, policy makers and individuals to push back against<br />
known threats and future proof themselves, going forward. This book is not only timely,<br />
though - it's necessary. In an age when data has gone way beyond abundant and data<br />
ethics are constantly being eroded, making sure we protect ourselves, our businesses<br />
and those with whom we interact is something that falls to us all.<br />
See page 15 for an extract from Annie Machon's book.<br />
Brian Wall<br />
Editor<br />
Computing Security<br />
brian.wall@btc.co.uk<br />
EDITOR: Brian Wall<br />
(brian.wall@btc.co.uk)<br />
LAYOUT/DESIGN: Ian Collis<br />
(ian.collis@btc.co.uk)<br />
SALES:<br />
Edward O’Connor<br />
(edward.oconnor@btc.co.uk)<br />
+ 44 (0)1689 616 000<br />
Daniella St Mart<br />
(daniella.stmart@btc.co.uk)<br />
+ 44 (0)1689 616 000<br />
Stuart Leigh<br />
(stuart.leigh@btc.co.uk)<br />
+ 44 (0)1689 616 000<br />
PUBLISHER: John Jageurs<br />
(john.jageurs@btc.co.uk)<br />
Published by Barrow & Thompkins<br />
Connexions Ltd (BTC)<br />
35 Station Square,<br />
Petts Wood, Kent, BR5 1LZ<br />
Tel: +44 (0)1689 616 000<br />
Fax: +44 (0)1689 82 66 22<br />
SUBSCRIPTIONS:<br />
UK: £35/year, £60/two years,<br />
£80/three years;<br />
Europe: £48/year, £85/two years,<br />
£127/three years<br />
R.O.W:£62/year, £115/two years,<br />
£168/three years<br />
Single copies can be bought for<br />
£8.50 (includes postage & packaging).<br />
Published 6 times a year.<br />
© <strong>2022</strong> Barrow & Thompkins<br />
Connexions Ltd. All rights reserved.<br />
No part of the magazine may be<br />
reproduced without prior consent,<br />
in writing, from the publisher.<br />
www.computingsecurity.co.uk <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> computing security<br />
@<strong>CS</strong>MagAndAwards<br />
3
Secure systems, secure data, secure people, secure business<br />
Computing Security <strong>Nov</strong>ember/<strong>Dec</strong>ember <strong>2022</strong><br />
inside this issue<br />
CONTENTS<br />
Computing<br />
Security<br />
UNDER LOCK AND KEY<br />
GDPR breaches are hit<br />
with massive EU fines<br />
OH,WHAT A NIGHT!<br />
NEWS<br />
OPINION<br />
INDUSTRY<br />
COMMENT<br />
CASE STUDIES<br />
PRODUCT REVIEWS<br />
DEEP INSIDE DEEPFAKES<br />
Growing threat<br />
sparks alarm<br />
Computing Security<br />
Awards <strong>2022</strong> celebrate<br />
the best of the best<br />
NO MASKING RANSOMWARE SPIKE<br />
COMMENT 3<br />
Why data ethics matter<br />
Businesses show ‘shocking’<br />
lack of readiness to defend themselves<br />
as attacks soar<br />
NEWS 6 & 8<br />
Bitdefender partners with Ferrari<br />
Ransomware on the rampage<br />
Pulling a FAST one<br />
Data breach cost hits all-time high<br />
Channel 4 steps up safety of data<br />
ARTICLES<br />
THE DATA ETHI<strong>CS</strong> QUEST 15<br />
Annie Machon's book, 'The Privacy<br />
Mission: Achieving Ethical Data for Our<br />
Lives Online', takes readers into a world<br />
where data ethics walks a fragile line<br />
SURVIVING THE SHOCKWAVES 10<br />
To misquote a line from a classic film<br />
and attribute it to the year that’s fast<br />
approaching: 'Fasten your seatbelts, it's<br />
going to be a bumpy 2023!' Computing<br />
Security has been asking those in the know,<br />
for better or worse, what they believe we<br />
might be in store for in those 12 months.<br />
PATH TO SECURITY ASSUREDNESS 18<br />
Paul Harris, managing director at Pentest<br />
AWARDS NIGHT A WIN-WIN-WIN! 16<br />
Limited, shows how confidence can be<br />
What an atmosphere, what an occasion!<br />
your information security secret weapon<br />
The Computing Security Awards <strong>2022</strong>,<br />
held at a top London venue, once again<br />
DYSTOPIAN WORLD OF DEEPFAKES 20<br />
showcased the enormous wealth of talent<br />
Matt Lewis, commercial research director<br />
that exists right across our industry. See all<br />
at NCC Group, considers what threats<br />
of the winners in our 2-page coverage.<br />
‘deepfakes’ might pose, in the wake of<br />
BBC series ‘The Captive’<br />
YOU AND YOUR DATA 22<br />
Nick Evans, GeoLang's sales and marketing<br />
manager, reveals why having a solid<br />
data management plan is so important<br />
RANSOMWARE ON THE RAMPAGE 24<br />
With 24% of businesses identified in recent<br />
GETTING THE BALANCE RIGHT 30<br />
research as having been victims subjected<br />
Mike Nelson, VP of IoT Security at<br />
to an attack, the omens for the year<br />
DigiCert, explains what the EU Cyber<br />
ahead look worrying. What are the latest<br />
Resilience Act means, in the first move<br />
strategies and techniques they can turn to<br />
to legislate cybersecurity for the IoT<br />
that will enable them to fight back?<br />
BUILDING A CAPTIVE AUDIENCE 32<br />
Packets provide the ’only truly definitive<br />
evidence of performance and security<br />
issues’ that happen on a network, states<br />
Mark Evans, VP of marketing, Endace,<br />
REGULATORS MEAN BUSINESS! 38<br />
who argues the case for packet capture<br />
The second largest ever fine for a breach<br />
of the General Data Protection Regulation<br />
THE SLIDE TOWARD DATA CARNAGE 34<br />
was slapped on Instagram recently - 405<br />
A new extortion technique could see<br />
million euros. Will this force organisations<br />
threat actors shift their focus towards<br />
to adopt stricter data management and<br />
leveraging Exmatter, in order to destroy<br />
protection measures going forward?<br />
data, rather than encrypt it, warns Cyderes<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk<br />
4
We focus on your<br />
cybersecurity threats,<br />
so you can focus on<br />
your business.<br />
Managed<br />
Services<br />
Identity & Access<br />
Management<br />
Professional<br />
Services
news<br />
Andy Harris,<br />
Osirium.<br />
PULLING A FAST ONE<br />
US business and media publication<br />
Fast Company being hacked - and<br />
then "obscene and racist" notifications<br />
being sent to Apple users - shows how<br />
vulnerable organisations are to such<br />
incidents. "Attackers are increasingly<br />
using weak, stolen, or otherwise<br />
compromised credentials to breach<br />
organisations," warns Andy Harris, CTO,<br />
Osirium. "Although many businesses<br />
have taken steps in implementing<br />
rigorous password policies, SysAdmin<br />
credentials still need protecting from<br />
abuse. Password education is a good<br />
place to start - and not sharing<br />
credentials is critical, as proven in<br />
the Fast Company breach.<br />
"Sharing passwords negates individual<br />
accountability," adds Harris, "something<br />
that Privileged Access Management<br />
[PAM] can preserve in a way that<br />
Password Vaults cannot."<br />
BITDEFENDER PARTNERS WITH FERRARI<br />
Bitdefender has entered into a multi-year partnership<br />
with Ferrari S.p.A. to become cybersecurity global<br />
partner of Scuderia Ferrari, which is competing in the<br />
FIA Formula 1 World Championship.<br />
As a partner, starting at the Formula 1 Singapore Airlines,<br />
Singapore Grand Prix <strong>2022</strong>, Bitdefender will display its<br />
company logo on Ferrari drivers' helmets, as well as on<br />
the F1-75 single-seater driven by Charles Leclerc and<br />
Carlos Sainz, and, from 2023, on racing suits and<br />
team uniforms.<br />
Comments Florin Talpes, Bitdefender co-founder and chief<br />
executive officer: "When every second counts, only the<br />
most advanced cars win races on the track, and only the<br />
most advanced technology has the power to effectively<br />
Ferrari driver Carlos Sainz.<br />
prevent, defend and respond to cyberattacks."<br />
RANSOMWARE ON THE RAMPAGE<br />
Nearly a quarter of businesses surveyed have suffered from<br />
a ransomware attack, with a fifth occurring in the past<br />
12 months. That is according to a latest annual report from<br />
cybersecurity specialist Hornetsecurity. The <strong>2022</strong> Ransomware<br />
Report, which polled more than 2,000 IT leaders, discloses<br />
that 24% have been victims of a ransomware attack, with<br />
one in five (20%) attacks happening in the last year.<br />
States Hornetsecurity CEO Daniel Hofmann: "Our survey<br />
shows that many in the IT community have a false sense of<br />
security. As bad actors develop new techniques, companies<br />
like ours have to do what it takes to come out ahead and<br />
protect businesses around the world."<br />
For more data and insights, go to this link:<br />
https://www.hornetsecurity.com/en/knowledgebase/ransomware/ransomware-attacks-survey-<strong>2022</strong><br />
PHISHING SCAM TARGETED WETRANSFER<br />
According to Metro, hackers have been actively adopting<br />
a new phishing scam by disguising malware as WeTransfer<br />
links. The scam involves hackers sending a 'Proof of Payment'<br />
document from WeTransfer, but instead sharing a link<br />
containing malware. Cybersecurity researchers from Cofense<br />
found that hackers distributed a malware called Lampion,<br />
using the misleading links<br />
States Jake Moore, global cyber security advisor at ESET:<br />
"People need to verify the source of attachments, irrespective<br />
of the carrier, and, if they are not expecting it, they should<br />
carry out further due diligence. If the attachment received is<br />
a zip file, people need to be extra cautious."<br />
Daniel Hofmann,<br />
Hornetsecurity.<br />
Jake Moore, ESET.<br />
6<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
news<br />
Bogdan<br />
Botezatu,<br />
Bitdefender.<br />
VULNERABILITIES COULD GIVE<br />
ATTACKERS FULL ACCESS TO ASSETS<br />
Bitdefender recently released<br />
vulnerability research on Device42, a<br />
comprehensive data centre and popular<br />
asset management platform that<br />
enables IT administrators to discover,<br />
map and manage hardware, software,<br />
devices and networks on premises and<br />
across cloud environments.<br />
Research reported that attackers who<br />
were exploiting these vulnerabilities<br />
could gain full access to the assets<br />
housed inside the platform through<br />
remote code execution (RCE). Bogdan<br />
Botezatu, director of threat research &<br />
reporting at Bitdefender, comments:<br />
"These vulnerabilities can expose<br />
extremely sensitive information<br />
belonging to organisations and, when<br />
they result in remote code execution,<br />
they can also be used to plant malware<br />
on the company's network. In order to<br />
protect their assets, organisations need<br />
to run periodic security assessments of<br />
third-party applications, identify<br />
vulnerabilities and misconfiguration, and<br />
patch immediately."<br />
DATA BREACH COST HITS ALL-TIME HIGH<br />
The average cost of a data breach rose to an all-time<br />
high of $4.4 million this year, according to IBM Security.<br />
Trevor Dearing, director of critical infrastructure solutions<br />
at Illumio, says many of the highest-cost breaches involved<br />
critical infrastructure, evidence that criminals have realised<br />
they can increase their profitability by disrupting the availability<br />
of services, thereby increasing the likelihood that<br />
their ransomware demands will be met, as organisations<br />
struggle to get life-saving systems back up and running as<br />
fast as possible.<br />
"By taking a Zero Trust approach, segmenting critical assets,"<br />
advises Dearing, "and only allowing known and verified<br />
communication between environments, security teams<br />
can limit the impact of an attack for both the organisation Trevor Dearing, Illumio.<br />
and its customers."<br />
VIPRE SPREADS THE E-LEARNING MESSAGE ACROSS EMEA<br />
VIPRE Security Group is now offering the full library<br />
of its award-winning training content to its partners<br />
and clients across Europe, the Middle East and Africa<br />
(EMEA). Inspired eLearning, part of VIPRE Security<br />
Group, offers "security awareness and compliance<br />
eLearning solutions that drive positive and measurable<br />
changes in organisational culture", says the company,<br />
helping businesses protect themselves against cyberattacks<br />
and regulatory violations.<br />
"With strict regulations in place from GDPR, PCI<br />
[Payment Card Industry Compliance], and businesses<br />
attempting to gain or retain ISO27001 accreditation,<br />
it has never been a better time for businesses to invest<br />
in their cybersecurity strategy," says the company’s<br />
VP EMEA B2B, Robert den Drijver.<br />
CHANNEL 4 STEPS UP SAFETY OF DATA<br />
Robert den Drijver, VIPRE.<br />
As part of protecting the information it collects, in line with regulations such as<br />
the GDPR, Channel 4 needs to secure vast amounts of information, including<br />
the data of 24 million All 4 subscribers, staff details and all of its intellectual<br />
property, and be able to demonstrate that this data is safe and secure.<br />
Previously, the television network would perform a penetration test and, after<br />
getting the results, have to fix the issue and then pay for another penetration test.<br />
"That could be quite a cycle," says Channel 4 CISO Brian Brackenborough,<br />
"depending on how complicated the particular project was." Now Channel 4 is<br />
saving the organisation's security department thousands each year, it is reported,<br />
after partnering with Invicti Security to gain complete visibility into its web assets.<br />
8<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
2023 predictions<br />
SURVIVING THE SHOCKWAVES<br />
TO SLIGHTLY MISQUOTE A PRICELESS LINE FROM A CLASSIC FILM AND ATTRIBUTE IT TO THE YEAR<br />
THAT'S RAPIDLY APPROACHING: 'FASTEN YOUR SEATBELTS, IT'S GOING TO BE A BUMPY RIDE!'<br />
You have only to look at the state of<br />
our economy and the political turmoil<br />
in the UK right now to realise 2023 is<br />
going to be a tough year to get through in<br />
sound health as a business. Never mind<br />
thriving, more a case of surviving.<br />
Meanwhile, as far as computing security<br />
goes, the challenges remain as immense as<br />
ever, if not more so, with the number of<br />
cyber-attacks soaring and the methods of<br />
infiltration growing ever more pervasive and<br />
sophisticated. What can we expect, then, in<br />
the year ahead? Which will prove to be the<br />
'killer' solutions to ward off the attackers?<br />
Will there be new ways to make ourselves<br />
safer -ie, where will the next breakthrough<br />
come from to bolster our resilience and<br />
safeguard the systems on which<br />
organisations depend? Computing Security<br />
has been asking those who spend their<br />
working days fighting against the 'darker<br />
forces'. Here is how they see the world, for<br />
better or worse, in the 12 months ahead.<br />
ANDY SYREWICZE, TECHNICAL<br />
EVANGELIST AT HORNETSECURITY<br />
"The rate of cyber security breaches is<br />
accelerating. There are many reasons for this,<br />
but we can really break it down to a few key<br />
things. First, it's a fact that the increasing<br />
complexity and requirements of IT systems<br />
create more opportunity for breaches. For<br />
example, with hybrid work, workers are<br />
more distributed than ever and IT teams are<br />
struggling to best manage this distributed<br />
workforce. Cloud deployments are becoming<br />
increasingly vast, with many third-party APIs<br />
and interconnected hooks into production<br />
systems. "Every API in use, every 'one-off'<br />
connection, is another avenue for cyber<br />
criminals to exploit in an attempt to<br />
compromise critical business systems. Digital<br />
transformation is accelerating, not slowing<br />
down, so we're expecting this trend to<br />
continue until a critical mass of businesses<br />
realise that there needs to be a balance<br />
between fast digital adoption and sustainable<br />
security across the entire digital estate.<br />
"Secondly, we've seen time and time again<br />
where massive security measures were<br />
sidestepped, simply because an end user<br />
fell prey to social engineering. For example,<br />
the recent Uber breach shows us that<br />
technologies like multi-factor authentication<br />
are still susceptible to social engineering<br />
techniques. In this case, a combination of<br />
MFA Prompt Fatigue and carefully crafted<br />
WhatsApp messages claiming to be from<br />
Uber support were enough to trick an<br />
external contractor into helping the attacker<br />
get past the MFA process. In this case, and<br />
many others like it, proper end-user security<br />
awareness training for all users will go a long<br />
way towards cultivating a sustainable security<br />
culture and help prevent future breaches.<br />
"Finally, one key thing we've seen with Zero-<br />
Day threats throughout the year is the fact<br />
that the amount of time between the<br />
discovery of an exploit and when it begins<br />
seeing use in the wild is shrinking. System<br />
admins are increasingly under pressure to<br />
apply Zero-Day patches in a timely manner,<br />
in order to mitigate these risks. In the coming<br />
year, system admins need to be aware of this<br />
shift, and make sure they stay informed and<br />
up to date on their patching schedules, in<br />
order to reduce vulnerability."<br />
MIKE NELSON, VP OF IOT SECURITY<br />
AT DIGICERT<br />
"Matter will become the household standard<br />
for the smart home. Interoperability is<br />
a problem that plagues home IoT. Many<br />
IoT home devices are proprietarily divided<br />
between vendors. In <strong>2022</strong>, Matter - a new<br />
smart home standard - erupted into the<br />
space, with the intention of securing and<br />
enabling communication between devices,<br />
no matter which vendor they come from.<br />
"In 2023, this ground-breaking new<br />
standard will likely be uptaken with<br />
great enthusiasm, as users, vendors and<br />
manufacturers seize hold of its undeniable<br />
benefits. Uptake has already been rapid,<br />
with Google, Amazon, Apple and Samsung<br />
backing it from inception. The latest<br />
Apple iOS 16 is already supporting it and<br />
manufacturers will not be able to resist<br />
adopting it for long."<br />
Code Signing will move to the cloud. "As<br />
Code-Signing becomes an ever-greater asset<br />
to supply chain security, industry regulators<br />
are stepping up. In <strong>Nov</strong>ember <strong>2022</strong>, the CA/B<br />
Forum will demand that private keys for OV<br />
Code Signing certificates be stored on devices<br />
that meet a minimum security standard.<br />
In 2023, we predict that users will migrate -<br />
en masse - to cloud signing as a direct<br />
response to this new hardware requirement."<br />
10<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
2023 predictions<br />
Meanwhile, EU Digital Identity will become<br />
a model for global government Identities,<br />
states Stephen Davidson, senior manager in<br />
DigiCert's global Governance, Risk and<br />
Compliance team.<br />
"The EU Digital Identity Wallet is a European<br />
Commission initiative under the eIDAS<br />
Regulation that will create a unified digital<br />
identification system across Europe. The EU<br />
Digital ID Wallet will allow European citizens<br />
to carry eID versions of their official government<br />
ID documents in a secure mobile wallet<br />
application for use in online authentication<br />
and electronic signatures. Also, the wallets<br />
will carry 'electronic attribute attestations' -<br />
supplemental aspects of identity like a<br />
professional qualification - that can be<br />
presented either with the personal identity<br />
or separately." The EU has significant crossborder<br />
projects lined up in financial services,<br />
education and healthcare, he points out.<br />
ASHLEY STEPHENSON, CTO,<br />
CORERO NETWORK SECURITY<br />
"The spiralling series of DDoS records will<br />
continue to be set and broken. In the last few<br />
months, we've seen multiple broken records<br />
for DDoS attack sizes, in terms of packets per<br />
second. In July, a record was set when one<br />
unnamed actor launched an attack of 659.6<br />
million packets-per-second. That record was<br />
broken shortly after in September, when<br />
another attack achieved a new record of<br />
704.8 million packets per second.<br />
"DDoS attacks have classically attempted<br />
to send fewer packets of larger sizes, which<br />
aim at paralysing the internet pipeline by<br />
exceeding available bandwidth. More recent<br />
record-breaking attacks, however, send more<br />
packets of smaller size, which target more<br />
transactional processing to overwhelm<br />
a target. In 2023, we'll see even more<br />
records broken as attackers deploy ever<br />
higher packets-per-second in their attacks."<br />
More breach reports and possible personal<br />
executive blowback. "The last few years have<br />
seen an explosion of data protection<br />
regulation around the world. In 2023, that<br />
will mean we see more breach reports as<br />
more organisations become compelled to<br />
publicly disclose these cyber incidents.<br />
"The legal responsibility for bad corporate<br />
behaviour when dealing with breaches may<br />
also redound to individual executives. Joe<br />
Sullivan, former head of security at Uber,<br />
was recently found guilty of hiding a breach<br />
on the ride-sharing giant in 2016. This<br />
example may set a precedent for other court<br />
cases in 2023 and make data protection<br />
decisions a matter of personal legal<br />
accountability for executives.<br />
"DDoS attackers will continue to outwit<br />
legacy defences," Stephenson further<br />
comments, "and DDoS will still be a weapon<br />
in the Ukraine conflict. "Cyberwarfare has<br />
always been an aspect of the conflict in<br />
Ukraine. DDoS attack numbers exploded<br />
after the Russian invasion in February and<br />
DDoS will continue to be an asymmetric<br />
weapon in the continuing struggle."<br />
CAMILLE CHARAUDEAU, VICE<br />
PRESIDENT, PRODUCT STRATEGY<br />
AT CYBELANGEL<br />
"Gartner named attack surface expansion as<br />
one of the top security threats of <strong>2022</strong> and<br />
we think this is going to continue in 2023.<br />
Most organisations start out by thinking of<br />
their external attack surface in terms of<br />
their known assets. As their security strategy<br />
matured, many progressed to tackling<br />
shadow IT, which are assets and services that<br />
their IT and security teams are unaware of,<br />
but are still owned by the organisation.<br />
"In 2023, enterprises will likely see increased<br />
attacks on their extended attack surfaces,<br />
which include their entire supply chain<br />
ecosystem of suppliers, distributors, partners,<br />
vendors, who in turn bring along their own<br />
supply chain with varying levels of maturity<br />
in security practices. With increased globalisation<br />
and decentralisation of operations,<br />
Mike Nelson, DigiCert: in 2023, users will<br />
migrate, en masse, to cloud signing.<br />
Andy Syrewicze, Hornetsecurity: system<br />
admins are increasingly under pressure to<br />
apply Zero-Day patches in a timely manner.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> computing security<br />
11
2023 predictions<br />
Camille Charaudeau, CybelAngel:<br />
enterprises will likely see increased<br />
attacks on extended attack surfaces.<br />
Stephen Cavey, Ground Labs: global<br />
regulators are now putting stronger laws<br />
in place to protect their citizens' data.<br />
an extended attack surface quickly expands<br />
beyond an organisation's own controlled<br />
perimeter and robust security practices.<br />
Simply doing business with companies with<br />
less mature security practices will increase<br />
risks in your own systems and processes.<br />
"Security leaders will need to supercharge<br />
their external attack surface management<br />
(EASM) programs to include digital risk<br />
protection solutions (DRPS), as these<br />
technologies strongly complement each<br />
other, to provide more comprehensive<br />
coverage than either alone. This means<br />
eliminating blind spots and achieving full<br />
visibility with a continuously updated asset<br />
inventory, and having a full suite of tools<br />
to handle business-critical risks, such as<br />
credentials leakage, typo-squatting threats<br />
or intellectual property exposure, to fully<br />
prevent multi-vector cyber-attacks.<br />
"Organisations need to go beyond<br />
perimeter-centric defence and start thinking<br />
like attackers," says Charaudeau. "This means<br />
adopting a proactive posture and taking an<br />
outside-in approach, with vigilant monitoring<br />
of possible exposures in their extended<br />
external attack surface. Doing this will enable<br />
enterprises to fully maximise the value of their<br />
vulnerability management, and endpoint<br />
detection and response programs, and<br />
ensure issues can be remediated expediently<br />
before bad actors can take advantage of<br />
them."<br />
STEPHEN CAVEY, CO-FOUNDER<br />
& CHIEF EVANGELIST, GROUND LABS<br />
"The twin forces of globalisation and the<br />
explosion of connected technology have<br />
made it easy for anyone to do business<br />
anywhere. Now, business owners can<br />
transact with people across the world<br />
from the comfort of their own living rooms.<br />
The ease with which businesses now interact<br />
with customers and partners anywhere in<br />
the world can betray a real concern of being<br />
involved in international business: data<br />
compliance.<br />
"Over the last five years, global regulators<br />
have recognised this reality and are now<br />
putting stronger laws in place to protect their<br />
citizens' data. If you do business in a territory<br />
- however small the revenue or however<br />
quick the transaction - then you may be<br />
subject to their data protection regulations.<br />
In 2023, as international regulations settle<br />
into place, organisations will slowly begin<br />
to understand what they need to comply<br />
with and where they need to comply. Either<br />
they'll make appropriate changes or face the<br />
consequences from any number of regulatory<br />
regimes around the world.<br />
"As cyber-attacks continue and cybercriminals<br />
become ever more creative, cyberinsurance<br />
will become harder to attain in<br />
2023. Premiums will increase, requirements<br />
will get tougher and more businesses will<br />
see rejections for cyber insurance coverage.<br />
Companies will begin to understand that<br />
they must invest in protecting and managing<br />
the data from the ground up and not merely<br />
buy a cyber-insurance policy to protect<br />
against potential losses.<br />
"As international regulation ramps up<br />
around the world, organisations will be<br />
forced to question how much data they need<br />
to collect about individuals, in order to deliver<br />
their product of service. Previous years have<br />
been characterised by a hungry accumulation<br />
of data, with the hopes that it could be<br />
monetised or used to improve services later<br />
down the line. However, as international<br />
regulation locks into place around the world,<br />
organisations will be made to account for<br />
the individual types of data they collect and<br />
justify this on an ongoing basis."<br />
DAN MURPHY, DISTINGUISHED<br />
ARCHITECT, INVICTI SECURITY<br />
From a major ride-sharing company to a<br />
well-known entertainment giant, breaches<br />
that expose sensitive data are becoming<br />
commonplace, points out Invicti Security’s<br />
distinguished architect Dan Murphy.<br />
"Neither of these attacks was a complex<br />
12<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
2023 predictions<br />
zero-day exploit. They both relied on the<br />
weakest links of any software process:<br />
people.<br />
"Unfortunately, user error will dominate<br />
the next year of cybersecurity pitfalls.<br />
Because software is now an unknowable<br />
complexity where nobody understands<br />
every single line of code, it's difficult to<br />
predict what may happen in the event of<br />
a malicious hacker setting their sights on<br />
your organisation. For similar reasons, we'll<br />
continue seeing exploits of Log4Shell. While<br />
organisations aware of Log4Shell instances<br />
can remediate them relatively efficiently, the<br />
current concern is in those older, dustier<br />
systems without clear-cut owners.<br />
"If there's confusion around how a system<br />
works and no robust DevSecOps team, it's<br />
easy for malicious hackers to slip under the<br />
radar and cause chaos. Persistent threat<br />
actors are exploiting this vulnerability, using<br />
it as one of the many lockpicks they reach<br />
for when trying to discover if a website is<br />
compromisable. That said, things have<br />
gotten incrementally better. Large-scale<br />
breaches and vulnerabilities serve as a<br />
wake-up call for the InfoSec community,<br />
even prompting government guidance on<br />
what organisations should do to protect<br />
themselves from bad actors.<br />
"Communication at this level shows<br />
decision-makers that cybersecurity is worth<br />
prioritising. Organisations attempting to<br />
right the ship should look at the tactics of<br />
malicious hackers and use them for good.<br />
An example of this is DAST. DAST scanning<br />
uses those same techniques to deliver<br />
DevSecOps professionals an end-to-end<br />
view of security debt and direct-action<br />
items to best secure their web apps and<br />
prevent vulnerabilities from slipping<br />
through the cracks."<br />
JACQUES FOURIE, DIRECTOR OF<br />
INFORMATION SECURITY, KOCHO<br />
Following the rise of high-profile cyberattacks<br />
this past year, we should expect to<br />
see the following three trends in 2023,<br />
Fourie predicts:<br />
Enhanced disaster recovery. "The capacity<br />
to recover from attacks is often overlooked<br />
in favour of outright prevention, yet it is the<br />
businesses that adopt a 'when, not if' mindset<br />
that will escape the worst results of a cyberattack.<br />
Therefore, the ability to successfully<br />
reduce the impact radii of threats is key to<br />
successfully rebuilding after an attack. Thus,<br />
businesses that understand the need to<br />
bolster cyber security will begin by moving<br />
to more resilient architectures to be secure by<br />
design, rather than rely on disaster recovery<br />
sites where live replication of threats and<br />
backing up the compromised data because<br />
the backup platform is not security<br />
conscious."<br />
Deepened vendor scrutiny and<br />
consolidation. "Supply chain risk is impacting<br />
every industry. Uncertainty has businesses<br />
reflecting on what systems are already in<br />
place and whether they still meet demands.<br />
The drive for consolidation is being<br />
accelerated by maturing digital regulations,<br />
which places pressure on suppliers to prove<br />
they are compliant to remain competitive.<br />
Additionally, initiatives like Cyber Essentials -<br />
a government accreditation scheme for cyber<br />
security - are proving challenging for larger<br />
organisations to adhere to, despite being<br />
increasingly seen as fundamental to proving<br />
a basic secure strategy."<br />
Securing modern digital assets. "Many<br />
organisations are opting for serverless<br />
architectures, like Platform as a Service<br />
(PaaS), to ease the overhead of cloud system<br />
management. Yet traditional security<br />
monitoring struggling to keep up, and the<br />
risk of limited coverage and failure to spot<br />
attacks is leading more organisations to<br />
consider re-platforming their security<br />
monitoring services. To aid visibility for the<br />
SOC post cloud migration, we are seeing<br />
more advanced XDR tooling that supports<br />
Dan Murphy, Invicti Security: user error<br />
will dominate the next year of cybersecurity<br />
pitfalls.<br />
Jacques Fourie, Kocho: it is the businesses<br />
that adopt a 'when, not if' mindset that will<br />
escape the worst results of a cyber-attack.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> computing security<br />
13
2023 predictions<br />
PaaS, such as containers. Next generation<br />
XDR can take telemetry from assets like<br />
containers into a more modern Security<br />
Orchestration, Automation and Response<br />
(SOAR) platform. Tools such as these are<br />
becoming an increasingly critical function<br />
to support, secure and ultimately keep up<br />
with digital transformation."<br />
STEPHANIE BEST, DIRECTOR OF<br />
PRODUCT MARKETING, SALT SECURITY<br />
"2023 will be the year of API security. API<br />
traffic has increased 168% over the past year,<br />
with malicious traffic growing 117% in<br />
the same period. As business infrastructure<br />
increasingly moves towards digitalisation,<br />
API traffic, malicious and otherwise, will<br />
only continue to increase through 2023. If<br />
businesses are to protect themselves from<br />
the torrent of attacks coming their way,<br />
they must recognise the uniqueness of API<br />
security. Traditional security solutions, such<br />
as WAFs, API gateways and bot mitigation,<br />
simply aren't effective at protecting from<br />
most attacks aimed at APIs.<br />
"Attacks on APIs are typically 'low and slow',<br />
with attackers searching for unique business<br />
logic flaws for weeks or even months before<br />
they succeed. As these attacks aren't as overt<br />
as more traditional methods, they cannot be<br />
detected by security tools that are not APIspecific.<br />
What's more, basic security tools<br />
such as authentication, authorisation and<br />
encryption fail to meet the challenge of<br />
contemporary API security.<br />
"Businesses require deep, detailed context to<br />
understand and protect their API ecosystems<br />
- that means being able to distinguish<br />
normal API activity from anomalies amidst<br />
millions of API calls. Basic security tools just<br />
don't provide that context, leaving businesses<br />
at risk.<br />
"While it's not certain that businesses will<br />
wise up to the importance of API security,<br />
attacks on APIs will certainly increase.<br />
Just this year, Australian telco giant Optus<br />
suffered an API security incident with<br />
catastrophic results. The breach resulted<br />
directly from broken user authentication, the<br />
second biggest API vulnerability, according to<br />
the OWASP API Security Top 10.<br />
"Attackers know that they can easily exfiltrate<br />
data from unauthenticated APIs. With an API<br />
security platform able to provide continuous<br />
visibility in runtime and show the normal<br />
behaviours of APIs versus anomalies, this<br />
threat could have been identified before<br />
the attacker accessed the user data. If<br />
organisations don't learn from Optus's<br />
mistakes, 2023 will be riddled with major<br />
API security failures. In short, 2023 is either<br />
going to be the year of API security or API<br />
security incidents. The end result will be<br />
determined by whether businesses wise up<br />
to the need for API-specific security or<br />
continue to rely on old security solutions for<br />
a very modern problem.<br />
JOHN GOODACRE, DIRECTOR OF THE<br />
UKRI'S DIGITAL SECURITY BY DESIGN<br />
CHALLENGE AND PROFESSOR OF<br />
COMPUTER ARCHITECTURES AT<br />
MANCHESTER UNIVERSITY<br />
"As we head into 2023, the financial impact<br />
of cybercrime is heading towards the $10<br />
trillion mark, with no signs of slowing. As<br />
our world becomes ever more connected<br />
and dependent on technology, the<br />
traditional approach to cyber security<br />
of cleanliness and the rush to patch will<br />
continue to struggle to keep up. The<br />
doom-and-gloom headlines will continue<br />
to be written about data loss and a lack of<br />
resilience or trust from an ever-increasing<br />
breadth of cyber-attack across the digital<br />
world.<br />
"IT teams and users alike are already<br />
stretched to the limit, many acknowledging<br />
that they do not have the skills or time to<br />
keep up with the almost weekly attempted<br />
attacks and zero-day patches. Simply<br />
monitoring for and patching vulnerabilities<br />
that are discovered at the user level is not<br />
a battle that can be won by the defenders,<br />
especially when attackers only need to be<br />
right once to exploit a vulnerability.<br />
"The UK is seeking to do something about<br />
this to balance responsibility across the<br />
supply chain. Already in <strong>2022</strong>, we have seen<br />
the Government's PSTI Bill looking to ensure<br />
that consumer products are shipped more<br />
securely by default, placing more<br />
responsibility on the product manufacturer.<br />
"The UK Government is not stopping here,<br />
though. As part of the UK's National Cyber<br />
Strategy, there is now a focus on the underlying<br />
technology that our digital world is<br />
built upon, ensuring products are not only<br />
secured by default to help reduce the<br />
number of vulnerabilities, but also secured<br />
by design of the components and enabling<br />
technologies to help protect against the<br />
inevitable remaining vulnerabilities.<br />
"UK Research and Innovation's Digital<br />
Security by Design Programme, part of<br />
the National Cyber Strategy, has been<br />
redesigning from the ground up the way<br />
software interacts with hardware, so it can<br />
block the exploitation of around 70% of<br />
the ongoing discovered vulnerabilities<br />
by design, while also enabling software<br />
development new ways to maintain<br />
resilience and integrity. Working across<br />
government, industry and academia, the<br />
£300m programme has been distributing a<br />
prototype, with developers and researchers<br />
finding more ways to protect everything<br />
digital from cyber and operational incidents.<br />
"As we move into 2023, we will really start<br />
to see early examples for sectors where this<br />
innovative technology can reduce threats<br />
and block exploitation of vulnerabilities.<br />
Developers and IT teams will become more<br />
vocal, pressing for the day they can benefit<br />
from new hardware that can actively block<br />
exploitation of vulnerabilities and their need<br />
to chase the ever-increasing number<br />
of patches."<br />
14<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
ook review<br />
YOU AND YOUR DATA ARE THE PRODUCT<br />
THIS ARTICLE IS AN EDITED EXTRACT FROM THE PRIVACY MISSION: ACHIEVING ETHICAL DATA FOR OUR<br />
LIVES ONLINE, BY ANNIE MACHON (PUBLISHED BY WILEY, <strong>2022</strong>)<br />
Making money from<br />
selling people's data is now a wellknown<br />
business model, whether<br />
that data is contact information or browsing<br />
history. How do you think Facebook grew so<br />
exponentially and became so rich? By selling<br />
our data to ad companies. Any free service<br />
available online will probably be using our<br />
data as their product by selling it to thirdparty<br />
organisations. This means that each one<br />
of us who uses this technology has become<br />
the product and we are being data farmed.<br />
What I would like you to understand is that<br />
the big corporations treat us like battery hens.<br />
All the data we churn out is being used<br />
to generate profit for other people; as<br />
individuals, we do not see a penny of it.<br />
The General Data Protection Regulation<br />
(GDPR) legislation introduced in the EU in<br />
2016 was put in place in an attempt to rein<br />
in some of the most aggressive data-farming<br />
practices. While it is good in theory, it does<br />
not seem to be that effective in practice. As<br />
the United States has not followed suit, there<br />
is little to deter big American corporations<br />
from continuing how they always have when<br />
it comes to their data collection, storage and<br />
sharing methods.<br />
If you look at a list of the world's biggest<br />
companies in <strong>2022</strong>, you will see that it is<br />
dominated by tech firms. Apple, Microsoft,<br />
Alphabet (Google), Amazon, Tesla, Meta and<br />
Tencent are all featured at the time of this<br />
writing.1 How do you think many of those<br />
companies made their money? Using data -<br />
our data. Data is the new oil.<br />
The drive to commoditise our data has often<br />
been likened to the oil rush at the end of the<br />
nineteenth and beginning of the twentieth<br />
centuries, when many huge American<br />
corporate fortunes and monopolies were<br />
established. The tech giants are merely<br />
continuing this trend of using data to build<br />
their wealth and, thanks to their huge wealth<br />
advantage, they are able to manipulate the<br />
sector to ensure their continued dominance.<br />
As soon as a rival technology appears that<br />
could threaten their business model, they buy<br />
the firm out.<br />
Although it is referred to as our data, I want<br />
you to realise that it is much more than data.<br />
This is your life. We live so much of our lives<br />
online that your 'data' covers every aspect of<br />
you, from your thoughts, relationships,<br />
political beliefs or activism to your financial<br />
and health records. All of this information is<br />
online and it is all accessible. There is a huge<br />
blurring of lines between our physical lives<br />
and online lives, which is what makes us so<br />
vulnerable.<br />
Those of us who grew up in a world without<br />
the internet, and who very clearly remember<br />
that time, may have a greater awareness of<br />
some of these issues. But if you are part of<br />
the generation termed digital natives (broadly,<br />
anyone born from the 1990s onward), this<br />
has always been your reality and you may<br />
never have considered the underlying<br />
concepts surrounding your privacy and<br />
human rights. In fact, these days I would<br />
argue that the only privacy we have as<br />
individuals is what goes on inside our heads.<br />
1. 'Biggest companies in the world <strong>2022</strong>',<br />
FinanceCharts.com, accessed 4 May <strong>2022</strong>, available at:<br />
https://www.financecharts.com/screener/biggest.<br />
Annie Machon is an international public speaker, writer,<br />
media commentator and political campaigner. She has also<br />
appeared in award-winning films and TV documentaries.<br />
She is currently a Director of the World Ethical Data<br />
Foundation. Machon is a former MI5 intelligence officer, a<br />
European board member of the drug reform organisation,<br />
Law Enforcement Action Partnership and a member of the<br />
Organising Committee of the Sam Adams Associates for<br />
Integrity in Intelligence.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> computing security<br />
15
<strong>2022</strong> <strong>CS</strong> Awards<br />
English National Opera singers Alexander<br />
Wall (right) and Damien Carter in full flow.<br />
Will we, won't we? Guests wait to hear if they<br />
have claimed one of this year's coveted awards.<br />
https://flic.kr/s/aHBqjAaQnn<br />
Computing Security Awards:<br />
winners all the way!<br />
IT WAS ANOTHER MOMENTOUS NIGHT AT THE COMPUTING SECURITY AWARDS, WHERE THE <strong>2022</strong> FINALISTS<br />
GATHERED TO CELEBRATE THIS PRESTIGIOUS EVENT - WHILE HOPING TO CLAIM ONE OF THE TITLES<br />
What an atmosphere, what an<br />
occasion! The Computing Security<br />
Awards <strong>2022</strong> once again proved<br />
overwhelmingly what an enormous wealth of<br />
talent exits right across our industry. The<br />
winners were duly applauded by those who<br />
attended, but it was just as much about<br />
celebrating all those who made it to the final<br />
in the various categories, which were hotly<br />
contested. If the mood was already uplifting<br />
at this gala event, it was made even more<br />
so by the uplifting voices and presence of<br />
English National Opera singers Alexander<br />
Wall and Damien Carter. They enjoyed a well<br />
deserved ovation and chorus of ‘encores’ at<br />
the end of their session. It only remains for<br />
Computing Security magazine to offer its<br />
warmest congratulations to each and every<br />
one of the companies and individuals who<br />
made it to the <strong>2022</strong> finals. And, of course,<br />
we look forward to seeing you all again for<br />
our next awards in 2023!<br />
You can see all of the <strong>2022</strong> winners here.<br />
https://computingsecurityawards.co.uk<br />
And here’s a taster of the event itself.<br />
https://youtu.be/-QGD7r5cpv0<br />
16<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
<strong>2022</strong> <strong>CS</strong> Awards<br />
THE <strong>2022</strong> WINNERS:<br />
Email Security Solution of the Year:<br />
Libraesva<br />
Anti Malware Solution of the Year:<br />
WatchGuard<br />
Incident Response & Investigation Security Service<br />
Provider of the Year:<br />
BlueVoyant<br />
Network Security Solution of the Year:<br />
Rohde & Schwarz Cybersecurity<br />
Encryption Solution of the Year:<br />
VIPRE Security<br />
Advanced Persistent Threat (APT) Solution of the Year:<br />
Gatewatcher<br />
Data Loss Prevention Solution of the Year:<br />
CoSoSys<br />
Cyber Security Compliance Award:<br />
Xcina Consulting<br />
AI and Machine Learning Based Security Solution of the<br />
Year:<br />
Fortinet<br />
Identity and Access Management Solution of the Year:<br />
SecurEnvoy<br />
Anti Phishing Solution of the Year:<br />
Metacompliance<br />
Secure Data & Asset Disposal Company of the Year:<br />
Gigacycle<br />
Cloud-delivered Security Solution of Year:<br />
Cyderes<br />
New Cloud-delivered Security Solution of the Year:<br />
Hornetsecurity<br />
Mobile Security Solution of the Year:<br />
Jamf<br />
Penetration Testing Solution of the Year:<br />
Kroll<br />
Breach and Attack Simulation Solution of the Year:<br />
SimSpace<br />
Data Protection as a Service Provider of the Year<br />
Veritas<br />
Remote Monitoring Security Solution of the Year:<br />
Zyxel<br />
Security Software Solution of the Year:<br />
Jamf<br />
Security Hardware Solution of the Year<br />
Arcserve<br />
New Security Hardware Solution of the Year<br />
Rohde & Schwarz Cybersecurity<br />
Security Education and Training Provider of the Year:<br />
Metacompliance<br />
Web Application Firewall of the Year:<br />
Rohde & Schwarz Cybersecurity<br />
Threat Intelligence Award:<br />
AT&T Cybersecurity<br />
Software as a Service (SaaS) Backup and Recovery<br />
Provider of the Year:<br />
Veritas<br />
Security Reseller of the Year:<br />
Cyderes<br />
Security Distributor of the Year:<br />
Brigantia<br />
Enterprise Security Solution of the Year:<br />
BlueVoyant<br />
SME Security Solution of the Year:<br />
VIPRE Security<br />
Individual Contribution to CyberSecurity Award:<br />
Robert O'Brien, Metacompliance<br />
Cyber Security Customer Service Award:<br />
Metacompliance<br />
Security Service Provider of the Year:<br />
Brookcourt Solutions<br />
Security Project of the Year - Public Sector:<br />
Swivel Secure & Durham County Council<br />
Security Project of the Year - Private Sector:<br />
VIPRE Security & Lodders<br />
Security Innovation Award<br />
BIO-key<br />
Editor's Choice:<br />
Veritas<br />
One to Watch Security - Product:<br />
Gatewatcher - AionIQ<br />
One to Watch Security - Company:<br />
BlueVoyant<br />
Security Company of the Year:<br />
Shearwater Group<br />
New Security Software Solution of the Year:<br />
GeoLang<br />
www.computingsecurity.co.uk <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> computing security<br />
@<strong>CS</strong>MagAndAwards<br />
17
security insights<br />
WHERE DOES YOUR SECURITY CONFIDENCE<br />
COME FROM? AND IS IT REALLY ENOUGH?<br />
PAUL HARRIS, MANAGING DIRECTOR AT PENTEST LIMITED, SHOWS HOW CONFIDENCE CAN<br />
BE YOUR INFORMATION SECURITY SECRET WEAPON. IT JUST HAS TO BE THE RIGHT TYPE<br />
In a world where nothing is 100% secure<br />
and malicious threats have the advantage in<br />
terms of time, no constraints on resources<br />
and no ethical barriers, we need to accept<br />
that 'perfect' security isn't realistic. Instead,<br />
organisations need to strive to achieve a high<br />
level of confidence in their security efforts,<br />
within the resource and budget limitations<br />
they have. By doing so, they help keep<br />
themselves protected against most of the<br />
threats they face.<br />
Having confidence in your information<br />
security is a goal every organisation should aim<br />
towards. However, it's important to recognise<br />
that not all confidence is created equal.<br />
Confidence and competence aren't always<br />
aligned; confidence certainly needs to be more<br />
than a feeling and misplaced confidence can<br />
be dangerous. So, how do you achieve (the<br />
right kind of) confidence in your information<br />
security?<br />
ADOPT A ZERO-TRUST APPROACH<br />
Zero-trust seems to be the buzzword of the<br />
day when it comes to information security.<br />
The idea being that every user needs to be<br />
authenticated, authorised and validated before<br />
being granted access. Basically, are we sure<br />
the user is who they say they are?<br />
This same approach, questioning<br />
everything and gaining proof,<br />
can be applied to all other areas<br />
concerning your security. Take,<br />
for example, external software<br />
providers. Many suppliers like to<br />
shout about the security benefits of<br />
their products, with terms like 'realtime<br />
A.I detection' or 'military grade<br />
security' used to instil a feeling of<br />
confidence in the customer's mind.<br />
But what do the claims really mean?<br />
Can they be backed up? What risks<br />
do you introduce in adopting this<br />
software? These are questions that<br />
organisations need to be asking<br />
themselves and their suppliers, helping<br />
build security confidence around these areas.<br />
The same approach can be used internally.<br />
For example, companies may have an internal<br />
software development team, and, in many<br />
cases, security checks will fall under their<br />
remit. But do developers have the right skillset<br />
to test security in a robust manner, and could<br />
there be a danger of 'marking their own<br />
homework'?<br />
By asking questions, challenging claims, and<br />
seeking proof, you start to build confidence<br />
that your defences are as strong as they can<br />
be, across all areas of your business.<br />
PUT YOUR CONFIDENCE TO THE TEST<br />
So, you've asked questions, challenged the<br />
claims and sought the proof you need. You're<br />
now confident that your security is robust<br />
enough to keep you secure against most<br />
threats. But how do you know your efforts<br />
have been truly effective? You need to put<br />
this confidence to the test.<br />
Having an independent expert, such as a<br />
penetration tester, compliance auditor or risk<br />
management consultant, assess your work is<br />
always a daunting prospect; it's completely<br />
understandable, but those with confidence<br />
should relish the opportunity. When you have<br />
this mindset, independent testing is a win-win<br />
situation. Think about it - either the test comes<br />
back with little to report, validating your<br />
efforts, or it highlights issues - issues that<br />
you can then use to improve upon.<br />
It's this mindset that sets apart the security<br />
great from the security good. They don't see<br />
testing as a criticism of their work, rather<br />
a benchmark for their efforts, a chance to<br />
improve and an opportunity to strengthen<br />
their security confidence further.<br />
So, the question you need to ask yourself is:<br />
how confident are you in your information<br />
security confidence?<br />
18<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
deepfakes<br />
THE DYSTOPIAN WORLD OF DEEPFAKES<br />
BBC'S RECENT DRAMA, 'THE CAPTURE', WAS AN ALARMING TAKE ON THE GROWING THREAT<br />
OF DEEP FAKES. WE ASK MATT LEWIS, COMMERCIAL RESEARCH DIRECTOR AT NCC GROUP,<br />
TO CONSIDER WHAT THREATS THESE MIGHT POSE IN THE 'REAL WORLD'<br />
Recently, we have seen how deepfake<br />
technology has become more<br />
sophisticated and readily available.<br />
The BBC recently released a second series of<br />
UK TV series 'The Capture', a thriller exploring<br />
the use of deepfakes for political deception<br />
and criminal framing, demonstrating the<br />
impact deepfakes are capable of making<br />
in day-to-day life.<br />
Within the series, deepfake technology is<br />
used to fabricate a statement from a British<br />
politician whereby they announce a major<br />
policy change regarding Chinese artificial<br />
intelligence technology. This mirrors<br />
something that's already happened in<br />
real life with Ukrainian President Volodymyr<br />
Zelensky, where he was portrayed to be<br />
surrendering in the country's conflict with<br />
Russia.<br />
Another sinister and sadly fatal case relating<br />
to deepfakes came earlier this year, with a<br />
young Egyptian girl taking her own life after<br />
she was allegedly blackmailed with deepfake<br />
pornography, created using her imagery.<br />
In early 2020, NCC Group partnered with<br />
University College London (UCL) on a<br />
research project investigating the capabilities<br />
of various free and open-source deepfake<br />
toolkits. It has now been over two years<br />
since this research and, since then, deepfake<br />
technology has become more sophisticated<br />
and is used more readily. So, let's revisit<br />
today's deepfake landscape, looking at<br />
technological developments and societal<br />
implications.<br />
HOW CAN DEEPFAKE TECHNOLOGY<br />
BE USED IN THE REAL WORLD?<br />
The technology of deepfakes has advanced<br />
and there are now many online apps<br />
available for users to create and play around<br />
with it. Improvements to leading opensource<br />
deepfake toolkits, such as DeepFaceLab, have<br />
also continued, rendering the technology<br />
more performant and realistic.<br />
As well as the technology being more<br />
readily available, we are also seeing more<br />
real-time generation of deepfakes. This<br />
includes hooking up to a computer's<br />
webcam to allow impersonation as other<br />
people in real time - for example, on video<br />
conferencing calls. 'The Capture' also does a<br />
good job of demonstrating this, as in series<br />
two a British politician's likeness is digitally<br />
recreated using deepfake technology, whilst<br />
he is supposedly live on TV, making it look<br />
and sound like he's said something else.<br />
HOW CAN WE PREPARE THE WORLD<br />
AGAINST DEEPFAKES?<br />
There is an urgent need for deepfake<br />
detection and blocking. More deepfakes are<br />
20<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
deepfakes<br />
being used in harmful or offensive contexts<br />
by all level of threat actor, from disgruntled<br />
lover seeking revenge, all the way up to<br />
organised crime groups and hostile national<br />
states.<br />
In 2021, the European Parliamentary<br />
Research Service (EPRS) released a study on<br />
tackling deepfakes in European policy. The<br />
study summarised a range of categories of<br />
risks associated with the technology, ranging<br />
from psychological, financial and societal<br />
harm. It includes risks from extortion,<br />
bullying and defamation, to stock-price<br />
manipulation, election interference and<br />
damage to national security.<br />
Various approaches are emerging from<br />
academia on deepfake detection and<br />
blocking, such as active illumination of a<br />
person's face during a video call and selfblended<br />
images. However, it can take time<br />
for new research to find its way into<br />
commercial and mainstream use; in the<br />
meantime, deepfake technology might find<br />
a way to bypass detection mechanisms.<br />
Propagation of deepfakes heavily relies on<br />
social media sharing. With this in mind,<br />
social media platforms ought to provide<br />
a level of deepfake detection and blocking.<br />
Facebook (Meta AI) has been researching<br />
methods to detect deepfakes and identify<br />
where they originate.<br />
When it comes to Business Identity<br />
Compromise (BIC), in addition to detection,<br />
businesses may also need to consider<br />
changes to current approval and workflow<br />
process. For example, where a process may<br />
allow for execution of a crucial operation<br />
or high-end financial transaction, requiring<br />
a two-person rule (if performing over video<br />
conferencing) might make it that much<br />
harder for a successful deepfake attack.<br />
Similarly, requiring an in-person physical<br />
presence, particularly now that most global<br />
pandemic restrictions are lifted, may be a<br />
necessity to mitigate the risks in this domain.<br />
In terms of advice on how to combat<br />
deepfakes, using state-of-the-art anti-fake<br />
technology, good security procedures and<br />
watermarking genuine videos should always<br />
be top of the list when looking at identifying<br />
and blocking deepfakes. Other, more soft,<br />
measures are to ensure employees and family<br />
are familiar with deepfakes, update and use<br />
different/strong passwords, perform regular<br />
backups and updates of data; also, using<br />
a good security package can always provide<br />
a barrier against deepfakes.<br />
DEEPFAKE LEGISLATION AND<br />
REGULATION<br />
Deepfakes pose many potential risks, such as<br />
manipulation of civil discourse, interference<br />
with elections and national security, alongside<br />
the erosion of trust in journalism and public<br />
institutions. It is therefore essential that<br />
legislation surrounding deepfakes is reviewed<br />
constantly, as this technology grows ever<br />
more popular.<br />
The UK law currently does not have a<br />
specific set of legislation for the use of<br />
deepfakes. However, there are established<br />
laws that may be more applicable when<br />
attempting to look at preventing deepfakes<br />
being used in an unwanted or manipulative<br />
way.<br />
It is also worth noting that, whilst specific<br />
legislation and regulation around deepfake<br />
abuse won't stop motivated attackers, it is still<br />
necessary to ensure that people abusing the<br />
technology can and will be identified and<br />
prosecuted for doing so.<br />
Despite the demand for legislation in this<br />
domain, concerns exist on a lack of progress<br />
across the EU and UK. The National Law<br />
Review writes: "In the UK, the answer is that<br />
English law is wholly inadequate at present<br />
to deal with deepfakes. The UK currently has<br />
no laws specifically targeting deepfakes and<br />
there is no 'deepfake intellectual property<br />
right' that could be invoked in a dispute.<br />
Similarly, the UK does not have a specific law<br />
protecting a person's 'image' or 'personality.<br />
It's created circumstances where people living<br />
in the UK will need to rely on a combination<br />
of different rights and laws, in order to try<br />
and protect themselves against deepfakes.<br />
However, these laws may currently not go far<br />
enough to protect those dealing with the<br />
malicious use of their image through<br />
deepfakes; as ever with rapidly advancing<br />
technology, we must ensure these advances<br />
do not outpace legislative and regulatory<br />
frameworks protections.<br />
Now we know deepfakes are here for good,<br />
how do we ensure they are safe to use?<br />
It's clear deepfakes are no longer confined<br />
to shows like the BBC's 'The Capture'. The<br />
technology is here to stay and it being used<br />
in the real world, continuing to advance in<br />
its ease of use, accessibility and realism.<br />
We therefore need urgent and continued<br />
research on deepfake detection and blocking<br />
mechanisms, whilst legislation and regulation<br />
need to catch up, in order to prevent and<br />
prosecute individuals abusing the technology.<br />
Matt Lewis,<br />
NCC Group.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> computing security<br />
21
data management<br />
YOU AND YOUR DATA ARE THE PRODUCT<br />
WHY IS IT SO IMPORTANT FOR BUSINESSES TO UNDERSTAND THE<br />
SENSITIVE DATA THEY ARE WORKING WITH? NICK EVANS, GEOLANG'S<br />
SALES AND MARKETING MANAGER, REVEALS WHAT COULD HAPPEN<br />
BY NOT HAVING A SOLID PLAN<br />
The amount of sensitive data your<br />
business stores is only increasing<br />
in size - and one of your major<br />
responsibilities is managing it. As more<br />
tools are used to manage everyday<br />
business, both on-prem and cloud,<br />
the amount of data being stored is just<br />
getting bigger! While lots of the data<br />
you collect may be completely harmless,<br />
critical, and sensitive information hides<br />
among it, often in plain sight.<br />
Anywhere you have data, you certainly<br />
also have sensitive data. To manage your<br />
sensitive data, you first must discover it.<br />
Solutions like GeoLang's Data Discovery<br />
tool help you to take the first step in<br />
maintaining your increasing amounts of<br />
sensitive data. But why is sensitive data<br />
protection more important than ever?<br />
What are some places your sensitive<br />
data could be hiding?<br />
WHY SHOULD WE PROTECT<br />
OUR SENSITIVE DATA?<br />
There are heavy fines issued in relation<br />
to Sensitive data being leaked through<br />
breaches and it's now vitally important to<br />
protect against any unauthorised access.<br />
With a heightened focus now on data<br />
compliance regulations and the potential<br />
massive damage to your reputation,<br />
intellectual property, efficiency, and<br />
bottom line - if you're not locating and<br />
classifying your data, your organisation<br />
is at risk.<br />
RISE IN PRIVACY REGULATIONS<br />
It is not just the public that cares how<br />
their details and information are being<br />
captured and used by businesses, but a<br />
massive focus from legislators worldwide.<br />
Since 2018 and the creation of Europe's<br />
General Data Protection Regulation (GDPR)<br />
and the California Consumer Privacy Act<br />
(CCPA) in 2020, many businesses have<br />
woken up to the need to manage their<br />
sensitive data better. With more than<br />
100 countries now having their own data<br />
privacy laws, it's a fact that regulations,<br />
like your sensitive data, are increasing all<br />
the time.<br />
The EU GDPR sets a maximum fine of<br />
€20 million (about £18 million) or 4%<br />
of annual global turnover - whichever is<br />
the greater - for businesses that do not<br />
comply with GDPR rules and fines for<br />
violating the CCPA can reach $7,500. With<br />
the evolution and addition of new privacy<br />
laws and regulations, remaining compliant<br />
is a constant challenge.<br />
Sensitive data protection allows you to<br />
sort out the confusion behind data privacy<br />
regulations and effectively deploy your<br />
limited resources so you can focus on<br />
other critical business needs.<br />
YOUR BRAND REPUTATION -<br />
IT'S ALL YOU HAVE GOT!<br />
Your systems, or 'Data Silos', hold extensive<br />
data about your employees, customers,<br />
and others with whom you do business -<br />
in essence, any data that relates to a<br />
person (e.g. Names, home addresses,<br />
payment card information, driving licence<br />
numbers, email addresses and other<br />
personal information).<br />
When collecting information from<br />
people, you accept the responsibility for<br />
protecting their information. Failing to do<br />
so results in severe reputation damage,<br />
but also a potential loss of business. There<br />
are many cases where a business that has<br />
suffered a public data leak has then gone<br />
on to see a decline in sales figures.<br />
BLOW TO CONFIDENCE<br />
This is due to the trust your customers had<br />
in your brand being damaged. The blow<br />
to consumer confidence can affect stock<br />
prices for months or years.<br />
22<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
data management<br />
TIME AND COST TO RECOVER<br />
FROM A DATA BREACH<br />
Data and privacy breaches continue to<br />
grow with more than 33 billion records<br />
projected to be stolen in 2023 - a 175%<br />
increase over 2018. According to IBMs<br />
latest 'Cost of a Data Breach Report', the<br />
global average cost of a cybersecurity<br />
breach is £3.41 million and rising. In the<br />
US, the average is much higher, $8.19<br />
million. The same report states that the<br />
average time a company takes to identify,<br />
contain, and recover from a breach is 280<br />
days. Implementing a data protection plan<br />
before a data incident (or breach) takes<br />
place is vital to a business's ability to<br />
survive and thrive. Without a solid data<br />
protection plan, you are driving around<br />
uninsured, with bald tyres. With no<br />
headlights. In the dark. Into oncoming<br />
traffic.<br />
LOCATING SENSITIVE DATA -<br />
THE RESOURCING CHALLENGE<br />
While businesses understand the need<br />
to control, manage, and reduce their<br />
sensitive data footprints, many struggle to<br />
keep up. The sheer amount of data, along<br />
with its huge ranges of locations - some<br />
you may not even know about - can seem<br />
like an impossible challenge, especially<br />
when a business's resources are already<br />
thinly spread. Many SMBs do not have<br />
an IT resource and outsource that role.<br />
Sensitive data can be anywhere across<br />
structured, unstructured, and cloud<br />
locations and many companies only<br />
point resources at protecting the cloud,<br />
while giving less attention to endpoints<br />
(Laptops, Desktops, File servers). In fact,<br />
employee machines, servers, and even<br />
printers could store sensitive information.<br />
Covid-19 and the new home working<br />
culture has only increased the risks as<br />
employees work remotely. Some data<br />
privacy management software is designed<br />
to find, classify, and protect sensitive<br />
information only in certain kinds of<br />
locations. However, just like any defence,<br />
your data security plan is only as strong<br />
as its weakest link.<br />
SEARCH EVERYWHERE.<br />
FIND EVERYTHING<br />
GeoLang's Data Discovery tool allows<br />
organisations to discover sensitive data<br />
and reduce privacy risks whilst preparing<br />
for the future - quickly and easily. With<br />
GeoLang, you can discover and classify<br />
SaaS, cloud, on-premises and endpoint<br />
sensitive data throughout your business.<br />
The Data Discovery solution offers automated<br />
data location support for Cloud<br />
and On-Prem set-ups of:<br />
Atlassian Confluence, Jira and Bitbucket<br />
Microsoft Office 365<br />
Google Workspace<br />
Hyland Alfresco<br />
Endpoints (Windows, Mac and Linux)<br />
In addition to finding your sensitive data,<br />
GeoLang Data Discovery can reduce<br />
potential exposure from data breaches by<br />
proactively prompting data owners to<br />
remove or remediate sensitive data from<br />
nonessential locations. Since you don't<br />
know what you don't know you need the<br />
ability to trust a tool that looks<br />
everywhere.<br />
Keep in mind your organisation's ongoing<br />
need for additional computers, new<br />
software and a growing cloud footprint.<br />
Companies scanning and remediating<br />
terabytes of data today will need to plan<br />
for petabytes of data tomorrow. Where<br />
is the sensitive data that could threaten<br />
your organisation, employees, compliance<br />
with privacy regulations and customer<br />
reputation? You can Schedule a demo of<br />
GeoLang Data Discovery to find out.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> computing security<br />
23
ansomware<br />
RANSOMWARE ON THE RAMPAGE<br />
WITH 24% OF BUSINESSES IDENTIFIED IN RECENT RESEARCH AS HAVING BEEN VICTIMS TO AN ATTACK,<br />
THE OMENS FOR THE YEAR AHEAD LOOK WORRYING. HOW CAN THEY START FIGHTING BACK?<br />
Nearly a quarter of businesses have<br />
suffered a ransomware attack,<br />
with a fifth occurring in the past 12<br />
months, according to an annual report<br />
from cybersecurity specialist Hornetsecurity.<br />
The company's <strong>2022</strong> Ransomware Report,<br />
which surveyed more than 2,000 IT leaders,<br />
discloses that 24% have been victims of<br />
a ransomware attack, with one in five<br />
(20%) attacks happening in the last year.<br />
Cyberattacks are certainly happening<br />
on a very wide scale with ever-increasing<br />
frequency. Last year's ransomware survey by<br />
Hornetsecurity revealed one in five (21%)<br />
companies experienced an attack; this year,<br />
it rose by 3% to 24%.<br />
"Attacks on businesses are increasing,<br />
and there is a shocking lack of awareness<br />
and preparation by IT pros," states<br />
Hornetsecurity CEO Daniel Hofmann.<br />
"Our survey shows that many in the IT<br />
community have a false sense of security.<br />
As bad actors develop new techniques,<br />
companies like ours have to do what it<br />
takes to come out ahead and protect<br />
businesses around the world."<br />
The <strong>2022</strong> Ransomware Report highlights<br />
a lack of knowledge on the security available<br />
to businesses. For example, a quarter (25%)<br />
of IT professionals either don't know or<br />
don't think that Microsoft 365 data can be<br />
impacted by a ransomware attack. Just as<br />
worryingly, 40% of IT professionals that use<br />
Microsoft 365 in their organisation admitted<br />
they do not have a recovery plan, should their<br />
Microsoft 365 data be compromised by a<br />
ransomware attack.<br />
"Microsoft 365 is vulnerable to phishing<br />
attacks and ransomware attacks, but, with<br />
the help of third-party tools, IT admins can<br />
back up their Microsoft 365 data securely and<br />
protect themselves from such attacks," adds<br />
Hofmann. Industry responses showed the<br />
widespread lack of preparedness from IT<br />
professionals and businesses. There has been<br />
an increase in businesses not having a disaster<br />
recovery plan in place, if they do succumb to<br />
the heightened threat of a cyberattack.<br />
In 2021, 16% of respondents reported<br />
having no disaster recovery plan in place. In<br />
<strong>2022</strong>, this grew to 19%, despite the rise in<br />
attacks. The survey also showed that more<br />
than one in five businesses (21%) that were<br />
attacked either paid up or lost data. Hackers<br />
have an incentive to run these ransomware<br />
attacks, because there's a decent chance that<br />
they'll get a payday - 7% of IT professionals<br />
whose organisations were attacked paid the<br />
ransom, while 14% admitted that they lost<br />
data to an attack.<br />
Hofmann concludes: "Interestingly, 97% of<br />
pros are moderately to extremely confident in<br />
their primary protection method, even if they<br />
don't use many of the most effective security<br />
measures available, such as immutable<br />
storage and air-gapped off-site storage. This<br />
tells us that more education is needed in the<br />
field and we're committed to this cause." You<br />
can read more at this link: hornetsecurity's<br />
ransomware attacks survey.<br />
FAST AND COST-EFFECTIVE RECOVERY<br />
Data backup alone is not enough to protect<br />
you, cautions Florian Malecki, executive vice<br />
president marketing, Arcserve. "Companies<br />
should also plan to recover data quickly and<br />
cost effectively, following a ransomware<br />
attack. With a well-thought-out recovery<br />
plan in place, you may be able to restore<br />
the exact version of a file or folder following<br />
a data loss properly and quickly."<br />
24<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
ansomware<br />
Immutable storage should be a vital<br />
component of your backup and recovery<br />
plan to allow you to safeguard your data,<br />
even if a ransomware attack victimises<br />
you, he states. "An immutable solution<br />
continually protects your data by taking<br />
snapshots every 90 seconds. These<br />
snapshots make it possible for you to go<br />
back to specific points in time before an<br />
attack and recover entire file systems in<br />
a matter of minutes. As a result, even if<br />
an attack is successful, your information<br />
will be quickly and easily recoverable to<br />
a very recent point in time."<br />
Because your backup data is immutableyour<br />
data can't be altered in any way by<br />
ransomware - there will always be a series<br />
of recovery points, ensuring your data<br />
remains protected, argues Malecki. "This<br />
immutability can also bridge the security<br />
and the operational infrastructure teams,<br />
which have traditionally been siloed. That<br />
means these two groups can speak the<br />
same language and work together in the<br />
face of ransomware threats.<br />
"If the worst happens and you fall victim to<br />
an attack, being in control of your recovery<br />
would be highly comforting to everyone<br />
involved in your organisation. Your data<br />
protection system should be able to deliver<br />
orchestrated recovery with a single click. In<br />
a ransomware attack, you should be able to<br />
recover confidently by safely spinning up<br />
copies of physical and virtual systems onsite<br />
and offsite in minutes-not hours or days.<br />
"An ideal data protection system will also<br />
use analytics to identify frequently used data<br />
that a business should always back up and<br />
less vital data that doesn't have to be. This<br />
system gives organisations an intelligent,<br />
tiered data architecture that provides rapid<br />
access to mission-critical information."<br />
DAMAGING IMPACT<br />
Ransomware attacks are at an all-time high,<br />
with 2021 receiving the largest ransomware<br />
payout by an insurance company ($40<br />
million, according to Matthew Woodward),<br />
and have witnessed a 94% increase from<br />
2021 to <strong>2022</strong> on US healthcare organisations,<br />
states Kyle Mitchell, commercial sales<br />
director for Whitaker Brothers. "Damage from<br />
ransomware can be costly for businesses,<br />
as recovering data can be time-consuming,<br />
often costing businesses money to resolve."<br />
To avoid any possible ransomware attack,<br />
he offers practical tips on preventing malware<br />
from reaching your organisation's devices.<br />
Analyse suspicious emails for any<br />
unorthodox attachments - ransomware<br />
can find its way onto your device through<br />
suspicious emails and email attachments.<br />
"These can often be found through emails<br />
that contain strange requests for information,<br />
scaremongering tactics and uncharacteristic<br />
requests from known associates. Ensure that<br />
you read a suspicious email carefully, paying<br />
close attention to the sender. If you are<br />
unsure if the email is trustworthy, avoid<br />
opening any attachments," says Mitchell.<br />
Create regular backups of your files -<br />
"Regular backups for your organisation are<br />
ideal to bounce back from a ransomware<br />
attack and should be created offline, so that<br />
digital attackers cannot target your data."<br />
Keep systems up to date - "Making sure that<br />
systems are up to date is an effective way to<br />
close all essential security gaps that digital<br />
attackers often try to exploit."<br />
Apply an Intrusion Detection Systems (IDS) -<br />
this compares network traffic logs to<br />
signatures that identify known malicious<br />
behaviour online.<br />
Actively inspect content - you can reduce<br />
the likelihood of ransomware attacks actually<br />
reaching your devices by actively inspecting<br />
the content. "This means filtering your files<br />
to only allow file types you want to receive,<br />
blocking websites that are known to be<br />
malicious, and using signatures to block<br />
known malicious code," he adds.<br />
Train your team - an effective security<br />
awareness training programme within your<br />
organisation can be crucial in stopping<br />
ransomware attacks.<br />
NATIONAL INFRASTRUCTURE TARGETED<br />
Meanwhile, two-thirds (65%) of Critical<br />
National Infrastructure (CNI) has fallen victim<br />
to a cyberattack over the past 12 months -<br />
statistics unveiled in new research from global<br />
cybersecurity company Forcepoint. The report<br />
examines the pressure CNI cybersecurity<br />
professionals face, as they balance the rapid<br />
pursuit of digital transformation with the<br />
cyber threat landscape.<br />
"Ransomware is perceived by cybersecurity<br />
professionals to present the greatest risk to<br />
CNI organisations," says Forcepoint. "This<br />
is unsurprising, given 57% report that their<br />
organisation fell victim to a ransomware<br />
attack in the last year, of whom 72%<br />
admitted to paying the ransom."<br />
When asked what aspects of the current<br />
cybersecurity threat landscape cause CNI<br />
cybersecurity professionals to worry the most,<br />
the challenge of managing more complex<br />
security solutions was superseded only by<br />
concerns that the Russia-Ukraine war could<br />
be increasing the risk of cyberattacks.<br />
And Forcepoint further states: "The rapid<br />
digital transformation of both IT and OT<br />
[operational technology] environments is<br />
compounding the challenge that CNI<br />
cybersecurity professionals are facing. When<br />
asked about its impact on their organisation,<br />
the most cited concern was the need to<br />
secure new technologies, because they were<br />
new to the organisation, as well as being<br />
difficult to secure properly."<br />
CNI cybersecurity professionals also believe<br />
a cyberattack on CNI could lead to disruptive<br />
behaviour amongst the general public, which<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> computing security<br />
25
ansomware<br />
Dan Turner, Forcepoint: cybersecurity<br />
professionals in CNI work in a climate<br />
of high risk and diverse threats.<br />
Daniel Hofmann, Hornetsecurity: attacks<br />
on businesses are increasing, yet there's a<br />
shocking lack of awareness and preparation<br />
by IT pros.<br />
increases the difficulty of mitigating or<br />
controlling the impact of an attack. In the US,<br />
the greatest concern was of a power outage,<br />
whereas cybersecurity professionals in the<br />
UK predict that disruption to personal<br />
banking would have the greatest impact."<br />
The threat of disruption is also amplified<br />
by what cybersecurity professionals believe<br />
motivates cyberattacks on CNI. The greatest<br />
threats were perceived to be from cyber<br />
gangs demonstrating their capabilities, acts<br />
of political retaliation, acts of hacktivism and<br />
acts of cyber warfare.<br />
"Unfortunately, the research has also found<br />
many CNI cybersecurity professionals are<br />
feeling the pressure of this high-pressure,<br />
high-complexity environment. Feelings of<br />
stress, anxiety and burnout are affecting over<br />
one-third of all CNI cybersecurity professionals<br />
[35%, 39% and 36% respectively]. "This is<br />
impacting their professional experience,<br />
with two-fifths of cybersecurity professionals<br />
reporting that the pressure to secure CNI<br />
has led them to have a low morale at work<br />
(40%), rising to 51% of UK employees.<br />
Worryingly, it is also affecting their personal<br />
well-being."<br />
Adds Dan Turner, vice president at<br />
Forcepoint: ""Understanding the challenges<br />
our cybersecurity professionals in CNI are<br />
facing helps us find better solutions to<br />
alleviate the burden on them. They work in<br />
a climate of high risk, diverse threats when<br />
rapid adoption of new technologies changes<br />
security parameters all the time. Knowing<br />
what motivates and worries our industry is<br />
key - it helps us help them in their efforts to<br />
ensure no new threat or technology puts<br />
our essential services at risk of disruption,<br />
so which, in turn, allows us to secure a safer<br />
and more sustainable future for everyone."<br />
BIGGEST CHALLENGES TO OVERCOME<br />
"Securing an expanding digital footprint<br />
is one of the biggest challenges facing<br />
companies," points out Sam Curry, chief<br />
security officer, Cybereason. "With ransomware<br />
attacks surging, the clock starts to<br />
immediately tick after ransomware has<br />
executed. And when the ransom itself is<br />
received, that is a time of high adrenaline,<br />
confusion and panic for most. This is actually<br />
by design on the part of the attackers.<br />
They attack, often, at night, on holidays<br />
and weekends to maximise pressure, and,<br />
therefore, the chance of poor decisionmaking<br />
and capitulation. According to a<br />
recent Cybereason study on ransomware<br />
attacks, more than 60% of organisations<br />
lack preparedness on holiday and weekends,<br />
and it limits their ability not only to assess<br />
the risk, but stop it as well. Hackers know<br />
this and they attack accordingly.<br />
"Companies can't pay their way out of<br />
ransomware and many decide they won't<br />
pay," adds Curry. "Hopefully, they are backing<br />
up data, but how quickly can the data be<br />
operational? If a company isn't backing up<br />
their data and still won't pay, that decision<br />
comes with weathering the pain of rebuilding.<br />
And what other trade-offs come into<br />
play? Can services continue? Is public safety<br />
or human life at risk? What is the cost of<br />
rebuilding? How long will it take to rebuild<br />
etc? There is the arithmetic of recovery, the<br />
risk equation, the truly compelling questions<br />
like not putting human life at risk and then<br />
there is also the ethical question of funding<br />
criminal activity."<br />
TICKING TIMEBOMB<br />
Given the massive strides that the security<br />
industry has been making in developing<br />
sophisticated network protection technology,<br />
this raises a vital question according to Mark<br />
Oakton, CEO/Consulting CISO, Infosec<br />
Partners: "Why is ransomware still able<br />
to keep CISOs awake at night and send<br />
shockwaves through the corporate world's<br />
boardrooms?" There are many reasons, he<br />
believes, including a reliance on outdated<br />
technology, combined with poor staff<br />
awareness and training - but ultimately the<br />
answer lies in human nature. "Ransomware<br />
attacks are typically the result of a simple<br />
26<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
Secure your<br />
modern<br />
workplace<br />
with awardwinning<br />
solutions<br />
Do your employees<br />
love their work technology<br />
and does your organisation<br />
trust that every device is safe?<br />
Jamf is here to help your organisation by:<br />
• Empowering all users to safely stay connected to resources<br />
• Protecting company data from the evolving threat landscape<br />
• Ensuring privacy and compliance without compromising<br />
on end‐user experience<br />
www.jamf.com<br />
Find out more<br />
and request<br />
your trial
ansomware<br />
Steve Forbes, Nominet: paying a ransom<br />
could make your business a bigger target<br />
in the future.<br />
Sam Curry, Cybereason: with ransomware<br />
attacks surging, the clock starts to<br />
immediately tick after ransomware has<br />
executed.<br />
lapse in judgement or concentration by<br />
a user who fails to spot a fake email, but<br />
also whether to pay or not is a decision only<br />
management can make. In the latter case,<br />
most people's natural reaction is likely to be<br />
to try to tough it out and pray that the IT<br />
team can get things back up and running.<br />
Unfortunately, the hackers have thought<br />
of that and typically built in the ticking<br />
timebomb factor, increasing pressure to<br />
cave in and pay up while there is still time<br />
for damage limitation," he says.<br />
In such situations, the management team<br />
finds itself between the proverbial rock and<br />
the hard place. "Stand firm and risk not just<br />
losing their entire OT systems, including<br />
business critical files and corporate data, but<br />
also the indirect costs, such as reputational<br />
damage and any incurred customer liability<br />
costs; or take the hit and move on as quickly<br />
as possible."<br />
In the end, adds Oakton, it all comes down<br />
to a simple cost/benefit decision, which<br />
usually means taking the least-worst financial<br />
impact option and giving in to the hacker's<br />
demands.<br />
"For its victims, ransomware holds some<br />
salutary lessons that need to be heeded, if<br />
they are going to avoid similar attacks in the<br />
future. Top of the list is: don't assume that<br />
you are now immune. Research has shown<br />
that hackers are very likely to be back to<br />
see if you have strengthened your defences.<br />
Next, ensure that you have a robust backup<br />
and recovery plan for all critical systems<br />
and, last but not least, put in place rigorous<br />
network management policies, backed by<br />
a programme of regular user education<br />
to engender a corporate culture of cyber<br />
awareness."<br />
ROBUST BACKUPS<br />
Steve Forbes, government cyber security<br />
expert, Nominet, picks up on the N<strong>CS</strong>C<br />
advice against paying a ransom, on the basis<br />
that there's no guarantee you'll actually have<br />
access restored, if you pay, and it could make<br />
your business a bigger target in the future.<br />
"But, if a worst-case scenario does happen,"<br />
he says, "and you hold out on paying a<br />
ransom, there are steps you can take to<br />
mitigate any damage and try to recover.<br />
"At a bare minimum, having robust backups<br />
on hand that have been tested and are<br />
resilient to malware is critical to get any<br />
impacted systems back online and<br />
operational in a quick manner. Ideally, this<br />
would be part of an incident response and<br />
crisis management plan that would be<br />
implemented at the first sign of trouble."<br />
Local authorities and national cyber<br />
agencies like the N<strong>CS</strong>C can also become<br />
a major lifeline in a ransomware situation,<br />
he adds. "They're the experts, and have all<br />
the procedures and actions in place to<br />
deploy when needed. Whether it's sharing<br />
technical advice for what to do or providing<br />
access to information, liaising with<br />
organisations like this can be invaluable.<br />
The quicker a business reaches out for help<br />
when disaster strikes, the better chance<br />
they have to recover and get back on track.<br />
Additionally, transparency with the authorities<br />
and any person or organisation that<br />
may be impacted by the incident is crucial.<br />
This can help to minimise reputational<br />
damage and reduce any fines that are<br />
imposed by regulatory bodies."<br />
Double extortion ransomware is another<br />
increasing trend for businesses to be wary<br />
of, where threat actors encrypt and hold<br />
hostage valuable data, putting additional<br />
pressure on them to pay up. "This is where,<br />
on top of having trusted backups, it is vital<br />
to have strong data encryption before it has<br />
a chance to be stolen, ensuring that, if an<br />
attacker is threatening to expose the data, it<br />
is at least protected," Forbes concludes.<br />
"Finally, organisations should ensure that only<br />
data that is required is retained, as this<br />
reduces the risk and impact, should any data<br />
be compromised."<br />
28<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
Unleash the<br />
security of<br />
ONE<br />
NETWORK<br />
SECURITY<br />
MULTI-FACTOR<br />
AUTHENTICATION<br />
SECURE<br />
CLOUD WI-FI<br />
ENDPOINT<br />
SECURITY<br />
Smart Security, Simply Done.<br />
Web: www.watchguard.com/uk | Email: uksales@watchguard.com | Tel: +44 (0) 203 608 9070
legislation<br />
EU CYBER RESILIENCE ACT UNVEILED<br />
GETTING THE BALANCE RIGHT<br />
MIKE NELSON, VP OF IOT SECURITY AT DIGICERT, EXPLAINS WHAT THE EU CYBER RESILIENCE ACT<br />
MEANS, IN THE FIRST MOVE TO LEGISLATE CYBERSECURITY FOR THE INTERNET OF THINGS<br />
The EU Cyber Resilience Act is the<br />
first EU-wide legislation to emerge<br />
that imposes cybersecurity rules<br />
on manufacturers. It will cover both<br />
hardware and software, and applies<br />
to both manufacturers and developers,<br />
making them responsible for the security<br />
of connected devices. The European<br />
Commission states that the regulation<br />
will tackle two issues: "the low level of<br />
cybersecurity of many of these products<br />
and more importantly the fact that many<br />
manufacturers do not provide updates<br />
to address vulnerabilities".<br />
WHAT WILL THE EU CYBER<br />
RESILIENCE ACT REQUIRE?<br />
The devil will be in the details as the<br />
requirements are developed and<br />
released. We anticipate that they will use<br />
non-prescriptive approaches similar to<br />
what we see in other regulations, like<br />
'encrypt sensitive data', 'devices must<br />
have the ability to be updated', 'ensure<br />
integrity of software and firmware' etc.<br />
However, to justify a penalty, they need<br />
to have some measurable approaches.<br />
There will likely be a requirement for<br />
regular updates, as that is one of the<br />
pain points that the European<br />
Commission raised. Sending automatic<br />
updates to a large scale of devices will<br />
be difficult without a solution that helps<br />
manufacturers maintain viability and<br />
automate tasks. Additionally, the EU<br />
Commission has stated that there will<br />
need to be more information available<br />
for consumers to make informed<br />
purchasing decisions and to set up their<br />
devices securely.<br />
HOW WILL THE EU CYBER<br />
RESILIENCE ACT AFFECT IOT<br />
MANUFACTURERS?<br />
IoT device manufacturers could face<br />
massive fines and penalties for noncompliance<br />
with the drafted EU Cyber<br />
Resilience Act. This is one of the first<br />
legislations to require a financial penalty<br />
for non-compliance. The EU is clear<br />
that, with this proposed legislation,<br />
the financial burden of devices will rest<br />
with manufacturers and developers.<br />
Furthermore, products that do not meet<br />
"essential" cybersecurity requirements will<br />
not be allowed to go to market. Thus,<br />
30<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
legislation<br />
manufacturers need to start incorporating<br />
security in the design of their<br />
products now, so that devices going<br />
to market in the next few years will be<br />
up to the required security standards.<br />
Market surveillance authorities in each<br />
EU member state will be responsible to<br />
fine non-compliant companies, up to<br />
a limit set within the act, and prohibit<br />
non-compliant devices from going<br />
to market. However, having one set<br />
standard for cybersecurity across the EU<br />
will also make it more streamlined and<br />
clearer for manufacturers on how to<br />
maintain compliance.<br />
HOW WILL THE EU CYBER<br />
RESILIENCE ACT AFFECT<br />
CONSUMERS?<br />
The EU Cyber Resilience Act will give<br />
consumers a better purchasing power<br />
and trust in their devices by requiring<br />
manufacturers to provide information<br />
on device security before purchasing.<br />
The rules will require more knowledge on<br />
how to choose products that are secure<br />
and how to set up devices in a secure<br />
way. Similar to how consumers look at<br />
nutrition labels on food products to<br />
better understand what they are made<br />
of, providing security information on<br />
devices upfront will allow consumers to<br />
make more informed purchase decisions.<br />
As manufacturers will be required to<br />
be more transparent on the cybersecurity<br />
in their devices, consumers will have<br />
increased trust in the connected devices<br />
that do go to market. Furthermore, the<br />
EU Commission anticipates it could even<br />
increase demand for "products with<br />
digital elements", if consumers trust the<br />
product security more.<br />
IOT SHOULD BE SECURE BY DESIGN<br />
Regulators shouldn't have to come in<br />
with heavy fines and consequences to<br />
drive security - but sadly all too often<br />
security is an afterthought in device<br />
development. In a perfect world,<br />
companies would realise the importance<br />
of protecting their assets, customers,<br />
reputation and employees, and do<br />
security the right way, because it's the<br />
right thing to do. Until we get there,<br />
we will have to continue tolerating<br />
regulators coming in with a stick.<br />
Additionally, the ability for national<br />
surveillance authorities to be able to<br />
prohibit or restrict the sale of nonconforming<br />
products will also be a stick<br />
that will drive better security.<br />
WHEN WILL THE CYBER RESILIENCE<br />
ACT BE ENFORCED?<br />
At this point, the EU Cyber Resilience Act<br />
is with the European Parliament and<br />
Council to examine and adopt. Once<br />
enacted, Member States will have up to<br />
two years to adopt the requirements.<br />
Thus, manufacturers should be prepared<br />
to comply with the act any time in the<br />
next few years.<br />
However, the trend of increasing<br />
regulation on connected devices will<br />
continue. The EU Cyber Resilience Act<br />
is just the first step; we anticipate that<br />
this regulation will become a guideline<br />
for other regulators to develop similar<br />
standards. In the future, there will be<br />
more regulation on the IoT and its<br />
design, not less. Thus, it's important<br />
for manufacturers to implement<br />
cybersecurity by design now, so<br />
they are prepared for the<br />
future of IoT regulation.<br />
In addition to more IoT<br />
regulation, we are seeing<br />
industries come together<br />
to solve for device<br />
security. For instance,<br />
the Matter protocol<br />
recently launched for<br />
smart home device<br />
interoperability, security<br />
and reliability may<br />
serve as an industrydriven<br />
roadmap for<br />
better IoT device security. Though the<br />
full details of the proposed EU legislation<br />
are yet to come out, it is likely that<br />
manufacturers complying with Matter<br />
security, using device attestation<br />
certificates and product attestation<br />
intermediates, would meet the<br />
requirements of the EU lawmakers.<br />
Furthermore, they will have the<br />
opportunity to signal security to<br />
consumers, given that Matter-compliant<br />
devices will carry the Matter seal of<br />
approval.<br />
Mike Nelson, VP of IoT<br />
Security at DigiCert<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> computing security<br />
31
packet data<br />
BUILDING A CAPTIVE AUDIENCE<br />
PACKET CAPTURE IS BECOMING INCREASINGLY IMPORTANT,<br />
AS MARK EVANS, VP OF MARKETING, ENDACE, EXPLAINS<br />
Mark Evans, VP of marketing, Endace.<br />
There's an adage amongst experienced<br />
SecOps and NetOps analysts - 'PCAP<br />
or it didn't happen' - highlighting<br />
why network packet capture data (the file<br />
extension .PCAP is a common file format)<br />
is so crucial. Packets provide the only truly<br />
definitive evidence of performance and<br />
security issues that happen on a network.<br />
If you can't see the packets, you may never<br />
know for certain exactly what happened.<br />
Recent widespread security vulnerabilities<br />
- such as Solarflare and Log4J 2 - have<br />
illustrated just why access to packet data<br />
on-demand is so important, igniting<br />
demand for full packet capture solutions<br />
to fill the visibility hole.<br />
Governments are also becoming aware<br />
of the importance of packet capture.<br />
The US White House has mandated,<br />
by February 2023, all Federal agencies<br />
must be able to provide access - when<br />
requested by CISA or the FBI - to a<br />
minimum of 72 hours of full packet<br />
capture data for investigating<br />
cybersecurity events.<br />
However, there's still confusion and<br />
misinformation about why packet data is<br />
important and what the term 'packet capture'<br />
means. Some organisations believe they can<br />
do packet capture by relying on network<br />
flow data and endpoint monitoring. Others<br />
only record a handful of packets relating<br />
to specific events or use 'triggered' packet<br />
capture, because they believe it saves on<br />
storage costs.<br />
This article seeks to clarify the confusion<br />
around packet capture, so organisations<br />
can make informed decisions.<br />
WHY IS PACKET DATA IMPORTANT?<br />
Packet payloads are often the only way<br />
to identify specifics: did a phishing attack<br />
compromise credentials? What data was<br />
stolen or modified in a breach? Or what<br />
malware was dropped on compromised<br />
hosts?<br />
While log files and flow data can indicate<br />
an issue has occurred, oftentimes they can't<br />
show the exact root cause of that problem.<br />
They don't provide crucial detail, such as the<br />
32<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
packet data<br />
actual 'payload' of data an attacker may<br />
have staged and exfiltrated. This leaves<br />
SecOps and NetOps teams blind to exactly<br />
what's happening on their network.<br />
With access to packet data, analysts can<br />
resolve problems faster and be certain<br />
about their conclusions. Packet data can<br />
also reduce analyst alert fatigue by providing<br />
the evidence necessary to tune detection<br />
systems to reduce false positive alerts and<br />
increase accuracy. It also enables analysts to<br />
prioritise, investigate and respond to events<br />
far more efficiently.<br />
THREE TYPES OF PACKET CAPTURE<br />
There are three types of packet capture used<br />
for security and network performance.<br />
The first, originally called 'packet sniffing',<br />
involves connecting a device to the network<br />
when a specific problem occurs so engineers<br />
can record ('sniff') small amounts of packet<br />
data to troubleshoot the problem. It's often<br />
referred to as 'ad-hoc' packet capture.<br />
The second type of packet capture is called<br />
'triggered packet capture' and happens<br />
when packet recording is only enabled in<br />
response to specific events - such as security<br />
alerts. Packet data relating to that event is<br />
then recorded to provide evidence for<br />
analysts for future investigation.<br />
The third and last type of packet recording<br />
is where all packets traversing the network<br />
are recorded and stored for as long as<br />
available storage allows. This is referred to<br />
as 'continuous' packet capture.<br />
PROS AND CONS OF AD-HOC,<br />
TRIGGERED AND CONTINUOUS<br />
PACKET CAPTURE<br />
Each type of packet capture can be useful.<br />
However, for enterprise cybersecurity<br />
purposes, both ad-hoc and triggered packet<br />
capture are problematic.<br />
Ad-hoc packet capture is insufficient for<br />
most security uses, because it relies on<br />
packet recording being implemented and<br />
enabled post-event - by which point<br />
evidence of crucial parts of an attack has<br />
typically already been missed. It's like turning<br />
on a surveillance camera after you've been<br />
burgled. Similarly, triggered packet capture<br />
is problematic because it assumes you can<br />
predict what traffic you might need to<br />
record ahead of time. Who could have<br />
foreseen the Solarflare attack, and how it<br />
would play out ahead of it happening?<br />
Continuous packet capture is the only<br />
reliable way to ensure record all the critical<br />
evidence of cybersecurity events. However,<br />
deploying continuous packet capture<br />
requires careful planning.<br />
STORAGE<br />
Accurately recording traffic continuously<br />
across an entire network requires dedicated<br />
recording infrastructure with significant<br />
capacity - often petabytes- to record days,<br />
weeks, or months of traffic. In the past,<br />
the cost of this infrastructure limited the<br />
widespread adoption of full packet capture<br />
to all but the largest enterprises. Or to<br />
specific industries - such as Banking,<br />
Telecommunications, Government and<br />
Military - where access to recorded packet<br />
data was considered essential regardless<br />
of cost. Thankfully, increased compute<br />
capacity, reduced storage costs, and new<br />
technologies like hardware compression<br />
mean continuous packet capture is now<br />
affordable for most organisations.<br />
How much storage do you need? The<br />
answer is how much 'lookback' time do<br />
you need/want? Typically, you'll want at least<br />
a week, and ideally a month or more. This<br />
gives SecOps and NetOps teams time to<br />
identify what packet data is important for<br />
investigating a specific issue and to archive<br />
evidence if necessary.<br />
RAPID SEARCH AND INTEGRATION<br />
WITH OTHER TOOLS<br />
Recorded packet data needs to be<br />
thoroughly indexed as it is captured - so<br />
analysts can quickly find traffic related<br />
to a particular host and protocol - or<br />
application - for a specific time period.<br />
This lets analysts quickly find what they<br />
need to complete investigations in a single,<br />
uninterrupted workflow, without requiring<br />
lengthy searches.<br />
Ideally, access to packets should be<br />
integrated into the tools analysts use<br />
already - eg, SIEM and SOAR, IDS/IPS<br />
and AI/ML solutions, and performance<br />
monitoring tools, so analysts can drilldown<br />
from alerts to related packets<br />
quickly.<br />
THE NEED FOR FORENSI<strong>CS</strong> SKILLS<br />
For packet data to be useful, analysts need<br />
to understand what it is showing them.<br />
Traditionally, this expertise has been limited<br />
to senior analysts - which are increasingly<br />
scarce resources. This is another reason<br />
why integrating packet forensics into<br />
existing tools is important. With the ability<br />
to go directly from an alert to relevant<br />
packet data, even junior analysts can find<br />
quickly what they need, making them that<br />
more productive and effective.<br />
For those looking to start with packet<br />
forensics, there's a wealth of useful<br />
information available. The Wireshark<br />
community (Wireshark is an open-source<br />
application that is the tool of choice for<br />
analysing packet data) and Youtube are<br />
both fantastic resources. Organisations<br />
like SANS also run many courses covering<br />
network forensics.<br />
A FINAL WORD<br />
Organisations need to ask themselves:<br />
'are we properly equipped to respond<br />
confidently when a serious security breach<br />
happens?' If they lack packet data, they<br />
must accept the risks associated with the<br />
lack of visibility and agility that results.<br />
If there's one thing that today's volatile<br />
cybersecurity landscape has taught us, it's<br />
that realising the gaps after the event is<br />
too late.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> computing security<br />
33
data threats<br />
WHY RANSOMWARE IS 'MOVING<br />
TOWARD DATA DESTRUCTION'<br />
SIGNS OF A NEW DATA EXTORTION TECHNIQUE SHOW THREAT ACTORS MAY LEVERAGE EXMATTER<br />
TO DESTROY, RATHER THAN ENCRYPT, DATA, ACCORDING TO A CYDERES THREAT REPORT<br />
Robert Herjavec,<br />
CEO, Cyderes.<br />
Data destruction is rumoured to<br />
be where ransomware is going to<br />
go, but we haven't seen it in the<br />
wild…until now. During a recent incident<br />
response, global managed cyber defence<br />
and response provider Cyderes and<br />
innovative inception platform Stairwell<br />
discovered signs that threat actors are<br />
actively in the process of staging and<br />
developing this capability.<br />
From big game hunting (BGH) to the<br />
growth of ransomware-as-a-service<br />
(RaaS) and data leak sites (DLS), the data<br />
extortion landscape is constantly<br />
evolving and experiencing<br />
new innovations from<br />
threat actors. Could the<br />
data extortion tactics<br />
of tomorrow turn<br />
to outright data<br />
destruction, in lieu of<br />
RaaS deployment?<br />
FAMILIAR TOOL,<br />
NEW TACTIC<br />
Cyderes Special<br />
Operations and<br />
Stairwell Threat<br />
Research teams<br />
discovered a<br />
sample of malware<br />
whose exfiltration<br />
behaviour aligns<br />
closely with previous<br />
reports of Exmatter, a .NET<br />
exfiltration tool. This sample<br />
was observed in conjunction<br />
with the deployment of BlackCat/ALPHV<br />
ransomware, which is allegedly run by<br />
affiliates of numerous ransomware groups,<br />
including BlackMatter. "Exmatter actually<br />
takes the ransomware game to a whole<br />
different level," says Robert Herjavec, CEO<br />
of Cyderes. "In the past, they'd get into<br />
your network, and they'd say, 'if you don't<br />
pay us, we're going to leak some data'.<br />
Now they go in, put an envelope around<br />
your data and, if you don't pay them, they<br />
start destroying it. It's frightening."<br />
Cyderes explains the sequence of events<br />
as follows. Exmatter is designed to take<br />
specific file types from selected directories<br />
and upload them to attacker-controlled<br />
servers before the ransomware itself is<br />
executed on the compromised systems.<br />
In this particular sample, the attacker<br />
attempts to corrupt files within the victim's<br />
environment, rather than encrypting them,<br />
and stages the files for destruction.<br />
First, the malware iterates over the drives<br />
of the victim machine, generating a queue<br />
of files that match a hardcoded list of<br />
designated extensions. Files matching<br />
those file extensions are added to the<br />
queue for exfiltration, which are then<br />
written to a folder with the same name<br />
as the victim machine's hostname on the<br />
actor-controlled server.<br />
As files upload to the actor-controlled<br />
server, the files that have been successfully<br />
copied to the remote server are queued to<br />
be processed by a class named Eraser.<br />
34<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
data threats<br />
A randomly-sized segment starting at the<br />
beginning of the second file is read into a<br />
buffer and then written into the beginning<br />
of the first file, first overwriting it and then<br />
corrupting the file.<br />
The development of capabilities to<br />
corrupt exfiltrated files within the victim<br />
environment marks a shift in data ransom<br />
and extortion tactics. Using legitimate file<br />
data from the victim machine to corrupt<br />
other files may be a technique to avoid<br />
heuristic-based detection for ransomware<br />
and wipers. Additionally, copying file data<br />
from one file to another is a much more<br />
benign functionality than sequentially<br />
overwriting files with random data or<br />
encrypting them.<br />
WHY DESTROY DATA,<br />
RATHER THAN ENCRYPT IT?<br />
With data exfiltration now the norm<br />
among threat actors, developing stable,<br />
secure and fast ransomware to encrypt<br />
files is a redundant and costly endeavour,<br />
compared to corrupting files and using<br />
the exfiltrated copies as the means of<br />
data recovery.<br />
"Today, we detect ransomware attacks<br />
based on certain behaviours that we see -<br />
that might be encrypting files, that might<br />
be deleting volume shadow files, or something<br />
similar," says Mike Wyatt, chief<br />
security officer at Cyderes. "But one<br />
thing we may not be looking for is data<br />
that's actually just being overwritten or<br />
corrupted. By overwriting data, a threat<br />
actor is able to achieve his goals faster.<br />
Unfortunately, it damages the files, rather<br />
than giving the victim the opportunity to<br />
pay for a decryption key."<br />
Another possible reason for this new<br />
tactic, which involves overwriting one<br />
legitimate file with another, is because<br />
EDR and other behavioural detections<br />
are getting better, explains Daniel Mayer,<br />
threat researcher at Stairwell, a company<br />
that helps organisations with security<br />
solutions and strategic partner to Cyderes.<br />
"Opening every file on a computer and just<br />
writing a bunch of data is suspicious; it<br />
looks like ransomware. There aren't a lot<br />
of executables that look like that. But<br />
opening one file and copying its contents<br />
to another? That's something that legitimately<br />
happens on computers all the time.<br />
It's a muddy indicator."<br />
Affiliates have also lost out on profits<br />
from successful intrusions, due to exploitable<br />
flaws in the ransomware deployed,<br />
as was the case with BlackMatter, the<br />
ransomware associated with previous<br />
appearances of this .NET-based exfiltration<br />
tool. Eliminating the step of encrypting<br />
the data makes the process faster and<br />
eliminates the risk of not getting the full<br />
pay-out or that the victim will find other<br />
ways to decrypt the data.<br />
GET THE INSIDE LOOK<br />
Artifacts within the sample indicate that<br />
the development of Exmatter is ongoing.<br />
Due to the nascent nature of the data<br />
destruction functionality within Exmatter,<br />
the Cyderes Special Operations and<br />
Stairwell Threat Research teams assess<br />
that data extortion actors are likely to<br />
continue experimenting with data<br />
exfiltration and destruction.<br />
For a more in-depth analysis, Cyderes<br />
collaborated with Stairwell, which expands<br />
Cyderes' 360-degree detection capabilities<br />
with its Inception platform. You can read<br />
the full research report here: Exmatter:<br />
Clues to the future of data extortion.<br />
Intelligence in Depth. The potential<br />
business impact of this new threat is<br />
indeed great, adds Cyderes, and reinforces<br />
organisations' focus on detection, response<br />
and recovery, "the critical defence-in-depth<br />
needed to prevent threat actors from<br />
getting in".<br />
How does Cyderes equip its clients with<br />
the tactics and tools they need to make<br />
sure they have the latest intelligence every<br />
day? "It's an information game," says Shelby<br />
Kaba, director of special operations at<br />
Cyderes. "We have several products that<br />
go out in the form of a Daily Intelligence<br />
Digest for our customers, an annual Stateof-Ransomware<br />
Report, and topical blogs<br />
written by our threat intelligence team and<br />
other thought leaders. Staying informed<br />
goes a long way."<br />
Join the experts. Interested in hearing<br />
more? You can join security executives and<br />
the experts who discovered the threat in<br />
this interactive panel discussion.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> computing security<br />
35
eaches<br />
MAJOR BREACH, HARSH LESSONS<br />
WHAT HARSH LESSONS CAN BE LEARNED FROM THE MAJOR BREACH<br />
SUFFERED BY UBER - AND HOW MIGHT SUCH ATTACKS BE STOPPED?<br />
Following the Uber security breach,<br />
disclosed in September this year, the<br />
cybersecurity sector is still buzzing.<br />
"While it is inevitable questions will be raised,<br />
it's important to reiterate this breach could<br />
not have been avoided by a single<br />
technology solution," points out Rich Turner,<br />
SVP EMEA at CyberArk. "Nor is it one in<br />
which a single person, company or provider<br />
was to blame. Saying that, there is a lot<br />
which can be learned from the breach, with<br />
it having a number of interesting elements<br />
for cybersecurity professionals to delve into."<br />
Turner lays out in detail what is known<br />
about the attack in five stages:<br />
Step 1: The attacker entered Uber's IT<br />
environment by gaining access to the<br />
credentials for its VPN infrastructure.<br />
Step 2: The contractor whose account was<br />
compromised likely did not have privileged<br />
access to key resources or any other special<br />
access permissions, but they did have access<br />
to a network share, just like other Uber<br />
employees. "Either this network share was<br />
reachable or the Access Control List was<br />
configured incorrectly to allow for broad<br />
read access," says Turner. "After, the hacker<br />
discovered a PowerShell script in the network<br />
share, which included privileged credentials<br />
for Uber's Privileged Access Management<br />
(PAM) solution hardcoded into it."<br />
Step 3: By stealing the administrator<br />
credentials that were hard-coded into the<br />
privileged access management solution,<br />
the attacker was able to further escalate<br />
their privileges.<br />
Step 4: According to an Uber update,<br />
the attacker eventually acquired 'elevated<br />
permissions to a number of tools'. Adds<br />
Turner: "Accessing the secrets of a privileged<br />
access management solution carried a high<br />
risk of harm. The SSO, consoles and cloud<br />
management console, which Uber uses<br />
to store private consumer and financial<br />
information, were reportedly all<br />
compromised by the hacker.<br />
Step 5: Uber said the attacker 'downloaded<br />
some internal Slack messages, as well as<br />
accessed or downloaded information from<br />
an internal application our finance team<br />
uses to track some bills' - a matter that the<br />
business reported it was looking into.<br />
PROTECTING EMBEDDED CREDENTIALS<br />
So, asks Turner, "how can a similar attack be<br />
stopped?", offering his recommendations<br />
for protecting embedded credentials.<br />
"Getting rid of any embedded credentials<br />
would be the first step towards preventing<br />
a similar attack. In addition to discontinuing<br />
this practice, we advise conducting an<br />
environment inventory to find and remove<br />
any hard-coded credentials that might be<br />
present in code, PaaS configurations, DevOps<br />
tools and internally developed applications."<br />
However, this is simpler to say than to do,<br />
he concedes. "In order to gradually reduce<br />
risk, focus first on your organisation's most<br />
important and potent credentials and secrets<br />
before spreading these best practices."<br />
Reiterating that neither the tools, nor<br />
the personnel in place at Uber, is to blame<br />
for this breach is important, he also states<br />
that nor is there a magic bullet for stopping<br />
cyberattacks. "No longer is it thought<br />
an attack can be completely prevented.<br />
However, we have some control over how<br />
far they go. Strong, layered cyber security<br />
defences may reduce attacks like the Uber<br />
breach. This should be strengthened by<br />
regular employee training to help them<br />
identify possible sources of danger.<br />
"These features make it more challenging<br />
for attackers to get a foothold, manoeuvre,<br />
find and accomplish their goals," adds Turner.<br />
"They also enable us to minimise the effectiveness<br />
and impact of attacks, and to resume<br />
regular activities as soon as feasible. This is<br />
the important knowledge we should absorb<br />
and use in our own organisations."<br />
36<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
www.adisa.global
GDPR<br />
REGULATORS MEAN BUSINESS!<br />
THE SECOND LARGEST EVER FINE FOR A BREACH OF THE EUROPEAN UNION'S GENERAL DATA PROTECTION<br />
REGULATION WAS SLAPPED ON INSTAGRAM RECENTLY - €405 MILLION. WILL THIS FORCE ORGANISATIONS<br />
TO ADOPT STRICTER DATA MANAGEMENT AND PROTECTION MEASURES GOING FORWARD?<br />
When Irish regulators recently fined<br />
Instagram 405 million euros for<br />
violating children's privacy, under<br />
the GDPR regulations, it signalled yet<br />
another step in the move towards holding<br />
all organisations to account, wherever<br />
violations were identified. The long-running<br />
complaint, in this instance, concerned<br />
children's data, particularly their phone<br />
numbers and email addresses. Some are<br />
said to have upgraded to business accounts<br />
to access analytics tools, such as profile<br />
visits, without realising this made more of<br />
their data public. Instagram owner Meta<br />
(formerly Facebook) has said it planned to<br />
appeal against the decision. It is the third<br />
fine handed to the company by the<br />
regulator.<br />
As for the biggest GDPR-related fine to<br />
date, this was meted out to Amazon:<br />
a massive €746 million, announced in the<br />
company's July 2021 earnings report, which<br />
was almost 15 times greater than the<br />
previous record at that time. The fine was<br />
imposed by Luxembourg's National<br />
Commission for Data Protection, which<br />
claimed the tech giant's processing of<br />
personal data did not comply with EU law.<br />
Amazon has lodged an appeal against the<br />
fine, only referring so far to a previous<br />
statement in July that "there has been no<br />
data breach, and no customer data has<br />
been exposed to any third party".<br />
STRICT MEASURES ESSENTIAL<br />
According to Dan Middleton, vice president<br />
UK & Ireland at security company Veeam,<br />
the news that Ireland's Data Protection<br />
Commission has issued the second largest<br />
GDPR fine in history drives home the critical<br />
importance of adopting strict data management<br />
and protection measures. "While it is<br />
by no means unique in this situation, the<br />
photo-sharing platform involved has<br />
changed its approach to data protection<br />
since the issues that led to the fine took<br />
place. However, this case demonstrates that<br />
past data management decisions have<br />
implications not just for the time at which<br />
they are made, but into the future. <strong>Dec</strong>ision<br />
makers need to be aware of any consequential<br />
issues that can arise when it comes<br />
to protecting and managing users' data.<br />
"Businesses must place data integrity,<br />
security and resilience at the heart of their<br />
operations to severely reduce, if not avert,<br />
the risk of their own and their end users'<br />
data being exposed to unwelcome<br />
consequences," adds Middleton. "Not only<br />
will this prevent hefty fines, such as those<br />
issued by the DPC, but it will ensure that<br />
38<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
GDPR<br />
their reputation doesn't suffer as a result of<br />
a management error or data protection<br />
oversight.<br />
"When companies are entrusted with their<br />
customers' sensitive data, there are no<br />
measures that go too far. They must be<br />
aware that they are custodians of any data<br />
they collect, process and use, and it is<br />
therefore their responsibility to ensure that<br />
this data is protected. This needs to go<br />
beyond a simple box-ticking exercise to<br />
ensure GDPR compliance, and instead<br />
a business-wide culture of transparency<br />
and responsibility must be adopted. When<br />
it comes to data protection, this should<br />
include a full business continuity strategy<br />
that includes resilience measures, along with<br />
secure, immutable backups and disaster<br />
recovery solutions that can be drawn upon,<br />
if data is maliciously accessed."<br />
WHATSAPP ALSO HIT HARD<br />
Last year, the DPC fined WhatsApp 225<br />
million euros, at that time the largest fine<br />
ever from the commission and the second<br />
highest under EU GDPR rules. Facebook<br />
(now Meta), which also owns WhatsApp,<br />
has its EU headquarters in Ireland. The fine<br />
relates to an investigation that began in<br />
2018 about whether WhatsApp had been<br />
transparent enough about how it handles<br />
information. The issues involved were highly<br />
technical, including whether WhatsApp<br />
supplied enough information to users about<br />
how their data was processed and if its<br />
privacy policies were clear enough. Those<br />
policies have since been updated several<br />
times.<br />
"WhatsApp is committed to providing a<br />
secure and private service," a company<br />
spokesperson said at the time, as reported<br />
by the BBC: "We have worked to ensure the<br />
information we provide is transparent and<br />
comprehensive and will continue to do<br />
so. We disagree with the decision today<br />
regarding the transparency we provided to<br />
people in 2018 and the penalties are entirely<br />
disproportionate." GDPR rules allows<br />
for fines of up to 4% of the offending<br />
company's global turnover.<br />
Clearly, the GDPR is proving effective, with<br />
the large fines administered so far to some<br />
big-name companies proving a reminder<br />
and deterrent to others when it comes to<br />
responsible management of data. All of<br />
which underscores the seriousness of<br />
purpose with which the regulations were<br />
planned. More than four years down the<br />
line since the regulations came into force,<br />
it's worth looking back at how they were<br />
structured and the European Commission's<br />
take on how effective they have proved<br />
since.<br />
First off, the European Commission accepts<br />
that most of the issues that are identified by<br />
Member States and stakeholders will most<br />
likely benefit from more experience in the<br />
application of the Regulation in the coming<br />
years. "Increasing global convergence<br />
around principles that are shared by the<br />
GDPR offers new opportunities to facilitate<br />
safe data flows, to the benefit of citizens<br />
and businesses alike," it states.<br />
IMPROVEMENTS WITH GDPR<br />
Businesses, including SMEs, now have just<br />
one set of rules to which to adhere. "The<br />
GDPR also creates a level playing field<br />
with companies not established in the EU<br />
but operating here. By establishing a<br />
harmonised framework for the protection<br />
of personal data, the GDPR ensures that all<br />
businesses in the internal market are bound<br />
by the same rules and benefit from the<br />
same opportunities, regardless of whether<br />
they are established and where the processing<br />
takes place. In addition, privacy has<br />
become a competitive quality that<br />
customers are increasingly taking into<br />
consideration when choosing their services.<br />
For SMEs, the implementation of the right<br />
to data portability has the potential to lower<br />
the barriers to entry to data protection<br />
friendly services. Compliance with the data<br />
protection rules and their transparent<br />
application will create trust between<br />
business and consumers when it comes<br />
to the use of their personal data."<br />
NEW TECHNOLOGIES<br />
The GDPR is seen as an essential and<br />
flexible tool to ensure the development<br />
of new technologies, in accordance with<br />
fundamental rights. "The implementation<br />
of the core principles of the GDPR is<br />
particularly crucial for data intensive<br />
processing. The risk-based and technologyneutral<br />
approach of the Regulation<br />
provides a level of data protection, which<br />
is adequate to the risk of the processing<br />
also by emerging technologies."<br />
The GDPR's technologically-neutral and<br />
future-proof approach was put to the test<br />
during the COVID-19 pandemic and has<br />
proven to be successful. Its principles-based<br />
rules supported the development of tools<br />
to combat and monitor the spread of the<br />
virus. The future-proof and risk-based<br />
approach of the GDPR is also being applied<br />
in the EU framework for Artificial<br />
Intelligence and in the implementation<br />
of the European Data Strategy, aimed at<br />
fostering data availability and at the<br />
creation of Common European Data<br />
Spaces.<br />
GLOBAL PROTECTION STANDARDS<br />
The GDPR has emerged as a reference point<br />
and acted as a catalyst for many countries<br />
and states around the world considering<br />
how to modernise their privacy rules.<br />
International instruments, such as the<br />
modernised 'Convention 108' of the Council<br />
of Europe or the 'Data Free Flow with Trust'<br />
initiative launched by Japan are also based<br />
on principles that are shared by the GDPR.<br />
This trend towards global convergence<br />
brings new opportunities for increasing the<br />
protection of Europeans, while, at the same<br />
time, facilitating data flows and lowering<br />
transaction costs for business operators.<br />
The GDPR offers a modernised toolbox to<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> computing security<br />
39
GDPR<br />
Dan Middleton, Veeam: Businesses must<br />
place data integrity, security and<br />
resilience at the heart of their operations.<br />
facilitate the transfer of personal data from<br />
the EU to a third country or international<br />
organisation, while ensuring that the data<br />
continues to benefit from a high level of<br />
protection. "This continuity of protection<br />
is important, given that in today's world<br />
data moves easily across borders and the<br />
protections guaranteed by the GDPR would<br />
be incomplete, if they were limited to<br />
processing inside the EU. The toolbox<br />
includes actively engaging with key partners<br />
with a view to reaching an adequacy<br />
finding and yielded important results such<br />
as the creation between the EU and Japan<br />
of the world's largest area of free and safe<br />
data flows. Ongoing work also concerns<br />
other transfer mechanisms, such as<br />
standard contractual clauses and<br />
certification, to harness the full potential of<br />
the GDPR rules on international transfers."<br />
What is all too clear from the sizeable fines<br />
that were imposed on Instagram and others<br />
is that data protection authorities are<br />
making use of a wide range of corrective<br />
powers provided by the GDPR, such as<br />
administrative fines, warnings and<br />
reprimands, orders to comply with data<br />
subject's requests, orders to bring processing<br />
operations into compliance with the<br />
Regulation, to rectify, erase or restrict<br />
processing. Nor is it all about fines as a<br />
means to keep businesses in line. As the<br />
EC states: "The GDPR also provides for a<br />
broader palette of corrective powers. For<br />
example, the effect of a ban on processing<br />
or the suspension of data flows can be<br />
much stronger than a financial penalty."<br />
CHANNEL 4 - TOTAL VISIBILITY<br />
One organisation intent on ensuring it<br />
meets its GDPR obligations is Channel 4,<br />
which is said to be saving its security<br />
department thousands each year after<br />
partnering with Invicti Security to gain<br />
complete visibility into its web assets.<br />
As part of protecting the information it<br />
collects, in line with regulations such as<br />
GDPR, Channel 4 - which operates the UK's<br />
biggest free streaming service, All 4, plus a<br />
network of 12 television channels - needs<br />
to secure vast amounts of information,<br />
including the data of 24 million All 4<br />
subscribers, as well as staff details, and all<br />
of its intellectual property and be able to<br />
demonstrate that this data is safe and<br />
secure.<br />
As a large organisation with thousands<br />
of web assets, security was previously a<br />
complex and expensive task, involving<br />
numerous penetration tests with multiple<br />
third parties, costing significant sums to the<br />
business. "We would perform a penetration<br />
test and after getting the results, we'd have<br />
to fix the issue and then pay for another<br />
penetration test," says Channel 4 CISO Brian<br />
Brackenborough. "That could be quite a<br />
cycle depending on how complicated the<br />
particular project was."<br />
Channel 4 now uses Invicti to gain visibility<br />
into whether websites are collecting<br />
personally identifiable information (PII). It<br />
can then perform vulnerability scans and<br />
penetration tests on those websites. The<br />
efficiency gains and cost savings are clear:<br />
partnering with Invicti saved Channel 4<br />
thousands in the first year alone. "The<br />
budget, which we were spending every<br />
year on penetration testing, decreased<br />
approximately 60%. The following year,<br />
it decreased close to 80%," he adds.<br />
Using Invicti, Channel 4 can start<br />
performing automated and continuous<br />
penetration tests or vulnerability scans<br />
against systems at certain milestones of<br />
a project to make sure it stays on track. It<br />
allows Channel 4 to catch any issues early<br />
on in the process, prioritising vulnerabilities<br />
that put the organisation at risk, so it can<br />
fix them with less manual effort.<br />
"That makes our lives a lot easier and allows<br />
us to ensure we are delivering projects on<br />
budget and on time," says Brackenborough.<br />
40<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2022</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
ALL-INCLUSIVE<br />
SECURITY<br />
SPAM FILTER &<br />
ADVANCED EMAIL SECURITY<br />
SIGNATURE & DISCLAIMER<br />
TOTAL PROTECTION<br />
ENTERPRISE BACKUP<br />
EMAIL ARCHIVING,<br />
ENCRYPTION & CONTINUITY<br />
BACKUP & RECOVERY<br />
FROM EMAIL SECURITY<br />
TO BACKUP & RECOVERY<br />
ALL IN ONE SOLUTION!<br />
START YOUR FREE<br />
30-DAY-TRIAL<br />
WWW.HORNETSECURITY.COM
Strengthen your data resilience with<br />
Immutable Backup from Arcserve<br />
Buy an Arcserve Appliance secured by Sophos,<br />
and get OneXafe immutable storage!<br />
Arm your business with a multi-layer protection approach to strengthen your overall data resilience. Arcserve<br />
brings you data backup, recovery, and immutable storage solutions with integrated cybersecurity to defeat<br />
ransomware and provide the best-in-class data management and data protection solution in the market.<br />
Arcserve UDP Data<br />
Protection Software<br />
Unified data and ransomware<br />
protection to neutralize<br />
ransomware attacks,<br />
restore data, and perform<br />
orchestrated recovery.<br />
Arcserve Appliances<br />
All-in-one enterprise backup,<br />
cybersecurity, and disaster<br />
recovery, with multipetabyte<br />
scalability.<br />
StorageCraft OneXafe<br />
Immutable Storage<br />
Scale-out object-based NAS<br />
storage with immutable<br />
snapshots to safeguard data.<br />
Get multi-layer protection!<br />
SCAN HERE