Architecture and Design Considerations - Build Security In - US-CERT
Architecture and Design Considerations - Build Security In - US-CERT
Architecture and Design Considerations - Build Security In - US-CERT
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Overview<br />
The Guide to the Software Engineering Body of Knowledge (SWEBOK) defines the design phase as both “the process of<br />
defining the architecture, components, interfaces, <strong>and</strong> other characteristics of a system or component” <strong>and</strong> “the result of [that]<br />
process.” The software design phase is the software engineering life cycle activity where software requirements are analyzed in<br />
order to produce a description of the software’s internal structure, which will be served as the basis for the software’s<br />
implementation.<br />
The software design phase consists of the architectural design <strong>and</strong> detailed design activities in the Software Development Life<br />
Cycle (SDLC). <strong>In</strong> the Waterfall model, these activities follow the software requirements analysis phase <strong>and</strong> precedes the<br />
implementation phase. However, the concepts presented in this pocket guide can be applied regardless of the development<br />
methodology employed. <strong>In</strong> any event, the practices <strong>and</strong> recommendations should be tailored to the realities of how the software<br />
is built.<br />
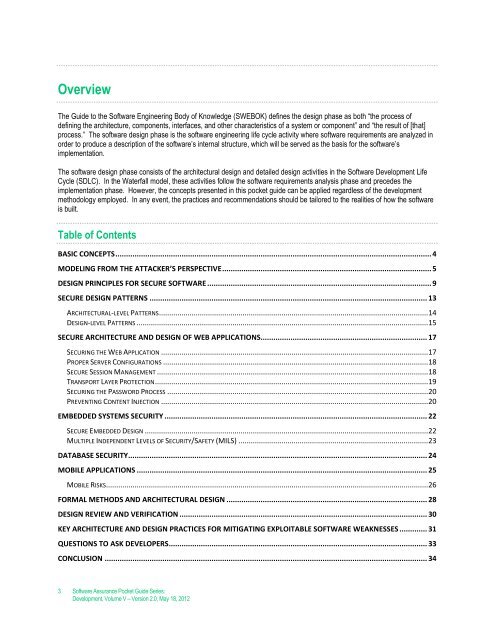
Table of Contents<br />
BASIC CONCEPTS .................................................................................................................................................... 4<br />
MODELING FROM THE ATTACKER’S PERSPECTIVE .................................................................................................. 5<br />
DESIGN PRINCIPLES FOR SECURE SOFTWARE ......................................................................................................... 9<br />
SECURE DESIGN PATTERNS .................................................................................................................................. 13<br />
ARCHITECTURAL-LEVEL PATTERNS .................................................................................................................................... 14<br />
DESIGN-LEVEL PATTERNS ............................................................................................................................................... 15<br />
SECURE ARCHITECTURE AND DESIGN OF WEB APPLICATIONS.............................................................................. 17<br />
SECURING THE WEB APPLICATION ................................................................................................................................... 17<br />
PROPER SERVER CONFIGURATIONS .................................................................................................................................. 18<br />
SECURE SESSION MANAGEMENT ..................................................................................................................................... 18<br />
TRANSPORT LAYER PROTECTION ...................................................................................................................................... 19<br />
SECURING THE PASSWORD PROCESS ................................................................................................................................ 20<br />
PREVENTING CONTENT INJECTION ................................................................................................................................... 20<br />
EMBEDDED SYSTEMS SECURITY ........................................................................................................................... 22<br />
SECURE EMBEDDED DESIGN ........................................................................................................................................... 22<br />
MULTIPLE INDEPENDENT LEVELS OF SECURITY/SAFETY (MILS) ............................................................................................. 23<br />
DATABASE SECURITY ............................................................................................................................................ 24<br />
MOBILE APPLICATIONS ........................................................................................................................................ 25<br />
MOBILE RISKS .............................................................................................................................................................. 26<br />
FORMAL METHODS AND ARCHITECTURAL DESIGN .............................................................................................. 28<br />
DESIGN REVIEW AND VERIFICATION .................................................................................................................... 30<br />
KEY ARCHITECTURE AND DESIGN PRACTICES FOR MITIGATING EXPLOITABLE SOFTWARE WEAKNESSES ............. 31<br />
QUESTIONS TO ASK DEVELOPERS ......................................................................................................................... 33<br />
CONCL<strong>US</strong>ION ....................................................................................................................................................... 34<br />
3 Software Assurance Pocket Guide Series:<br />
Development, Volume V – Version 2.0, May 18, 2012