Veille Technologique Sécurité - cert devoteam
Veille Technologique Sécurité - cert devoteam
Veille Technologique Sécurité - cert devoteam
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
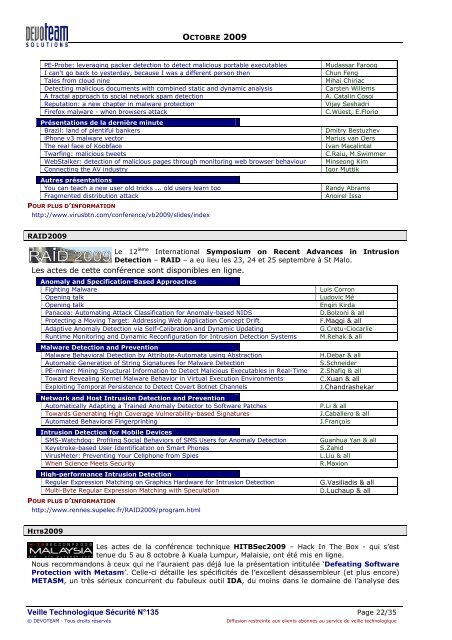
OCTOBRE 2009<br />
PE-Probe: leveraging packer detection to detect malicious portable executables<br />
I can't go back to yesterday, because I was a different person then<br />
Tales from cloud nine<br />
Detecting malicious documents with combined static and dynamic analysis<br />
A fractal approach to social network spam detection<br />
Reputation: a new chapter in malware protection<br />
Firefox malware - when browsers attack<br />
Présentations de la dernière minute<br />
Brazil: land of plentiful bankers<br />
iPhone v3 malware vector<br />
The real face of Koobface<br />
Twarfing: malicious tweets<br />
WebStalker: detection of malicious pages through monitoring web browser behaviour<br />
Connecting the AV industry<br />
Autres présentations<br />
You can teach a new user old tricks ... old users learn too<br />
Fragmented distribution attack<br />
POUR PLUS D’INFORMATION<br />
http://www.virusbtn.com/conference/vb2009/slides/index<br />
Mudassar Farooq<br />
Chun Feng<br />
Mihai Chiriac<br />
Carsten Willems<br />
A. Catalin Cosoi<br />
Vijay Seshadri<br />
C.Wüest, E.Florio<br />
Dmitry Bestuzhev<br />
Marius van Oers<br />
Ivan Macalintal<br />
C.Raiu, M.Swimmer<br />
Minseong Kim<br />
Igor Muttik<br />
Randy Abrams<br />
Anoirel Issa<br />
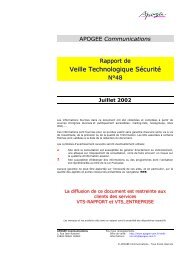
RAID2009<br />
Le 12 ième International Symposium on Recent Advances in Intrusion<br />
Detection – RAID – a eu lieu les 23, 24 et 25 septembre à St Malo.<br />
Les actes de cette conférence sont disponibles en ligne.<br />
Anomaly and Specification-Based Approaches<br />
Fighting Malware<br />
Opening talk<br />
Opening talk<br />
Panacea: Automating Attack Classification for Anomaly-based NIDS<br />
Protecting a Moving Target: Addressing Web Application Concept Drift<br />
Adaptive Anomaly Detection via Self-Calibration and Dynamic Updating<br />
Runtime Monitoring and Dynamic Reconfiguration for Intrusion Detection Systems<br />
Malware Detection and Prevention<br />
Malware Behavioral Detection by Attribute-Automata using Abstraction<br />
Automatic Generation of String Signatures for Malware Detection<br />
PE-miner: Mining Structural Information to Detect Malicious Executables in Real-Time<br />
Toward Revealing Kernel Malware Behavior in Virtual Execution Environments<br />
Exploiting Temporal Persistence to Detect Covert Botnet Channels<br />
Network and Host Intrusion Detection and Prevention<br />
Automatically Adapting a Trained Anomaly Detector to Software Patches<br />
Towards Generating High Coverage Vulnerability-based Signatures<br />
Automated Behavioral Fingerprinting<br />
Intrusion Detection for Mobile Devices<br />
SMS-Watchdog: Profiling Social Behaviors of SMS Users for Anomaly Detection<br />
Keystroke-based User Identification on Smart Phones<br />
VirusMeter: Preventing Your Cellphone from Spies<br />
When Science Meets Security<br />
High-performance Intrusion Detection<br />
Regular Expression Matching on Graphics Hardware for Intrusion Detection<br />
Multi-Byte Regular Expression Matching with Speculation<br />
POUR PLUS D’INFORMATION<br />
http://www.rennes.supelec.fr/RAID2009/program.html<br />
Luis Corron<br />
Ludovic Mé<br />
Engin Kirda<br />
D.Bolzoni & all<br />
F.Maggi & all<br />
G.Cretu-Ciocarlie<br />
M.Rehak & all<br />
H.Debar & all<br />
S.Schneider<br />
Z.Shafiq & all<br />
C.Xuan & all<br />
J.Chandrashekar<br />
P.Li & all<br />
J.Caballero & all<br />
J.François<br />
Guanhua Yan & all<br />
S.Zahid<br />
L.Liu & all<br />
R.Maxion<br />
G.Vasiliadis & all<br />
D.Luchaup & all<br />
HITB2009<br />
Les actes de la conférence technique HITBSec2009 – Hack In The Box - qui s’est<br />
tenue du 5 au 8 octobre à Kuala Lumpur, Malaisie, ont été mis en ligne.<br />
Nous recommandons à ceux qui ne l’auraient pas déjà lue la présentation intitulée ‘Defeating Software<br />
Protection with Metasm’. Celle-ci détaille les spécificités de l’excellent désassembleur (et plus encore)<br />
METASM, un très sérieux concurrent du fabuleux outil IDA, du moins dans le domaine de l’analyse des<br />
<strong>Veille</strong> <strong>Technologique</strong> Sécurité N°135 Page 22/35<br />
© DEVOTEAM - Tous droits réservés Diffusion restreinte aux clients abonnés au service de veille technologique