sKyWIper (a.k.a. Flame a.k.a. Flamer): A complex ... - CrySyS Lab
sKyWIper (a.k.a. Flame a.k.a. Flamer): A complex ... - CrySyS Lab
sKyWIper (a.k.a. Flame a.k.a. Flamer): A complex ... - CrySyS Lab
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
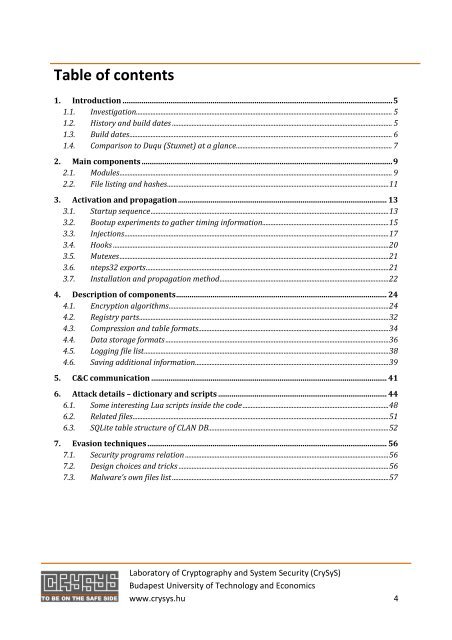
Table of contents<br />
1. Introduction .............................................................................................................................................5<br />
1.1. Investigation............................................................................................................................................................ 5<br />
1.2. History and build dates ...................................................................................................................................... 5<br />
1.3. Build dates................................................................................................................................................................ 6<br />
1.4. Comparison to Duqu (Stuxnet) at a glance............................................................................................... 7<br />
2. Main components ...................................................................................................................................9<br />
2.1. Modules...................................................................................................................................................................... 9<br />
2.2. File listing and hashes.......................................................................................................................................11<br />
3. Activation and propagation............................................................................................................. 13<br />
3.1. Startup sequence.................................................................................................................................................13<br />
3.2. Bootup experiments to gather timing information.............................................................................15<br />
3.3. Injections.................................................................................................................................................................17<br />
3.4. Hooks ........................................................................................................................................................................20<br />
3.5. Mutexes....................................................................................................................................................................21<br />
3.6. nteps32 exports....................................................................................................................................................21<br />
3.7. Installation and propagation method.......................................................................................................22<br />
4. Description of components.............................................................................................................. 24<br />
4.1. Encryption algorithms......................................................................................................................................24<br />
4.2. Registry parts........................................................................................................................................................32<br />
4.3. Compression and table formats....................................................................................................................34<br />
4.4. Data storage formats ........................................................................................................................................36<br />
4.5. Logging file list.....................................................................................................................................................38<br />
4.6. Saving additional information......................................................................................................................39<br />
5. C&C communication ........................................................................................................................... 41<br />
6. Attack details – dictionary and scripts ........................................................................................ 44<br />
6.1. Some interesting Lua scripts inside the code.........................................................................................48<br />
6.2. Related files............................................................................................................................................................51<br />
6.3. SQLite table structure of CLAN DB..............................................................................................................52<br />
7. Evasion techniques ............................................................................................................................. 56<br />
7.1. Security programs relation ............................................................................................................................56<br />
7.2. Design choices and tricks ................................................................................................................................56<br />
7.3. Malware’s own files list ....................................................................................................................................57<br />
<strong>Lab</strong>oratory of Cryptography and System Security (<strong>CrySyS</strong>)<br />
Budapest University of Technology and Economics<br />
www.crysys.hu 4