Cisco CCNA Security Practice Exam Questions - The Cisco ...
Cisco CCNA Security Practice Exam Questions - The Cisco ...
Cisco CCNA Security Practice Exam Questions - The Cisco ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
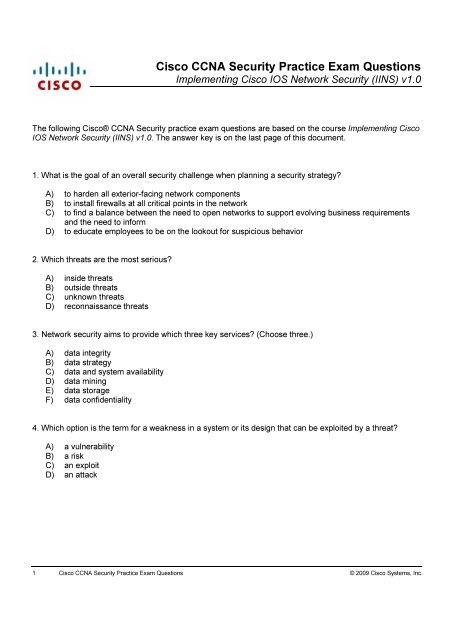
<strong>Cisco</strong> CCN A S e cu r it y P r a ct ice E x a m Q u e st ion s<br />
Implementing <strong>Cisco</strong> IOS Network <strong>Security</strong> (IINS) v1.0<br />
Th e follow ing <strong>Cisco</strong>® <strong>CCNA</strong> S ecurity practice ex am q uestions are based on th e course I m p l e m e n t i n g C i s c o<br />
I O S N e t w o r k S e c u r i t y ( I I N S ) v 1 . 0 . Th e answ er k ey is on th e last pag e of th is d ocum ent.<br />
1. W h at is th e g oal of an ov erall security ch alleng e w h en planning a security strateg y ?<br />
A ) to h ard en all ex terior-facing netw ork com ponents<br />
B ) to install firew alls at all critical points in th e netw ork<br />
C) to find a balance betw een th e need to open netw ork s to support ev olv ing business req uirem ents<br />
and th e need to inform<br />
D ) to ed ucate em ploy ees to be on th e look out for suspicious beh av ior<br />
2. W h ich th reats are th e m ost serious?<br />
A ) insid e th reats<br />
B ) outsid e th reats<br />
C) unk now n th reats<br />
D ) reconnaissance th reats<br />
3. Netw ork security aim s to prov id e w h ich th ree k ey serv ices? ( Ch oose th ree.)<br />
A ) d ata integ rity<br />
B ) d ata strateg y<br />
C) d ata and sy stem av ailability<br />
D ) d ata m ining<br />
E ) d ata storag e<br />
F ) d ata confid entiality<br />
4. W h ich option is th e term for a w eak ness in a sy stem or its d esig n th at can be ex ploited by a th reat?<br />
A ) a v ulnerability<br />
B ) a risk<br />
C) an ex ploit<br />
D ) an attack<br />
1 C i s c o C C N A S e c u r i t y P r a c t i c e E x a m Q u e s t i o n s © 20 0 9 C i s c o S y s t e m s , I n c .
5. W h ich option is th e term for th e lik elih ood th at a particular th reat using a specific attack w ill ex ploit a<br />
particular v ulnerability of a sy stem th at results in an und esirable conseq uence?<br />
A ) a v ulnerability<br />
B ) a risk<br />
C) an ex ploit<br />
D ) an attack<br />
6. W h ich option is th e term for w h at h appens w h en com puter cod e is d ev eloped to tak e ad v antag e of a<br />
v ulnerability ? F or ex am ple, suppose th at a v ulnerability ex ists in a piece of softw are, but nobod y k now s<br />
about th is v ulnerability .<br />
A ) a v ulnerability<br />
B ) a risk<br />
C) an ex ploit<br />
D ) an attack<br />
7. W h at is th e first step y ou sh ould tak e w h en consid ering securing y our netw ork ?<br />
A ) I nstall a firew all.<br />
B ) I nstall an intrusion prev ention sy stem .<br />
C) U pd ate serv ers and user PCs w ith th e latest patch es.<br />
D ) D ev elop a security policy .<br />
8. W h ich option is a k ey principle of th e <strong>Cisco</strong> S elf-D efend ing Netw ork strateg y ?<br />
A ) S ecurity is static and sh ould prev ent m ost k now n attack s on th e netw ork .<br />
B ) Th e self-d efend ing netw ork sh ould be th e k ey point of y our security policy .<br />
C) I nteg rate security th roug h out th e ex isting infrastructure.<br />
D ) U pper m anag em ent is ultim ately responsible for policy im plem entation.<br />
9. W h ich th ree options are areas of router security ? ( Ch oose th ree.)<br />
A ) ph y sical security<br />
B ) access control list security<br />
C) zone-based firew all security<br />
D ) operating sy stem security<br />
E ) router h ard ening<br />
F ) <strong>Cisco</strong> I O S -I PS security<br />
2 C i s c o C C N A S e c u r i t y P r a c t i c e E x a m Q u e s t i o n s © 20 0 9 C i s c o S y s t e m s , I n c .
10 . Y ou h av e sev eral operating g roups in y our enterprise th at req uire d iffering access restrictions to th e<br />
routers to perform th eir j ob roles. Th ese g roups rang e from H elp D esk personnel to ad v anced<br />
troublesh ooters. W h at is one m eth od olog y for controlling access rig h ts to th e routers in th ese situations?<br />
A ) config ure A CL s to control access for th e d ifferent g roups<br />
B ) config ure m ultiple priv ileg e lev el access<br />
C) im plem ent sy slog g ing to m onitor th e activ ities of th e g roups<br />
D ) config ure TA CA CS + to perform scalable auth entication<br />
11. W h ich of th ese options is a G U I tool for perform ing security config urations on <strong>Cisco</strong> routers?<br />
A ) S ecurity A ppliance D ev ice M anag er<br />
B ) <strong>Cisco</strong> CL I Config uration M anag em ent Tool<br />
C) <strong>Cisco</strong> S ecurity D ev ice M anag er<br />
D ) <strong>Cisco</strong> S ecurity M anag er<br />
12. W h en im plem enting netw ork security , w h at is an im portant config uration task th at y ou sh ould perform<br />
to assist in correlating netw ork and security ev ents?<br />
A ) Config ure Netw ork Tim e Protocol.<br />
B ) Config ure sy nch ronized sy slog reporting .<br />
C) Config ure a com m on repository of all netw ork ev ents for ease of m onitoring .<br />
D ) Config ure an autom ated netw ork m onitoring sy stem for ev ent correlation.<br />
13. W h ich of th ese options is a <strong>Cisco</strong> I O S feature th at lets y ou m ore easily config ure security features on<br />
y our router?<br />
A ) <strong>Cisco</strong> S elf-D efend ing Netw ork<br />
B ) im plem enting A A A com m and auth orization<br />
C) th e a u t o s e c u r e CL I com m and<br />
D ) perform ing a security aud it v ia S D M<br />
14. W h ich th ree of th ese options are som e of th e best practices w h en y ou im plem ent an effectiv e firew all<br />
security policy ? ( Ch oose th ree.)<br />
A ) Position firew alls at strateg ic insid e locations to h elp m itig ate insid e nontech nical attack s.<br />
B ) Config ure log g ing to capture all ev ents for forensic purposes.<br />
C) U se firew alls as a prim ary security d efense; oth er security m easures and d ev ices sh ould be<br />
im plem ented to enh ance y our netw ork security .<br />
D ) Position firew alls at k ey security bound aries.<br />
E ) D eny all traffic by d efault and perm it only necessary serv ices.<br />
3 C i s c o C C N A S e c u r i t y P r a c t i c e E x a m Q u e s t i o n s © 20 0 9 C i s c o S y s t e m s , I n c .
15. W h ich statem ent is true w h en config uring access control lists ( A CL s) on a <strong>Cisco</strong> router?<br />
A ) A CL s filter all traffic th roug h and sourced from th e router.<br />
B ) A pply th e A CL to th e interface prior to config uring access control entries to ensure th at controls are<br />
applied im m ed iately upon config uration.<br />
C) A n “ im plicit d eny ” is applied to th e start of th e A CL entry by d efault.<br />
D ) O nly one A CL per protocol, per d irection, and per interface is allow ed .<br />
16. W h ich option correctly d efines asy m m etric encry ption?<br />
A ) uses th e sam e k ey s to encry pt and d ecry pt d ata<br />
B ) uses M D 5 h ash ing alg orith m s for d ig ital sig nag e encry ption<br />
C) uses d ifferent k ey s to encry pt and d ecry pt d ata<br />
D ) uses S H A -1 h ash ing alg orith m s for d ig ital sig nag e encry ption<br />
17. W h ich option is a d esirable feature of using sy m m etric encry ption alg orith m s?<br />
A ) Th ey are often used for w ire-speed encry ption in d ata netw ork s.<br />
B ) Th ey are based on com plex m ath em atical operations and can easily be accelerated by h ard w are.<br />
C) Th ey offer sim ple k ey m anag em ent properties.<br />
D ) Th ey are best used for one-tim e encry ption need s.<br />
18. W h ich option is true of using cry ptog raph ic h ash es?<br />
A ) Th ey are easily rev ersed to d eciph er th e m essag e contex t.<br />
B ) Th ey conv ert arbitrary d ata into a fix ed -leng th d ig est.<br />
C) Th ey are based on a tw o-w ay m ath em atical function.<br />
D ) Th ey are used for encry pting bulk d ata com m unications.<br />
19. W h ich option is true of intrusion prev ention sy stem s?<br />
A ) Th ey operate in prom iscuous m od e.<br />
B ) Th ey operate in inline m od e.<br />
C) Th ey h av e no potential im pact on th e d ata seg m ent being m onitored .<br />
D ) Th ey are m ore v ulnerable to ev asion tech niq ues th an I D S .<br />
20 . W h ich statem ent is true w h en using zone-based firew alls on a <strong>Cisco</strong> router?<br />
A ) Policies are applied to traffic m ov ing betw een zones, not betw een interfaces.<br />
B ) Th e firew alls can be config ured sim ultaneously on th e sam e interface as classic CB A C using th e i p<br />
i n s p e c t CL I com m and .<br />
C) I nterface A CL s are applied before zone-based policy firew alls w h en th ey are applied outbound .<br />
D ) W h en config ured w ith th e “ PA S S ” action, stateful inspection is applied to all traffic passing betw een<br />
th e config ured zones.<br />
4 C i s c o C C N A S e c u r i t y P r a c t i c e E x a m Q u e s t i o n s © 20 0 9 C i s c o S y s t e m s , I n c .
C C N A S e c u r i t y P r a c t i c e Q u e s t i o n s A n s w e r K e y<br />
1. C<br />
2. A<br />
3. A , C, F<br />
4. A<br />
5. B<br />
6. C<br />
7. D<br />
8. C<br />
9. A , D , E<br />
10 . B<br />
11. C<br />
12. A<br />
13. C<br />
14. C, D , E<br />
15. D<br />
16. C<br />
17. A<br />
18. B<br />
19. B<br />
20 . A<br />
5 C i s c o C C N A S e c u r i t y P r a c t i c e E x a m Q u e s t i o n s © 20 0 9 C i s c o S y s t e m s , I n c .