Detecting and Defending against Malicious Attacks in the iTrust ...
Detecting and Defending against Malicious Attacks in the iTrust ...
Detecting and Defending against Malicious Attacks in the iTrust ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
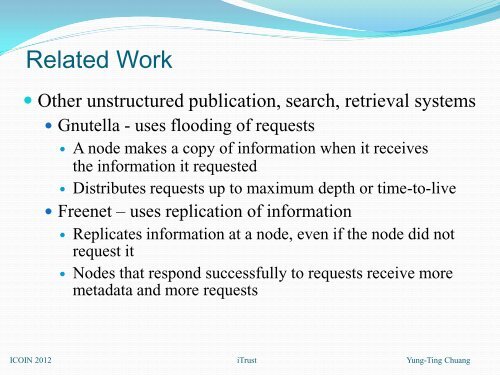
Related Work<br />
O<strong>the</strong>r unstructured publication, search, retrieval systems<br />
Gnutella - uses flood<strong>in</strong>g of requests<br />
A node makes a copy of <strong>in</strong>formation when it receives<br />
<strong>the</strong> <strong>in</strong>formation it requested<br />
Distributes requests up to maximum depth or time-to-live<br />
Freenet – uses replication of <strong>in</strong>formation<br />
Replicates <strong>in</strong>formation at a node, even if <strong>the</strong> node did not<br />
request it<br />
Nodes that respond successfully to requests receive more<br />
metadata <strong>and</strong> more requests<br />
ICOIN 2012 <strong>iTrust</strong> Yung-T<strong>in</strong>g Chuang