LNCS 2820 - Ambiguity Resolution via Passive OS Fingerprinting
LNCS 2820 - Ambiguity Resolution via Passive OS Fingerprinting
LNCS 2820 - Ambiguity Resolution via Passive OS Fingerprinting
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
<strong>Ambiguity</strong> <strong>Resolution</strong> <strong>via</strong> <strong>Passive</strong> <strong>OS</strong> <strong>Fingerprinting</strong> 203<br />
when all available memory resources are consumed, the memory manager calls<br />
back into these cache routines to free memory, effectively wiping out as much<br />
of the cache as needed for the system to continue monitoring. When memory<br />
resources become available again, the cache can be rebuilt.<br />
7 Experiments and Results<br />
Using the mapping tool described in Section 4, we were able to map almost 1,200<br />
hosts and identify 42 different operating systems.<br />
The TCP options tests gathered 223 unique responses from different operating<br />
systems 3 , which is a wealth of information that can be used to identify<br />
hosts.<br />
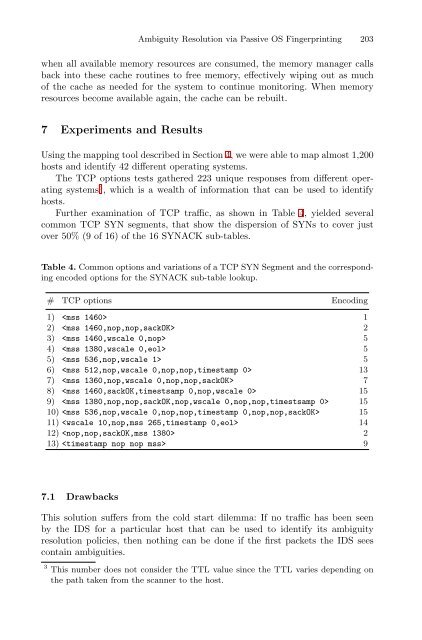
Further examination of TCP traffic, as shown in Table 4, yielded several<br />
common TCP SYN segments, that show the dispersion of SYNs to cover just<br />
over 50% (9 of 16) of the 16 SYNACK sub-tables.<br />
Table 4. Common options and variations of a TCP SYN Segment and the corresponding<br />
encoded options for the SYNACK sub-table lookup.<br />
# TCP options Encoding<br />
1) 1<br />
2) 2<br />
3) 5<br />
4) 5<br />
5) 5<br />
6) 13<br />
7) 7<br />
8) 15<br />
9) 15<br />
10) 15<br />
11) 14<br />
12) 2<br />
13) 9<br />
7.1 Drawbacks<br />
This solution suffers from the cold start dilemma: If no traffic has been seen<br />
by the IDS for a particular host that can be used to identify its ambiguity<br />
resolution policies, then nothing can be done if the first packets the IDS sees<br />
contain ambiguities.<br />
3 This number does not consider the TTL value since the TTL varies depending on<br />
the path taken from the scanner to the host.