Targeting the iOS Kernel - Reverse Engineering Mac OS X
Targeting the iOS Kernel - Reverse Engineering Mac OS X
Targeting the iOS Kernel - Reverse Engineering Mac OS X
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
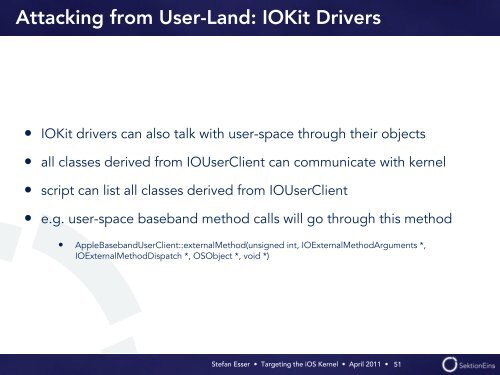
Attacking from User-Land: IOKit Drivers<br />
• IOKit drivers can also talk with user-space through <strong>the</strong>ir objects<br />
• all classes derived from IOUserClient can communicate with kernel<br />
• script can list all classes derived from IOUserClient<br />
• e.g. user-space baseband method calls will go through this method<br />
• AppleBasebandUserClient::externalMethod(unsigned int, IOExternalMethodArguments *,<br />
IOExternalMethodDispatch *, <strong>OS</strong>Object *, void *)<br />
Stefan Esser • <strong>Targeting</strong> <strong>the</strong> <strong>i<strong>OS</strong></strong> <strong>Kernel</strong> • April 2011 •<br />
51