Tieyan LI (Terry) - School of Information Systems - Singapore ...
Tieyan LI (Terry) - School of Information Systems - Singapore ...
Tieyan LI (Terry) - School of Information Systems - Singapore ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
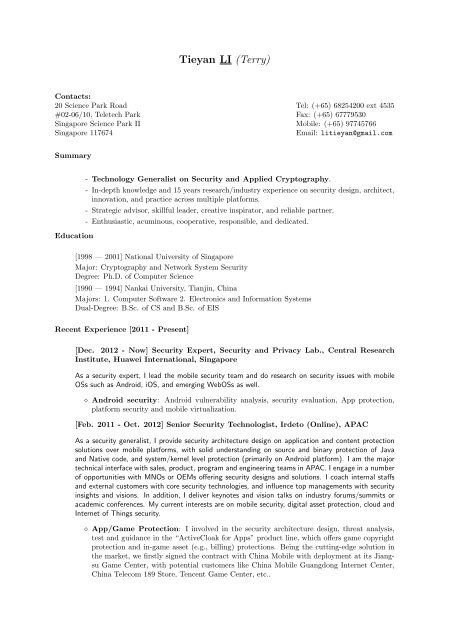
<strong>Tieyan</strong> <strong>LI</strong> (<strong>Terry</strong>)<br />
Contacts:<br />
20 Science Park Road<br />
#02-06/10, Teletech Park<br />
<strong>Singapore</strong> Science Park II<br />
<strong>Singapore</strong> 117674<br />
Tel: (+65) 68254200 ext 4535<br />
Fax: (+65) 67779530<br />
Mobile: (+65) 97745766<br />
Email: litieyan@gmail.com<br />
Summary<br />
Education<br />
- Technology Generalist on Security and Applied Cryptography.<br />
- In-depth knowledge and 15 years research/industry experience on security design, architect,<br />
innovation, and practice across multiple platforms.<br />
- Strategic advisor, skillful leader, creative inspirator, and reliable partner.<br />
- Enthusiastic, acuminous, cooperative, responsible, and dedicated.<br />
[1998 — 2001] National University <strong>of</strong> <strong>Singapore</strong><br />
Major: Cryptography and Network System Security<br />
Degree: Ph.D. <strong>of</strong> Computer Science<br />
[1990 — 1994] Nankai University, Tianjin, China<br />
Majors: 1. Computer S<strong>of</strong>tware 2. Electronics and <strong>Information</strong> <strong>Systems</strong><br />
Dual-Degree: B.Sc. <strong>of</strong> CS and B.Sc. <strong>of</strong> EIS<br />
Recent Experience [2011 - Present]<br />
[Dec. 2012 - Now] Security Expert, Security and Privacy Lab., Central Research<br />
Institute, Huawei International, <strong>Singapore</strong><br />
As a security expert, I lead the mobile security team and do research on security issues with mobile<br />
OSs such as Android, iOS, and emerging WebOSs as well.<br />
⋄ Android security: Android vulnerability analysis, security evaluation, App protection,<br />
platform security and mobile virtualization.<br />
[Feb. 2011 - Oct. 2012] Senior Security Technologist, Irdeto (Online), APAC<br />
As a security generalist, I provide security architecture design on application and content protection<br />
solutions over mobile platforms, with solid understanding on source and binary protection <strong>of</strong> Java<br />
and Native code, and system/kernel level protection (primarily on Android platform). I am the major<br />
technical interface with sales, product, program and engineering teams in APAC. I engage in a number<br />
<strong>of</strong> opportunities with MNOs or OEMs <strong>of</strong>fering security designs and solutions. I coach internal staffs<br />
and external customers with core security technologies, and influence top managements with security<br />
insights and visions. In addition, I deliver keynotes and vision talks on industry forums/summits or<br />
academic conferences. My current interests are on mobile security, digital asset protection, cloud and<br />
Internet <strong>of</strong> Things security.<br />
⋄ App/Game Protection: I involved in the security architecture design, threat analysis,<br />
test and guidance in the “ActiveCloak for Apps” product line, which <strong>of</strong>fers game copyright<br />
protection and in-game asset (e.g., billing) protections. Being the cutting-edge solution in<br />
the market, we firstly signed the contract with China Mobile with deployment at its Jiangsu<br />
Game Center, with potential customers like China Mobile Guangdong Internet Center,<br />
China Telecom 189 Store, Tencent Game Center, etc..
⋄ Android Platform Security: I involved in “Android platform security” solution, which<br />
provides kernel level protection for Android security architecture, with innovative application<br />
control and analysis, domain isolation (BYOD) and trusted apps capabilities. I assist<br />
business exploration and technical strategy <strong>of</strong> the solution in Asia Pacific region and technically<br />
promote it through major MNOs like China Mobile, China Unicom, China Telecom,<br />
LG U+, KT, SKT (Korea), SingTel (<strong>Singapore</strong>) and OEMs like Samsung, HTC, Huawei.<br />
⋄ Open Mobile Platform Security: I involved in the security baseline requirements, architecture<br />
design, and lifecycle assurance in the “ActiveCloak for Apps” product line, which<br />
<strong>of</strong>fers strong protection for enabler APIs in mobile applications. The product is being developed<br />
and deployed as OMP 1.0 at China Mobile Liaoning Location Center, OMP 1.1 at<br />
China Mobile Guangdong Mobile Market, and OMP 2.0 at China Mobile Research Institute<br />
(CMRI).<br />
⋄ Media Protection: I involved in the security assurance and attack monitoring for the “ActiveCloak<br />
for Media” (ACM) product line, which <strong>of</strong>fers strong protection <strong>of</strong> media copyright<br />
protection and media path protection. These include Samsung for hardening Samsung’s<br />
SmartView HDCP 2.0 clients, Astro (Malaysia), TV Bank (Japan), and Foxtel (Australia)<br />
for Over-The-Top (OTT) DRM solutions conforming to Micros<strong>of</strong>t PlayReady Final Licensee<br />
(PRFL) robustness and compliance rules.<br />
Public Speeches:<br />
⋄ RSA China 2012 28-29 Aug. 2012. Chengdu, China.<br />
Topic: Open Platform Security for Mobile Internet<br />
http://www.emc-china.com/rsaconference/2012/en/index.php<br />
⋄ 6th International Mobile Internet Conference 21-22 Aug. 2012. Beijing, China.<br />
Topic: The Adventure <strong>of</strong> Alice and Robot: Securing Mobile Apps in the wild Android.<br />
http://labs.chinamobile.com/imic2012<br />
Research Experience [1999 - 2011]<br />
[Oct. 2001 - Feb. 2011] Principal Investigator & Security Scientist, Cryptography<br />
and Security Dept., Institute for InfoComm Research (I 2 R), A*STAR <strong>Singapore</strong><br />
For years, I have been doing security related projects as a team leader. I experienced on managing<br />
the whole project life-cycle from exploring new directions, investigating the challenges, securing<br />
the funding; to organizing the team, allocating resources, and running the project until successful<br />
completion.<br />
⋄ A Security Framework for EPCglobal Network. (PI, A*star Public Sector Funding,<br />
S$479K, Aug. 2008-Aug. 2011)<br />
⋄ Real-Time Secure RFID-Based Track and Trace in Aerospace MRO Supply<br />
Chain. (Co-PI, A*star Aerospace program (security part), S$523K, Jan. 2009-Jan. 2011)<br />
⋄ Privacy Protection in RFID <strong>Systems</strong>. (04/2007-03/2009, Research collaboration project<br />
with Kyushu Univ. Japan, A*Star Co-funding)<br />
⋄ Secure and real-time RFID based track and trace information management in<br />
EPCglobal-enabled supply chains. (05/2007-10/2008, Joint Research Project: I 2 R-<br />
SIMtech, A*Star funding)<br />
⋄ SenSec: A more secure and efficient link layer sensor security framework. (A*star<br />
flagship project on sensor network 2004-05)<br />
⋄ mSSA: A flexible MPEG-4 authentication framework, a complementary for multimedia<br />
DRM solutions. (A*star core project 2003-04)<br />
⋄ Disruptive security issues in cloud computing, trusted computing, mobile phone security,<br />
user interface, VoIP, tamper-resistant s<strong>of</strong>tware/hardware, etc.
[Jan. 1999 - Oct. 2001] Ph.D. Candidate, <strong>School</strong> <strong>of</strong> Computing, National University<br />
<strong>of</strong> <strong>Singapore</strong><br />
I pursued my Ph.D. study on cryptography and network security at department <strong>of</strong> computer science,<br />
NUS. I explored various cryptographic algorithms, protocols, architectures, and security tools as well.<br />
I finally focused on “intrusion detection using mobile agent techniques” as my Ph.D. topic.<br />
Work Experience [1994 - 1998]<br />
[Apr. 1998 - Dec. 1998] Chief Technologist, NewPost Computer Pte. Ltd., Beijing,<br />
China<br />
I joined a startup and managed 20 + engineers. We worked on small scale network integration and<br />
database development projects. Beyond a technical role, I had also taken part in business development,<br />
sales and marketing.<br />
[Dec. 1997 - Apr. 1998] Senior Engineer, System Design Department <strong>of</strong> AsiaInfo<br />
Corp., Beijing, China<br />
AsiaInfo is one <strong>of</strong> the earliest Internet companies in China (IPOed on NASDAQ). I was mainly responsible<br />
for large scale network design <strong>of</strong> ChinaNet and partially supporting pre-sales and product<br />
management.<br />
[Jun. 1994 - Dec. 1997] S<strong>of</strong>tware Engineer, R&D center, North China Institute <strong>of</strong><br />
Computing Technology, Taiji Computer Co., Beijing, China<br />
Freshly graduated, I joined the R&D center and participated in several national key projects. I was<br />
technically enriched in several aspects like s<strong>of</strong>tware development, network management and security<br />
assessment.<br />
Invention<br />
[2008-2010] Working drafts.<br />
-“RFID authenticator for secure memory devices”<br />
-“Data synchronization and conflict resolution for RFID applications”<br />
-“2-mode Tag Authentication Scheme in RFID-enabled Supply Chain”<br />
-“Method and System for Protecting RFID tags in RFID-enabled Supply Chains”<br />
-“2-Factor Authorization for Tag Memory Access”<br />
-“WiFi, RFID, and handheld device enabled multi-mode wireless localization system”<br />
-“Circle <strong>of</strong> Trust (COT) model for dynamic collaboration in supply chains”<br />
-“A Flexible RFID Privacy Protection Device”<br />
[Jul. 2006] RFID Anti-Counterfeiting Series, PCT NO. WO 2008/085135 A1.<br />
“Methods and <strong>Systems</strong> <strong>of</strong> Marking and Verifying An <strong>Information</strong> Tag”. with Y. Wu, W. He, P.S.<br />
Tan, T.L. Lim. US Provisional (Jan. 2007- Jan. 2008), Filed for US patent on Jan. 2008.<br />
-“Method on protecting EPC RFID tags against counterfeiting”<br />
-“Method on protecting a batch <strong>of</strong> EPC RFID tags”<br />
-“Method on protecting a set <strong>of</strong> undetachable EPC RFID tags”<br />
-“An invisible marking scheme for the verification <strong>of</strong> EPC RFID tags”<br />
-“Privacy enhanced tag protection method for secure RFID supply chain”<br />
[Jun. 2003] Rcrypto – PCT NO. WO 2005/034423 A1, SG NO. 120791<br />
“Resilient Public Key Cryptographic System” with A. Lux, F. Bao, R. Deng. And in news: The<br />
RCrypto vaccine in COMPUTERWORLD-<strong>Singapore</strong>, Vol. 10, Issue No. 13, 18-24 February<br />
2004.
Certificate <strong>of</strong> Training<br />
[2001] Certificate <strong>of</strong> “Training on Project Management”<br />
[2006] Certificate <strong>of</strong> “Training on Commercial Law & Intellectual Property Management”<br />
Pr<strong>of</strong>essional<br />
Adjunct A/Pr<strong>of</strong>essor:<br />
-<strong>School</strong> <strong>of</strong> <strong>Information</strong> System, <strong>Singapore</strong> Management University (2010 onward)<br />
Advisor:<br />
-A Startup on Cloud Security in <strong>Singapore</strong> (Red Herring Award 2012)<br />
-A Startup on eCommerce in China (O2O IC Market, $500K Funding)<br />
-A Startup on Social Networking in China (First-round Funding: $1M)<br />
Steering Committee:<br />
-Workshop on RFID Security (Asia, 2009 onward)<br />
Selected Publications (2010-2011)<br />
My publications/citations are available from Google Scholar and DBLP:<br />
⋄ http://scholar.google.com.sg/scholarq=tieyan+li&hl=en&as sdt=2001&as sdtp=on<br />
⋄ http://www.informatik.uni-trier.de/˜ley/db/indices/a-tree/l/Li:<strong>Tieyan</strong>.html<br />
Journal publications:<br />
(Reverse Chronological Order)<br />
1. <strong>Tieyan</strong> Li, Guilin Wang, “Analyzing a Family <strong>of</strong> Key Protection Schemes against Modification<br />
Attacks’, IEEE Transactions on Dependable and Secure Computing (IEEE TDSC),<br />
vol. 8, no. 5, pp. 770-776, Sep./Oct. 2011, doi:10.1109/TDSC.2010.44<br />
2. Shaoying Cai, Yingjiu Li, <strong>Tieyan</strong> Li, Robert Deng, Haixia Yao, “Achieving High Security<br />
and Efficiency in RFID-Tagged Supply Chains”, International Journal <strong>of</strong> Applied Cryptography,<br />
Vol. 2, No. 1, 2010, Pages 3-12.<br />
3. Qiang Yan, Robert H. Deng, Yingjiu Li, <strong>Tieyan</strong> Li, “On the Potential <strong>of</strong> Limitation-oriented<br />
Malware Detection and Prevention Techniques on Mobile Phones”. International Journal <strong>of</strong><br />
Security and Its Applications (IJSIA), Volume 4, No.1, 2010, pp.21-30.<br />
Conference publications:<br />
(Reverse Chronological Order)<br />
1. <strong>Tieyan</strong> Li, Guilin Wang and Yingjiu Li, “Secure and Practical Key Distribution for RFID-<br />
Enabled Supply Chains”, 7th International ICST Conference on Security and Privacy in<br />
Communication Networks (SecureComm 2011), Sept. 7-9 2011, London.<br />
2. Qiang Yan, Jin Han, Yingjiu Li, Robert Deng, <strong>Tieyan</strong> Li, “A S<strong>of</strong>tware-Based Root-<strong>of</strong>-<br />
Trust Primitive on Multicore Platforms”, 6th ACM Symposium on <strong>Information</strong>, Computer<br />
and Communications Security (ASIACCS’11), March 22-24, 2011. Hong Kong.<br />
3. Shaoying Cai, Chunhua Su, Yingjiu Li, <strong>Tieyan</strong> Li, Robert Deng, “Protecting and Restraining<br />
the Third Party in RFID-Enabled 3PL Supply Chains”, Sixth International Conference<br />
on <strong>Information</strong> <strong>Systems</strong> Security (ICISS’10), 15-19 December 2010. India.<br />
4. Pedro Peris-Lopez, Julio C. Hernandez-Castro, Juan M. E. Tapiador, Raphael C.-W. Phan,<br />
<strong>Tieyan</strong> Li, “Quasi-Linear Cryptanalysis <strong>of</strong> a Secure RFID Ultralightweight Authentication<br />
Protocol”, The 6th China International Conference on <strong>Information</strong> Security and Cryptology<br />
(Inscrypt’10). 20-23 Oct. 2010, Shanghai, China.<br />
5. Qiang Yan, Yingjiu Li, Robert Deng, <strong>Tieyan</strong> Li, Zheng Yan, “Pseudonym-based RFID<br />
Discovery Service to Mitigate Unauthorized Tracking in Supply Chain Management”, The<br />
Second International Symposium on Data, Privacy, & E-Commerce (ISDPE 2010), 13-14<br />
Sept. 2010. Buffalo/Niagara Falls. USA.