Navigating the Dataverse: Privacy, Technology ... - The ICHRP
Navigating the Dataverse: Privacy, Technology ... - The ICHRP
Navigating the Dataverse: Privacy, Technology ... - The ICHRP
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Identity is <strong>the</strong>refore unitary and authoritative. “<strong>The</strong> aim of identity mechanisms is to be<br />
able to link or tie a single identity to a single individual. Additional identities on top of<br />
this ‘true’ identity are constructed as criminal or at <strong>the</strong> very least suspicious... <strong>The</strong>re is<br />
no recognition in government discourse that <strong>the</strong>re could be personal preferences for<br />
multiple or overlapping identities without malign intent.” 99 Pseudonyms are suspect.<br />
Identities are considered valuable. “[Y]our identity is one of your most valuable assets”<br />
because it provides access to numerous services and institutions. 100 It is also easily stolen,<br />
being (in an echo of <strong>the</strong> “dividual”) something somehow separable from <strong>the</strong> individual<br />
to whom it “properly belongs”. 101 It is vulnerable and must be regularly checked and<br />
monitored through “trusted institutions”. As a result, paradoxically, individuals become<br />
dependent on organisations both to assign and protect <strong>the</strong>ir personal identities.<br />
Identity is expansive, in that it includes all manner of information about <strong>the</strong> person.<br />
At <strong>the</strong> same time it is shallow, reduced only to those aspects of <strong>the</strong> person that lend<br />
<strong>the</strong>mselves easily and quickly to measurement and monitoring. It becomes a form of<br />
password that determines access to numerous sites and services. This is precisely why<br />
it is valuable to criminals.<br />
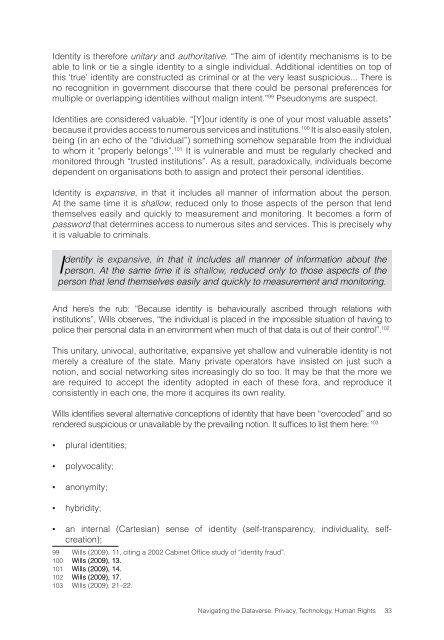
Identity is expansive, in that it includes all manner of information about <strong>the</strong><br />
person. At <strong>the</strong> same time it is shallow, reduced only to those aspects of <strong>the</strong><br />
person that lend <strong>the</strong>mselves easily and quickly to measurement and monitoring.<br />
And here’s <strong>the</strong> rub: “Because identity is behaviourally ascribed through relations with<br />
institutions”, Wills observes, “<strong>the</strong> individual is placed in <strong>the</strong> impossible situation of having to<br />
police <strong>the</strong>ir personal data in an environment when much of that data is out of <strong>the</strong>ir control”. 102<br />
This unitary, univocal, authoritative, expansive yet shallow and vulnerable identity is not<br />
merely a creature of <strong>the</strong> state. Many private operators have insisted on just such a<br />
notion, and social networking sites increasingly do so too. It may be that <strong>the</strong> more we<br />
are required to accept <strong>the</strong> identity adopted in each of <strong>the</strong>se fora, and reproduce it<br />
consistently in each one, <strong>the</strong> more it acquires its own reality.<br />
Wills identifies several alternative conceptions of identity that have been “overcoded” and so<br />
rendered suspicious or unavailable by <strong>the</strong> prevailing notion. It suffices to list <strong>the</strong>m here: 103<br />
▪<br />
▪<br />
▪<br />
▪<br />
plural identities;<br />
polyvocality;<br />
anonymity;<br />
hybridity;<br />
▪<br />
an internal (Cartesian) sense of identity (self-transparency, individuality, selfcreation);<br />
99 Wills (2009), 11, citing a 2002 Cabinet Office study of “identity fraud”.<br />
100 Wills (2009), 13.<br />
101 Wills (2009), 14.<br />
102 Wills (2009), 17.<br />
103 Wills (2009), 21–22.<br />
<strong>Navigating</strong> <strong>the</strong> <strong>Dataverse</strong>: <strong>Privacy</strong>, <strong>Technology</strong>, Human Rights 33