CS 742 Computer Communication Networks Final Exam - Name ...
CS 742 Computer Communication Networks Final Exam - Name ...
CS 742 Computer Communication Networks Final Exam - Name ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
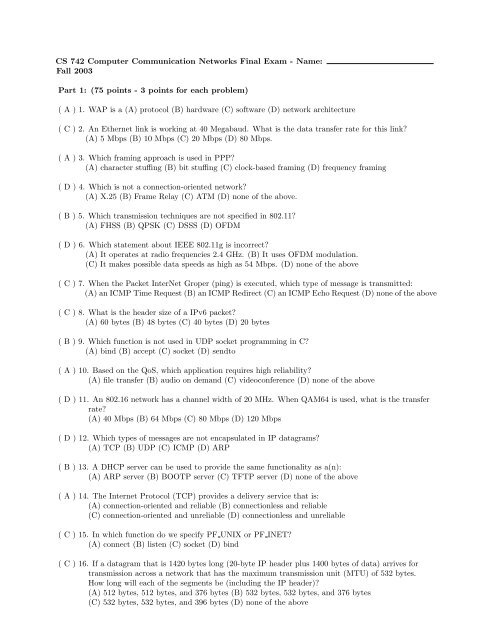
<strong>CS</strong> <strong>742</strong> <strong>Computer</strong> <strong>Communication</strong> <strong>Networks</strong> <strong>Final</strong> <strong>Exam</strong> - <strong>Name</strong>:<br />
Fall 2003<br />
Part 1: (75 points - 3 points for each problem)<br />
( A ) 1. WAP is a (A) protocol (B) hardware (C) software (D) network architecture<br />
( C ) 2. An Ethernet link is working at 40 Megabaud. What is the data transfer rate for this link?<br />
(A) 5 Mbps (B) 10 Mbps (C) 20 Mbps (D) 80 Mbps.<br />
( A ) 3. Which framing approach is used in PPP?<br />
(A) character stuffing (B) bit stuffing (C) clock-based framing (D) frequency framing<br />
( D ) 4. Which is not a connection-oriented network?<br />
(A) X.25 (B) Frame Relay (C) ATM (D) none of the above.<br />
( B ) 5. Which transmission techniques are not specified in 802.11?<br />
(A) FHSS (B) QPSK (C) DSSS (D) OFDM<br />
( D ) 6. Which statement about IEEE 802.11g is incorrect?<br />
(A) It operates at radio frequencies 2.4 GHz. (B) It uses OFDM modulation.<br />
(C) It makes possible data speeds as high as 54 Mbps. (D) none of the above<br />
( C ) 7. When the Packet InterNet Groper (ping) is executed, which type of message is transmitted:<br />
(A) an ICMP Time Request (B) an ICMP Redirect (C) an ICMP Echo Request (D) none of the above<br />
( C ) 8. What is the header size of a IPv6 packet?<br />
(A) 60 bytes (B) 48 bytes (C) 40 bytes (D) 20 bytes<br />
( B ) 9. Which function is not used in UDP socket programming in C?<br />
(A) bind (B) accept (C) socket (D) sendto<br />
( A ) 10. Based on the QoS, which application requires high reliability?<br />
(A) file transfer (B) audio on demand (C) videoconference (D) none of the above<br />
( D ) 11. An 802.16 network has a channel width of 20 MHz. When QAM64 is used, what is the transfer<br />
rate?<br />
(A) 40 Mbps (B) 64 Mbps (C) 80 Mbps (D) 120 Mbps<br />
( D ) 12. Which types of messages are not encapsulated in IP datagrams?<br />
(A) TCP (B) UDP (C) ICMP (D) ARP<br />
( B ) 13. A DHCP server can be used to provide the same functionality as a(n):<br />
(A) ARP server (B) BOOTP server (C) TFTP server (D) none of the above<br />
( A ) 14. The Internet Protocol (TCP) provides a delivery service that is:<br />
(A) connection-oriented and reliable (B) connectionless and reliable<br />
(C) connection-oriented and unreliable (D) connectionless and unreliable<br />
( C ) 15. In which function do we specify PF UNIX or PF INET?<br />
(A) connect (B) listen (C) socket (D) bind<br />
( C ) 16. If a datagram that is 1420 bytes long (20-byte IP header plus 1400 bytes of data) arrives for<br />
transmission across a network that has the maximum transmission unit (MTU) of 532 bytes.<br />
How long will each of the segments be (including the IP header)?<br />
(A) 512 bytes, 512 bytes, and 376 bytes (B) 532 bytes, 532 bytes, and 376 bytes<br />
(C) 532 bytes, 532 bytes, and 396 bytes (D) none of the above
( B ) 17. Which device operates in the data link layer?<br />
(A) repeater (B) bridge (C) router (D) gateway<br />
( D ) 18. Which is not a routing algorithm or protocol?<br />
(A) Distance Vector (B) BGP (C) OSPF (D) none of the above<br />
( D ) 19. Which type is set to query the domain name server in nslookup?<br />
(A) MX (B) HINFO (C) CNAME (D) NS<br />
( B ) 20. In Java socket programming, which class represents a socket for sending and receiving<br />
datagram packets on the server side?<br />
(A) DatagramPacket (B) DatagramSocket (C) ServerSocket (D) DatagramServerSocket<br />
( D ) 21. The assigned port for the SMTP server is:<br />
(A) 21 (B) 22 (C) 23 (D) 25<br />
( C ) 22. Which server interprets name to IP address and vice versa?<br />
(A) SMTP (B) FTP (C) DNS (D) DHCP<br />
( B ) 23. IPv6 represents local loopback address as<br />
(A) ::127.0.0.0 (B) ::1 (C) ::0 (D) none of the above<br />
( A ) 24. Which can be used to encrypt and decrypt email?<br />
(A) PGP (B) TLS (C) RTP (D) SSH<br />
( A ) 25. Which command prints network connections, routing tables, and interface statistics?<br />
(A) netstat (B) ping (C) traceroute (D) dig<br />
Part 2: (125 points)<br />
1. (15 pts.) Briefly explain these terminologies. If they are acronyms, also write what they stand for.<br />
(a) BGP Border Gateway Protocol (BGP) is a protocol for exchanging routing information between<br />
autonomous systems.<br />
(b) NAT Network Address Translation (NAT) is the translation of an IP address used within one<br />
network to a different IP address known within another network.<br />
(c) <strong>CS</strong>MA/CA Carrier Sensing Multiple Access with Collision Avoidance (<strong>CS</strong>MA/CA) is a protocol<br />
used in wireless networking.<br />
(d) AODV Ad hoc On-demand Distance Vector (AODV) is a routing algorithm used to solve the<br />
problem of mobile routers.<br />
(e) HTTPS The HyperText Transport Protocol Secure (HTTPS), is standard encrypted communication<br />
mechanism on the World Wide Web. It is just HTTP over SSL.<br />
2. (10 pts.) Complete the following table listing the seven layers in the OSI 7-Layer Reference Model.<br />
Then, identify three of the four layers used in the TCP/IP protocol suite (write TCP/IP beside them).<br />
<strong>Final</strong>ly, identify where the following protocols belong: TCP, UDP, IP, ICMP, PPP, RARP, IMAP.<br />
• Layer 7: Application Layer - IMAP (TCP/IP)<br />
• Layer 6: Presentation Layer<br />
• Layer 5: Session Layer<br />
• Layer 4: Transport Layer - TCP, UDP (TCP/IP)<br />
• Layer 3: Network Layer - IP, ICMP (TCP/IP)<br />
• Layer 2: Data Link Layer - PPP, RARP (TCP/IP)<br />
• Layer 1: Physical Layer
3. (9 pts.) Recall the Nyquist’s theorem:<br />
A filtered signal, run through a filter of bandwidth H Hz, can be completely reconstructed<br />
by taking 2H exact samples per second. If the signal has V discrete levels:<br />
max. data rate = 2Hlog 2 (V ) bits/sec.<br />
Now, answer the following questions:<br />
(a) A media server is transmitting a video of 2 x 2 inch at a resolution 60 pixels per inch, 2 bytes/pixel<br />
color encoding and 30 frames/second. Calculate the bandwidth necessary for transmitting in real<br />
times.<br />
(b) A noiseless channel is 2-MHz wide. How many bits per second can be sent on this noiseless channel<br />
if four-level digital signals are used?<br />
(c) Without loss of the resolution and color, how many frames per second can this media server<br />
transfer on this noiseless channel?<br />
Ans:<br />
(a) A frame size is 2 × 2 × 60 2 × 2 × 8 = 0.2304 Mbps. The bandwidth is 0.2304 × 30 = 6.912 Mbps.<br />
(b) The noiseless channel provide 2 × 2 log 2 (4) = 8 Mbps transfer rate.<br />
(c) It can transfer 8/0.2304 = 34 frames/s<br />
4. (12 pts.) Suppose that a code consists of the following valid codewords: {00000000, 00001111, 11110000,<br />
11111111}.<br />
(a) What is the Hamming distance of the code?<br />
(b) Can a single bit error be corrected? Explain.<br />
(c) If a codeword 00000011 is received, it must contain errors. Assuming that only two errors have<br />
occurred, can these two errors be corrected? Briefly explain how it would corrected, or why it<br />
cannot be corrected.<br />
Ans:<br />
(a) The Hamming distance of the code is 4 because the number of bit positions in which two codewords<br />
differ is 4.<br />
(b) Yes, to correct a single bit error the Hamming distance 2 × 1 + 1 = 3 is required. The Hamming<br />
distance of the code is 4 > 3. So one bit error can be corrected.<br />
(c) No, there is no way to tell 00000000 or 00001111 will be the correct codeword. To correct 2 bit<br />
error, 2d + 1 = 2 × 2 + 1 = 5 Hamming distance is required.
5. (7 pts.) Using the divisor polynomial x 4 + x + 1 for CRC, what frame will be transmitted for the data<br />
M = 110011001?<br />
ns: M(x) = 110011001, C(x) = 10011, r = 4<br />
1101101<br />
--------------<br />
10011 )1100110010000<br />
10011<br />
------<br />
10101<br />
10011<br />
-------<br />
11000<br />
10011<br />
------<br />
10111<br />
10011<br />
-------<br />
10000<br />
10011<br />
--------<br />
1100<br />
So the transmission frame T(x) is 1100110011100<br />
6. (8 pts.) Suppose that 2 n stations use the adaptive tree walk protocol to arbitrate access to a shared<br />
channel. At a certain instant 2 stations become ready. What are the minimum and maximum number<br />
of bit slots needed to walk the tree if 2 n is much larger than 1?<br />
(a) The minimum number happens when two stations are in two different subtrees from the root. It<br />
will be 3 bit slots.<br />
(b) The maximum number happens when two stations are in the same deepst subtree. Traversing<br />
from the root node, there are n collision nodes and n + 1 nodes without collision. So the maximum<br />
number is n + n + 1 = 2n + 1.<br />
7. (6 pts.) Suppose a router has built up the routing table as shown in the following table. The router<br />
can deliver packets directly over interfaces eth0 and eth1, or it can forward packets to other routers in<br />
the table.<br />
Destination Netmask Gateway<br />
156.26.10.0 255.255.255.128 eth0<br />
156.26.10.128 255.255.255.128 eth1<br />
156.26.11.0 255.255.255.192 R1<br />
<br />
R2<br />
Describe what the router does with a packet addressed to each of the following destinations:<br />
(a) 156.26.10.239 - deliver packets directly through eth1<br />
(b) 156.26.11.208 - forward to R2<br />
(c) 156.26.12.27 - forward to R2<br />
8. (9 pts.) For the network 168.78.16.0/20, answer the following questions:<br />
(a) How many IP addresses can be allocated?<br />
(b) What is the last IP address?<br />
(c) What is the netmask?<br />
Ans:<br />
(a) 2 32−20 = 2 12 = 4096.<br />
(b) 16 × 256 = 4096, 16 + 16 − 1 = 31 ⇒ 168.78.31.255.<br />
(c) The host ranges from 168.78.16.0 to 168.78.31.255. The first, second, and forth part of the netmask<br />
are 255, 255, and 0, respectively. The third part of the netmask 256 − 2 24−20 = 240. Hence, the<br />
netmask is 255.255.240.0.
9. (12 pts.) An organization has a class C network 192.168.1 and wants to form subnets for 3 departments,<br />
with hosts as follows:<br />
A<br />
B<br />
C<br />
72 hosts<br />
46 hosts<br />
52 hosts<br />
(a) There are 170 hosts in all. Give a possible arrangement of network and subnet masks to make<br />
this possible.<br />
(b) Suggest what the organization might do if the department C grows to 70 hosts.<br />
Ans:<br />
(a)<br />
Department Network Netmask IP Addresses<br />
A 192.168.1.0/25 255.255.255.128 128<br />
B 192.168.1.128/26 255.255.255.192 64<br />
C 192.168.1.192/26 255.255.255.224 64<br />
(b) These are possible choices: either assign multiple subnets to single department, abandon subnets<br />
and buy a bridge, or let B and C use the same subnet. Here is a possible deployment giving A<br />
two subnets, of sizes 64 and 32; every other department gets a sigle subnet of size of the next<br />
highest power of 2:<br />
Department Network Netmask IP Addresses<br />
A 192.168.1.0/26 255.255.255.192 64<br />
A 192.168.1.64/27 255.255.255.224 32<br />
B 192.168.1.96/26 255.255.255.192 64<br />
C 192.168.1.160/27 255.255.255.224 32<br />
C 192.168.1.192/26 255.255.255.192 64<br />
10. (12 pts.) For True or False questions, if it is false, explain why.<br />
(a) Each host computer or router can only be assigned one Internet (IP) address.<br />
(b) The address 156.26.255.255 is a valid host IP address.<br />
(c) The ARP is used to obtain an IP address.<br />
(d) For wireless communication, error-detecting can be used to make the transmission reliable.<br />
Ans:<br />
(a) False, a host with two Ethernet cards should have two IP addresses, also routers always have<br />
multiple IP addresses assigned<br />
(b) False, the address 156.26.255.255 is used to broadcast a message to all hosts on the network<br />
156.26.0.0.<br />
(c) False, the ARP is used to obtain the hardware address.<br />
(d) False, error-correcting should be used to make the transmission reliable.<br />
11. (8 pts.) Encrypt the following plaintext using a transposition cipher based on the key LEOPARD.<br />
plaintext = H A V E A G R E A T W I N T E R B R E A K<br />
L E O P A R D<br />
4 3 5 6 1 7 2<br />
H A V E A G R<br />
E A T W I N T<br />
E R B R E A K<br />
ciphertext = A I E R T K A A R H E E V T B E W R G N A
12. (8 pts.) Using the RSA public key cryptography algorithm.<br />
(a) If p = 11 and q = 13, list five legal values for d.<br />
(b) If p = 5, q = 17, and d = 7, find e.<br />
Ans:<br />
(a) z = (p - 1) × (q - 1) = 10 × 12 = 120. d should be relatively prime to 120. The possible values<br />
for d are 7, 11, 13, 17, 19, 23, 29, etc.<br />
(b) z = (5 - 1) × (17 - 1) = 64. 7e % 64 = 1, 65, 129, 257, 321, 385. 7e = 385 e = 55<br />
13. (9 pts.) Choose one of the following questions to answer:<br />
Ans:<br />
• Describe the steps the TCP client and server go through in C socket programming.<br />
• Describe the steps the TCP client and server go through in Java socket programming.<br />
• The steps the TCP client and server go through in C socket programming:<br />
(a) The TCP client goes through four steps:<br />
i. Create a TCP socket using socket().<br />
ii. Establish a connection to the server using connect().<br />
iii. Communicate using send() and recv().<br />
iv. Close the connection with close().<br />
(b) The TCP server goes through three steps:<br />
i. Create a TCP socket using socket().<br />
ii. Assign a port number to the socket with bind().<br />
iii. Tell the system to allow connections to be made to that port, using listen().<br />
iv. Repeatedly do the following:<br />
A. Call accept() to get a new socket for each client connection.<br />
B. Communicate with the client via that new socket using send() and recv().<br />
C. Close the client connection using close().<br />
• The steps the TCP client and server go through in Java socket programming:<br />
(a) The TCP client goes through three steps:<br />
i. Construct an instance of Socket: The constructor establishes a TCP connection to the<br />
specified remote host and port.<br />
ii. Communicate using the socket’s I/O streams: A connected instance of Socket contains<br />
an InputStream and OutputStream that can be used just like any other Java I/O stream.<br />
iii. Close the connection using the close() method of Socket.<br />
(b) The TCP server goes through two steps:<br />
i. Construct a ServerSocket instance, specifying the local port. This socket listens for incoming<br />
connections to the specified port.<br />
ii. Repeatedly do the following:<br />
A. Call the accept() method of ServerSocket to get the next incoming client connection.<br />
Upon establishment of a new client connection, an instance of Socket for the new<br />
connection is created and returned by accept().<br />
B. Communicate with the client using the returned Socket’s InputStream and Output-<br />
Stream.<br />
C. Close the new client socket connection using the close() method of Socket.