Crypto Virology Seminar.PPT - 123SeminarsOnly
Crypto Virology Seminar.PPT - 123SeminarsOnly
Crypto Virology Seminar.PPT - 123SeminarsOnly
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
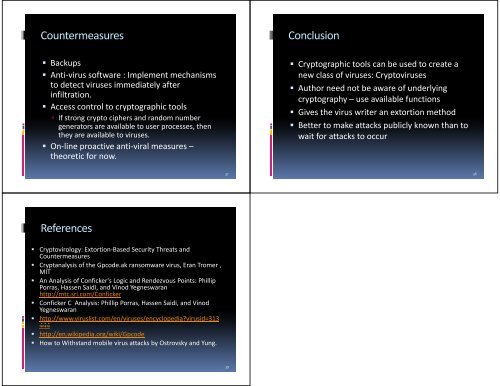
Countermeasures<br />
BBackups k<br />
Anti‐virus software : Implement mechanisms<br />
to detect viruses immediately after<br />
infiltration.<br />
Access control to cryptographic tools<br />
If strong crypto ciphers and random number<br />
generators are available to user processes, then<br />
they are available to viruses.<br />
On‐line proactive anti‐viral measures –<br />
theoretic for now now.<br />
References<br />
<strong>Crypto</strong>virology: Extortion‐Based Security Threats and<br />
Countermeasures<br />
Cryptanalysis of the Gpcode.ak ransomware virus, Eran Tromer ,<br />
MIT<br />
An Analysis of Conficker's Logic and Rendezvous Points: Phillip<br />
Porras, Hassen Saidi, and Vinod Yegneswaran<br />
http://mtc.sri.com/Conficker<br />
CConficker fi k C Analysis: A l i Philli Phillip PPorras, HHassen Sidi Saidi, and d Vi Vinod d<br />
Yegneswaran<br />
http://www.viruslist.com/en/viruses/encyclopedia?virusid=313<br />
444<br />
http://en.wikipedia.org/wiki/Gpcode<br />
How to Withstand mobile virus attacks by Ostrovsky and Yung.<br />
37<br />
39<br />
Conclusion<br />
C<strong>Crypto</strong>graphic hi tools l can bbe used d to create a<br />
new class of viruses: <strong>Crypto</strong>viruses<br />
Author h need d not bbe aware of f underlying d l<br />
cryptography –use available functions<br />
Gives the virus writer an extortion method<br />
Better to make attacks publicly known than to<br />
wait for attacks to occur<br />
38