z/VSE: 45 Years of Progress - z/VM - IBM
z/VSE: 45 Years of Progress - z/VM - IBM
z/VSE: 45 Years of Progress - z/VM - IBM
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
The CCA host library is available<br />
free at http://ibm.com/security/cryptocards/;<br />
select PCIe Cryptographic<br />
Coprocessor from the navigation bar on<br />
the left side <strong>of</strong> the page for more information<br />
or to download the CCA package.<br />
The host library provides the tools<br />
necessary to manage secure master keys<br />
and build applications in C or Java that<br />
can exploit the diverse array <strong>of</strong> cryptographic<br />
functions available with CEX2C<br />
and CEX3C.<br />
A Peek Under the Covers<br />
All these new features are great, but<br />
you have to jump in and move some bits<br />
and bytes around. Building successful<br />
solutions requires understanding what<br />
the application must do from a cryptographic<br />
standpoint and creating a specification<br />
that identifies the algorithms<br />
and functions required. In addition, you<br />
must determine how keys will be managed<br />
in accordance with the security<br />
policy. Then it’s a simple matter <strong>of</strong> picking<br />
the right verb and parameters to<br />
create the crypto building blocks needed.<br />
The CCA verbs are similar in format,<br />
so crypto components can be built<br />
quickly. The following explains how to<br />
implement one <strong>of</strong> the verbs based on a<br />
specification.<br />
The Java entry points for each verb<br />
are similar to the C entry points and are<br />
distinguished by adding the letter “J” to<br />
the C entry point name. For example,<br />
CSNBKGN is the C entry point for the<br />
key generate verb, and CSNBKGNJ is<br />
the Java entry point for the same verb.<br />
Figures 1 and 2 show simple examples<br />
that generate a single length data key.<br />
These examples aren’t complete solutions<br />
or programming style guides;<br />
they’re code samples for simple key generate<br />
verbs in C and Java.<br />
Incorporating cryptography into an<br />
application can be a daunting task, but<br />
hopefully these examples show how<br />
simple it can be when each part is built<br />
step by step. The examples generate a<br />
single length key (an 8-byte value)<br />
which can be used later to encrypt a<br />
data string using the Data Encryption<br />
Standard (DES) algorithm. The key isn’t<br />
imported or exported; it’s generated and<br />
used as an operational key only. It may<br />
be useful to download the Programmer’s<br />
Guide from www-03.ibm.com/security/<br />
cryptocards/; the keywords are described<br />
on pages 132 to 139.<br />
In the examples, an operational key<br />
(keyword: OP) is needed. Other options,<br />
such as a pair <strong>of</strong> operational keys (keyword:<br />
OPOP), some other pair <strong>of</strong> keys<br />
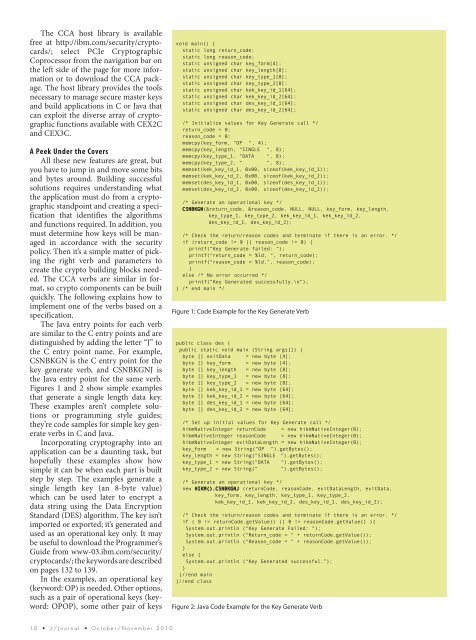
void main() {<br />
static long return_code;<br />
static long reason_code;<br />
static unsigned char key_form[4];<br />
static unsigned char key_length[8];<br />
static unsigned char key_type_1[8];<br />
static unsigned char key_type_2[8];<br />
static unsigned char kek_key_id_1[64];<br />
static unsigned char kek_key_id_2[64];<br />
static unsigned char des_key_id_1[64];<br />
static unsigned char des_key_id_2[64];<br />
/* Initialize values for Key Generate call */<br />
return_code = 0;<br />
reason_code = 0;<br />
memcpy(key_form, “OP “, 4);<br />
memcpy(key_length, “SINGLE “, 8);<br />
memcpy(key_type_1, “DATA “, 8);<br />
memcpy(key_type_2, “ “, 8);<br />
memset(kek_key_id_1, 0x00, size<strong>of</strong>(kek_key_id_1));<br />
memset(kek_key_id_2, 0x00, size<strong>of</strong>(kek_key_id_2));<br />
memset(des_key_id_1, 0x00, size<strong>of</strong>(des_key_id_1));<br />
memset(des_key_id_2, 0x00, size<strong>of</strong>(des_key_id_2));<br />
/* Generate an operational key */<br />
CSNBKGN(&return_code, &reason_code, NULL, NULL, key_form, key_length,<br />
key_type_1, key_type_2, kek_key_id_1, kek_key_id_2,<br />
des_key_id_1, des_key_id_2);<br />
/* Check the return/reason codes and terminate if there is an error. */<br />
if (return_code != 0 || reason_code != 0) {<br />
printf(“Key Generate failed: “);<br />
printf(“return_code = %ld, “, return_code);<br />
printf(“reason_code = %ld.”, reason_code);<br />
}<br />
else /* No error occurred */<br />
printf(“Key Generated successfully.\n”);<br />
} /* end main */<br />
Figure 1: Code Example for the Key Generate Verb<br />
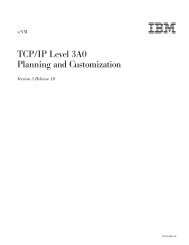
public class des {<br />
public static void main (String args[]) {<br />
byte [] exitData = new byte [4];<br />
byte [] key_form = new byte [4];<br />
byte [] key_length = new byte [8];<br />
byte [] key_type_1 = new byte [8];<br />
byte [] key_type_2 = new byte [8];<br />
byte [] kek_key_id_1 = new byte [64];<br />
byte [] kek_key_id_2 = new byte [64];<br />
byte [] des_key_id_1 = new byte [64];<br />
byte [] des_key_id_2 = new byte [64];<br />
/* Set up initial values for Key Generate call */<br />
hikmNativeInteger returnCode = new hikmNativeInteger(0);<br />
hikmNativeInteger reasonCode = new hikmNativeInteger(0);<br />
hikmNativeInteger exitDataLength = new hikmNativeInteger(0);<br />
key_form = new String(“OP “).getBytes();<br />
key_length = new String(“SINGLE “).getBytes();<br />
key_type_1 = new String(“DATA “).getBytes();<br />
key_type_2 = new String(“ “).getBytes();<br />
/* Generate an operational key */<br />
new HIKM().CSNBKGNJ (returnCode, reasonCode, exitDataLength, exitData,<br />
key_form, key_length, key_type_1, key_type_2,<br />
kek_key_id_1, kek_key_id_2, des_key_id_1, des_key_id_2);<br />
/* Check the return/reason codes and terminate if there is an error. */<br />
if ( 0 != returnCode.getValue() || 0 != reasonCode.getValue() ){<br />
System.out.println (“Key Generate Failed: “);<br />
System.out.println (“Return_code = “ + returnCode.getValue());<br />
System.out.println (“Reason_code = “ + reasonCode.getValue());<br />
}<br />
else {<br />
System.out.println (“Key Generated successful.”);<br />
}<br />
}//end main<br />
}//end class<br />
Figure 2: Java Code Example for the Key Generate Verb<br />
1 0 • z / J o u r n a l • O c t o b e r / N o v e m b e r 2 0 1 0