slides - Stanford Crypto Group
slides - Stanford Crypto Group
slides - Stanford Crypto Group
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
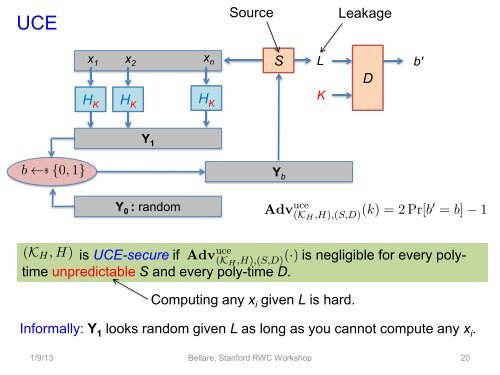
UCE<br />
x1 x x 2<br />
n S<br />
H K<br />
H K<br />
Y 1<br />
Y 0 : random<br />
H K<br />
Source Leakage<br />
is UCE-secure if is negligible for every polytime<br />
unpredictable S and every poly-time D.<br />
Y b<br />
Computing any x i given L is hard.<br />
Informally: Y 1 looks random given L as long as you cannot compute any x i.<br />
1/9/13 Bellare, <strong>Stanford</strong> RWC Workshop<br />
L<br />
K<br />
D<br />
b'<br />
20