Global Phishing Survey: Trends and Domain Name Use in 2H2012
Global Phishing Survey: Trends and Domain Name Use in 2H2012
Global Phishing Survey: Trends and Domain Name Use in 2H2012
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
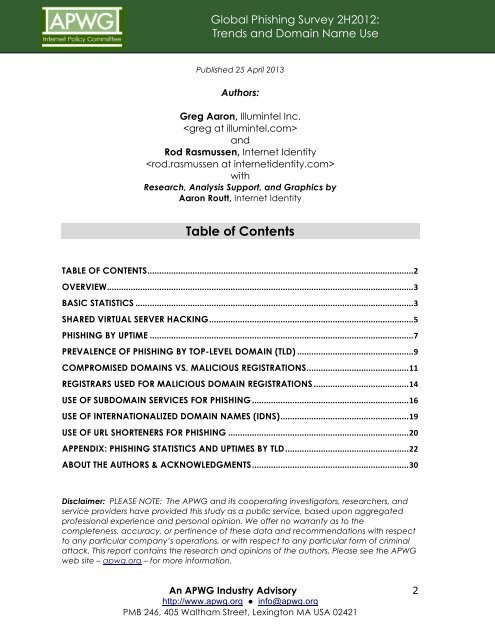
<strong>Global</strong> <strong>Phish<strong>in</strong>g</strong> <strong>Survey</strong> <strong>2H2012</strong>:<br />
<strong>Trends</strong> <strong>and</strong> <strong>Doma<strong>in</strong></strong> <strong>Name</strong> <strong>Use</strong><br />
Published 25 April 2013<br />
Authors:<br />
Greg Aaron, Illum<strong>in</strong>tel Inc.<br />
<br />
<strong>and</strong><br />
Rod Rasmussen, Internet Identity<br />
<br />
with<br />
Research, Analysis Support, <strong>and</strong> Graphics by<br />
Aaron Routt, Internet Identity<br />
Table of Contents<br />
TABLE OF CONTENTS................................................................................................................2<br />
OVERVIEW.................................................................................................................................3<br />
BASIC STATISTICS .....................................................................................................................3<br />
SHARED VIRTUAL SERVER HACKING......................................................................................5<br />
PHISHING BY UPTIME ...............................................................................................................7<br />
PREVALENCE OF PHISHING BY TOP-LEVEL DOMAIN (TLD) .................................................9<br />
COMPROMISED DOMAINS VS. MALICIOUS REGISTRATIONS...........................................11<br />
REGISTRARS USED FOR MALICIOUS DOMAIN REGISTRATIONS ........................................14<br />
USE OF SUBDOMAIN SERVICES FOR PHISHING ..................................................................16<br />
USE OF INTERNATIONALIZED DOMAIN NAMES (IDNS)......................................................19<br />
USE OF URL SHORTENERS FOR PHISHING ............................................................................20<br />
APPENDIX: PHISHING STATISTICS AND UPTIMES BY TLD....................................................22<br />
ABOUT THE AUTHORS & ACKNOWLEDGMENTS..................................................................30<br />
Disclaimer: PLEASE NOTE: The APWG <strong>and</strong> its cooperat<strong>in</strong>g <strong>in</strong>vestigators, researchers, <strong>and</strong><br />
service providers have provided this study as a public service, based upon aggregated<br />
professional experience <strong>and</strong> personal op<strong>in</strong>ion. We offer no warranty as to the<br />
completeness, accuracy, or pert<strong>in</strong>ence of these data <strong>and</strong> recommendations with respect<br />
to any particular company’s operations, or with respect to any particular form of crim<strong>in</strong>al<br />
attack. This report conta<strong>in</strong>s the research <strong>and</strong> op<strong>in</strong>ions of the authors. Please see the APWG<br />
web site – apwg.org – for more <strong>in</strong>formation.<br />
An APWG Industry Advisory<br />
http://www.apwg.org ● <strong>in</strong>fo@apwg.org<br />
PMB 246, 405 Waltham Street, Lex<strong>in</strong>gton MA USA 02421<br />
2