Security Automation - IAC - Defense Technical Information Center
Security Automation - IAC - Defense Technical Information Center
Security Automation - IAC - Defense Technical Information Center
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
DoD Activities Underway to<br />
Mature SCAP Standards<br />
by Kevin Bingham and Scott Messick<br />
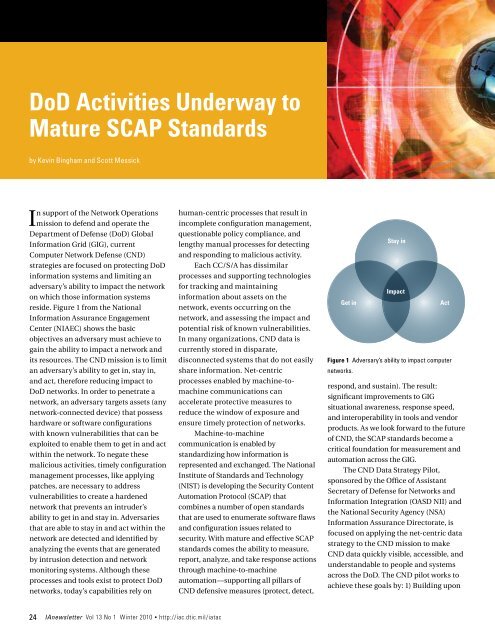
In support of the Network Operations<br />
mission to defend and operate the<br />
Department of <strong>Defense</strong> (DoD) Global<br />
<strong>Information</strong> Grid (GIG), current<br />
Computer Network <strong>Defense</strong> (CND)<br />
strategies are focused on protecting DoD<br />
information systems and limiting an<br />
adversary’s ability to impact the network<br />
on which those information systems<br />
reside. Figure 1 from the National<br />
<strong>Information</strong> Assurance Engagement<br />
<strong>Center</strong> (NIAEC) shows the basic<br />
objectives an adversary must achieve to<br />
gain the ability to impact a network and<br />
its resources. The CND mission is to limit<br />
an adversary’s ability to get in, stay in,<br />
and act, therefore reducing impact to<br />
DoD networks. In order to penetrate a<br />
network, an adversary targets assets (any<br />
network-connected device) that possess<br />
hardware or software configurations<br />
with known vulnerabilities that can be<br />
exploited to enable them to get in and act<br />
within the network. To negate these<br />
malicious activities, timely configuration<br />
management processes, like applying<br />
patches, are necessary to address<br />
vulnerabilities to create a hardened<br />
network that prevents an intruder’s<br />
ability to get in and stay in. Adversaries<br />
that are able to stay in and act within the<br />
network are detected and identified by<br />
analyzing the events that are generated<br />
by intrusion detection and network<br />
monitoring systems. Although these<br />
processes and tools exist to protect DoD<br />
networks, today’s capabilities rely on<br />
human-centric processes that result in<br />
incomplete configuration management,<br />
questionable policy compliance, and<br />
lengthy manual processes for detecting<br />
and responding to malicious activity.<br />
Each CC/S/A has dissimilar<br />
processes and supporting technologies<br />
for tracking and maintaining<br />
information about assets on the<br />
network, events occurring on the<br />
network, and assessing the impact and<br />
potential risk of known vulnerabilities.<br />
In many organizations, CND data is<br />
currently stored in disparate,<br />
disconnected systems that do not easily<br />
share information. Net-centric<br />
processes enabled by machine-tomachine<br />
communications can<br />
accelerate protective measures to<br />
reduce the window of exposure and<br />
ensure timely protection of networks.<br />
Machine-to-machine<br />
communication is enabled by<br />
standardizing how information is<br />
represented and exchanged. The National<br />
Institute of Standards and Technology<br />
(NIST) is developing the <strong>Security</strong> Content<br />
<strong>Automation</strong> Protocol (SCAP) that<br />
combines a number of open standards<br />
that are used to enumerate software flaws<br />
and configuration issues related to<br />
security. With mature and effective SCAP<br />
standards comes the ability to measure,<br />
report, analyze, and take response actions<br />
through machine-to-machine<br />
automation—supporting all pillars of<br />
CND defensive measures (protect, detect,<br />
Get in<br />
Stay in<br />
Impact<br />
Act<br />
Figure 1 Adversary’s ability to impact computer<br />
networks.<br />
respond, and sustain). The result:<br />
significant improvements to GIG<br />
situational awareness, response speed,<br />
and interoperability in tools and vendor<br />
products. As we look forward to the future<br />
of CND, the SCAP standards become a<br />
critical foundation for measurement and<br />
automation across the GIG.<br />
The CND Data Strategy Pilot,<br />
sponsored by the Office of Assistant<br />
Secretary of <strong>Defense</strong> for Networks and<br />
<strong>Information</strong> Integration (OASD NII) and<br />
the National <strong>Security</strong> Agency (NSA)<br />
<strong>Information</strong> Assurance Directorate, is<br />
focused on applying the net-centric data<br />
strategy to the CND mission to make<br />
CND data quickly visible, accessible, and<br />
understandable to people and systems<br />
across the DoD. The CND pilot works to<br />
achieve these goals by: 1) Building upon<br />
24 IAnewsletter Vol 13 No 1 Winter 2010 • http://iac.dtic.mil/iatac