ACOMP2010-program-v3.pdf
ACOMP2010-program-v3.pdf
ACOMP2010-program-v3.pdf
- TAGS
- www.cse.hcmut.edu.vn
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
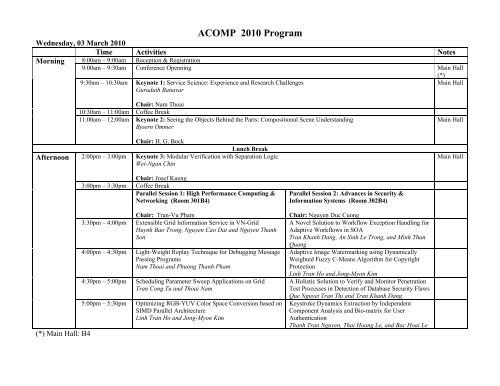
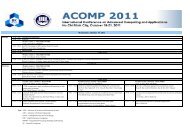
ACOMP 2010 Program<br />
Wednesday, 03 March 2010<br />
Time Activities Notes<br />
Morning 8:00am – 9:00am Reception & Registration<br />
9:00am – 9:30am Conference Openning Main Hall<br />
9:30am – 10:30am Keynote 1: Service Science: Experience and Research Challenges<br />
Guruduth Banavar<br />
Chair: Nam Thoai<br />
10:30am – 11:00am Coffee Break<br />
11:00am – 12:00am Keynote 2: Seeing the Objects Behind the Parts: Compositional Scene Understanding<br />
Bjoern Ommer<br />
Chair: H. G. Bock<br />
Afternoon 2:00pm – 3:00pm<br />
Lunch Break<br />
Keynote 3: Modular Verification with Separation Logic<br />
Wei-Ngan Chin<br />
(*) Main Hall: B4<br />
Chair: Josef Kueng<br />
3:00pm – 3:30pm Coffee Break<br />
Parallel Session 1: High Performance Computing &<br />
Networking (Room 301B4)<br />
Chair: Tran-Vu Pham<br />
3:30pm – 4:00pm Extensible Grid Information Service in VN-Grid<br />
Huynh Bao Trong, Nguyen Cao Dat and Nguyen Thanh<br />
Son<br />
4:00pm – 4:30pm Light-Weight Replay Technique for Debugging Message<br />
Passing Programs<br />
Nam Thoai and Phuong Thanh Pham<br />
4:30pm – 5:00pm Scheduling Parameter Sweep Applications on Grid<br />
Tran Cong Tu and Thoai Nam<br />
5:00pm – 5:30pm Optimizing RGB-YUV Color Space Conversion based on<br />
SIMD Parallel Architecture<br />
Linh Tran Ho and Jong-Myon Kim<br />
Parallel Session 2: Advances in Security &<br />
Information Systems (Room 302B4)<br />
Chair: Nguyen Duc Cuong<br />
A Novel Solution to Workflow Exception Handling for<br />
Adaptive Workflows in SOA<br />
Tran Khanh Dang, An Sinh Le Trong, and Minh Than<br />
Quang<br />
Adaptive Image Watermarking using Dynamically<br />
Weighted Fuzzy C-Means Algorithm for Copyright<br />
Protection<br />
Linh Tran Ho and Jong-Myon Kim<br />
A Holistic Solution to Verify and Monitor Penetration<br />
Test Processes in Detection of Database Security Flaws<br />
Que Nguyet Tran Thi and Tran Khanh Dang<br />
Keystroke Dynamics Extraction by Independent<br />
Component Analysis and Bio-matrix for User<br />
Authentication<br />
Thanh Tran Nguyen, Thai Hoang Le, and Bac Hoai Le<br />
(*)<br />
Main Hall<br />
Main Hall<br />
Main Hall
Thursday, 04 March 2010<br />
Time Activities Notes<br />
Morning 8:00am – 8:30am Reception & Registration<br />
8:30am – 9:30am Keynote 4: Security Models in Information Systems<br />
Josef Kueng<br />
Main Hall<br />
Chair: Rajkumar Buyya<br />
9:30am-9:45am Coffee Break<br />
9:45am – 10:45am Keynote 5: Cloud Computing: The Next Revolution in Information Technology<br />
Rajkumar Buyya<br />
Chair: Tran-Vu Pham<br />
10:45am-11:00am Coffee Break<br />
Parallel Session 3: Advances in Security &<br />
Information Systems (Room 301B4)<br />
Parallel Session 4: Advances in Software<br />
Engineering (Room 302B4)<br />
Chair: Huynh Quyet Thang<br />
Chair: Tran Dan Thu<br />
11:00am – 11:30am An Extensible and Pragmatic Hybrid Indexing Scheme Model Checking in Generating Counter-Examples for<br />
for MAC-based LBS Privacy-Preserving in Commercial Automatic Software Verification<br />
DBMSs<br />
Thang H. Bui, Anh T. Do, Tho T. Quan, and Khai T.<br />
Tran Khanh Dang and Quoc Cuong To<br />
Huynh<br />
11:30am – 12:00am A Comprehensive Framework for Evaluating Privacy Automated Verification of Programs with Real<br />
Preserving Techniques in Location-Based Services Arithmetic<br />
Le Hung Tran, Hong Ngoc Tran, Truong Toan Nguyen<br />
and Tran Khanh Dang<br />
Binh Le, Wei-Ngan Chin, and Phung H. Nguyen<br />
12:00am – 12:30pm BBF: A Bloom-Bloomier Filter for Pattern Matching in Model-based Generation of Structured Error-Flows in<br />
Clam Antivirus<br />
Imperative Programs<br />
Nguyen Duy Anh Tuan, Bui Trung Hieu, and Tran Ngoc Tho T. Quan , Duc L. N. Hoang, Vu H. Nguyen, and<br />
Thinh<br />
Lunch Break<br />
Phung H. Nguyen<br />
Afternoon 2:00pm – 3:00pm Keynote 6: Trends in Theory, Numerical Methods and Applications of Optimization of Dynamic Processes<br />
Ekaterina A. Kostina<br />
Chair: Vladimir Savchenko<br />
3:00pm – 3:30pm Coffee Break<br />
Parallel Session 5: Scientific Computing<br />
(Room 301B4)<br />
Chair: M. S. Mommer<br />
3:30pm – 4:00pm Cubic Spline Interpolation Based Parametric Model<br />
Order Reduction<br />
Nguyen Thanh Son and Angelika Bunse-Gerstner<br />
Parallel Session 6: Embedded System and VLSI<br />
Design (Room 302B4)<br />
Chair: Thuong Le-Tien<br />
Enhanced FPGA-based architecture for regular<br />
expression matching in NIDS<br />
Le Hoang Long, Tran Trung Hieu, Vu Tan Tai, Nguyen<br />
Hoa Hung, Tran Ngoc Thinh, and Do Dang Thach<br />
Main Hall<br />
Main Hall
4:00pm – 4:30pm Selecting Meaningful Predictor Variables: A Case Study<br />
with Bridge Monitoring Data<br />
Tran Vinh Tan and Nguyen Van Minh Man<br />
4:30pm – 5:00pm Clustering Mixed Data for Rough Set Approach<br />
Thein Than Thwin, Khaing Zarchi Tun, Swe Swe Nyein,<br />
Nyein Nyein Ei, Cynthia Myint<br />
5:00pm – 5:20pm Object Detection Based on Edge, Corner and HoG<br />
Feature<br />
Bao Nguyen Thien, Yutaka Yamada, and Tadashi Matsuo<br />
A Run-Time Detector for Violated Memory Access in<br />
Embedded Systems<br />
Nam Ho and Anh-Vu Dinh-Duc<br />
Packet classification with TCAM and Cuckoo Hashing<br />
on FPGA<br />
Le Trong Nhan and Dinh Duc Anh Vu<br />
Large scale Automatic Vehicle Location System using<br />
ZigBee<br />
Phuong Vo-Tan, Khoi Phan-Dinh, Anh-Vu Dinh-Duc<br />
Friday, 05 March 2010<br />
Time Activities Notes<br />
Morning 8:00am – 8:30am Reception & Registration<br />
8:30am – 9:30am Keynote 7: Speculations about The Art of Numerical Simulation<br />
Vladimir Savchenko<br />
Main Hall<br />
Chair: Ekaterina A. Kostina<br />
9:30am – 10:00am Coffee Break<br />
Parallel Session 7: Advances in Security & Information<br />
Systems (Room 301B4)<br />
Parallel Session 8: Scientific Computing<br />
(Room 302B4)<br />
Chair: Josef Kueng<br />
Chair: Ekaterina A. Kostina<br />
10:00am – 10:20am M3AR: A Privacy Preserving Algorithm Maintains An efficient algorithm for the shortest path problem<br />
Association Rules<br />
inside simple polygons without triangulation<br />
Huynh Van Quoc Phuong, Tran Khanh Dang, and Vo Thi<br />
Ngoc Chau<br />
Phan Thanh An and Tran Van Hoai<br />
10:20am – 10:40am A New Approach to Time Series Forecasting using A Newton-Picard Approach for Efficient Numerical<br />
Simulated Annealing Algorithms<br />
Solution of Time-Periodic Parabolic PDE Constrained<br />
Mai Thai Son, Nguyen Luong Anh Tuan, Nguyen Tran Cao Optimization Problems<br />
Tan Khoa, Le Quang Loc, and Lu Nhat Vinh<br />
Mommer M. S., A. Potschka, J. P. Schloeder, and H. G.<br />
Bock<br />
10:40am – 11:00am A Study of Scientific Collaborations and Its Implications A Lipidikar Tretise-based approach for Burmese<br />
for Building Research Supporting Environments Tokenization<br />
Tran Vu Pham and Khoa T. Cao<br />
Thein Than Thwin, Aye Thida Win, Phyo Phyo Wai, Mie<br />
Mie Su Thwin<br />
11:00am – 11:20pm An Investigation into the Effect of Security on Reliability Facial Expression Classification Based on Multi<br />
in a VoIP Network<br />
Artificial Neural Network<br />
Ohnmar Nhway, Myint Myint Thein, Thinn Thinn Win, Soe<br />
Lai Phyue, Aye Myat Mon, Aye Thida Win, and Phyo Phyo<br />
Wai<br />
Thai Hoang Le, and Hai Son Tran
11:20am – 11:40am Business Service Engineering and Gap Analysis for<br />
Conceptual SOA Analysis<br />
Dinh Khoa Nguyen<br />
11:30am – 12:15pm Talk: Scientific Computing for the Preservation of the Cultural Heritage - Experiences with Conservation and<br />
Restauration of Temple Ruins in the Angkor Region<br />
H.G. Bock<br />
Chair: Ekaterina A. Kostina<br />
Afternoon<br />
Lunch Break<br />
Parallel Session 9: Advances in Security & Information<br />
Systems, and Software Engineering (Room 301B4)<br />
Parallel Session 10: High Performance Computing &<br />
Networking (Room 302B4)<br />
Chair: Duong Tuan Anh<br />
Chair: Thanh Son Nguyen<br />
2:00pm – 2:20pm Checking implementation of UML 2 sequence diagram Scheduling algorithms for parallel and independent<br />
Anh-Hoang Truong, Dinh-Phuc Nguyen, and Chung- applications on Computational Grids<br />
Tuyen Luu<br />
Nam Thoai and Tuan Anh Dao<br />
2:20pm – 2:40pm Secure Multiparties Computation based on DSA digital Approach to Internet-Based Monitoring and Control<br />
signature and RSA cryptosystem<br />
Systems Using OPC UA<br />
Wai Wai Zin, Thein Than Thwin, Aye Myat Nyo, Hnin Wint Vu Van Tan and Myeong-Jae Yi<br />
Khaing, Thandar Su Nge Htwe, and Than Naing Soe<br />
2:40pm – 3:00pm Comparison for the accuracy of defect fix effort estimation Diverse Analysis of A Supercomputer Workload: A<br />
Myintzu Phyo Aung, Tin Zar Thaw, Naw Lay Wah, Swe Case Study<br />
Swe Nyein, Zar Lwin Phyo, Khaing Zar Chi Htun, Mie Mie Hung Bui, Baochuan Lu, Linh Ngo, Amy Apon<br />
Thet Thwin<br />
3:00pm – 3:20pm Efficient Routing in Hyper de Bruijn Aster Networks Early Abnormal Overload Detection And The Solution<br />
Ngoc Chi Nguyen, Nguyen Thanh Phuong, Truong Minh On Content Delivery Network<br />
Nhat<br />
Cam Nguyen Tan, Son Dang Truong, and Tan Cao<br />
Dang<br />
7:00pm Conference Banquet & Closing<br />
Starlight Restaurant (level 11) - OSCAR SAIGON HOTEL<br />
68A Nguyễn Huệ, Dist. 1<br />
Main Hall
Thursday, 04 March 2010<br />
Friday, 05 March 2010<br />
Tutorials<br />
Time Activities Venue Notes<br />
Afternoon 2:00pm – 4:00pm Tutorial 1: Ubiquitous Computing for Smart Worlds in Physical and Cyber Spaces<br />
by Jianhua Ma<br />
Time Activities Venue Notes<br />
Afternoon 2:00pm – 4:00pm Tutorial 2: Freifunk Mesh Networks<br />
by Mario Behling<br />
303B4<br />
303B4








![[8] 2002 e-business-strategies-for-virtual-organizations](https://img.yumpu.com/8167654/1/190x257/8-2002-e-business-strategies-for-virtual-organizations.jpg?quality=85)