AES Guest Lecturer
AES Guest Lecturer
AES Guest Lecturer
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
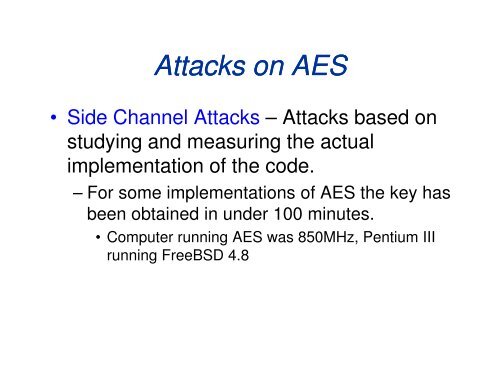
Attacks on <strong>AES</strong><br />
• Side Channel Attacks – Attacks based on<br />
studying and measuring the actual<br />
implementation of the code.<br />
– For some implementations of <strong>AES</strong> the key has<br />
been obtained in under 100 minutes.<br />
• Computer running <strong>AES</strong> was 850MHz, Pentium III<br />
running FreeBSD 4.8






![[PDF] The Thickness and Chromatic Number of r - Gammeter.com](https://img.yumpu.com/3978766/1/190x245/pdf-the-thickness-and-chromatic-number-of-r-gammetercom.jpg?quality=85)