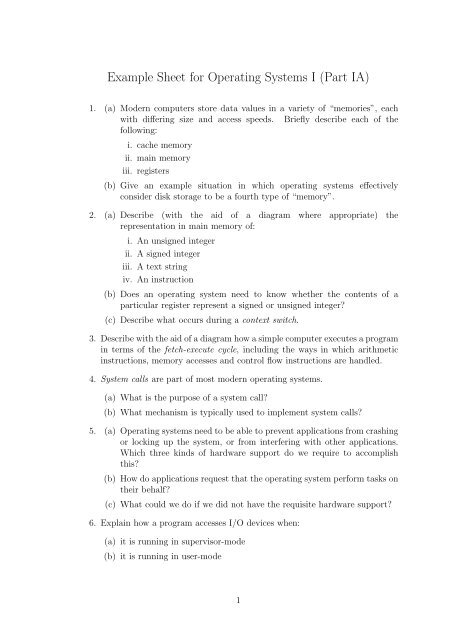
Example Sheet for Operating Systems I (Part IA)
Example Sheet for Operating Systems I (Part IA)
Example Sheet for Operating Systems I (Part IA)
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>Example</strong> <strong>Sheet</strong> <strong>for</strong> <strong>Operating</strong> <strong>Systems</strong> I (<strong>Part</strong> <strong>IA</strong>)<br />
1. (a) Modern computers store data values in a variety of “memories”, each<br />
with differing size and access speeds. Briefly describe each of the<br />
following:<br />
i. cache memory<br />
ii. main memory<br />
iii. registers<br />
(b) Give an example situation in which operating systems effectively<br />
consider disk storage to be a fourth type of “memory”.<br />
2. (a) Describe (with the aid of a diagram where appropriate) the<br />
representation in main memory of:<br />
i. An unsigned integer<br />
ii. A signed integer<br />
iii. A text string<br />
iv. An instruction<br />
(b) Does an operating system need to know whether the contents of a<br />
particular register represent a signed or unsigned integer?<br />
(c) Describe what occurs during a context switch.<br />
3. Describe with the aid of a diagram how a simple computer executes a program<br />
in terms of the fetch-execute cycle, including the ways in which arithmetic<br />
instructions, memory accesses and control flow instructions are handled.<br />
4. System calls are part of most modern operating systems.<br />
(a) What is the purpose of a system call?<br />
(b) What mechanism is typically used to implement system calls?<br />
5. (a) <strong>Operating</strong> systems need to be able to prevent applications from crashing<br />
or locking up the system, or from interfering with other applications.<br />
Which three kinds of hardware support do we require to accomplish<br />
this?<br />
(b) How do applications request that the operating system per<strong>for</strong>m tasks on<br />
their behalf?<br />
(c) What could we do if we did not have the requisite hardware support?<br />
6. Explain how a program accesses I/O devices when:<br />
(a) it is running in supervisor-mode<br />
(b) it is running in user-mode<br />
1
7. From the point of view of the device driver, data may be read from an<br />
I/O device using polling, inerrupt-driven programmed I/O, or direct memory<br />
access (DMA). Briefly explain each of these terms, and in each case outline<br />
using pseudo-code (or a flow chart) the flow of control in the device driver<br />
when reading data from the device.<br />
8. From the point of view of the application programmer, data may be read<br />
from a device in a blocking, non-blocking or asynchronous fashion. Using<br />
a keyboard as an example device, describe the expected behaviour in each<br />
case.<br />
9. Process scheduling can be preemptive or non-preemptive. Compare and<br />
contrast these approaches, commenting on issues of simplicity, fairness,<br />
per<strong>for</strong>mance and required hardware support.<br />
10. (a) Describe how the CPU is allocated to processes if static priority<br />
scheduling is used. Be sure to consider the various possibilities available<br />
in the case of a tie.<br />
(b) “All scheduling algorithms are essentially priority scheduling<br />
algorithms.”<br />
Discuss this statement with reference to the first-come first-served<br />
(FCFS), shortest job first (SJF), shortest remaining time first (SRTF)<br />
and round-robin (RR) scheduling algorithms.<br />
(c) What is the major problem with static priority scheduling and how may<br />
it be addressed?<br />
(d) Why do many CPU scheduling algorithms try to favour I/O intensive<br />
jobs?<br />
11. An operating system uses a single queue round-robin scheduling algorithm<br />
<strong>for</strong> all processes. You are told that a quantum of three time units is used.<br />
(a) What can you infer about the scheduling algorithm?<br />
(b) Why is this sort of algorithm suitable <strong>for</strong> a multi-user operating system?<br />
(c) The following processes are to be scheduled by the operating system.<br />
Process Creation Time Required Computing Time<br />
P 1 0 9<br />
P 2 1 4<br />
P 3 7 2<br />
None of the processes ever blocks. New processes are added to the tail of<br />
the queue and do not disrupt the currently running process. Assuming<br />
context switches are instantaneous, determine the response time <strong>for</strong> each<br />
process.<br />
(d) Give one advantage and one disadvantage of using a small quantum.<br />
2
12. (a) Describe with the aid of a diagram the life-cycle of a process. You should<br />
describe each of the states that it can be in, and the reasons it moves<br />
between these states.<br />
(b) What in<strong>for</strong>mation does the operating system keep in the process control<br />
block?<br />
(c) What in<strong>for</strong>mation do the shortest job first (SJF) and shortest remaining<br />
time first (SRTF) algorithms require about each job or process? How<br />
can this in<strong>for</strong>mation be obtained?<br />
(d) Give one advantage and one disadvantage of non-preemptive scheduling.<br />
(e) What steps does the operating system take when an interrupt occurs?<br />
Consider both the programmed I/O and DMA cases, and the interaction<br />
with the CPU scheduler.<br />
(f) What problems could occur if a system experienced a very high interrupt<br />
load? What if the device[s] in question were DMA-capable?<br />
13. (a) What is the address binding problem?<br />
(b) The address binding problem can be solved at compile time, load time<br />
or run time. For each case, explain what <strong>for</strong>m the solution takes, and<br />
give one advantage and one disadvantage.<br />
14. For each of the following, indicate if the statement is true or false, and explain<br />
why:<br />
(a) Preemptive schedulers require hardware support.<br />
(b) A context switch can be implemented by a flip-flop stored in the<br />
translation lookaside buffer (TLB).<br />
(c) Non-blocking I/O is possible even when using a block device.<br />
(d) Shortest job first (SJF) is an optimal scheduling algorithm.<br />
(e) Round-robin scheduling can suffer from the so-called ‘convoy effect’.<br />
(f) A paged virtual memory is smaller than a segmented one.<br />
(g) Direct memory access (DMA) makes devices go faster.<br />
(h) System calls are an optional extra in modern operating systems.<br />
(i) In Unix, hard-links cannot span mount points.<br />
(j) The Unix shell supports redirection to the buffer cache.<br />
15. Most operating systems provide each process with its own address space by<br />
providing a level of indirection between virtual and physical addresses.<br />
(a) Give three benefits of this approach.<br />
(b) Are there any drawbacks? Justify your answer.<br />
(c) A processor may support a paged or a segmented virtual address space.<br />
3
i. Sketch the <strong>for</strong>mat of a virtual address in each of these cases, and<br />
explain using a diagram how this address is translated to a physical<br />
one.<br />
ii. In which case is physical memory allocation easier? Justify your<br />
answer.<br />
iii. Give two benefits of the segmented approach.<br />
16. File systems comprise a directory service and a storage service.<br />
(a) What are the two main functions of the directory service?<br />
(b) What is a directory hierarchy? Explain your answer with the aid of a<br />
diagram.<br />
(c) What in<strong>for</strong>mation is held in file meta-data?<br />
(d) What is a hard link? Does file system support <strong>for</strong> hard links place any<br />
restrictions on the location of file meta-data?<br />
(e) What is a soft (or symbolic) link? Does file system support <strong>for</strong> soft links<br />
place any restrictions on the location of file meta-data?<br />
17. (a) In the context of memory management, under which circumstances do<br />
external and internal fragmentation occur? How can each be handled?<br />
(b) What is the purpose of a page table? What sort of in<strong>for</strong>mation might it<br />
contain? How does it interact with a TLB?<br />
(c) Describe with the aid of a diagram a two-level page table. Explain the<br />
motivation behind the structure and how it operates.<br />
18. Describe the basic access control scheme used in the Unix filing system. How<br />
does UNIX support more advanced access control policies?<br />
19. Briefly compare and contrast the notion of process in the Windows XP and<br />
Unix operating systems. How is scheduling carried out in each case?<br />
20. (a) Describe with the aid of a diagram the on-disk layout of a Unix V7<br />
filesystem. Include in your description the role of the superblock, and<br />
the way in which free inodes and data blocks are managed.<br />
(b) Describe with the aid of a diagram a Unix V7 inode.<br />
(c) Estimate the largest file size supported by a Unix V7 filesystem.<br />
(d) Suggest one reliability enhancement and two per<strong>for</strong>mance enhancements<br />
which could be made to the Unix V7 filesystem.<br />
21. (a) Describe with the aid of a diagram the structure of the Windows XP<br />
operating system. Sketch the functions of each component, and clearly<br />
indicate which parts execute in kernel mode and which in user mode.<br />
(b) Compare and contrast the object namespace in Windows XP with the<br />
directory namespace of Unix.<br />
(c) Compare and contrast blocking, non-blocking and asynchronous I/O.<br />
4
(d) Give four techniques which can improve I/O per<strong>for</strong>mance.<br />
22. (a) Describe, with the aid of diagrams where appropriate, how Unix<br />
implements and manages:<br />
i. a hierarchical name space <strong>for</strong> files<br />
ii. allocation of storage on disk<br />
iii. file-system and file meta-data<br />
iv. pipes<br />
(b) A Unix system administrator decides to make a ‘versioned’ file-system<br />
in which there are a number of directories called /root-dd-mm-yyyy,<br />
each of which holds a copy of the file-system on day dd, month mm<br />
and year yyyy. The idea is that at any particular time only the<br />
most recent snapshow will be used as the ‘real’ filesystem root, but<br />
that all previous snapshots will be available by explicitly accessing the<br />
directory in question. In this way the system administrator hopes to<br />
allow resilience to mistaken edits or unintentional deletions by users, or<br />
to hardware problems such as a disk head crash.<br />
To implement this, the system administrator arranges <strong>for</strong> a program<br />
to run every morning at 01:00 which recursively ‘copies’ the current<br />
snapshot to the new one. However to save disk space, hardlinks are used<br />
in place of actual copies. Once the ‘copy’ is complete, the new snapshot<br />
is used as the new root.<br />
To what extent will this scheme provide the functionality the system<br />
administrator hopes <strong>for</strong>? What advantages and disadvantages does it<br />
have?<br />
23. Describe how CPU scheduling algorithms favour I/O intensive jobs in the (a)<br />
Unix and (b) Windows NT operating systems.<br />
24. Describe with the aid of a diagram a Unix inode. You should explain the<br />
motivation behind indirect blocks, and how they are used when accessing a<br />
file.<br />
25. Describe the operation of the Unix shell with reference to the process<br />
management system calls it makes use of. You might like to use pseudocode<br />
or a diagram to aid with your description.<br />
5