Detecting and Defending against Malicious Attacks in the iTrust ...
Detecting and Defending against Malicious Attacks in the iTrust ...
Detecting and Defending against Malicious Attacks in the iTrust ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
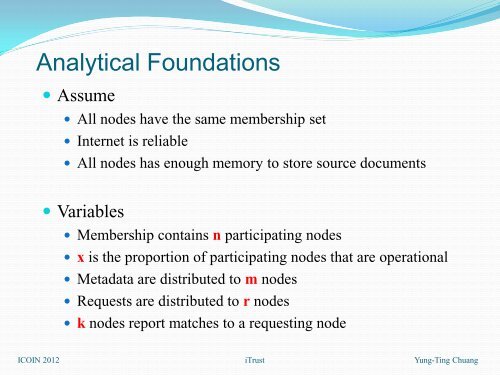
Analytical Foundations<br />
Assume<br />
All nodes have <strong>the</strong> same membership set<br />
Internet is reliable<br />
All nodes has enough memory to store source documents<br />
Variables<br />
Membership conta<strong>in</strong>s n participat<strong>in</strong>g nodes<br />
x is <strong>the</strong> proportion of participat<strong>in</strong>g nodes that are operational<br />
Metadata are distributed to m nodes<br />
Requests are distributed to r nodes<br />
k nodes report matches to a request<strong>in</strong>g node<br />
ICOIN 2012 <strong>iTrust</strong> Yung-T<strong>in</strong>g Chuang