Resume - Njit - New Jersey Institute of Technology
Resume - Njit - New Jersey Institute of Technology
Resume - Njit - New Jersey Institute of Technology
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
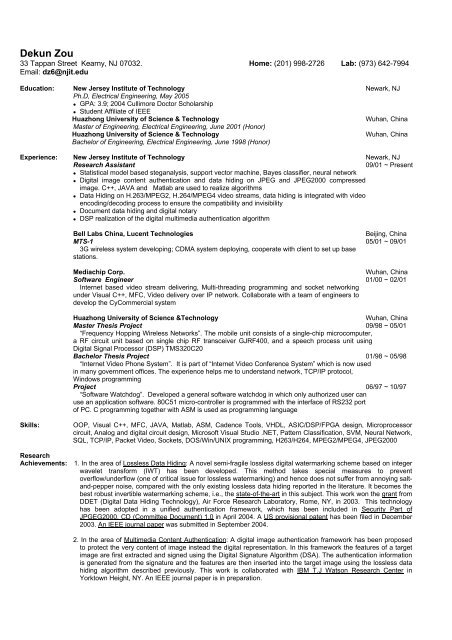
Dekun Zou<br />
33 Tappan Street Kearny, NJ 07032. Home: (201) 998-2726 Lab: (973) 642-7994<br />
Email: dz6@njit.edu<br />
Education: <strong>New</strong> <strong>Jersey</strong> <strong>Institute</strong> <strong>of</strong> <strong>Technology</strong> <strong>New</strong>ark, NJ<br />
Ph.D, Electrical Engineering, May 2005<br />
GPA: 3.9; 2004 Cullimore Doctor Scholarship<br />
Student Affiliate <strong>of</strong> IEEE<br />
Huazhong University <strong>of</strong> Science & <strong>Technology</strong> Wuhan, China<br />
Master <strong>of</strong> Engineering, Electrical Engineering, June 2001 (Honor)<br />
Huazhong University <strong>of</strong> Science & <strong>Technology</strong> Wuhan, China<br />
Bachelor <strong>of</strong> Engineering, Electrical Engineering, June 1998 (Honor)<br />
Experience: <strong>New</strong> <strong>Jersey</strong> <strong>Institute</strong> <strong>of</strong> <strong>Technology</strong> <strong>New</strong>ark, NJ<br />
Research Assistant 09/01 ~ Present<br />
Statistical model based steganalysis, support vector machine, Bayes classifier, neural network<br />
Digital image content authentication and data hiding on JPEG and JPEG2000 compressed<br />
image. C++, JAVA and Matlab are used to realize algorithms<br />
Data Hiding on H.263/MPEG2, H.264/MPEG4 video streams, data hiding is integrated with video<br />
encoding/decoding process to ensure the compatibility and invisibility<br />
Document data hiding and digital notary<br />
DSP realization <strong>of</strong> the digital multimedia authentication algorithm<br />
Bell Labs China, Lucent Technologies Beijing, China<br />
MTS-1 05/01 ~ 09/01<br />
3G wireless system developing; CDMA system deploying, cooperate with client to set up base<br />
stations.<br />
Mediachip Corp. Wuhan, China<br />
S<strong>of</strong>tware Engineer 01/00 ~ 02/01<br />
Internet based video stream delivering, Multi-threading programming and socket networking<br />
under Visual C++, MFC, Video delivery over IP network. Collaborate with a team <strong>of</strong> engineers to<br />
develop the CyCommercial system<br />
Huazhong University <strong>of</strong> Science &<strong>Technology</strong> Wuhan, China<br />
Master Thesis Project 09/98 ~ 05/01<br />
“Frequency Hopping Wireless Networks”. The mobile unit consists <strong>of</strong> a single-chip microcomputer,<br />
a RF circuit unit based on single chip RF transceiver GJRF400, and a speech process unit using<br />
Digital Signal Processor (DSP) TMS320C20<br />
Bachelor Thesis Project 01/98 ~ 05/98<br />
“Internet Video Phone System”. It is part <strong>of</strong> “Internet Video Conference System” which is now used<br />
in many government <strong>of</strong>fices. The experience helps me to understand network, TCP/IP protocol,<br />
Windows programming<br />
Project 06/97 ~ 10/97<br />
“S<strong>of</strong>tware Watchdog”. Developed a general s<strong>of</strong>tware watchdog in which only authorized user can<br />
use an application s<strong>of</strong>tware. 80C51 micro-controller is programmed with the interface <strong>of</strong> RS232 port<br />
<strong>of</strong> PC. C programming together with ASM is used as programming language<br />
Skills: OOP, Visual C++, MFC, JAVA, Matlab, ASM, Cadence Tools, VHDL, ASIC/DSP/FPGA design, Microprocessor<br />
circuit, Analog and digital circuit design, Micros<strong>of</strong>t Visual Studio .NET, Pattern Classification, SVM, Neural Network,<br />
SQL, TCP/IP, Packet Video, Sockets, DOS/Win/UNIX programming, H263/H264, MPEG2/MPEG4, JPEG2000<br />
Research<br />
Achievements: 1. In the area <strong>of</strong> Lossless Data Hiding: A novel semi-fragile lossless digital watermarking scheme based on integer<br />
wavelet transform (IWT) has been developed. This method takes special measures to prevent<br />
overflow/underflow (one <strong>of</strong> critical issue for lossless watermarking) and hence does not suffer from annoying saltand-pepper<br />
noise, compared with the only existing lossless data hiding reported in the literature. It becomes the<br />
best robust invertible watermarking scheme, i.e., the state-<strong>of</strong>-the-art in this subject. This work won the grant from<br />
DDET (Digital Data Hiding <strong>Technology</strong>), Air Force Research Laboratory, Rome, NY, in 2003. This technology<br />
has been adopted in a unified authentication framework, which has been included in Security Part <strong>of</strong><br />
JPGEG2000, CD (Committee Document) 1.0 in April 2004. A US provisional patent has been filed in December<br />
2003. An IEEE journal paper was submitted in September 2004.<br />
2. In the area <strong>of</strong> Multimedia Content Authentication: A digital image authentication framework has been proposed<br />
to protect the very content <strong>of</strong> image instead the digital representation. In this framework the features <strong>of</strong> a target<br />
image are first extracted and signed using the Digital Signature Algorithm (DSA). The authentication information<br />
is generated from the signature and the features are then inserted into the target image using the lossless data<br />
hiding algorithm described previously. This work is collaborated with IBM T.J Watson Research Center in<br />
Yorktown Height, NY. An IEEE journal paper is in preparation.
Patents:<br />
Publications:<br />
3. In the area <strong>of</strong> Text Document Data Hiding: A data hiding scheme aiming at formatted text documents has been<br />
invented. It is a blind algorithm, meaning the original document is not needed for hidden data extraction. The<br />
performance on robustness is superior over all existing technologies. The stego-document can be subjected to<br />
printing, copying and scanning. Specifically, the hidden data can still be correctly extracted after the document<br />
has experienced one printing, followed by 10 times <strong>of</strong> copying, and one scanning. This is the best blind robust<br />
document data hiding algorithm compared with all the existing algorithms. This invention has been disclosed to<br />
NJIT in July 2004. A US provisional patent has been filed in December 2004. A research proposal has been<br />
submitted to DDET, Air Force Research Laboratory in May 2004. This technology opens possibility to Digital<br />
Notarization.<br />
4. In the area <strong>of</strong> Steganalysis: Steganalysis is to detect the hidden message, and is urgently requested by military<br />
and cyber security. So far, the area is very young. The most hard stegnography methods to be detected are the<br />
so-called spread-spectrum based algorithms. There exists no previous steganalysis methods which can handle<br />
this tough case. As a major team member in the research group, I have made significant contribution to this area.<br />
Our recent investigation indicates that our newly developed framework can detect stego-media created by using<br />
the typical spread-spectrum scheme with a successful rate close to 80%. This work in this regard leads to a<br />
proposal submitted to DDET Air Force Research Laboratory in September. Patents and IEEE journal papers are<br />
expected.<br />
1. Dekun Zou, Y.Q. Shi, Z. Ni: Method and Apparatus for Lossless Image Data Hiding that does Not Generate Saltpepper<br />
Noise and Is Robust against Compression, US Provisional Patent filed in December 2003.<br />
2. Dekun Zou, Y.Q. Shi: Formatted Text Document Data Hiding Using Inter-word Space Modulation Robust to<br />
Scanning Copying and Printing, US Provisional Patent filed in December 2004.<br />
1. Dekun Zou, Tianlin Dong: On the Application <strong>of</strong> Single Chip RF Transceiver GJRF400, Journal <strong>of</strong> Mobile<br />
Communications, China, March 2001<br />
2. Dekun Zou, Chai Wah Wu, Yun Q. Shi: A Content-based Image authentication system with lossless data hiding,<br />
IEEE International Conference on Multimedia and Expo (ICME), vol.2, pp.213-216, July 2003<br />
3. C. Manikopoulos, Y.Q. Shi, S. Song, Z. Zhang, Z. Ni; Dekun Zou; Detection <strong>of</strong> block DCT-based steganography in<br />
gray-scale images IEEE International Workshop on Multimedia Signal Processing (MMSP), pp.355-358, Dec. 2002<br />
4. Dekun Zou, Yun Q. Shi Z. Ni: A Semi-fragile Lossless Digital Watermarking Scheme Based on Integer Wavelet<br />
Transform, IEEE International Workshop on Multimedia Signal Processing(MMSP), pp.195-198, Sept. 2004<br />
5. Yun Q. Shi, Z. Ni, Dekun Zou, Changyin Liang and Guorong Xuan: Lossless data hiding: Fundamentals,<br />
Algorithms and Applications, International Symposium on Circuit and System (ISCAS), vol.2, pp.33-36, May 2004<br />
6. G. Xuan, J. Zheng, C. Yang , Yun Q. Shi, Dekun Zou: A Secure Internet-Based Personal Identity Verification<br />
System Using Lossless Watermarking and Fingerprint Recognition, International Workshop on Digital<br />
Watermarking, Oct. 2004<br />
7. Dekun Zou, Y.Q. Shi: Formatted Text Document Data Hiding Robust to Scanning Copying and Printing, IEEE<br />
ISCAS 05<br />
8. Yun Q. Shi, G. Xuan, Dekun Zou: Effective Steganalysis Based on Statistical Moments <strong>of</strong> Wavelet Characteristic<br />
Function, IEEE ITCC05<br />
9. Dekun Zou, Y.Q. Shi, Z. Ni: An Invertible Data Hiding Scheme Robust to Lossy Compression, Submitted to IEEE<br />
Transaction on Multimedia for review<br />
10. Yun Q. Shi, G. Xuan, Dekun Zou: Image Steganalysis Based on Moments <strong>of</strong> Wavelet Characteristic Function,<br />
Submitted to IEE Electronics Letters for review<br />
Personality: Creative, hardworking, easy going, cooperative, teamwork, devoted when working or playing