Security Automation - IAC - Defense Technical Information Center
Security Automation - IAC - Defense Technical Information Center
Security Automation - IAC - Defense Technical Information Center
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
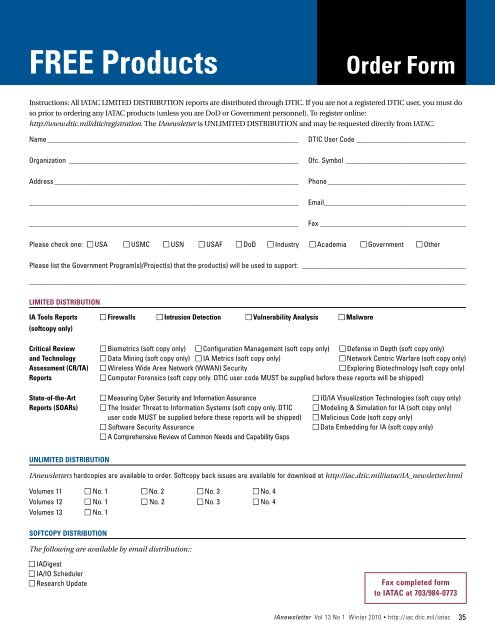
FREE Products<br />
Order Form<br />
Instructions: All IATAC LIMITED DISTRIBUTION reports are distributed through DTIC. If you are not a registered DTIC user, you must do<br />
so prior to ordering any IATAC products (unless you are DoD or Government personnel). To register online:<br />
http://www.dtic.mil/dtic/registration. The IAnewsletter is UNLIMITED DISTRIBUTION and may be requested directly from IATAC.<br />
Name______________________________________________________________________<br />
Organization_ _______________________________________________________________<br />
Address____________________________________________________________________<br />
__________________________________________________________________________<br />
__________________________________________________________________________<br />
DTIC User Code_______________________________<br />
Ofc. Symbol_ _________________________________<br />
Phone_______________________________________<br />
Email_______________________________________<br />
Fax_________________________________________<br />
Please check one: n USA n USMC n USN n USAF n DoD n Industry n Academia n Government n Other<br />
Please list the Government Program(s)/Project(s) that the product(s) will be used to support: ______________________________________________<br />
________________________________________________________________________________________________________________________<br />
LIMITED DISTRIBUTION<br />
IA Tools Reports n Firewalls n Intrusion Detection n Vulnerability Analysis n Malware<br />
(softcopy only)<br />
Critical Review n Biometrics (soft copy only) n Configuration Management (soft copy only) n <strong>Defense</strong> in Depth (soft copy only)<br />
and Technology n Data Mining (soft copy only) n IA Metrics (soft copy only) n Network Centric Warfare (soft copy only)<br />
Assessment (CR/TA) n Wireless Wide Area Network (WWAN) <strong>Security</strong> n Exploring Biotechnology (soft copy only)<br />
Reports<br />
n Computer Forensics (soft copy only. DTIC user code MUST be supplied before these reports will be shipped)<br />
State-of-the-Art n Measuring Cyber <strong>Security</strong> and <strong>Information</strong> Assurance n IO/IA Visualization Technologies (soft copy only)<br />
Reports (SOARs) n The Insider Threat to <strong>Information</strong> Systems (soft copy only. DTIC n Modeling & Simulation for IA (soft copy only)<br />
user code MUST be supplied before these reports will be shipped) n Malicious Code (soft copy only)<br />
n Software <strong>Security</strong> Assurance<br />
n Data Embedding for IA (soft copy only)<br />
n A Comprehensive Review of Common Needs and Capability Gaps<br />
UNLIMITED DISTRIBUTION<br />
IAnewsletters hardcopies are available to order. Softcopy back issues are available for download at http://iac.dtic.mil/iatac/IA_newsletter.html<br />
Volumes 11 n No. 1 n No. 2 n No. 3 n No. 4<br />
Volumes 12 n No. 1 n No. 2 n No. 3 n No. 4<br />
Volumes 13 n No. 1<br />
SOFTCOPY DISTRIBUTION<br />
The following are available by email distribution::<br />
n IADigest<br />
n IA/IO Scheduler<br />
n Research Update<br />
Fax completed form<br />
to IATAC at 703/984-0773<br />
IAnewsletter Vol 13 No 1 Winter 2010 • http://iac.dtic.mil/iatac 35