TCP-PCP: A Transport Control Protocol Based on the Prediction of ...
TCP-PCP: A Transport Control Protocol Based on the Prediction of ...
TCP-PCP: A Transport Control Protocol Based on the Prediction of ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
<str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g>: A <str<strong>on</strong>g>Transport</str<strong>on</strong>g> <str<strong>on</strong>g>C<strong>on</strong>trol</str<strong>on</strong>g> <str<strong>on</strong>g>Protocol</str<strong>on</strong>g> based <strong>on</strong><br />
<strong>the</strong> Predicti<strong>on</strong> <strong>of</strong> C<strong>on</strong>gesti<strong>on</strong> Probability over<br />
Wired/Wireless Hybrid Networks<br />
Jin Ye ∗† , Jianxin Wang ∗ , Liang R<strong>on</strong>g ∗ , and Weijia Jia ‡<br />
∗ School <strong>of</strong> Informati<strong>on</strong> Science and Engineering, Central South University, ChangSha, China, 410083<br />
† College <strong>of</strong> Informati<strong>on</strong> Science and Engineering, Guilin university <strong>of</strong> Electr<strong>on</strong>ic Technology, Guilin, China, 541004<br />
‡ Department <strong>of</strong> Computer Science, City University <strong>of</strong> H<strong>on</strong>g K<strong>on</strong>g, China<br />
Email: yejin@gliet.edu.cn, jxwang@mail.csu.edu.cn, csulr<strong>on</strong>g@gmail.com, wjia@cs.cityu.edu.hk<br />
Abstract—Many <strong>of</strong> packet loss as a result <strong>of</strong> factors o<strong>the</strong>r<br />
than c<strong>on</strong>gesti<strong>on</strong> impact <strong>the</strong> performance <strong>of</strong> <str<strong>on</strong>g>TCP</str<strong>on</strong>g> in wired/wirelss<br />
hybrid networks. Firstly, this paper proposes <strong>on</strong>e c<strong>on</strong>cept <strong>of</strong><br />
C<strong>on</strong>gesti<strong>on</strong> Probability (CP) and analyzes <strong>the</strong> correlati<strong>on</strong> <strong>of</strong> CP<br />
and network state. Then a <str<strong>on</strong>g>Transport</str<strong>on</strong>g> <str<strong>on</strong>g>C<strong>on</strong>trol</str<strong>on</strong>g> <str<strong>on</strong>g>Protocol</str<strong>on</strong>g> named<br />
as <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> is proposed, which is based <strong>on</strong> <strong>the</strong> Predicti<strong>on</strong> <strong>of</strong><br />
C<strong>on</strong>gesti<strong>on</strong> Probability instead <strong>of</strong> single loss event. Depending<br />
<strong>on</strong> <strong>the</strong> ECN mechanism, <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> calculates <strong>the</strong> value <strong>of</strong> CP<br />
by analyzing some latest loss events. The <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> sender’s<br />
behavior is c<strong>on</strong>trolled by <strong>the</strong> change <strong>of</strong> CP value. Simulati<strong>on</strong><br />
results show that <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> can improve <str<strong>on</strong>g>TCP</str<strong>on</strong>g> performance more<br />
efficiently than Westwood and Jersey.<br />
I. INTRODUCTION<br />
Transmissi<strong>on</strong> <str<strong>on</strong>g>C<strong>on</strong>trol</str<strong>on</strong>g> <str<strong>on</strong>g>Protocol</str<strong>on</strong>g> (<str<strong>on</strong>g>TCP</str<strong>on</strong>g>) was designed to cope<br />
with packet loss due to network c<strong>on</strong>gesti<strong>on</strong>. However, packet<br />
loss may be induced also by wireless links with characteristics<br />
<strong>of</strong> high bit error rate, low bandwidth, l<strong>on</strong>g delay, frequent<br />
mobility and so <strong>on</strong>. Thus, <strong>the</strong> assumpti<strong>on</strong> that packet loss is<br />
an indicator <strong>of</strong> network c<strong>on</strong>gesti<strong>on</strong> may not adapt to wireless<br />
envir<strong>on</strong>ment, which results in poor performance <strong>of</strong> traditi<strong>on</strong>al<br />
<str<strong>on</strong>g>TCP</str<strong>on</strong>g> in wireless networks [1] [2].<br />
<str<strong>on</strong>g>TCP</str<strong>on</strong>g> enhancements over wired/wireless hybrid networks<br />
have focused <strong>on</strong> differentiating packet losses. As a most<br />
significant <strong>on</strong>e, <str<strong>on</strong>g>TCP</str<strong>on</strong>g> Westwood [3] adopts available bandwidth<br />
estimati<strong>on</strong> to discriminate <strong>the</strong> cause <strong>of</strong> packet loss. The sender<br />
derives <strong>the</strong> network bandwidth by exploiting <strong>the</strong> rate and pattern<br />
<strong>of</strong> <strong>the</strong> returning ACK stream. Up<strong>on</strong> experiencing a packet<br />
loss, <strong>the</strong> sender adjusts <strong>the</strong> c<strong>on</strong>gesti<strong>on</strong> window dynamically<br />
according to <strong>the</strong> estimati<strong>on</strong>. This is <strong>the</strong> key innovative idea in<br />
c<strong>on</strong>trary to <str<strong>on</strong>g>TCP</str<strong>on</strong>g> Reno, which “blindly” halves <strong>the</strong> c<strong>on</strong>gesti<strong>on</strong><br />
window after three duplicate ACKs.<br />
In Westwood, packet losses are differentiated based <strong>on</strong> <strong>the</strong><br />
interval <strong>of</strong> ACK arrival. However, correct classificati<strong>on</strong> based<br />
<strong>on</strong> end-to-end informati<strong>on</strong> has been found to be difficult. For<br />
example, RTT(Round Trip Time) jitter <strong>of</strong> wireless networks<br />
is more than 10 times larger than that <strong>of</strong> wired networks [4],<br />
which leads to little correlati<strong>on</strong> between nature <strong>of</strong> loss and<br />
observable metric. This is similar as o<strong>the</strong>r metrics including<br />
that <strong>of</strong> Westwood. Subsequently, how to effectively estimate<br />
eligible bandwidth in hybrid networks is still an open issue<br />
[5] [6].<br />
As an enhancement to Westwood, <str<strong>on</strong>g>TCP</str<strong>on</strong>g> Jersey [7] uses<br />
<strong>the</strong> ECN (Explicit C<strong>on</strong>gesti<strong>on</strong> Notificati<strong>on</strong>) signal as a tool<br />
to distinguish between c<strong>on</strong>gesti<strong>on</strong> loss and corrupti<strong>on</strong> loss.<br />
The sender checks <strong>the</strong> ACK when <strong>the</strong>re is packet dropping.<br />
The loss event will be identified as c<strong>on</strong>gesti<strong>on</strong> induced if<br />
its CE(C<strong>on</strong>gesti<strong>on</strong> Explicit) bit is set 1, o<strong>the</strong>rwise it will be<br />
classified to be corrupti<strong>on</strong> induced.<br />
There are two problems that should be discussed:<br />
(1)Many simulati<strong>on</strong>s dem<strong>on</strong>strate that ECN mechanism can<br />
not differentiate packet loss efficiently [8] [9]. Actually <strong>the</strong><br />
reas<strong>on</strong> is that ECN is a proactive c<strong>on</strong>gesti<strong>on</strong> c<strong>on</strong>trol and its<br />
feedback is a temporary signal. That is to say, network states<br />
reflected by ECN may change quickly. It is incorrect to trigger<br />
c<strong>on</strong>gesti<strong>on</strong> c<strong>on</strong>gtrol based <strong>on</strong> single ECN feedback.<br />
Moreover, <strong>the</strong> signal <strong>of</strong> a loss event and <strong>the</strong> loss reas<strong>on</strong><br />
become now-obsolete because <strong>of</strong> <strong>the</strong> large feedback latency<br />
in hybrid network. Therefore, it is pivotal to make better use<br />
<strong>of</strong> <strong>the</strong> informati<strong>on</strong> <strong>on</strong> loss events and <strong>the</strong>ir classificati<strong>on</strong>.<br />
(2)Even if loss events are classified accurately, how to use<br />
<strong>the</strong> classificati<strong>on</strong> result needs to be c<strong>on</strong>sidered deeply. By<br />
far, most <str<strong>on</strong>g>TCP</str<strong>on</strong>g> variants do not adjust its sending rate if loss<br />
events are caused by n<strong>on</strong> c<strong>on</strong>gesti<strong>on</strong> factors. Actually, such<br />
strategy has been questi<strong>on</strong>ed because it may lead to c<strong>on</strong>gesti<strong>on</strong><br />
collapse [10]. Therefore, <str<strong>on</strong>g>TCP</str<strong>on</strong>g> variants should focus <strong>on</strong> how<br />
to trigger c<strong>on</strong>gesti<strong>on</strong> c<strong>on</strong>trol appropriately o<strong>the</strong>r than how to<br />
differentiate packet loss accurately.<br />
In fact, reas<strong>on</strong>s <strong>of</strong> packet dropping are more complicated in<br />
hybrid networks, including link disc<strong>on</strong>necti<strong>on</strong>, routing change<br />
and hand<strong>of</strong>f, and so <strong>on</strong>. It is becoming more and more difficult<br />
to shield high layer from n<strong>on</strong>-c<strong>on</strong>gesti<strong>on</strong> losses. Therefore,<br />
finding a more precise c<strong>on</strong>gesti<strong>on</strong>-aware scheme is <strong>the</strong> best<br />
way to improve <str<strong>on</strong>g>TCP</str<strong>on</strong>g> performance in hybrid networks.<br />
By and large, <strong>the</strong> protocols like Westwood and Jersey solve<br />
<strong>the</strong> problem <strong>of</strong> c<strong>on</strong>gesti<strong>on</strong> c<strong>on</strong>trol over hybrid network by<br />
decoupling c<strong>on</strong>gesti<strong>on</strong> loss and corrupti<strong>on</strong> loss in different<br />
ways. However, more aspects should be c<strong>on</strong>sidered <strong>on</strong> <strong>the</strong>ir<br />
soluti<strong>on</strong>s.<br />
978-1-4244-2324-8/08/$25.00 © 2008 IEEE.<br />
This full text paper was peer reviewed at <strong>the</strong> directi<strong>on</strong> <strong>of</strong> IEEE Communicati<strong>on</strong>s Society subject matter experts for publicati<strong>on</strong> in <strong>the</strong> IEEE "GLOBECOM" 2008 proceedings.
In order to mitigate <strong>the</strong> impact <strong>of</strong> dynamic metric and large<br />
delay, this paper proposes a more precise c<strong>on</strong>gesti<strong>on</strong>-aware<br />
scheme, a protocol named <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g>, in which ECN feedback<br />
is utilized in a novel method. The sender analyzes <strong>the</strong> network<br />
state from <strong>the</strong> latest ECN feedback informati<strong>on</strong>, which is<br />
termed as Predicti<strong>on</strong> <strong>of</strong> C<strong>on</strong>gesti<strong>on</strong> Probability. The result is<br />
used to c<strong>on</strong>trol <strong>the</strong> sender’s behavior. Simulati<strong>on</strong> results show<br />
that <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> outperforms Westwood and Jersey in hybrid<br />
networks.<br />
The rest <strong>of</strong> <strong>the</strong> paper is organized as follows. Secti<strong>on</strong> II<br />
presents CP and investigates <strong>the</strong> correlati<strong>on</strong> between CP<br />
and network state. Secti<strong>on</strong> III describes <strong>the</strong> new protocol<br />
in detail. Secti<strong>on</strong> IV discusses and analyzes <strong>the</strong> simulati<strong>on</strong><br />
results. Finally, c<strong>on</strong>cluding remarks for our work are presented<br />
in Secti<strong>on</strong> V.<br />
II. PREDICTION OF CONGESTION PROBABILITY<br />
The key idea <strong>of</strong> CPECN is to analysis <strong>the</strong> distributi<strong>on</strong> <strong>of</strong><br />
CE bit from ECN feedbacks and predict c<strong>on</strong>gesti<strong>on</strong> states by<br />
<strong>the</strong> correlati<strong>on</strong> between feedback serials.<br />
A. C<strong>on</strong>gesti<strong>on</strong> Probability<br />
ECN signal indicates <strong>the</strong> imminent c<strong>on</strong>gesti<strong>on</strong> instead <strong>of</strong><br />
c<strong>on</strong>gesti<strong>on</strong> already occurring. Since <strong>the</strong> state <strong>of</strong> network<br />
changes dynamically, <strong>the</strong> c<strong>on</strong>gesti<strong>on</strong> loss may occur or not<br />
in <strong>the</strong> next epoch. In o<strong>the</strong>r words, <strong>the</strong> c<strong>on</strong>gesti<strong>on</strong> situati<strong>on</strong><br />
may ei<strong>the</strong>r c<strong>on</strong>tinue, or clear up. Therefore, it is not suitable<br />
for <str<strong>on</strong>g>TCP</str<strong>on</strong>g> sender in resp<strong>on</strong>se to such uncertain signal directly.<br />
Single ECN feedback <strong>on</strong>ly reflects <strong>the</strong> network state at some<br />
earlier point in time, thus several ECN feedbacks can reflect<br />
<strong>the</strong> dynamic change <strong>of</strong> network state at several intervals. So<br />
it is more reas<strong>on</strong>able to resp<strong>on</strong>d to several ECN feedbacks<br />
toge<strong>the</strong>r in an appropriate way.<br />
In order to characterize serial ECN feedbacks, we introduce<br />
<strong>the</strong> new c<strong>on</strong>cepti<strong>on</strong> <strong>of</strong> CP (C<strong>on</strong>gesti<strong>on</strong> Probability), which<br />
can be calculated as follows while packet loss occurring:<br />
CP[i] = 1<br />
m ∗<br />
m−1 <br />
wi ∗ ACK[i].ecnecho (1)<br />
i=0<br />
where ACK[i].ecnecho is <strong>the</strong> value <strong>of</strong> CE bit in ACK[i],<br />
wi is <strong>the</strong> weight <strong>of</strong> ACK[i] and m−1<br />
i=0 wi = 1, CP[i]<br />
is calculated based <strong>on</strong> ACK series with m amount before<br />
ACK[i], that is ACK[i], ACK[i − 1], ..., ACK[i − m − 1].<br />
To be c<strong>on</strong>cise, ACK[i].ecnecho is expressed as ACK[i] in<br />
this paper.<br />
The sender is always ga<strong>the</strong>ring CE bit from ACK and calculating<br />
<strong>the</strong> current CP value by using EWMA (Exp<strong>on</strong>entially<br />
Weighted Moving Average) predictor shown in Eq.(1). We<br />
divide <strong>the</strong> m ACKs into several segments and each ACK will<br />
be assigned with a weight. The weight <strong>of</strong> ACKs in <strong>the</strong> same<br />
segment are equal, which means that <strong>the</strong> ACKs in <strong>the</strong> same<br />
segment have <strong>the</strong> same impact <strong>on</strong> <strong>the</strong> judgement <strong>of</strong> network<br />
state. By this way, <strong>the</strong> role <strong>of</strong> <strong>on</strong>e single ACK is decreased<br />
and that <strong>of</strong> all ACKs in <strong>on</strong>e segment is increased. So <strong>the</strong><br />
judgement <strong>of</strong> network state is build <strong>on</strong> <strong>the</strong> change trends <strong>of</strong><br />
ECN feedback.<br />
If <strong>the</strong> last m ACKs are divided into n segments, <strong>the</strong>n CP[i]<br />
can be calculated as following:<br />
where<br />
CP[i] =<br />
n<br />
j=1<br />
wj ∗ n<br />
m ∗<br />
m<br />
n j−1<br />
<br />
i= m<br />
n (j−1)<br />
ACK[i] (2)<br />
n<br />
wj =1 (3)<br />
j=1<br />
Generally, <strong>the</strong> weight <strong>of</strong> <strong>the</strong> new ACK is larger than that <strong>of</strong><br />
<strong>the</strong> old <strong>on</strong>e. So <strong>the</strong> weight <strong>of</strong> <strong>the</strong> ACKs in each segment are<br />
assigned as following:<br />
wj = α ∗ wj−1,α∈ (0, 1) (4)<br />
In traditi<strong>on</strong>al <str<strong>on</strong>g>TCP</str<strong>on</strong>g> protocol, <strong>the</strong> sender enters <strong>the</strong> slowstart<br />
mode after receiving three duplicate ACK packets. So<br />
we choose four ACK packets to compose <strong>on</strong>e segment, i.e:<br />
m =4∗ n (5)<br />
By using <strong>the</strong> formulas (3),(4),(5), we can rewrite <strong>the</strong> formula<br />
(2)asfollowing:<br />
CP[i] =<br />
n<br />
j=1<br />
wj ∗ 1<br />
4 ∗<br />
4j−1 <br />
i=4(j−1)<br />
The formula ( 6) can be expanded to<br />
CP[i] =w1 ∗ 1<br />
4 ∗<br />
3<br />
i=0<br />
ACK[i]+ w1<br />
α<br />
+ ... + w1<br />
∗<br />
αn−1<br />
1<br />
4 ∗<br />
4n−1 <br />
i=4(n−1)<br />
ACK[i],i∈ [1,m] (6)<br />
∗ 1<br />
4 ∗<br />
7<br />
ACK[i]<br />
i=4<br />
ACK[i]<br />
When CP[i +1] >CP[i], <strong>the</strong> c<strong>on</strong>gesti<strong>on</strong> probability is<br />
increasing. Meanwhile, <strong>the</strong> c<strong>on</strong>gesti<strong>on</strong> probability may be<br />
decreasing when CP[i +1]
ECN feedback. On <strong>the</strong> c<strong>on</strong>trary, if <strong>the</strong> CE bit <strong>of</strong> <strong>the</strong> latest<br />
arriving ACK is 1, <strong>the</strong>value<strong>of</strong>△CP will bel<strong>on</strong>g to [−1, 1].<br />
In this case, it can not be determined that whe<strong>the</strong>r <strong>the</strong> network<br />
is going to become c<strong>on</strong>gesti<strong>on</strong> or not. Whatever <strong>the</strong> CE bit <strong>of</strong><br />
<strong>the</strong> new arriving ACK is, △CP ≤ 0 always indicates that <strong>the</strong><br />
network c<strong>on</strong>gesti<strong>on</strong> may be relieved.<br />
For simplicity, <strong>the</strong> last m ACKs are divided into 2 segments,<br />
that is n =2and m =8.Letw1 =0.25 ∗ w2. Byusing<strong>the</strong><br />
formulas (3) and (4), we can get w1 =0.2 and w2 =0.8. All<br />
<strong>the</strong>se parameters are used in <strong>the</strong> following simulati<strong>on</strong>s.<br />
B. Analysis <strong>of</strong> C<strong>on</strong>gesti<strong>on</strong> Probability<br />
In this subsecti<strong>on</strong>, <strong>the</strong> correlati<strong>on</strong> <strong>of</strong> CP and network<br />
states is analyzed by simulati<strong>on</strong>s. The network topology for<br />
simulati<strong>on</strong> is <strong>the</strong> same as that used in Ref. [13], which is a<br />
typical topology for wired/wireless hybrid network(which is<br />
also shown in Fig.7). One <str<strong>on</strong>g>TCP</str<strong>on</strong>g> Reno flow traverses al<strong>on</strong>g<br />
a bottleneck link and a wireless terminal. When <strong>the</strong> sender<br />
receives <strong>the</strong> signal <strong>of</strong> packet dropping or <strong>the</strong> ACK packet in<br />
which <strong>the</strong> CE bit is 1, it regulates <strong>the</strong> sending window size<br />
according to <str<strong>on</strong>g>TCP</str<strong>on</strong>g> Reno. Packets <strong>on</strong> routers will be marked if<br />
<strong>the</strong> average queue length exceeds <strong>the</strong> given threshold.<br />
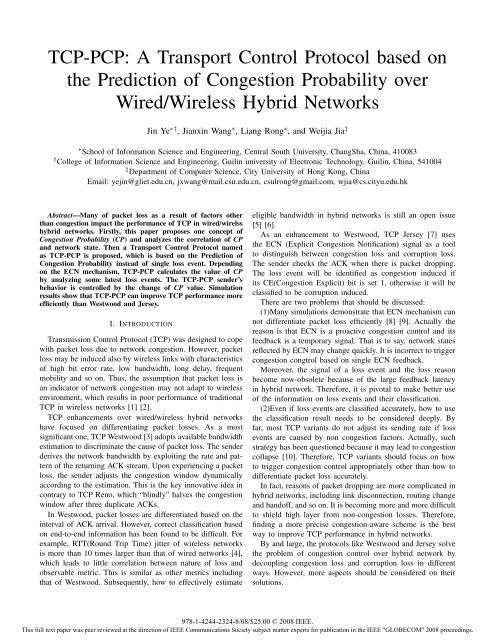
In Fig.1, <strong>the</strong> size <strong>of</strong> <str<strong>on</strong>g>TCP</str<strong>on</strong>g> sending window, <strong>the</strong> queue length<br />
<strong>of</strong> bottleneck link and CP are shown while <strong>the</strong> loss rate <strong>of</strong><br />
wireless link is 0 and 0.001. As shown in Fig.1(a), <strong>the</strong> size<br />
<strong>of</strong> <str<strong>on</strong>g>TCP</str<strong>on</strong>g> sending window varies very regularly because <strong>of</strong> no<br />
loss in wireless link. While <strong>the</strong>re exists packet loss in wireless<br />
link, <strong>the</strong> size <strong>of</strong> <str<strong>on</strong>g>TCP</str<strong>on</strong>g> sending window changes frequently and<br />
irregularly, which is shown in Fig.1(b). From Fig.1(a) and<br />
Fig.1(b), it is obvious that <strong>the</strong> average size <strong>of</strong> <strong>the</strong> sender<br />
window without packet loss is larger than that with packet<br />
loss.<br />
The queue length <strong>of</strong> bottleneck link is shown in Fig.1(c) and<br />
Fig.1(d). As shown in Fig.1(c), <strong>the</strong>re are 4 periods in which<br />
<strong>the</strong> queue length is larger than <strong>the</strong> given threshold. In this<br />
case, <strong>the</strong> router marks <strong>the</strong> packet and <strong>the</strong> sender will receive<br />
<strong>the</strong> ACK packet with CE=1. It is clear that <strong>the</strong> changes <strong>of</strong> <strong>the</strong><br />
sending window is be c<strong>on</strong>s<strong>on</strong>ant with that <strong>of</strong> <strong>the</strong> queue length.<br />
In Fig.1(d), <strong>the</strong>re is <strong>on</strong>ly <strong>on</strong>e period in which <strong>the</strong> queue length<br />
is larger than <strong>the</strong> given threshold. But <strong>the</strong> sending window<br />
does not change according to <strong>the</strong> queue length because <strong>the</strong>re<br />
are packets losses in wireless link.<br />
The statistic <strong>of</strong> CP under different situati<strong>on</strong> are shown in<br />
Fig.1(e) and Fig.1(f) respectively. It is indicated that trend <strong>of</strong><br />
CP changing is c<strong>on</strong>sistent with that <strong>of</strong> queue length. So we<br />
can capture network states according to △CP. The detailed<br />
figures show how CP value ranged in <strong>on</strong>e <strong>of</strong> <strong>the</strong> period,<br />
which show that CP can sense c<strong>on</strong>gesti<strong>on</strong> accurately and<br />
characterize c<strong>on</strong>gesti<strong>on</strong> particularly. Compared with end-toend<br />
metrics or single ECN feedback, CP can provide more<br />
accurate and richer informati<strong>on</strong> about network states.<br />
III. <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> PROTOCOL<br />
A. The descripti<strong>on</strong> <strong>of</strong> <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> protocol<br />
<str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> protocol c<strong>on</strong>trols <str<strong>on</strong>g>TCP</str<strong>on</strong>g> behavior based <strong>on</strong> predicti<strong>on</strong><br />
<strong>of</strong> CP. Fig.2 gives <strong>the</strong> pseudo code <strong>of</strong> <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g>’s sender<br />
CWND(pkt)<br />
Queue Length(byte)<br />
CP[i]<br />
CP[i]<br />
45<br />
40<br />
35<br />
30<br />
25<br />
20<br />
15<br />
10<br />
5<br />
Loss rate: 0<br />
0<br />
4 6 8 10 12<br />
Time(s)<br />
14 16 18 20<br />
(a) <str<strong>on</strong>g>TCP</str<strong>on</strong>g> window without link loss<br />
5000<br />
4000<br />
3000<br />
2000<br />
1000<br />
Loss rate: 0<br />
0<br />
4 6 8 10 12<br />
Time(s)<br />
14 16 18 20<br />
(c) Queue Length without link loss<br />
1.2<br />
1.0<br />
0.8<br />
0.6<br />
0.4<br />
0.2<br />
0.0<br />
1.0<br />
0.8<br />
0.6<br />
0.4<br />
0.2<br />
0.0<br />
4 6 8 10 12 14 16 18 20<br />
Time(s)<br />
Loss rate: 0<br />
7.40 7.45 7.50 7.55 7.60 7.65<br />
Time(s)<br />
(e) CP without link loss<br />
CWND(pkt)<br />
Queue length(byte)<br />
CP [i]<br />
CP [i]<br />
40<br />
35<br />
30<br />
25<br />
20<br />
15<br />
10<br />
5<br />
0<br />
5000<br />
4000<br />
3000<br />
2000<br />
1000<br />
Loss rate: 0.001<br />
4 6 8 10 12<br />
Time(s)<br />
14 16 18 20<br />
(b) <str<strong>on</strong>g>TCP</str<strong>on</strong>g> window with link loss<br />
0<br />
4 6 8 10 12 14 16 18 20<br />
Time(s)<br />
Loss rate: 0.001<br />
(d) Queue Length with link loss<br />
1.2<br />
1.0<br />
0.8<br />
0.6<br />
0.4<br />
0.2<br />
0.0<br />
1.2<br />
1.0<br />
0.8<br />
0.6<br />
0.4<br />
0.2<br />
0.0<br />
4 6 8 10 12 14 16 18 20<br />
Time(s)<br />
Loss rate: 0.001<br />
7.3 7.4 7.5 7.6 7.7 7.8<br />
Time(s)<br />
(f) CP with link loss<br />
Fig. 1: Correlati<strong>on</strong> between CP and network state<br />
receiving procedure.<br />
While receiving an ACK packet, <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> sender will<br />
recalculate new CP value and get △CP.<br />
If <strong>the</strong> current ACK is new, <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> sender operates <strong>the</strong><br />
same as <str<strong>on</strong>g>TCP</str<strong>on</strong>g> NewReno does. Since routers support ECN and<br />
<str<strong>on</strong>g>TCP</str<strong>on</strong>g> senders negotiate about ECN, senders will check CE bit<br />
<strong>of</strong> arrived ACK. If it is set to 1, senders will trigger ecnacti<strong>on</strong>()<br />
and <strong>the</strong>n deal with packets in slow start or c<strong>on</strong>gesti<strong>on</strong><br />
avoidance.<br />
If current ACK is duplicate and △CP > 0, <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g><br />
sender c<strong>on</strong>cludes that <strong>the</strong> c<strong>on</strong>gesti<strong>on</strong> occurs. The sender will<br />
adjust <strong>the</strong> sending rate and retransmit <strong>the</strong> data packet. If<br />
978-1-4244-2324-8/08/$25.00 © 2008 IEEE.<br />
This full text paper was peer reviewed at <strong>the</strong> directi<strong>on</strong> <strong>of</strong> IEEE Communicati<strong>on</strong>s Society subject matter experts for publicati<strong>on</strong> in <strong>the</strong> IEEE "GLOBECOM" 2008 proceedings.
Recv( ACK[i] ):<br />
CP[i] → CP[i − 1];<br />
calculate CP[i];<br />
CP[i]-CP[i − 1] →△CP ;<br />
if newACK <strong>the</strong>n<br />
if ACK[i].CE=1<br />
ecn-acti<strong>on</strong>()<br />
SS() or CA()<br />
else<br />
SS() or CA() //Same as Newreno<br />
endif;<br />
else <strong>the</strong>n<br />
if △CP > 0<br />
Rate<str<strong>on</strong>g>C<strong>on</strong>trol</str<strong>on</strong>g>() //Same as Westwood<br />
Retransmit()<br />
else<br />
Retransmit()<br />
endif;<br />
Fig. 2: Pseudo code <strong>of</strong> <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g>’s sender receiving procedure<br />
Time t1<br />
Time t2<br />
Ack[ 7]<br />
ecnecho Ack[ 0]<br />
ecnecho<br />
Time t3 A<br />
0 0 0 1 1 1 1 1<br />
1 0 0 0 1 1 1 1<br />
1 1 0 0 0 1 1 1<br />
Time t3 B 0 1 0 0 0 1 1 1<br />
Fig. 3: The first scenario<br />
current ACK is duplicate and △CP ≤ 0, <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> sender<br />
<strong>on</strong>ly retransmits <strong>the</strong> data packet. <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> modified sender’s<br />
behavior by △CP when <strong>the</strong>re are packet losses. This is <strong>the</strong><br />
important distinguishing feature <strong>of</strong> <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> with respect to<br />
o<strong>the</strong>r <str<strong>on</strong>g>TCP</str<strong>on</strong>g> variants. For example, <strong>the</strong> sender <strong>of</strong> <str<strong>on</strong>g>TCP</str<strong>on</strong>g> Westwood<br />
will trigger Rate<str<strong>on</strong>g>C<strong>on</strong>trol</str<strong>on</strong>g> without care about <strong>the</strong> situati<strong>on</strong> <strong>of</strong><br />
mid routers, and that <strong>of</strong> Jersey will decide whe<strong>the</strong>r to do<br />
Rate<str<strong>on</strong>g>C<strong>on</strong>trol</str<strong>on</strong>g> just by single ECN signal.<br />
Additi<strong>on</strong>ally, <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g>’s sender estimates <strong>the</strong> eligible bandwidth<br />
based <strong>on</strong> ACK packets arriving interval and adjusts<br />
<strong>the</strong> ssthresh (slow star thresh) and cwnd appropriately. This<br />
method to do Rate<str<strong>on</strong>g>C<strong>on</strong>trol</str<strong>on</strong>g> procedure is <strong>the</strong> same as <str<strong>on</strong>g>TCP</str<strong>on</strong>g><br />
Westwood, which can be described as follows.<br />
ssthresh =(BWE∗RT Tmin)/seg size;<br />
if(cwnd > ssthresh) cwnd = ssthresh;<br />
Like <str<strong>on</strong>g>TCP</str<strong>on</strong>g> Jersey, <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> also employs threshold marking<br />
method in ECN. C<strong>on</strong>cretely, <strong>the</strong> router marks all <strong>the</strong> packets<br />
when <strong>the</strong> EWMA-averaged queue length exceeds a given<br />
threshold, which is set to 1/3 <strong>of</strong> <strong>the</strong> link buffer capacity in<br />
experiments.<br />
B. Analysis <strong>of</strong> <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g><br />
In this secti<strong>on</strong>, we give two scenarios to show how <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<br />
<str<strong>on</strong>g>PCP</str<strong>on</strong>g> works in hybrid networks.<br />
As shown in Fig 3, <strong>the</strong> CE lists at t1, t2 and t3 are<br />
given, where t2 is <strong>the</strong> time when <strong>the</strong> sender receives <strong>the</strong> first<br />
ACK packet after t1, and t3 is after t2. Att1, <strong>the</strong> CE list<br />
<strong>of</strong> <strong>the</strong> latest 8 ACK packets is 00011111. At t2, <strong>the</strong> sender<br />
Time t1<br />
Time t2<br />
Time t3<br />
Time t4 A<br />
Time t4 B<br />
Ack[ 7]<br />
ecnecho Ack[ 0]<br />
ecnecho<br />
0<br />
0<br />
0 1<br />
1 1<br />
0 0 0 0 1 1 1 1<br />
0 0 0 0 0 1 1 1<br />
1 0 0 0 0 0 1 1<br />
0 0 0 0 0 0 1 1<br />
Fig. 4: The sec<strong>on</strong>d scenario<br />
receives a duplicate ACK in which CE=1. So <strong>the</strong> CE list<br />
<strong>of</strong> <strong>the</strong> latest 8 ACK packets is 10001111 at t2. In some<br />
protocols, for example, <str<strong>on</strong>g>TCP</str<strong>on</strong>g> Jersey, <strong>the</strong> sender will trigger<br />
c<strong>on</strong>gesti<strong>on</strong> c<strong>on</strong>trol. However, In <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g>, calculating result<br />
<strong>of</strong> CP[1] = CP[2] = 0.4 means that probability <strong>of</strong> c<strong>on</strong>gesti<strong>on</strong><br />
occurred in time t2 is not increased. So <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> sender does<br />
not invoke Rate<str<strong>on</strong>g>C<strong>on</strong>trol</str<strong>on</strong>g> procedure at t2.<br />
At t3, if <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g>’s sender receives a duplicate ACK in<br />
which CE=1 and gets CP[3] = 0.55. DuetoCP[3] >CP[2],<br />
<str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g>’s sender predicts that c<strong>on</strong>gesti<strong>on</strong> would occur so<strong>on</strong><br />
and triggers <strong>the</strong> c<strong>on</strong>gesti<strong>on</strong> c<strong>on</strong>trol mechanism at <strong>the</strong> moment.<br />
On <strong>the</strong> c<strong>on</strong>trary, if <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g>’s sender receives a duplicate<br />
ACK in which CE=0 and gets CP[3] = 0.35. Due to<br />
CP[3] CP[3]. On <strong>the</strong> c<strong>on</strong>trary,<br />
as l<strong>on</strong>g as CP[4] is less than CP[3], <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g>’s sender will<br />
not decrease <strong>the</strong> sending rate.<br />
It is obvious that in <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> protocol, even if <strong>the</strong> sender<br />
received duplicate ACKs caused by several errors, as l<strong>on</strong>g<br />
as <strong>the</strong> queue length does not exceed <strong>the</strong> threshold or <strong>the</strong><br />
c<strong>on</strong>gesti<strong>on</strong> probability does not increase, <strong>the</strong> sender will not<br />
decrease its sending rate. C<strong>on</strong>trarily, even if <strong>the</strong>re is <strong>on</strong>ly <strong>on</strong>e<br />
duplicate packet arrival, <strong>the</strong> sending rate might decline because<br />
<strong>of</strong> CP value being increased.<br />
As a whole, <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> is based <strong>on</strong> ECN mark. By deducing<br />
a c<strong>on</strong>gesti<strong>on</strong> probability, <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> can protect <str<strong>on</strong>g>TCP</str<strong>on</strong>g> c<strong>on</strong>necti<strong>on</strong><br />
from short-term, recoverable, n<strong>on</strong>-c<strong>on</strong>gestive packet<br />
losses, and enhance its performance in hybrid network eventually.<br />
IV. PERFORMANCE EVALUATION<br />
We have d<strong>on</strong>e <strong>the</strong> necessary code modificati<strong>on</strong> in NS2 [11]<br />
to simulate <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g>. The modificati<strong>on</strong> includes overwriting<br />
978-1-4244-2324-8/08/$25.00 © 2008 IEEE.<br />
This full text paper was peer reviewed at <strong>the</strong> directi<strong>on</strong> <strong>of</strong> IEEE Communicati<strong>on</strong>s Society subject matter experts for publicati<strong>on</strong> in <strong>the</strong> IEEE "GLOBECOM" 2008 proceedings.<br />
1<br />
1
S<br />
10Mbps<br />
45ms<br />
BS<br />
2Mbps<br />
1ms<br />
Fig. 5: Network Topology 1<br />
Fig. 6: Comparis<strong>on</strong> <strong>of</strong> throughput <strong>on</strong> network topology 1<br />
droptail, downloading Westwood [13] and Jersey [12], appending<br />
<str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> and so <strong>on</strong>.<br />
A. Throughput analysis <strong>on</strong> topology 1<br />
The simulati<strong>on</strong> envir<strong>on</strong>ment is <strong>the</strong> same with that used<br />
in Ref. [12]. As shown in Fig.5, <strong>the</strong> source c<strong>on</strong>nects to a<br />
base stati<strong>on</strong> via a 10 Mb/s wired link with 45 ms <strong>on</strong>eway<br />
delay. The base stati<strong>on</strong> is linked to <strong>the</strong> destinati<strong>on</strong>, a<br />
wireless mobile node, via a 2 Mb/s loss channel with 1 ms<br />
delay. A single <str<strong>on</strong>g>TCP</str<strong>on</strong>g> c<strong>on</strong>necti<strong>on</strong> running a l<strong>on</strong>g-lived FTP<br />
applicati<strong>on</strong> delivers data from <strong>the</strong> source to <strong>the</strong> destinati<strong>on</strong>.<br />
We run <strong>the</strong> simulati<strong>on</strong> for <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g>, Westwood, and Jersey<br />
respectively. In our experiments, <strong>the</strong> random link error rate at<br />
<strong>the</strong> wireless bottleneck link varies from 0.001 to 0.1, which<br />
creates by a simple uni<strong>on</strong> error model. The simulati<strong>on</strong> time<br />
is 100 sec<strong>on</strong>ds. The throughput <strong>of</strong> different protocols are<br />
shown in Fig.6. Throughput <strong>of</strong> Westwood falls behind that <strong>of</strong><br />
Jersey and <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> because Westwood handles corrupti<strong>on</strong> by<br />
estimate available bandwidth <strong>on</strong>ly. For link error rate smaller<br />
than 0.005, Jersey and <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> perform closely to each<br />
o<strong>the</strong>r. Bey<strong>on</strong>d that point, <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> starts to outperform Jersey.<br />
Especially when <strong>the</strong> loss rate increases to 0.01, <strong>the</strong> throughput<br />
<strong>of</strong> <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> outperforms Jersey by 23% and Westwood by<br />
50%.<br />
B. Throughput analysis <strong>on</strong> topology 2<br />
Simulati<strong>on</strong>s <strong>of</strong> this secti<strong>on</strong> are based <strong>on</strong> <strong>the</strong> topology shown<br />
in Fig.7,which is <strong>the</strong> same as that used in Ref. [13]. As shown<br />
in Fig.7, <strong>on</strong>e <str<strong>on</strong>g>TCP</str<strong>on</strong>g> flow is sent from R0 to R3, link R1-R2<br />
emulates a l<strong>on</strong>g delay pipe <strong>of</strong> Internet, and <strong>the</strong> last hop is a<br />
wireless link with error model. C<strong>on</strong>cretely, <strong>the</strong> bandwidth <strong>of</strong><br />
access link is 100 Mbps with 3 ms delay, <strong>the</strong> bandwidth <strong>of</strong><br />
wireless link is 10 Mbps with 3 ms delay. The bandwidth <strong>of</strong><br />
bottleneck is 5 Mbps with 40 ms delay. The buffer is set to<br />
be 100 packets. The simulati<strong>on</strong> lasts for 100 s.<br />
Fig.8 gives <strong>the</strong> throughput comparis<strong>on</strong> <strong>of</strong> <strong>the</strong> three algorithms<br />
under different link. As shown in Fig.8, Jersey’s<br />
throughput is close to Westwood’s, which is different from<br />
D<br />
R0<br />
100 Mbps<br />
3 ms<br />
R1<br />
5 Mbps<br />
40 ms<br />
R2<br />
10 Mbps<br />
3 ms<br />
Fig. 7: Network topology 2<br />
Fig. 8: Comparis<strong>on</strong> <strong>of</strong> throughput <strong>on</strong> network topology 2<br />
<strong>the</strong> simulati<strong>on</strong> results in topology 1. The reas<strong>on</strong> is that <strong>the</strong>re<br />
is an obvious bottleneck in topology 2, which results in<br />
more c<strong>on</strong>gesti<strong>on</strong> losses. It is observed that Jersey experiences<br />
performance degradati<strong>on</strong> in <strong>the</strong> case that c<strong>on</strong>gesti<strong>on</strong> losses<br />
and error losses coexist. It is clear that <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> can get<br />
higher throughput in this case. Especially, when <strong>the</strong> packet loss<br />
rate is 0.01, Jersey’s throughput is 1300Kbps and Westwood’s<br />
throughput is 1340Kbps, but <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> can get 1444Kbps<br />
throughput.<br />
Then we introduce exp<strong>on</strong>ential distributed ON/OFF flow in<br />
topology 2. Its sending rate is 5 Mbps, and <strong>the</strong>re are 25 ms<br />
to be “<strong>on</strong>” state in 100 ms period. Throughput under such<br />
situati<strong>on</strong> are shown in Table I.<br />
TABLE I: Comparis<strong>on</strong> <strong>of</strong> throughput with ON/OFF flow in<br />
network topology 2<br />
Loss rate: 0.001 Loss rate: 0.005 Loss rate: 0.01<br />
<str<strong>on</strong>g>Protocol</str<strong>on</strong>g> <str<strong>on</strong>g>TCP</str<strong>on</strong>g> UDP <str<strong>on</strong>g>TCP</str<strong>on</strong>g> UDP <str<strong>on</strong>g>TCP</str<strong>on</strong>g> UDP<br />
(kbps) (kbps) (kbps) (kbps) (kbps) (kbps)<br />
Westwood 1694 936 1457 971 1346 970<br />
Jersey 1437 1114 1393 1041 1359 1039<br />
<str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> 1679 994 1618 1039 1482 1055<br />
As shown in Table I, <strong>the</strong> throughput <strong>of</strong> <strong>the</strong> three algorithms<br />
are decreasing with <strong>the</strong> increasing <strong>of</strong> loss rate. Westwood’s<br />
throughput decreases by 20% when link loss rate varies from<br />
0.001 to 0.01, but <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g>’s throughput <strong>on</strong>ly decreases<br />
by 11%. Moreover, <strong>the</strong> total throughput <strong>of</strong> <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> is <strong>the</strong><br />
highest in <strong>the</strong> three algorithms. It is anticipated that <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g><br />
can cope with error losses better than <strong>the</strong> o<strong>the</strong>r <str<strong>on</strong>g>TCP</str<strong>on</strong>g> variants<br />
by using c<strong>on</strong>gesti<strong>on</strong> probability.<br />
C. Fairness analysis<br />
Fairness is an important metric for evaluating <str<strong>on</strong>g>TCP</str<strong>on</strong>g> protocol.<br />
Multiple c<strong>on</strong>necti<strong>on</strong>s <strong>of</strong> <strong>the</strong> same <str<strong>on</strong>g>TCP</str<strong>on</strong>g> scheme must cooperate<br />
fairly. Network topology 3 shown in Fig.9 is used to test this<br />
978-1-4244-2324-8/08/$25.00 © 2008 IEEE.<br />
This full text paper was peer reviewed at <strong>the</strong> directi<strong>on</strong> <strong>of</strong> IEEE Communicati<strong>on</strong>s Society subject matter experts for publicati<strong>on</strong> in <strong>the</strong> IEEE "GLOBECOM" 2008 proceedings.<br />
R3
S1<br />
Si<br />
Sn<br />
100 Mbps<br />
3 ms<br />
R1<br />
20 Mbps<br />
40 ms<br />
R2<br />
10 Mbps<br />
3 ms<br />
Fig. 9: Network topology 3<br />
metric, in which <strong>the</strong> network settings are marked. As shown<br />
in Fig.9, 10 same <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> flows share a 20 Mbps bottleneck<br />
link.<br />
We use Jain’s fairness index to justify <strong>the</strong> fairness <strong>of</strong><br />
<str<strong>on</strong>g>TCP</str<strong>on</strong>g> variants Ref. [14]. Simulati<strong>on</strong> results are summarized in<br />
Table II, which show that all <str<strong>on</strong>g>TCP</str<strong>on</strong>g> variants including <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<br />
<str<strong>on</strong>g>PCP</str<strong>on</strong>g> achieve fairly satisfactory fairness index with different<br />
link losses. Meanwhile, it is shown from Table II that <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<br />
<str<strong>on</strong>g>PCP</str<strong>on</strong>g> still keeps higher throughput than Westwood and Jersey<br />
in this case.<br />
TABLE II: Comparis<strong>on</strong> <strong>of</strong> fairness and throughput<br />
Westwood Jersey <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g><br />
LossRate Thru Fair Thru Fair Thru Fair<br />
(kbps) (-) (kbps) (-) (kbps) (-)<br />
0 1759 0.935 1783 0.962 1795 0.997<br />
0.001 1741 0.998 1757 0.999 1761 0.999<br />
0.005 1612 0.999 1619 1.0 1647 1.0<br />
0.01 1457 0.999 1489 0.998 1532 0.999<br />
D. Friendliness analysis<br />
The experiment <strong>of</strong> friendliness partiti<strong>on</strong>s ten flows into two<br />
parts, <strong>on</strong>e uses <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g>, <strong>the</strong> o<strong>the</strong>r uses <strong>the</strong> traditi<strong>on</strong>al <str<strong>on</strong>g>TCP</str<strong>on</strong>g><br />
protocol, such as Westwood.<br />
Table III gives <strong>the</strong> change <strong>of</strong> average throughput, which is<br />
calculated by summing up <strong>the</strong> throughput <strong>of</strong> <strong>the</strong> same <str<strong>on</strong>g>TCP</str<strong>on</strong>g><br />
variant and divided by <strong>the</strong> number <strong>of</strong> c<strong>on</strong>necti<strong>on</strong>s. It is clear<br />
that <strong>the</strong> bandwidth allocati<strong>on</strong> <strong>of</strong> <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> and Westwood is<br />
close to its fair share without link loss occurring. When <strong>the</strong><br />
link loss rate raises from 0.1% to 1%, <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> achieves<br />
higher throughput than Westwood. The results are according<br />
with that <strong>of</strong> <strong>on</strong>e <str<strong>on</strong>g>TCP</str<strong>on</strong>g> flow. But <strong>the</strong> increase is within a<br />
tolerable range as regard to friendliness performance. It can be<br />
c<strong>on</strong>cluded that <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> can coexist friendly with Westwood.<br />
V. CONCLUSION<br />
In this paper we proposed a novel <str<strong>on</strong>g>Transport</str<strong>on</strong>g> <str<strong>on</strong>g>C<strong>on</strong>trol</str<strong>on</strong>g> <str<strong>on</strong>g>Protocol</str<strong>on</strong>g><br />
based <strong>on</strong> <strong>the</strong> predicti<strong>on</strong> <strong>of</strong> C<strong>on</strong>gesti<strong>on</strong> Probability. It<br />
can improve <str<strong>on</strong>g>TCP</str<strong>on</strong>g> throughput in hybrid networks because <strong>the</strong><br />
sender judges network state by serial ECN feedbacks o<strong>the</strong>r<br />
than single ECN feedback or packet dropping.<br />
Actually, <strong>the</strong> c<strong>on</strong>gesti<strong>on</strong>-aware scheme used in <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g><br />
can be easily extended to existed <str<strong>on</strong>g>TCP</str<strong>on</strong>g> variants. Our next works<br />
focus <strong>on</strong> checking its functi<strong>on</strong> <strong>on</strong> o<strong>the</strong>r <str<strong>on</strong>g>TCP</str<strong>on</strong>g> variants both <strong>on</strong><br />
NS2 simulati<strong>on</strong> and wired/wirelss testbed.<br />
D1<br />
Di<br />
Dn<br />
TABLE III: Friendliness Performance<br />
Loss rate: 0 Loss rate:0.001<br />
Westwood:<str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> Westwood <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> Westwood <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g><br />
(kbps) (kbps) (kbps) (kbps)<br />
3:7 1162.00 1174.85 1161.33 1174.14<br />
5:5 1316.80 1331.40 1312.80 1329.40<br />
7:3 1519.28 1536.66 1511.00 1539.00<br />
Loss rate: 0.005 Loss rate:0.01<br />
Westwood:<str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> Westwood <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g> Westwood <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-<str<strong>on</strong>g>PCP</str<strong>on</strong>g><br />
(kbps) (kbps) (kbps) (kbps)<br />
3:7 1289.66 1314.85 1099.00 1186.57<br />
5:5 1294.80 1319.80 1269.80 1352.2<br />
7:3 1485.28 1508.33 1388.14 1506.00<br />
ACKNOWLEDGEMENT<br />
This work was partially supported by <strong>the</strong> Nati<strong>on</strong>al Natural<br />
Science Foundati<strong>on</strong> <strong>of</strong> China (60673164), Provincial Natural<br />
Science Foundati<strong>on</strong> <strong>of</strong> Hunan (06JJ10009), <strong>the</strong> Specialized<br />
Research Fund for <strong>the</strong> Doctoral Program <strong>of</strong> Higher Educati<strong>on</strong><br />
<strong>of</strong> China (20060533057), Program for New Century Excellent<br />
Talents in University (NCET-05-0683), CityU Strategic<br />
Research Grant No. 7002214.<br />
REFERENCES<br />
[1] T. Nurmela, “Distinguishing between c<strong>on</strong>gesti<strong>on</strong> and corrupti<strong>on</strong> using<br />
end-to-end approaches,” Seminar <strong>on</strong> Selected Topics <strong>on</strong> <str<strong>on</strong>g>Transport</str<strong>on</strong>g> <str<strong>on</strong>g>Protocol</str<strong>on</strong>g>s<br />
for Wireless Internet, 2004.<br />
[2] Gurtov, S. Floyd, “Modeling Wireless Links for <str<strong>on</strong>g>Transport</str<strong>on</strong>g> <str<strong>on</strong>g>Protocol</str<strong>on</strong>g>s,”<br />
ACM SIGCOMM Computer Communicati<strong>on</strong>s Review, Vol. 34, No. 2,<br />
April 2004.<br />
[3] C. Casetti, M. Gerla, S. Mascolo, M. Y. Sanadidi, R. Wang, “<str<strong>on</strong>g>TCP</str<strong>on</strong>g> Westwood:<br />
bandwidth estimati<strong>on</strong> for enhanced transport over wireless links,”<br />
ACM C<strong>on</strong>ference <strong>on</strong> Mobile Computing and Networking (MOBICOM),<br />
Rome, July 2001.<br />
[4] V. Raghunathan and P. R. Kumar, “A Counterexample in C<strong>on</strong>gesti<strong>on</strong><br />
<str<strong>on</strong>g>C<strong>on</strong>trol</str<strong>on</strong>g> <strong>of</strong> Wireless Networks,” Performance Evaluati<strong>on</strong>, vol. 64, no. 5,<br />
pp. 399-418, June 2007.<br />
[5] K. Xu, Y .Tian, N. Ansari, “Improving <str<strong>on</strong>g>TCP</str<strong>on</strong>g> performance in integrated<br />
wireless communicati<strong>on</strong>s networks,” Computer Networks, vol. 47, no. 2,<br />
pp. 219-237, 2005.<br />
[6] F. Abrantes, M. Ricardo, “XCP for shared-Access Multi-Rate Media,”<br />
ACM SIGOSOMM Computer Communicati<strong>on</strong> Review, vol. 36, no. 3,<br />
pp. 27-38, July 2006.<br />
[7] K. Xu, Y. Tian, and N. Ansari, <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-Jersey for Wireless IP Communicati<strong>on</strong>s,IEEE<br />
Journal <strong>on</strong> Selected Areas in Communicati<strong>on</strong>s, Vol. 22, No.<br />
4, pp. 747-756, May 2004.<br />
[8] S. Biaz, X. Wang, “Can ECN Be Used to Differentiate C<strong>on</strong>gesti<strong>on</strong><br />
Losses from Wireless Losses,” Technical Report CSSE04-04, May, 2004.<br />
[9] H. Bai, D. Lilja, and M. Atiquzzaman, “Applying speculative technique<br />
to improve <str<strong>on</strong>g>TCP</str<strong>on</strong>g> throughput over lossy links,” IEEE Global Ccmmunicati<strong>on</strong>s<br />
C<strong>on</strong>ference (GLOBECOM), St. Louis, November 2005.<br />
[10] Xu C.b.,Ke ping, L. Shi zh<strong>on</strong>g, “An improved <str<strong>on</strong>g>TCP</str<strong>on</strong>g> c<strong>on</strong>gesti<strong>on</strong> c<strong>on</strong>trol<br />
mechanism <str<strong>on</strong>g>TCP</str<strong>on</strong>g>-RD for wireless network,” JOURNAL-CHINA INSTI-<br />
TUTE OF COMMUNICATIONS, 2003, VOL 24; PART 3, pages 86-90.<br />
[11] VINT Project UC Berkeley/LBNL, NS2: network simulator versi<strong>on</strong> 2.<br />
http://www.isi.edu/nsnam/ns.<br />
[12] <str<strong>on</strong>g>TCP</str<strong>on</strong>g> Jersey Home Page, http://web.njit.edu/anl/download.html.<br />
[13] Westwood Home Page, http://www.cs.ucla.edu/NRL/hpi/tcpw/index.html.<br />
[14] R. Jain, D. chiu, and W. Hawe, “A quantitative measure <strong>of</strong> fairness and<br />
discriminati<strong>on</strong> in shared computer systems,”DEC,Res.Rep.TR-301,1984.<br />
978-1-4244-2324-8/08/$25.00 © 2008 IEEE.<br />
This full text paper was peer reviewed at <strong>the</strong> directi<strong>on</strong> <strong>of</strong> IEEE Communicati<strong>on</strong>s Society subject matter experts for publicati<strong>on</strong> in <strong>the</strong> IEEE "GLOBECOM" 2008 proceedings.