LNCS 2820 - Ambiguity Resolution via Passive OS Fingerprinting
LNCS 2820 - Ambiguity Resolution via Passive OS Fingerprinting
LNCS 2820 - Ambiguity Resolution via Passive OS Fingerprinting
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
198 G. Taleck<br />
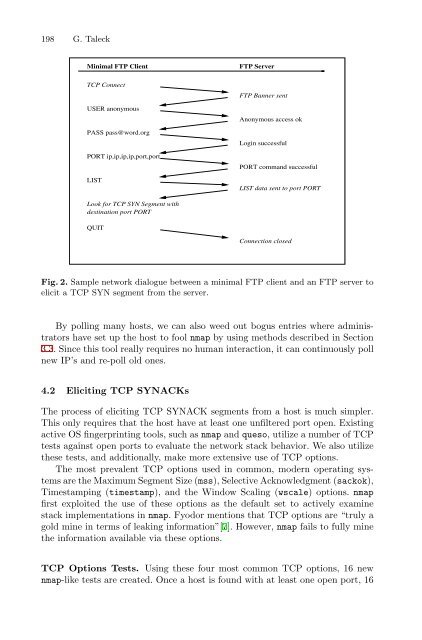
Minimal FTP Client<br />
FTP Server<br />
TCP Connect<br />
USER anonymous<br />
PASS pass@word.org<br />
PORT ip,ip,ip,ip,port,port<br />
LIST<br />
FTP Banner sent<br />
Anonymous access ok<br />
Login successful<br />
PORT command successful<br />
LIST data sent to port PORT<br />
Look for TCP SYN Segment with<br />
destination port PORT<br />
QUIT<br />
Connection closed<br />
Fig. 2. Sample network dialogue between a minimal FTP client and an FTP server to<br />
elicit a TCP SYN segment from the server.<br />
By polling many hosts, we can also weed out bogus entries where administrators<br />
have set up the host to fool nmap by using methods described in Section<br />
3.3. Since this tool really requires no human interaction, it can continuously poll<br />
new IP’s and re-poll old ones.<br />
4.2 Eliciting TCP SYNACKs<br />
The process of eliciting TCP SYNACK segments from a host is much simpler.<br />
This only requires that the host have at least one unfiltered port open. Existing<br />
active <strong>OS</strong> fingerprinting tools, such as nmap and queso, utilize a number of TCP<br />
tests against open ports to evaluate the network stack behavior. We also utilize<br />
these tests, and additionally, make more extensive use of TCP options.<br />
The most prevalent TCP options used in common, modern operating systems<br />
are the Maximum Segment Size (mss), Selective Acknowledgment (sackok),<br />
Timestamping (timestamp), and the Window Scaling (wscale) options. nmap<br />
first exploited the use of these options as the default set to actively examine<br />
stack implementations in nmap. Fyodor mentions that TCP options are “truly a<br />
gold mine in terms of leaking information”[7]. However, nmap fails to fully mine<br />
the information available <strong>via</strong> these options.<br />
TCP Options Tests. Using these four most common TCP options, 16 new<br />
nmap-like tests are created. Once a host is found with at least one open port, 16