McAfee Agent 4.0 Patch 3 for Windows Release Notes
McAfee Agent 4.0 Patch 3 for Windows Release Notes
McAfee Agent 4.0 Patch 3 for Windows Release Notes
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
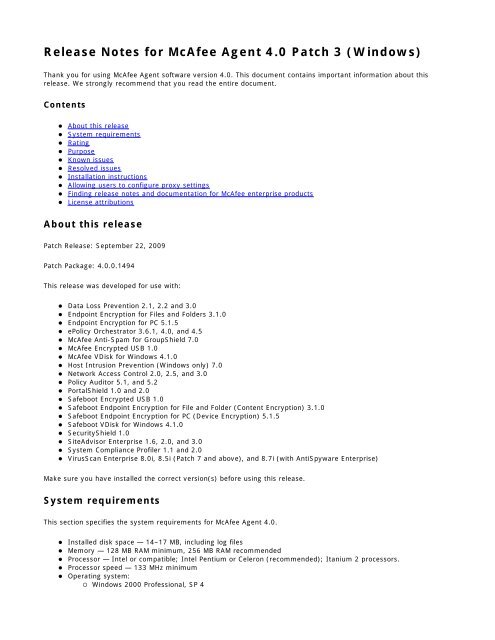
<strong>Release</strong> <strong>Notes</strong> <strong>for</strong> <strong>McAfee</strong> <strong>Agent</strong> <strong>4.0</strong> <strong>Patch</strong> 3 (<strong>Windows</strong>)<br />
Thank you <strong>for</strong> using <strong>McAfee</strong> <strong>Agent</strong> software version <strong>4.0</strong>. This document contains important in<strong>for</strong>mation about this<br />
release. We strongly recommend that you read the entire document.<br />
Contents<br />
About this release<br />
System requirements<br />
Rating<br />
Purpose<br />
Known issues<br />
Resolved issues<br />
Installation instructions<br />
Allowing users to configure proxy settings<br />
Finding release notes and documentation <strong>for</strong> <strong>McAfee</strong> enterprise products<br />
License attributions<br />
About this release<br />
<strong>Patch</strong> <strong>Release</strong>: September 22, 2009<br />
<strong>Patch</strong> Package: <strong>4.0</strong>.0.1494<br />
This release was developed <strong>for</strong> use with:<br />
Data Loss Prevention 2.1, 2.2 and 3.0<br />
Endpoint Encryption <strong>for</strong> Files and Folders 3.1.0<br />
Endpoint Encryption <strong>for</strong> PC 5.1.5<br />
ePolicy Orchestrator 3.6.1, <strong>4.0</strong>, and 4.5<br />
<strong>McAfee</strong> Anti-Spam <strong>for</strong> GroupShield 7.0<br />
<strong>McAfee</strong> Encrypted USB 1.0<br />
<strong>McAfee</strong> VDisk <strong>for</strong> <strong>Windows</strong> 4.1.0<br />
Host Intrusion Prevention (<strong>Windows</strong> only) 7.0<br />
Network Access Control 2.0, 2.5, and 3.0<br />
Policy Auditor 5.1, and 5.2<br />
PortalShield 1.0 and 2.0<br />
Safeboot Encrypted USB 1.0<br />
Safeboot Endpoint Encryption <strong>for</strong> File and Folder (Content Encryption) 3.1.0<br />
Safeboot Endpoint Encryption <strong>for</strong> PC (Device Encryption) 5.1.5<br />
Safeboot VDisk <strong>for</strong> <strong>Windows</strong> 4.1.0<br />
SecurityShield 1.0<br />
SiteAdvisor Enterprise 1.6, 2.0, and 3.0<br />
System Compliance Profiler 1.1 and 2.0<br />
VirusScan Enterprise 8.0i, 8.5i (<strong>Patch</strong> 7 and above), and 8.7i (with AntiSpyware Enterprise)<br />
Make sure you have installed the correct version(s) be<strong>for</strong>e using this release.<br />
System requirements<br />
This section specifies the system requirements <strong>for</strong> <strong>McAfee</strong> <strong>Agent</strong> <strong>4.0</strong>.<br />
Installed disk space — 14–17 MB, including log files<br />
Memory — 128 MB RAM minimum, 256 MB RAM recommended<br />
Processor — Intel or compatible; Intel Pentium or Celeron (recommended); Itanium 2 processors.<br />
Processor speed — 133 MHz minimum<br />
Operating system:<br />
<strong>Windows</strong> 2000 Professional, SP 4
Rating<br />
<strong>Windows</strong> 2000 Server, SP 4<br />
<strong>Windows</strong> 2000 Advanced Server, SP 4<br />
<strong>Windows</strong> 2000 Datacenter Server, SP 4<br />
<strong>Windows</strong> 2003 Server, Standard Edition, SP 1 or 2<br />
<strong>Windows</strong> 2003 Server, Enterprise Edition, SP 1 or 2<br />
<strong>Windows</strong> 2003 Server R2, Standard Edition, SP 1 or 2<br />
<strong>Windows</strong> 2003 Server R2, Enterprise Edition, SP 1 or 2<br />
<strong>Windows</strong> 2003 Server, Standard x64 Edition, SP 1 or 2<br />
<strong>Windows</strong> 2003 Server, Enterprise x64 Edition, SP 1 or 2<br />
<strong>Windows</strong> 2003 Server R2, Standard x64 Edition, SP 1 or 2<br />
<strong>Windows</strong> 2003 Server R2, Enterprise x64 Edition, SP 1 or 2<br />
<strong>Windows</strong> XP Embedded<br />
<strong>Windows</strong> XP Home, SP 1 and 2<br />
<strong>Windows</strong> XP Professional, SP 1, 2, and 3<br />
<strong>Windows</strong> XP Professional, x64 SP 2<br />
<strong>Windows</strong> XP Tablet PC 2005<br />
<strong>Windows</strong> Vista, SP 1 and 2<br />
<strong>Windows</strong> Vista x64, SP 1 and 2<br />
<strong>Windows</strong> Server 2008<br />
<strong>Windows</strong> Server 2008 x64<br />
<strong>Windows</strong> Server 2008 R2<br />
<strong>Windows</strong> 7<br />
<strong>Windows</strong> 7 x64<br />
Note: VirusScan Enterprise <strong>Windows</strong> 7 support requires VSE 8.7i <strong>Patch</strong> 2 or above.<br />
Complete <strong>Windows</strong> 7 support requires <strong>McAfee</strong> <strong>Agent</strong> Extension patch 3 be installed on the ePolicy Orchestrator<br />
server<br />
This release does not support <strong>Windows</strong> 95, <strong>Windows</strong> 98, <strong>Windows</strong> Millennium Edition or <strong>Windows</strong> NT.<br />
The <strong>McAfee</strong> Security single tray icon does not appear on 64-bit systems.<br />
<strong>McAfee</strong> recommends this release <strong>for</strong> all environments. This update should be applied at the earliest convenience. For<br />
more in<strong>for</strong>mation, see KB article KB51560.<br />
Purpose<br />
This document supplements the <strong>McAfee</strong> <strong>Agent</strong> <strong>4.0</strong> Readme file in the release package, and details fixes included in<br />
<strong>McAfee</strong> <strong>Agent</strong> <strong>4.0</strong> <strong>Patch</strong> releases.<br />
This <strong>Patch</strong> contains a variety of improvements. <strong>McAfee</strong> has spent a significant amount of time finding, fixing, and<br />
testing the fixes in this release. Please review the Known and Resolved Issues lists <strong>for</strong> additional in<strong>for</strong>mation on the<br />
individual issues.<br />
Refer to online KnowledgeBase article KB65953 at https://kc.mcafee.com <strong>for</strong> the most current in<strong>for</strong>mation regarding<br />
this release.<br />
Known issues<br />
Known issues in this release of the software are described below:<br />
Issue: This patch fails to install on systems without a “My Documents” folder or with a “My Documents” folder<br />
that is mapped to a network folder on systems with a <strong>McAfee</strong> <strong>Agent</strong> version less than <strong>4.0</strong>.0.1437. In these<br />
scenarios the <strong>McAfee</strong> <strong>Agent</strong> fails to install. Once this patch is installed, Resolved Issue 1 prevents this from<br />
occurring in subsequent <strong>McAfee</strong> <strong>Agent</strong> upgrades. (Reference: 485728, 474870)<br />
Workaround: A system must be without the <strong>McAfee</strong> <strong>Agent</strong>, have a local “My Documents” folder, or have a
<strong>McAfee</strong> <strong>Agent</strong> version that is <strong>4.0</strong>.0.1437 or newer installed, prior to installing this patch.<br />
Issue: On systems with EMC’s Power Path software installed, the <strong>McAfee</strong> <strong>Agent</strong> fails to start and the error<br />
message “Cannot generate keypair” appears in the <strong>Agent</strong>_ log file. (Reference: 452955,<br />
436864, 445158, 447296, 451228, 437592 )<br />
Workaround: The <strong>McAfee</strong> <strong>Agent</strong> must be rolled back to Common Management <strong>Agent</strong> version 3.6.0 <strong>Patch</strong> 4 or<br />
upgraded to <strong>McAfee</strong> <strong>Agent</strong> 4.5 <strong>for</strong> the systems with EMC's Power Path software installed.<br />
Issue: The <strong>McAfee</strong> <strong>Agent</strong> now allows update and deployment tasks to be postponed. When an end user<br />
postpones a deployment the error message “The task has failed” appears in the <strong>Agent</strong>_ log file.<br />
(Reference: 469427, 503321)<br />
Workaround: There is no known workaround <strong>for</strong> this issue.<br />
Resolved issues<br />
Issues that are resolved in this release are listed below.<br />
1. Issue: The <strong>McAfee</strong> <strong>Agent</strong> installation process checked <strong>for</strong> the existence of the “My Documents” folder. If it was<br />
not present or mapped to a network folder, the installation failed. (Reference: 474870)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> installation process no longer requires the “My Documents” folder to be present.<br />
2. Issue: The <strong>McAfee</strong> <strong>Agent</strong> upgrade process failed to update the sitelist.xml file with all of the required policy<br />
in<strong>for</strong>mation, resulting in the incorrect repository sort order being used. (Reference: 450082)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> upgrade process has been updated to trigger the system to request the current<br />
site list from the ePolicy Orchestrator server.<br />
3. Issue: The <strong>McAfee</strong> <strong>Agent</strong> installation process would fail when the current user's user name contained non-ASCII<br />
(ex. Japanese) characters. (Reference: 453206)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> installation process now allows user names to contain non-ASCII characters.<br />
4. Issue: The presence of certain environment variables (i.e. http_proxy, ftp_proxy) caused the <strong>McAfee</strong> <strong>Agent</strong> to<br />
attempt to communicate using the proxy address specified in the variable. (Reference: 457621)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> now uses the proxy specified on the Proxy Policy Setting page only and avoids<br />
the use of any environment variables.<br />
5. Issue: When attempting to determine if the system is a laptop the Property Collection process could cause the<br />
<strong>McAfee</strong> <strong>Agent</strong> to crash or fail to respond. (Reference: 457837)<br />
Resolution: The Property Collection process has been updated to always return even if it cannot determine<br />
whether the system is a laptop. The system appears as “Unknown” in the ePolicy Orchestrator console when this<br />
occurs.<br />
6. Issue: The “/<strong>for</strong>ceinstall” switch failed to cause a new <strong>McAfee</strong> <strong>Agent</strong> GUID to be created when installing over an<br />
existing installation. (Reference: 462869)<br />
Resolution: The “/<strong>for</strong>ceinstall” switch now regenerates the <strong>McAfee</strong> <strong>Agent</strong> GUID when installing over an existing<br />
installation.<br />
Note: When using the “/<strong>for</strong>ceinstall” switch in combination with the “/upgrade” switch a new <strong>McAfee</strong> <strong>Agent</strong><br />
GUID is not generated.<br />
7. Issue: When the Update process failed to download a file from a UNC repository the download would not be<br />
attempted from the next repository. (Reference: 462898)
Resolution: The Update process now attempts to download the file from all defined repositories until it is<br />
successfully downloaded or all available repositories are exhausted.<br />
8. Issue: When a product detection or installation script was executing and the Update process failed to download<br />
a requested file and failed over to a subsequent repository, a second Update dialog box was displayed.<br />
(Reference: 462953)<br />
Resolution: The Update process now only displays one Update dialog box per update.<br />
9. Issue: When the Update process failed to download a requested file and failed over to a subsequent repository,<br />
a DAT or Engine update could fail. (Reference: 464970)<br />
Resolution: The Update process now allows DAT or Engine updating to complete when failing over to a<br />
subsequent repository.<br />
10. Issue: On 64-bit Microsoft <strong>Windows</strong> systems with no users logged on the error message “Failed to Open<br />
Process. Error code 57” appeared in the <strong>Agent</strong>_ log file. (Reference: 468073)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> no longer records this message.<br />
11. Issue: The <strong>McAfee</strong> <strong>Agent</strong> allowed an update task to be postponed, but it did not allow deployment tasks to be<br />
postponed. (Reference: 469427)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> now allows update and deployment tasks to be postponed.<br />
12. Issue: When a Super<strong>Agent</strong> repository had more than five systems waiting to connect <strong>for</strong> download, subsequent<br />
system connections were rejected causing the associated download to fail. (Reference: 471505)<br />
Resolution: Super<strong>Agent</strong> repositories now support up to 200 systems waiting to connect <strong>for</strong> download.<br />
13. Issue: On Microsoft Vista machines, the reported User Name property was always the name of the first user to<br />
log on after the system was restarted. (Reference: 472980)<br />
Resolution: The User Name property is now reported as the most recently logged on user.<br />
14. Issue: When the <strong>McAfee</strong> <strong>Agent</strong> failed to connect to ePolicy Orchestrator or ePolicy Orchestrator rejected the<br />
connection during a <strong>McAfee</strong> <strong>Agent</strong> “Wakeup with Full Properties” request, the <strong>McAfee</strong> <strong>Agent</strong> would only send<br />
incremental properties the next time it reported its properties. (Reference: 475006)<br />
Resolution: <strong>McAfee</strong> <strong>Agent</strong> “Wakeup with Full Properties” requests are now retried until successfully sent to the<br />
ePolicy Orchestrator.<br />
15. Issue: During passive transfers the <strong>McAfee</strong> <strong>Agent</strong> failed to respond correctly to certain non-Microsoft FTP<br />
responses causing the deployment or update to fail. (Reference: 477298)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> now properly responds to standard passive FTP transfer response codes.<br />
16. Issue: The “/upgrade” switch failed to remove or upgrade obsolete data from previous installations. (Reference:<br />
479814)<br />
Resolution: The “/upgrade” switch now properly removes or upgrades obsolete data from previous installations.<br />
17. Issue: When viewed through the <strong>Windows</strong> Task Manager, the <strong>McAfee</strong> Status Monitor process (udaterui.exe)<br />
reported 16 I/O Reads per second at idle. (Reference: 484245)<br />
Resolution: The <strong>McAfee</strong> Status Monitor process now only per<strong>for</strong>ms read operations when required.
18. Issue: When policy en<strong>for</strong>cement occurred while the repository was being sorted, the <strong>McAfee</strong> <strong>Agent</strong> would leak<br />
virtual memory. (Reference: 484776)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> no longer leaks memory when en<strong>for</strong>cing policies during a repository sort.<br />
19. Issue: When directed to use a language other than the system default through the “UseLanguage” feature, the<br />
reported language remained the system default language. (Reference: 492157)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> now properly reports the language in use.<br />
20. Issue: The <strong>McAfee</strong> <strong>Agent</strong> did not support the ePolicy Orchestrator “Duplicate List” feature. (Reference: 494754,<br />
500714)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> now supports the ePolicy Orchestrator “Duplicate List” feature.<br />
21. Issue: When the “catalog.z” file was larger than 4,096 bytes, updates via Local and Distributed UNC<br />
repositories failed and the error message “Error occurred while downloading catalog.z” appeared in the <strong>Agent</strong>_<br />
log file. (Reference: 480163)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> is no longer dependant on the size of the “catalog.z” file.<br />
22. Issue: The <strong>McAfee</strong> <strong>Agent</strong> was vulnerable to the issue described in Security Bulletin SB10002, “<strong>McAfee</strong> Security<br />
Bulletin - ActiveX security issue in CMA and <strong>McAfee</strong> <strong>Agent</strong>. (Reference: 495121)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> upgrade process has been updated to implement the required registry<br />
modifications.<br />
23. Issue: The <strong>McAfee</strong> <strong>Agent</strong> did not provide an embedded credential installation package. (Reference: 432427)<br />
Resolution: An embedded credential installation package is now available. The embedded credential package is<br />
separate from the General Use package. If you require the embedded credentials package<br />
(MA400P3Win_EMBEDDED.zip), it is available on the <strong>McAfee</strong> download and ServicePortal sites.<br />
Note: The embedded credentials package is several megabytes larger than the General Use package. Please<br />
note that this can result in a significant impact in some environments. The ability to embed credentials is the<br />
only difference between the packages.<br />
Issues from the <strong>Patch</strong> 2 release of the software that are resolved in this release are listed below.<br />
1. Issue: The error message “Failed >> Setting naInet transfer option RelativePath =” appeared in the McScript<br />
and Aviview log files when a UNC repository when it was defined without a subdirectory following a share name.<br />
For example, the definition “\\server\share\directory” worked as expected, but the definition “\\server\share”<br />
caused the error message to appear. The download would work correctly in spite of this error message.<br />
(Reference: 391232, 455183)<br />
Resolution: UNC repositories can now be defined with or without specifying a subdirectory.<br />
2. Issue: When a UNC repository was configured to use download credentials and to use ping time repository<br />
sorting, and the UNC repository was inaccessible <strong>for</strong> pinging, the <strong>McAfee</strong> <strong>Agent</strong> might run with lowered<br />
privileges. When this occurred, the error message “Permission denied” appeared in the <strong>Agent</strong>_ log file when the<br />
<strong>McAfee</strong> <strong>Agent</strong> attempted to write to the registry. (Reference: 416303, 417404, 432919, 432931)<br />
Resolution: The UNC Repository Updater process now continues to run under the System user’s credentials<br />
when a UNC repository cannot be reached during the ping time sorting process.<br />
3. Issue: When UNC repositories were configured to use the download credentials of the logged-on user and the<br />
logged-on user was not an Administrator, the download would fail. (Reference: 418162, 424677, 425454,<br />
437584, 458651, 466124, 466186)
Resolution: The UNC Repository Updater process now allows UNC replication using the logged-on user’s<br />
credentials.<br />
4. Issue: The download of a product deployment process could fail when an earlier version of the product had<br />
been deployed. (Reference: 421222)<br />
Resolution: The product deployment process has been updated to consistently detect and deploy updated<br />
products.<br />
5. Issue: Updates via a UNC repository would fail on 64-bit systems when the update was configured to use the<br />
credentials of the logged-on user. When this occurred, the error message “Failed to steal Explorer token” would<br />
appear in the <strong>Agent</strong>_ log file. (Reference: 429292)<br />
Resolution: The UNC Repository Updater process now runs on 64-bit operating systems when defined to use<br />
download credentials.<br />
6. Issue: During the repository download process when the download of a product failed and a subsequent<br />
download of a different product succeeded, the download session was treated as a success and not retried using<br />
the next repository. (Reference: 429950, 429759)<br />
Resolution: The repository download process has been updated to retry the entire update from the next<br />
repository when any products fail to download.<br />
7. Issue: The <strong>McAfee</strong> <strong>Agent</strong> no longer provided an embedded credential installation package option. (Reference:<br />
432427)<br />
Resolution: An embedded credential installation package is now available through <strong>McAfee</strong> Tier III Support. For<br />
in<strong>for</strong>mation on obtaining this package, see KB article KB59954.<br />
8. Issue: Requesting updates from the ePolicy Orchestrator server through HTTP resulted in a large number of<br />
“client denied by server configuration…” error messages to be incorrectly reported in the server log file.<br />
(Reference: 433704)<br />
Resolution: The HTTP connection process has been updated to avoid creating this error message incorrectly.<br />
9. Issue: During the deployment of Host Intrusion Prevention, the product detection script would prematurely end<br />
when the Host Intrusion Prevention service was not registered. (Reference: 436914)<br />
Resolution: The script engine has been updated to properly detect and report unregistered services as an error<br />
rather than exiting.<br />
10. Issue: Non-English versions of the <strong>McAfee</strong> <strong>Agent</strong> could fail to apply incremental DAT updates, and instead<br />
download the full DAT package, resulting in unnecessary network bandwidth consumption. (Reference: 439397,<br />
441679, 443381)<br />
Resolution: The DAT update process has been updated to ensure that non-English versions apply incremental<br />
updates correctly.<br />
11. Issue: The error message “File is corrupt. Downloading complete file again.” would be incorrectly written to the<br />
McScript log file during the update process. (Reference: 440080, 445479)<br />
Resolution: The update process has been updated to record this error message only when the file download<br />
process detects a corrupt file.<br />
12. Issue: After a successful update of a DAT file, a temporary copy of the DAT package would not be deleted from<br />
the <strong>McAfee</strong> <strong>Agent</strong> data directory, resulting in unnecessary disk space consumption. (Reference: 440930)<br />
Note: This issue could consume all of a system's available disk space.
Resolution: The DAT update process now deletes the DAT package after a successful update.<br />
13. Issue: The <strong>McAfee</strong> <strong>Agent</strong> upgrade process would fail to install when it could not successfully terminate the<br />
currently running version, resulting in a <strong>McAfee</strong> <strong>Agent</strong> that failed to start. (Reference: 441182)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> upgrade process has been updated so that if it detects that the currently<br />
installed version cannot be stopped, it quits and leaves the currently running version of the <strong>McAfee</strong> <strong>Agent</strong><br />
operational.<br />
14. Issue: The error log file did not “roll over,” resulting in unnecessary disk space consumption. (Reference:<br />
449107, 449111, 449341, 450554, 462905)<br />
Note: This issue could consume all of a system's available disk space.<br />
Resolution: The error log file now “rolls over” in the same manner as the <strong>Agent</strong>_ log file.<br />
Note: When writing a message to the error log file, the size of the current file is checked. If the size equals or<br />
exceeds the file size limit set in the registry, the following actions will occur:<br />
If the backup file (<strong>Agent</strong>__backup.log) exists in the target folder, it is deleted.<br />
The current file (<strong>Agent</strong>_.log) is renamed as the backup file.<br />
A new current file is created and the message is written in this file.<br />
15. Issue: When the Internet Explorer setting “Automatically detect settings” is selected and “Use a proxy server<br />
<strong>for</strong> your LAN” is not selected, an automated configuration script caused the update process to fail. (Reference:<br />
450058, 451906, 452028, 461210, 463930)<br />
Resolution: The update process now runs as expected, independent of these Internet Explorer settings.<br />
Issues from the <strong>Patch</strong> 1 release of the software that are resolved in this release are listed below.<br />
1. Issue: An update dialog box appeared in English rather than the non-English language running on the system.<br />
(Reference: 389523)<br />
Resolution: Update dialog boxes now appear in the language running on the system.<br />
2. Issue: When using the “/<strong>for</strong>ceinstall” switch and only changing the data (/datadir=) folder, the<br />
upgrade process did not remove the old data folder and used the new folder. (Reference: 393182)<br />
Resolution: Now when using the “/<strong>for</strong>ceinstall” switch and changing the data (/datadir=) folder,<br />
the upgrade process removes the old data folder and uses the new folder.<br />
3. Issue: When the <strong>Agent</strong>Events folder was missing, the upgrade process failed. (Reference: 393764)<br />
Resolution: Now the upgrade process creates the <strong>Agent</strong>Events folder when it is missing.<br />
4. Issue: Managed product installation routines were executed each time a deployment task ran on systems that<br />
used a language other than English. (Reference: 399232)<br />
Resolution: Managed product installation routines now execute only when necessary.<br />
5. Issue: If the installation or data folder contained a double-byte character, the upgrade process failed.<br />
(Reference: 404111)<br />
Resolution: Now the installation and data folders can contain non-English characters.<br />
6. Issue: When executing the VirusScan update process (mcupdate.exe) with the “/update” and “/quiet” switches,<br />
an upgrade dialog box would still be displayed. (Reference: 405004)
Resolution: The VirusScan update process now honors the “/quiet” switch.<br />
7. Issue: The upgrade process was checking <strong>for</strong> the existence of the “My Favorites” and “Fonts” folders. If they<br />
were not present, the upgrade failed. (Reference: 405314)<br />
Resolution: The upgrade process no longer requires the “My Favorites” and “Fonts” folders to be present.<br />
8. Issue: When an error occurred during Host Intrusion Prevention policy en<strong>for</strong>cement, the system could be<br />
“locked out of the network”. (Reference: 406896)<br />
Resolution: Now the ePolicy Orchestrator server connection in<strong>for</strong>mation (server IP, name and port, and<br />
incoming agent wake-up port) is recorded. This allows Host Intrusion Prevention to create specific rules that<br />
allow communication to and from the ePolicy Orchestrator server, even in the absence of Host IPS policies.<br />
9. Issue: The name of the ePO server the system last communicated with appears in the XML log file. The value is<br />
initially blank and remained blank <strong>for</strong> a period of time after the first communication. (Reference: 407154)<br />
Resolution: The name of the ePO server the system last communicated with now appears immediately after the<br />
last server communication.<br />
10. Issue: The <strong>McAfee</strong> <strong>Agent</strong> deployed managed products to Microsoft Vista or <strong>Windows</strong> Server 2008 that were not<br />
supported on these plat<strong>for</strong>ms. (Reference: 408989)<br />
Resolution: Managed products are now deployed only to their supported plat<strong>for</strong>ms.<br />
11. Issue: The Mirror task created a duplicate repository, but it failed to copy the sitestat.xml file. This caused the<br />
duplicate repository to remain disabled. (Reference: 409637)<br />
Resolution: The Mirror task now copies the sitestat.xml file to the duplicated repository.<br />
12. Issue: During a managed product update, a dialog box could be presented requesting a system reboot. The<br />
dialog box asked the user if they wanted to reboot now and rebooted the system even when the user selected<br />
“No”. (Reference: 410573)<br />
Resolution: The managed product update process now honors the user's selected reboot response.<br />
13. Issue: Certain dates, such as leap years, were recorded incorrectly in the <strong>Agent</strong>_.xml log file.<br />
(Reference: 413415)<br />
Resolution: All dates are now recorded correctly in the <strong>Agent</strong>_.xml log file.<br />
14. Issue: The <strong>McAfee</strong> <strong>Agent</strong> only updated the VirusScan engine if the minor version was newer than what was<br />
installed. This prevented the VirusScan engine from updating to a newer build of the same version. (Reference:<br />
414065)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> now supports build-to-build VirusScan engine updates.<br />
15. Issue: The installation and upgrade processes failed if the data folder was located in the “<strong>Windows</strong>” or “WinNT”<br />
folders. (Reference: 415578)<br />
Resolution: Now the installation and upgrade processes allow the data folder to be located in the “<strong>Windows</strong>” or<br />
“WinNT” folders with the exception of the system32 folder. The installation and upgrade processes prohibit the<br />
data folder from including the system32 folder.<br />
16. Issue: Some non-<strong>McAfee</strong> product installation routines removed critical registry entries, such as the <strong>Windows</strong><br />
IStream COM registration, causing the <strong>McAfee</strong> <strong>Agent</strong> to fail. (Reference: 416298)<br />
Resolution: The upgrade process now re-registers the ole32.dll file when it detects it is missing.
17. Issue: The installation and upgrade processes failed if the installation or data folders contained double-byte<br />
characters. (Reference: 416559)<br />
Resolution: The installation and upgrade processes now allow the installation and data folders to contain<br />
double-byte characters.<br />
18. Issue: Several install and uninstall error messages made no sense when displayed on a Japanese language<br />
system. (Reference: 418729)<br />
Resolution: The upgrade process now displays meaningful install and uninstall error messages on a Japanese<br />
language system.<br />
19. Issue: On systems running VirusScan Enterprise version 8.0 the <strong>McAfee</strong> <strong>Agent</strong> did not remove the Temp files<br />
created during the execution of an “<strong>Agent</strong> Update Task”. (Reference: 419066)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> now removes the Temp files created during the execution of an “<strong>Agent</strong> Update<br />
Task”.<br />
Note: This change does not remove the Temp files created during the execution of an “<strong>Agent</strong> Update Task”<br />
prior to implementing this patch.<br />
20. Issue: During Policy En<strong>for</strong>cement, when the <strong>McAfee</strong> <strong>Agent</strong> failed to compile the policy file, the policy<br />
en<strong>for</strong>cement failed and the agent crashed on the next Policy En<strong>for</strong>cement. (Reference: 423070)<br />
Resolution: The <strong>McAfee</strong> <strong>Agent</strong> now detects failed Policy En<strong>for</strong>cements and retries the policy compilation until it<br />
completes successfully.<br />
21. Issue: DAT updates were postponed indefinitely and the message “Update will be retried after 3 mins because<br />
update is already in progress” appeared repeatedly in the agent log file. (Reference: 424203)<br />
Resolution: The DAT update process now terminates properly when it detects an error in an FTP transaction.<br />
22. Issue: In environments running the Early Adopter <strong>Release</strong> (November 11, 2008) the “/<strong>for</strong>ceinstall” switch did<br />
not work when applied against the MA <strong>4.0</strong> <strong>Patch</strong> 1 package generally available <strong>for</strong> download. (Reference:<br />
454619)<br />
Resolution: The MA <strong>4.0</strong> <strong>Patch</strong> 1 package has been updated allowing the “/<strong>for</strong>ceinstall” switch to work as<br />
expected.<br />
Issues previously resolved in the policy (Extension) pages are listed below.<br />
1. Issue: When a repository was added <strong>for</strong> one site, the user had to go to every other site and turn off the<br />
repository in the agent policies. In environments with a large number of repositories, this was very labor<br />
intensive. (Reference: 239994)<br />
Resolution: A checkbox has been added to “<strong>Agent</strong> Policy on Repository Page” that allows new repositories to be<br />
excluded by default. Now when a repository is added and the new checkbox is checked, the new repository is<br />
added to the disable list <strong>for</strong> each of the existing repositories.<br />
2. Issue: In environments with a large number of repositories, the policy page required several minutes to load.<br />
(Reference: 372087)<br />
Resolution: The policy page now loads in a much more reasonable amount of time.<br />
Installation instructions<br />
This section provides instructions <strong>for</strong> installing and upgrading <strong>McAfee</strong> <strong>Agent</strong> <strong>4.0</strong> <strong>for</strong> use with ePolicy Orchestrator<br />
versions 3.6.x and <strong>4.0</strong>.
Note: An embedded credentials package is available. For more in<strong>for</strong>mation and best practice recommendations, see<br />
KB article KB65538.<br />
Tasks<br />
Installing on ePolicy Orchestrator 3.6.x systems<br />
Installing on ePolicy Orchestrator 4.x systems<br />
Upgrading<br />
Installing, upgrading and uninstalling using <strong>Windows</strong> command-line switches<br />
Installing on ePolicy Orchestrator 3.6.x systems<br />
This section provides instructions <strong>for</strong> installing <strong>McAfee</strong> <strong>Agent</strong> <strong>4.0</strong> <strong>for</strong> use with ePolicy Orchestrator version 3.6.x on each<br />
of the supported operating systems.<br />
You must have administrator rights to per<strong>for</strong>m this task.<br />
1. Download and extract the agent package, MA400P3WIN.zip.<br />
2. Check in the NAP file, CMA360.nap, from the extracted agent package to the ePolicy Orchestrator repository.<br />
3. Check in the agent package to the ePolicy Orchestrator repository.<br />
4. Use one of these methods to install the agent on client systems:<br />
Push an agent using the Send <strong>Agent</strong> Install option.<br />
For third-party deployment methods, create an agent installation package, FramePkg.exe, using the<br />
<strong>Agent</strong> Installation Package Creation wizard.<br />
Create a deployment task.<br />
Installing on ePolicy Orchestrator 4.x systems<br />
This section provides instructions <strong>for</strong> installing <strong>McAfee</strong> <strong>Agent</strong> <strong>4.0</strong> <strong>for</strong> use with ePolicy Orchestrator <strong>4.0</strong> on <strong>Windows</strong><br />
using two different methods.<br />
Tasks<br />
Installing on <strong>Windows</strong> using ePolicy Orchestrator <strong>4.0</strong><br />
Installing on <strong>Windows</strong> using ePolicy Orchestrator 4.5<br />
Installing on <strong>Windows</strong> using third-party deployment methods<br />
Installing on <strong>Windows</strong> using ePolicy Orchestrator <strong>4.0</strong><br />
You must have administrator rights on the <strong>Windows</strong> system to per<strong>for</strong>m this task. The agent extension must be installed<br />
on the ePolicy Orchestrator server be<strong>for</strong>e the agent is installed on any clients.<br />
1. Download the current agent extension, EPOAGENTMETA.zip, and the <strong>Patch</strong> 3 agent package, MA400P3WIN.zip,<br />
to the system containing the ePolicy Orchestrator server.<br />
2. Install the agent extension:<br />
a. In the ePolicy Orchestrator <strong>4.0</strong> console, click Configuration.<br />
b. On the Extensions tab, click Install extension.<br />
c. Browse to the location containing EPOAGENTMETA.zip, select it and click OK. The Install Extensions<br />
summary page appears.<br />
d. Click OK to complete the installation of the extension.<br />
3. Check in the agent package to the ePolicy Orchestrator repository:<br />
Note: If installing on a computer running Common Management <strong>Agent</strong> 3.6, the package must be checked in to<br />
the Current repository branch.<br />
a. In the ePolicy Orchestrator <strong>4.0</strong> console, click Software.<br />
b. Click Check In Package.<br />
c. Browse to the location containing MA400P3WIN.zip, select it and click Next.<br />
d. Ensure that Current is selected in the Branch field.
e. Click Save.<br />
4. Create a deployment task or push the agent to client systems. If using the push method, follow these steps:<br />
a. In the ePolicy Orchestrator <strong>4.0</strong> console, click Systems.<br />
b. Select the target systems or groups.<br />
c. Click Deploy <strong>Agent</strong>.<br />
d. Select the version of the agent to be deployed.<br />
e. Type valid credentials in the Domain, User name, and Password fields.<br />
f. Click OK.<br />
Installing on <strong>Windows</strong> using ePolicy Orchestrator 4.5<br />
You must have administrator rights on the <strong>Windows</strong> system to per<strong>for</strong>m this task. The agent extension must be installed<br />
on the ePolicy Orchestrator server be<strong>for</strong>e the agent is installed on any clients.<br />
1. Download the current agent extension, EPOAGENTMETA.zip, and the <strong>Patch</strong> 3 agent package, MA400P3WIN.zip,<br />
to the system containing the ePolicy Orchestrator server.<br />
2. Install the agent extension:<br />
a. In the ePolicy Orchestrator 4.5 console, click Menu->Software->Extensions.<br />
b. Click “Install Extension” and browse to the location containing EPOAGENTMETA.zip, select it and click OK.<br />
The Install Extensions summary page appears.<br />
c. Browse to the location containing EPOAGENTMETA.zip, select it and click OK. The Install Extensions<br />
summary page appears.<br />
d. Click OK to complete the installation of the extension.<br />
3. Check in the agent package to the ePolicy Orchestrator repository:<br />
Note: If installing on a computer running Common Management <strong>Agent</strong> 3.6, the package must be checked in to<br />
the Current repository branch.<br />
a. In the ePolicy Orchestrator 4.5 console, click Menu->Software->Master Repository.<br />
b. Click Actions->Check In Package.<br />
c. Browse to the location containing MA400P3WIN.zip, select it and click Next.<br />
d. Ensure that Current is selected in the Branch field.<br />
e. Click Save.<br />
4. Create a deployment task or push the agent to client systems. If using the push method, follow these steps:<br />
a. In the ePolicy Orchestrator 4.5 console, click System Tree.<br />
b. Select the target systems or groups.<br />
c. Click Actions-><strong>Agent</strong>->Deploy <strong>Agent</strong><br />
d. Select the version of the agent to be deployed.<br />
e. Type valid credentials in the Domain, User name, and Password fields.<br />
f. Click OK.<br />
Installing on <strong>Windows</strong> using third-party deployment methods<br />
The agent extension must be installed on the ePolicy Orchestrator server be<strong>for</strong>e the agent is installed on any clients.<br />
Tip: This task requires the creation of an agent installation package, FramePkg.exe (see Step 4). Installation of the<br />
package requires administrator rights.<br />
1. Download the current agent extension, EPOAGENTMETA.zip, and the <strong>Patch</strong> 3 agent package, MA400P3WIN.zip,<br />
to the system containing the ePolicy Orchestrator server.<br />
2. Install the agent extension:<br />
a. In the ePolicy Orchestrator <strong>4.0</strong> console, click Configuration.<br />
b. On the Extensions tab, click Install extension.<br />
c. Browse to the location containing EPOAGENTMETA.zip, select it and click OK. The Install Extensions<br />
summary page appears.<br />
d. Click OK to complete the installation of the extension.<br />
3. Using the ePolicy Orchestrator <strong>4.0</strong> console, check in the agent package to the Current (default) repository<br />
branch.<br />
4. Create an installation package:<br />
a. In the ePolicy Orchestrator <strong>4.0</strong> console, click Systems.<br />
b. At the bottom of the System Tree, click New Systems.<br />
c. Select Create and download the agent installation package.
d. Deselect Use Credentials.<br />
e. Click OK. The Download file dialog box opens.<br />
f. Select FramePkg.exe and save it to the desktop.<br />
5. Note the location of the downloaded FramePkg.exe to identify it when using your third-party deployment<br />
system. You can add parameters and switches as allowed by your deployment system. For a list of available<br />
parameters, see Installing, upgrading and uninstalling using <strong>Windows</strong> command-line switches.<br />
Upgrading<br />
This section provides instructions <strong>for</strong> upgrading the agent from versions 3.5.5 and 3.6 to <strong>McAfee</strong> <strong>Agent</strong> <strong>4.0</strong>.<br />
Upgrading on <strong>Windows</strong> using FramePkg_upd.exe<br />
You must have administrator rights to per<strong>for</strong>m this task.<br />
1. Download and extract the <strong>Patch</strong> 3 agent package, MA400P3WIN.zip, to a temporary location.<br />
2. Copy FramePkg_upd.exe to a location on the target client.<br />
3. From the command line on the client, type /FramePkg_upd.exe /upgrade, where is the location<br />
containing the copied file. This command is the equivalent of double-clicking FramePkg_upd.exe in the folder<br />
containing the installation package.<br />
Installing, upgrading and uninstalling using <strong>Windows</strong> command-line<br />
switches<br />
This section describes using selected command-line and MSI parameters to specify installation and upgrading<br />
preferences. Use the list of tasks as a menu from which to select those that suit your circumstances and preferences.<br />
Tasks<br />
Installing the agent and data in their default locations using default site list and key in<strong>for</strong>mation<br />
Installing the agent in specified folders<br />
Installing the agent with user-selected policies<br />
Installing the agent and specifying the log folder<br />
Installing the agent with user-selected site in<strong>for</strong>mation and user-selected keys<br />
Installing the agent by <strong>for</strong>ce<br />
Installing without requiring specific user privileges<br />
Installing silently<br />
Installing with specification of interface and log file language<br />
Upgrading agent to a new version<br />
Uninstalling the agent<br />
Converting from unmanaged mode to managed mode<br />
Converting from managed mode to unmanaged mode<br />
Changing server<br />
Installing the agent and data in their default locations using default site<br />
list and key in<strong>for</strong>mation<br />
Use this command to install the agent, site list and keys in their default locations. This command is the equivalent of<br />
double-clicking the program file in the installation package.<br />
framepkg.exe<br />
Installing the agent in specified folders<br />
Use this command to install the agent in a folder other than the default. The example shown here specifies a folder <strong>for</strong><br />
the installation files (instdir) and a folder <strong>for</strong> the data files (datadir). These can be the same or different folders.
framepkg.exe /install=agent /instdir= /datadir=<br />
Installing the agent with user-selected policies<br />
Use this command <strong>for</strong> installation and upgrade to include policies selected by the administrator rather than the default<br />
policies.<br />
framepkg.exe /install=agent /agentpolicy=<br />
Note: Policies are stored in the server.xml file.<br />
The following steps illustrate how to create a server.xml file:<br />
1. Configure the policies on an ePolicy Orchestrator server.<br />
2. En<strong>for</strong>ce the policies on a selected client. The client’s server.xml file now includes the user-selected policies. The<br />
server.xml can be found on the client at Documents and Settings\All Users\Application Data\<strong>McAfee</strong>\Common<br />
Framework.<br />
3. Copy the new server.xml file from the client to a shared location.<br />
Installing the agent and specifying the log folder<br />
Use this command to install the agent in its default location and specify a log file other than the default log file as the<br />
record of the agent’s activities.<br />
framepkg.exe /install=agent /logdir=<br />
Note: The /logdir parameter can be appended to other installation commands.<br />
Installing the agent with user-selected site in<strong>for</strong>mation and user-selected<br />
keys<br />
Use this command to install the agent and specify a site list file and security keys (srpubkey.bin and reqseckey.bin)<br />
other than the defaults. This command is useful when upgrading an agent using FramePkg_upd.exe. It specifies the<br />
server with which the agent communicates, irrespective of the site in<strong>for</strong>mation embedded in the original installation<br />
package.<br />
framepkg.exe /install=agent /siteinfo=<br />
The security keys must be located in the same folder as the site list. Use ePolicy Orchestrator to export the files:<br />
1. Export the Sitelist file:<br />
a. Select Software | Master Repository.<br />
b. Click Export Sitelist.<br />
c. Save the file to a new location.<br />
2. Export the security keys:<br />
a. Select Configuration | Server Settings | Security Keys, and click Edit.<br />
b. Select Master <strong>Agent</strong>-server secure communication key, and click Export.<br />
c. Save the files to the same location as the Sitelist file.<br />
Installing the agent by <strong>for</strong>ce<br />
Use this command to delete the currently installed agent and <strong>for</strong>ce install a different agent only when:<br />
Downgrading to an earlier version of the agent.<br />
Changing the names of the folders that contain the agent.
Restoring the agent’s settings to a default state.<br />
framepkg.exe /install=agent /<strong>for</strong>ceinstall<br />
Note: <strong>McAfee</strong> strongly advises that you only use /<strong>for</strong>ceinstall to install the <strong>McAfee</strong> <strong>Agent</strong> under the conditions stated<br />
above, because the command:<br />
Deletes current program files and restores data files to a default state. As a result, all user-configured<br />
repositories and user-created tasks are lost.<br />
Removes the currently installed agent and introduces the risk that installation of the replacement agent could<br />
fail. As a result, one or more systems could have no agent at all.<br />
Sometimes requires a restart of the system.<br />
Installing without requiring specific user privileges<br />
Use this command to allow all users access to agent files and registry, regardless of their user privileges.<br />
framepkg.exe /install=agent /defaultpermissions<br />
Installing silently<br />
Use this command to install the agent without displaying in<strong>for</strong>mation dialog boxes on the client.<br />
framepkg.exe /install=agent /s or framepkg.exe /install=agent /silent<br />
Installing with specification of interface and log file language<br />
Use this command to install the agent and specify a language other than the target computer’s native language.<br />
framepkg.exe /install=agent /uselanguage=<br />
Language codes are:<br />
Language Code<br />
Chinese (Simplified) 0804<br />
Chinese (Traditional) 0404<br />
Dutch 0413<br />
English 0409<br />
French 040C<br />
German 0407<br />
Italian 0410<br />
Japanese 0411<br />
Korean 0412<br />
Polish 0415
Portuguese 0416<br />
Spanish 040A<br />
Swedish 041D<br />
Note: To restore the computer’s native language, type /resetlanguage<br />
Upgrading the agent to a new version<br />
Use either of these commands to upgrade the agent to a new version.<br />
framepkg_upd.exe or framepkg.exe /upgrade<br />
Using these commands is the equivalent of double-clicking FramePkg_upd.exe in the installation package.<br />
Uninstalling the agent<br />
Some managed products, such as <strong>McAfee</strong> VirusScan Enterprise and <strong>McAfee</strong> Host Intrusion Prevention, incorporate their<br />
own copies of the agent.<br />
Disconnect the agent from its ePO server, and if there are no point-products using it <strong>for</strong> updating, remove it<br />
completely:<br />
frminst.exe /remove=agent<br />
Remove the agent completely, but only if it is not connected to an ePO server and no point-products are using it<br />
<strong>for</strong> updating:<br />
frminst.exe /uninstall<br />
Remove the agent completely, even if it is connected to an ePO server or point-products are using it <strong>for</strong><br />
updating:<br />
frminst.exe /<strong>for</strong>ceuninstall<br />
Converting from unmanaged mode to managed mode<br />
Use this task to convert a client currently operating in unmanaged mode to managed mode.<br />
If the sitelist.xml file is from ePolicy Orchestrator <strong>4.0</strong>.0 or later, the security keys must be located in the same folder as<br />
the site list.<br />
frminst.exe /install=agent /siteinfo=<br />
Converting from managed mode to unmanaged mode<br />
Use this task to convert a client currently operating in managed mode to unmanaged mode.<br />
frminst.exe /remove=agent<br />
Changing server
Use this task to change the server with which a client communicates.<br />
The security keys must be located in the same folder as the site list.<br />
frminst.exe /siteinfo=<br />
Allowing users to configure proxy settings<br />
Laptop users of <strong>Windows</strong> can configure proxy settings <strong>for</strong> downloading <strong>McAfee</strong> VirusScan Enterprise updates while in<br />
the field. This requires making changes in the ePolicy Orchestrator console and in the VirusScan console. The ePolicy<br />
Orchestrator changes must be completed be<strong>for</strong>e making the VirusScan changes.<br />
Tasks<br />
Changes in the ePolicy Orchestrator console<br />
Changes in the VirusScan console<br />
Changes in the ePolicy Orchestrator console<br />
You must have ePolicy Orchestrator administrator rights to per<strong>for</strong>m this task.<br />
1. Select Systems | System Tree and select or create the systems where proxy settings are to be allowed.<br />
2. Select Systems | Policy Catalog.<br />
3. In the Product field, select <strong>McAfee</strong> <strong>Agent</strong>.<br />
4. In the Category field, select General.<br />
5. Select a policy (<strong>for</strong> example, “My Default”) and click “Edit.”<br />
6. Click Proxy.<br />
7. Select “Use Internet Explorer settings (<strong>Windows</strong> only),” then select “Allow user to configure proxy settings.” The<br />
new policy is en<strong>for</strong>ced at the next agent-to-server communication interval (ASCI). Alternatively, you can trigger<br />
en<strong>for</strong>cement by invoking an agent wake-up call. See the ePolicy Orchestrator Product Guide <strong>for</strong> instructions.<br />
Changes in the VirusScan console<br />
Any remote user who can access VirusScan Enterprise can per<strong>for</strong>m this task.<br />
1. From the Tools menu of the VirusScan Console, select Edit AutoUpdate Repository List.<br />
2. Select the Proxy settings tab.<br />
3. Select “Use Internet Explorer settings (<strong>Windows</strong> only),” then select “Allow user to configure proxy settings.”<br />
4. Click Configure, then supply the required HTTP or FTP in<strong>for</strong>mation, then click OK.<br />
Finding documentation <strong>for</strong> <strong>McAfee</strong> enterprise products<br />
1. Go to the <strong>McAfee</strong> ServicePortal (mysupport.mcafee.com) and, under Support by Reading, click Product<br />
Documentation.<br />
2. Select a Product.<br />
3. Select a Version.<br />
4. Select a product document.<br />
License attributions<br />
This product includes or may include:<br />
Software developed by the OpenSSL Project <strong>for</strong> use in the OpenSSL Toolkit (http://www.openssl.org/). | Cryptographic<br />
software written by Eric A. Young and software written by Tim J. Hudson | Some software programs that are licensed<br />
(or sublicensed) to the user under the GNU General Public License (GPL) or other similar Free Software licenses which,<br />
among other rights, permit the user to copy, modify and redistribute certain programs, or portions thereof, and have
access to the source code. The GPL requires that <strong>for</strong> any software covered under the GPL, which is distributed to<br />
someone in an executable binary <strong>for</strong>mat, that the source code also be made available to those users. For any such<br />
software covered under the GPL, the source code is made available on this CD. If any Free Software licenses require<br />
that <strong>McAfee</strong> provide rights to use, copy or modify a software program that are broader than the rights granted in this<br />
agreement, then such rights shall take precedence over the rights and restrictions herein. * Software originally written<br />
by Henry Spencer, Copyright 1992, 1993, 1994, 1997 Henry Spencer. | Software originally written by Robert Nordier,<br />
Copyright © 1996-7 Robert Nordier. | Software written by Douglas W. Sauder. | Software developed by the Apache<br />
Software Foundation (http://www.apache.org/). A copy of the license agreement <strong>for</strong> this software can be found at<br />
www.apache.org/licenses/LICENSE-2.0.txt. | International Components <strong>for</strong> Unicode (“ICU”) Copyright © 1995-2002<br />
International Business Machines Corporation and others. | Software developed by CrystalClear Software, Inc.,<br />
Copyright © 2000 CrystalClear Software, Inc. | FEAD® Optimizer® technology, Copyright Netopsystems AG, Berlin,<br />
Germany. | Outside In® Viewer Technology © 1992-2001 Stellent Chicago, Inc. and/or Outside In® HTML Export, ©<br />
2001 Stellent Chicago, Inc. | Software copyrighted by Thai Open Source Software Center Ltd. and Clark Cooper, ©<br />
1998, 1999, 2000. | Software copyrighted by Expat maintainers. | Software copyrighted by The Regents of the<br />
University of Cali<strong>for</strong>nia, © 1996, 1989, 1998-2000. | Software copyrighted by Gunnar Ritter. | Software copyrighted by<br />
Sun Microsystems, Inc., 4150 Network Circle, Santa Clara, Cali<strong>for</strong>nia 95054, U.S.A., © 2003. | Software copyrighted by<br />
Gisle Aas. © 1995-2003. | Software copyrighted by Michael A. Chase, © 1999-2000. * Software copyrighted by Neil<br />
Winton, © 1995-1996. | Software copyrighted by RSA Data Security, Inc., © 1990-1992. | Software copyrighted by<br />
Sean M. Burke, © 1999, 2000. | Software copyrighted by Martijn Koster, © 1995. | Software copyrighted by Brad<br />
Appleton, © 1996-1999. | Software copyrighted by Michael G. Schwern, © 2001. | Software copyrighted by Graham<br />
Barr, © 1998. | Software copyrighted by Larry Wall and Clark Cooper, © 1998-2000. | Software copyrighted by Frodo<br />
Looijaard, © 1997. | Software copyrighted by the Python Software Foundation, Copyright © 2001, 2002, 2003. A copy<br />
of the license agreement <strong>for</strong> this software can be found at www.python.org. | Software copyrighted by Beman Dawes,<br />
© 1994-1999, 2002. | Software written by Andrew Lumsdaine, Lie-Quan Lee, Jeremy G. Siek © 1997-2000 University<br />
of Notre Dame. | Software copyrighted by Simone Bordet & Marco Cravero, © 2002. | Software copyrighted by Stephen<br />
Purcell, © 2001. | Software developed by the Indiana University Extreme! Lab (http://www.extreme.indiana.edu/). |<br />
Software copyrighted by International Business Machines Corporation and others, © 1995-2003. | Software developed<br />
by the University of Cali<strong>for</strong>nia, Berkeley and its contributors. | Software developed by Ralf S. Engelschall<br />
<strong>for</strong> use in the mod_ssl project (http:// www.modssl.org/). | Software copyrighted by Kevlin<br />
Henney, © 2000-2002. | Software copyrighted by Peter Dimov and Multi Media Ltd. © 2001, 2002. | Software<br />
copyrighted by David Abrahams, © 2001, 2002. See http://www.boost.org/libs/bind/bind.html <strong>for</strong> documentation. |<br />
Software copyrighted by Steve Cleary, Beman Dawes, Howard Hinnant & John Maddock, © 2000. | Software<br />
copyrighted by Boost.org, © 1999-2002. | Software copyrighted by Nicolai M. Josuttis, ©1999. | Software copyrighted<br />
by Jeremy Siek, © 1999-2001. | Software copyrighted by Daryle Walker, © 2001. | Software copyrighted by Chuck<br />
Allison and Jeremy Siek, © 2001, 2002. | Software copyrighted by Samuel Krempp, © 2001. See http://www.boost.org<br />
<strong>for</strong> updates, documentation, and revision history. | Software copyrighted by Doug Gregor (gregod@cs.rpi.edu), ©<br />
2001, 2002. | Software copyrighted by Cadenza New Zealand Ltd., © 2000. | Software copyrighted by Jens Maurer, ©<br />
2000, 2001. | Software copyrighted by Jaakko Järvi (jaakko.jarvi@cs.utu.fi), © 1999, 2000. | Software copyrighted by<br />
Ronald Garcia, © 2002. | Software copyrighted by David Abrahams, Jeremy Siek, and Daryle Walker, © 1999-2001. |<br />
Software copyrighted by Stephen Cleary (shammah@voyager.net), © 2000. | Software copyrighted by Housemarque<br />
Oy , © 2001. | Software copyrighted by Paul Moore, © 1999. | Software copyrighted<br />
by Dr. John Maddock, © 1998-2002. | Software copyrighted by Greg Colvin and Beman Dawes, © 1998, 1999. |<br />
Software copyrighted by Peter Dimov, © 2001, 2002. | Software copyrighted by Jeremy Siek and John R. Bandela, ©<br />
2001. | Software copyrighted by Joerg Walter and Mathias Koch, © 2000-2002. | Software copyrighted by Carnegie<br />
Mellon University © 1989, 1991, 1992. | Software copyrighted by Cambridge Broadband Ltd., © 2001-2003. | Software<br />
copyrighted by Sparta, Inc., © 2003-2004. | Software copyrighted by Cisco, Inc and In<strong>for</strong>mation Network Center of<br />
Beijing University of Posts and Telecommunications, © 2004. | Software copyrighted by Simon Josefsson, © 2003. |<br />
Software copyrighted by Thomas Jacob, © 2003-2004. | Software copyrighted by Advanced Software Engineering<br />
Limited, © 2004. | Software copyrighted by Todd C. Miller, © 1998. | Software copyrighted by The Regents of the<br />
University of Cali<strong>for</strong>nia, © 1990, 1993, with code derived from software contributed to Berkeley by Chris Torek.<br />
COPYRIGHT<br />
Copyright © 2009 <strong>McAfee</strong>, Inc. All Rights Reserved.<br />
No part of this publication may be reproduced, transmitted, transcribed, stored in a retrieval system, or translated into<br />
any language in any <strong>for</strong>m or by any means without the written permission of <strong>McAfee</strong>, Inc., or its suppliers or affiliate<br />
companies.<br />
TRADEMARK ATTRIBUTIONS
AVERT, EPO, EPOLICY ORCHESTRATOR, FOUNDSTONE, GROUPSHIELD, INTRUSHIELD, LINUXSHIELD, MAX (MCAFEE<br />
SECURITYALLIANCE EXCHANGE), MCAFEE, NETSHIELD, PORTALSHIELD, PREVENTSYS, SECURITYALLIANCE,<br />
SITEADVISOR, TOTAL PROTECTION, VIRUSSCAN, WEBSHIELD are registered trademarks or trademarks of <strong>McAfee</strong>, Inc.<br />
and/or its affiliates in the US and/or other countries. <strong>McAfee</strong> Red in connection with security is distinctive of <strong>McAfee</strong><br />
brand products. All other registered and unregistered trademarks herein are the sole property of their respective<br />
owners.<br />
LICENSE INFORMATION<br />
License Agreement<br />
NOTICE TO ALL USERS: CAREFULLY READ THE APPROPRIATE LEGAL AGREEMENT CORRESPONDING TO THE LICENSE<br />
YOU PURCHASED, WHICH SETS FORTH THE GENERAL TERMS AND CONDITIONS FOR THE USE OF THE LICENSED<br />
SOFTWARE. IF YOU DO NOT KNOW WHICH TYPE OF LICENSE YOU HAVE ACQUIRED, PLEASE CONSULT THE SALES AND<br />
OTHER RELATED LICENSE GRANT OR PURCHASE ORDER DOCUMENTS THAT ACCOMPANY YOUR SOFTWARE<br />
PACKAGING OR THAT YOU HAVE RECEIVED SEPARATELY AS PART OF THE PURCHASE (AS A BOOKLET, A FILE ON THE<br />
PRODUCT CD, OR A FILE AVAILABLE ON THE WEB-SITE FROM WHICH YOU DOWNLOADED THE SOFTWARE PACKAGE).<br />
IF YOU DO NOT AGREE TO ALL OF THE TERMS SET FORTH IN THE AGREEMENT, DO NOT INSTALL THE SOFTWARE. IF<br />
APPLICABLE, YOU MAY RETURN THE PRODUCT TO MCAFEE OR THE PLACE OF PURCHASE FOR A FULL REFUND.