Internet Security and Risks
Internet Security and Risks
Internet Security and Risks
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
| ACE |<br />
Date of Presentation: 24 October 2012<br />
<strong>Internet</strong> <strong>Security</strong> <strong>and</strong> <strong>Risks</strong><br />
Executive Summary<br />
Introduction to modern issues related to the internet<br />
<strong>Risks</strong> to Consumers <strong>and</strong> management of such risks<br />
<strong>Risks</strong> to Businesses <strong>and</strong> management of such risks<br />
1.0 Introduction<br />
Contributors:<br />
Isaiah Chia<br />
ZICHIA1@e.ntu.edu.sg<br />
Ow-Yang Zhi Yan<br />
Z090086@e.ntu.edu.sg<br />
Cyberspace – the internet <strong>and</strong> other computer-based networks – is becoming one of the most<br />
important infrastructures that characterize many modern societies. Among the network of<br />
cyberspace are systems that control <strong>and</strong> manage infrastructures such as energy delivery, emergency<br />
services, banking <strong>and</strong> finance, military systems <strong>and</strong> many other applications. Regions’ economic <strong>and</strong><br />
social stability may also depend on these networks.<br />
Dependencies on networks for communication <strong>and</strong> business operations continue to grow along with<br />
the growth of cyberspace. Today, the <strong>Internet</strong> in particular, which has grown without any planning<br />
or central organization, is a vast network of networks. Destructive acts using computer networks<br />
have cost billions of dollars <strong>and</strong> continue to threaten the resources of network-connected critical<br />
infrastructure.<br />
In this research paper, we intend to first identify the various threats to individuals <strong>and</strong> businesses<br />
alike linked to increasing proliferation of internet usage, possible impact <strong>and</strong> finally propose<br />
alternatives to mitigate these risks.<br />
2.0 Consumers’ Risk<br />
The number of internet users has been increasing across time as the global economy is increasingly<br />
reliant on the internet to communicate <strong>and</strong> relay information across distances. We often sign up for<br />
online services with our email addresses without much thought, proceeding to key in our desired<br />
username <strong>and</strong> password methodically, only to be greeted by a welcome message upon the<br />
successful creation of the account. The sign up process has become an expected routine for new<br />
users for most online services that we often overlook the possible risks that are associated with it. In<br />
spite of the numerous phishing advisories that suggest that we ascertain if the information is<br />
transmitted over a hypertext transfer protocol secure (https) connection, the use of https merely<br />
prevents a third party from intercepting the transmitted information. As important as a secure<br />
connection may be, it overlooks the password storage policies of the website you are creating an<br />
account on, which is an additional risk factor most users fail to recognize.<br />
NTU – RISK MANAGEMENT SOCIETY – RESEARCH DEPARTMENT Page 1 of 4
| ACE |<br />
Websites employ an array of methods to store your account password in their database to facilitate<br />
your log in to the website. The straight-forward method would be to store passwords in an<br />
unencrypted plaintext format in the database, <strong>and</strong> this puts your associated email account at a risk if<br />
you were to use the same password for both log ins. Should the database of the website be<br />
compromised due to a security vulnerability, the attacker will be able to access your email account<br />
with the password you signed up with on the website, compromising all other accounts which are<br />
tagged to the same email address, as a “forget-password attack” could be employed to reset your<br />
password for your other accounts having access to your email account. As such, since most websites<br />
do not reveal the method of storing the passwords in the database, it is prudent to use a different<br />
password for your email account <strong>and</strong> accounts for your other web services. This will protect your<br />
email account should the website ever be compromised.<br />
As a recommendation, we highly recommend users to not only change their password periodically,<br />
but to have a combination of passwords to be used for different services. Email passwords <strong>and</strong> web<br />
services passwords should ideally be different, <strong>and</strong> login passwords into your computer should be<br />
different from email accounts <strong>and</strong> other web services. This will impede the ease at which all your<br />
accounts will be compromised simultaneously should any one of your password be leaked in the<br />
occurrence of an unfortunate event.<br />
3.0 Business <strong>Security</strong> <strong>Risks</strong><br />
Businesses are also not spared from internet risks. A key trend coloring the world of business is how<br />
computers have transformed into critical business systems. Information gathering was indeed made<br />
easier with availability of information in the internet. Many solutions can be sourced with a click of<br />
the mouse. Over the past few years, there were many instances of high-profile data breach cases<br />
involving businesses. Many have the perception that only large corporations are targeted by hackers<br />
<strong>and</strong> information thieves. However, the reality is that hackers are increasingly targeting small<br />
businesses because of the assumption that many among the latter do not have advanced know-how<br />
or resources to protect their data against sophisticated internet attacks. In this paper, we will discuss<br />
3 possible threats businesses may face on the internet.<br />
3.1 Malicious Codes<br />
Malicious codes are encoded in any part of a software system or script that is intended to cause<br />
undesired effects, security breaches or damage to a system. Malicious code describes a broad<br />
category of system security terms that includes attack scripts, viruses, worms, Trojan horses,<br />
backdoors, <strong>and</strong> malicious active content, <strong>and</strong> they tend to exploit internet-based services such as<br />
email. These threats have to be highlighted as we use these technologies for day-to-day operations.<br />
The threats of these malicious codes can be colossal; imagine the scenario, for example, if<br />
companies the size of Microsoft had to turn off their email systems to survive a malicious code<br />
attack.<br />
Fortunately, it is possible to reduce the impact <strong>and</strong> mitigate the risk of malicious code by using tried<br />
<strong>and</strong> tested business practices. They are:<br />
• Educate users about the computer virus threat<br />
NTU – RISK MANAGEMENT SOCIETY – RESEARCH DEPARTMENT Page 2 of 4
| ACE |<br />
• Install reputable anti-virus software on workstations, servers <strong>and</strong> internet gateways<br />
• Train users on how to use their anti-virus software properly<br />
• Train system administrators to manage anti-virus software<br />
• Making sure the anti-virus policy is up to date<br />
3.2 Spear Phishing<br />
Spear phishing is a type of phishing attack that focuses its attention on a single user or department<br />
within an organization, <strong>and</strong> where the attacker impersonates someone within the organization in a<br />
position of trust <strong>and</strong> requesting information such as login IDs <strong>and</strong> passwords. Another type of attack<br />
involves asking users to click on a link, which deploys spyware that can steal data. Once hackers get<br />
this data, they can gain entry into secured networks.<br />
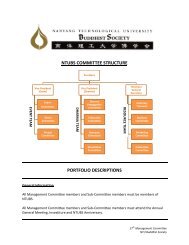
According to Cisco, spear phishing requires more work from cybercriminal – forging corporate logos,<br />
snaring employees address etc. But their targets are more likely to trust <strong>and</strong> fall victim to the<br />
fraudulent emails, <strong>and</strong> payoffs are bigger when scams succeed. Figure 1 below quantifies the likely<br />
payoff for a normal phishing attack vis-à-vis that of a targeted spear phishing attack.<br />
3.3 Unsecured Wireless <strong>Internet</strong> Networks<br />
Figure 1: Payoff comparison<br />
Businesses are quickly adopting <strong>and</strong> implementing wireless <strong>Internet</strong> networks. While having wireless<br />
networks provide businesses an opportunity to streamline their network using minimal physical<br />
infrastructure, there are security risks that businesses need to address. Hackers <strong>and</strong> fraudsters can<br />
gain entry to businesses’ computers through an open wireless <strong>Internet</strong> network, <strong>and</strong> as a result,<br />
NTU – RISK MANAGEMENT SOCIETY – RESEARCH DEPARTMENT Page 3 of 4
| ACE |<br />
breach data security. This risk is amplified by the fact that many small businesses may not use strong<br />
wireless security to protect their systems.<br />
Knowing the risks <strong>and</strong> possible implications associated to it, businesses can mitigate these<br />
unnecessary security risks via two methods.<br />
Firstly, the default password should be changed. Most network devices, including wireless access<br />
points, are pre-configured with default administrator passwords to simplify setup. These default<br />
passwords are easily found online, so they provide little protection. Changing default passwords<br />
makes it harder for attackers to take control of the device.<br />
Secondly, businesses should encrypt the wireless network. WEP (Wired Equivalent Privacy) <strong>and</strong> WPA<br />
(Wi-Fi Protected Access) both encrypt information on wireless devices. However, WEP has a number<br />
of security issues that make it less effective than WPA, so it will be advisable to use gears that<br />
support encryption via WPA. Encrypting the data would prevent anyone who might be able to<br />
monitor your network wireless traffic from viewing your data.<br />
References<br />
Cisco (June 2011) Email attack: Now it’s personal. Retrieved from:<br />
http://www.cisco.com/en/US/prod/collateral/vpndevc/ps10128/ps10339/ps10354/targeted_attacks.pdf<br />
Disclaimer<br />
The information set forth herein has been obtained or derived from sources generally available to the public <strong>and</strong> believed<br />
by the author(s) to be reliable, but the author(s) does not make any representation or warranty, express or implied, as to<br />
its accuracy or completeness. The information is not intended to be used as the basis of any investment decisions by any<br />
person or entity. This information does not constitute investment advice, nor is it an offer or a solicitation of an offer to<br />
buy or sell any security. This report should not be considered to be a recommendation by any individual affiliated with NTU<br />
RMS Research Department.<br />
NTU – RISK MANAGEMENT SOCIETY – RESEARCH DEPARTMENT Page 4 of 4