Program for HICSS â 41
Program for HICSS â 41
Program for HICSS â 41
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
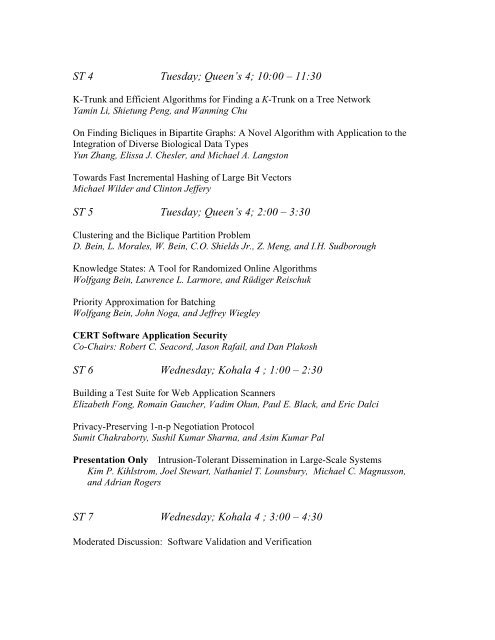
ST 4 Tuesday; Queen’s 4; 10:00 – 11:30<br />
K-Trunk and Efficient Algorithms <strong>for</strong> Finding a K-Trunk on a Tree Network<br />
Yamin Li, Shietung Peng, and Wanming Chu<br />
On Finding Bicliques in Bipartite Graphs: A Novel Algorithm with Application to the<br />
Integration of Diverse Biological Data Types<br />
Yun Zhang, Elissa J. Chesler, and Michael A. Langston<br />
Towards Fast Incremental Hashing of Large Bit Vectors<br />
Michael Wilder and Clinton Jeffery<br />
ST 5 Tuesday; Queen’s 4; 2:00 – 3:30<br />
Clustering and the Biclique Partition Problem<br />
D. Bein, L. Morales, W. Bein, C.O. Shields Jr., Z. Meng, and I.H. Sudborough<br />
Knowledge States: A Tool <strong>for</strong> Randomized Online Algorithms<br />
Wolfgang Bein, Lawrence L. Larmore, and Rüdiger Reischuk<br />
Priority Approximation <strong>for</strong> Batching<br />
Wolfgang Bein, John Noga, and Jeffrey Wiegley<br />
CERT Software Application Security<br />
Co-Chairs: Robert C. Seacord, Jason Rafail, and Dan Plakosh<br />
ST 6 Wednesday; Kohala 4 ; 1:00 – 2:30<br />
Building a Test Suite <strong>for</strong> Web Application Scanners<br />
Elizabeth Fong, Romain Gaucher, Vadim Okun, Paul E. Black, and Eric Dalci<br />
Privacy-Preserving 1-n-p Negotiation Protocol<br />
Sumit Chakraborty, Sushil Kumar Sharma, and Asim Kumar Pal<br />
Presentation Only Intrusion-Tolerant Dissemination in Large-Scale Systems<br />
Kim P. Kihlstrom, Joel Stewart, Nathaniel T. Lounsbury, Michael C. Magnusson,<br />
and Adrian Rogers<br />
ST 7 Wednesday; Kohala 4 ; 3:00 – 4:30<br />
Moderated Discussion: Software Validation and Verification