THE EXTREME FUTURE (Part 3)
THE EXTREME FUTURE (Part 3)
THE EXTREME FUTURE (Part 3)
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
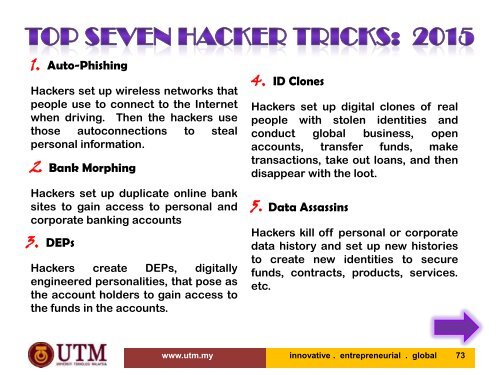
1. Auto-Phishing<br />
Hackers set up wireless networks that<br />
people use to connect to the Internet<br />
when driving. Then the hackers use<br />
those autoconnections to steal<br />
personal information.<br />
2 Bank Morphing<br />
Hackers set up duplicate online bank<br />
sites to gain access to personal and<br />
corporate banking accounts<br />
3. DEPs<br />
Hackers create DEPs, digitally<br />
engineered personalities, that pose as<br />
the account holders to gain access to<br />
the funds in the accounts.<br />
4. ID Clones<br />
Hackers set up digital clones of real<br />
people with stolen identities and<br />
conduct global business, open<br />
accounts, transfer funds, make<br />
transactions, take out loans, and then<br />
disappear with the loot.<br />
5. Data Assassins<br />
Hackers kill off personal or corporate<br />
data history and set up new histories<br />
to create new identities to secure<br />
funds, contracts, products, services.<br />
etc.<br />
www.utm.my innovative . entrepreneurial . global 73