Hong Kong: IT innovation hub? - enterpriseinnovation.net
Hong Kong: IT innovation hub? - enterpriseinnovation.net
Hong Kong: IT innovation hub? - enterpriseinnovation.net
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
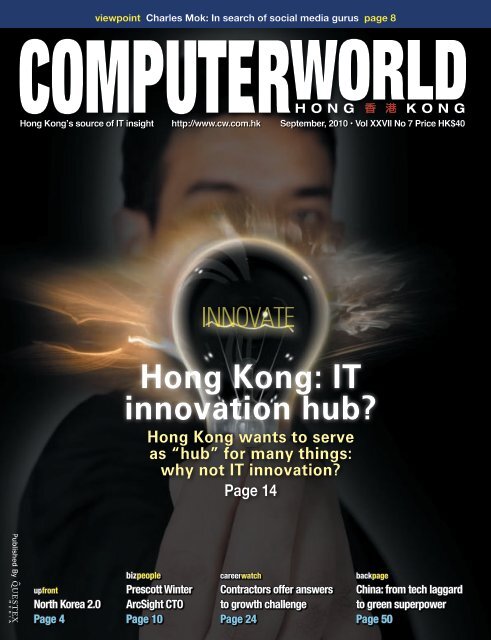
viewpoint Charles Mok: In search of social media gurus page 8<br />
<strong>Hong</strong> <strong>Kong</strong>’s source of <strong>IT</strong> insight http://www.cw.com.hk September, 2010 • Vol XXVII No 7 Price HK$40<br />
<strong>Hong</strong> <strong>Kong</strong>: <strong>IT</strong><br />
<strong>innovation</strong> <strong>hub</strong><br />
<strong>Hong</strong> <strong>Kong</strong> wants to serve<br />
as “<strong>hub</strong>” for many things:<br />
why not <strong>IT</strong> <strong>innovation</strong><br />
Page 14<br />
upfront<br />
North Korea 2.0<br />
www.cw.com.hk<br />
Page 4<br />
bizpeople<br />
Prescott Winter<br />
ArcSight CTO<br />
Page 10<br />
careerwatch<br />
Contractors offer answers<br />
to growth challenge<br />
Page 24<br />
backpage<br />
China: from tech laggard<br />
to green superpower<br />
Page 50<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 1
2 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
c o n t e n t s September 2010<br />
coverstory<br />
<strong>Hong</strong> <strong>Kong</strong>: <strong>IT</strong><br />
<strong>innovation</strong> <strong>hub</strong><br />
<strong>Hong</strong> <strong>Kong</strong> wants to serve as “<strong>hub</strong>” for<br />
many things: why not <strong>IT</strong> <strong>innovation</strong><br />
Page 14<br />
4 upfront<br />
North Korea 2.0<br />
6 news<br />
8 viewpoint<br />
10 bizpeople<br />
Networks scrutiny is the only real security<br />
Prescott Winter spent 25 years in the<br />
USA’s National Security Agency before<br />
pursuing a tech-security career in the<br />
private sector. Computerworld <strong>Hong</strong><br />
<strong>Kong</strong>’s Stefan Hammond gets the story<br />
12 chinawatch<br />
Chinese outsourcer seeks U.S. workers<br />
with IQ of 125 and up, Baidu sues<br />
Chinese security company<br />
40industryevent<br />
The time has come for<br />
real-time apps<br />
The new customer: the case<br />
for predicting and exceeding<br />
expectations<br />
36 industryevent<br />
CIOs back in the fray as Asian <strong>IT</strong><br />
recovers<br />
Top <strong>Hong</strong> <strong>Kong</strong> CIOs and <strong>IT</strong> heads<br />
discuss “CIO Opportunities in the New<br />
Economy”<br />
24 careerwatch<br />
Contractors offer answers to growth<br />
challenge<br />
Companies and individuals ponder<br />
mindset shift as contracting offers flexible<br />
expansion options<br />
38 industryevent<br />
The kaleidoscope of post-financial crisis<br />
<strong>IT</strong> management<br />
The pluses and minuses of swimming at<br />
low tide<br />
44 techguide<br />
IBM rolls out new zEnterprise mainframe<br />
server and auxiliary products<br />
Big iron from Big Blue features 96<br />
microprocessors clocking in at 5.2GHz<br />
46 industryprofile<br />
<strong>Hong</strong> <strong>Kong</strong> firm k-matrix targets online<br />
marketing benchmarks<br />
Social media marketing is the way to<br />
go, says CEO Edmund Lee<br />
50 backpage<br />
China: from tech laggard to green<br />
superpower<br />
China’s scale will eventually lead the<br />
world in clean energy, writes Robert<br />
Clark<br />
Check: www.cw.com.hk for daily<br />
news and online features.<br />
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 3
UPFRONT s t e fa n h a m m o n d<br />
North Korea 2.0<br />
Few associate the antisocial regime of North Korea with technology. Yet<br />
recently, Uriminzokkiri (a Web site that provides Korean-language news<br />
and propaganda from North Korea’s central news agency) has spawned<br />
a Facebook page, a YouTube channel and a Twitter account with over 10,000<br />
followers.<br />
According to Tokyo-based journalist Martyn Williams from IDG’s News Service,<br />
the Web site appears to be run from servers in China but is ultimately<br />
controlled from Pyongyang, the capital of North Korea. The Facebook group appeared<br />
one day in late August and was quickly removed, only to be replaced by<br />
another—with content similar to the original and hundreds of “friends” since it<br />
became available. “The profile details it as belonging to a single male who wants<br />
to <strong>net</strong>work and meet friends and has interests in Korean<br />
reunification and, perhaps bizarrely, lactose free milk,”<br />
wrote Williams.<br />
Why is North Korea suddenly opening these channels<br />
State-control is no joke north of the 38th parallel (expect<br />
revolutionary ballet rather than Pyongyang toddlers lipsyncing<br />
to South Korean pop tunes on the YouTube), but<br />
Stefan Hammond<br />
Editor<br />
shammond@<br />
questexasia.com<br />
North Korea is inevitably changing as time passes. There<br />
are attempts by South Korean firms to leverage the potential<br />
of the North, including an industrial park just north<br />
of the border. Untouched raw mineral-potential means<br />
North Korea has material the rest of the world is willing<br />
to buy. While North Korea remains the most bizarre “walled garden” on earth,<br />
the southern half of the peninsula has massive broadband pe<strong>net</strong>ration and widespread<br />
manufacture of high-tech devices.<br />
The long isolation of North Korea means integration with the rest of the world<br />
will be difficult. But look at China’s example: it’s possible to emerge from isolation<br />
and participate in the world community (China has been urging North<br />
Korea to create and develop Special Economic Zones, and following the Chinese<br />
model seems a sensible idea for a nation that’s been largely insensible since the<br />
1950s).<br />
A US State Department spokesman welcomed the North’s fledgling tweets. “We<br />
welcome North Korea to Twitter and the <strong>net</strong>worked world,” wrote Philip Crowley,<br />
on his Twitter account. “The Hermit Kingdom will not change overnight, but<br />
technology once introduced can’t be shut down.”<br />
“Just ask Iran,” tweeted Crowley.<br />
Stefan Hammond<br />
Editor<br />
shammond@questexasia.com<br />
http://www.cw.com.hk<br />
Computerworld <strong>Hong</strong> <strong>Kong</strong> is published by Questex Asia Ltd, 501 Cambridge<br />
House, Taikoo Place, 979 King’s Road, Quarry Bay, <strong>Hong</strong> <strong>Kong</strong>.<br />
PUBLISHER Simon Yeung syeung@questexasia.com<br />
ED<strong>IT</strong>ORIAL<br />
ED<strong>IT</strong>OR-IN-CHIEF Chee Sing Chan cchan@questexasia.com<br />
ED<strong>IT</strong>OR Stefan Hammond shammond@questexasia.com<br />
SENIOR REPORTER Teresa Leung tleung@questexasia.com<br />
contributing writer Ross Milburn<br />
SALES<br />
ACCOUNT DIRECTOR Connie Yip cyip@questexasia.com<br />
MARKETING & SALES Carvin Lee clee@questexasia.com<br />
SUPPORTING EXECUTIVE<br />
ADMINISTRATION<br />
ART DIRECTOR Eric Lam elam@questexasia.com<br />
Circulation & John Lam jlam@questexasia.com<br />
Distribution Director<br />
ASSISTANT CIRCULATION Allie Mok amok@questexasia.com<br />
MANAGER<br />
MANAGEMENT<br />
Managing Director Jonathan Bigelow jbigelow@questexasia.com<br />
HR & ADMIN MANAGER Janis Lam janislam@questexasia.com<br />
BUSINESS MANAGER Eunice Chan echan@questexasia.com<br />
Computerworld <strong>Hong</strong> <strong>Kong</strong> is published monthly. All material is Copyright<br />
2010 by Questex Media Group, Inc. Reproduction is strictly forbidden<br />
without written permission.<br />
Sales and Custom Publishing Enquiries: E-mail can be sent to syeung@<br />
questexasia.com<br />
Computerworld <strong>Hong</strong> <strong>Kong</strong> is circulated to <strong>IT</strong>, computing<br />
and inter<strong>net</strong> companies and other private<br />
and public companies who use <strong>IT</strong> and computing.<br />
It is edited for <strong>IT</strong> professionals, engineers, and senior<br />
managers responsible for design, installation,<br />
marketing and maintenance of <strong>IT</strong> systems and <strong>net</strong>works.<br />
Free subscription offer valid in <strong>Hong</strong> <strong>Kong</strong><br />
only. To subscribe, go to www.cw.com.hk.<br />
Computerworld <strong>Hong</strong> <strong>Kong</strong> (ISSN 1023-4934) is<br />
published eleven times yearly by Questex Asia Ltd.<br />
Subscription rates: 1 year HK$330 (<strong>Hong</strong> <strong>Kong</strong> only),<br />
HK$440 (Macau only), US$109 (within Asia) and (852) 2589-1313<br />
US$119 (outside Asia), 2 years HK$580 (<strong>Hong</strong> <strong>Kong</strong><br />
only), HK$770 (Macau only), US$190 (within Asia)<br />
and US$210 (outside Asia). Single/Back issue (if<br />
available) HK$40 per copy (<strong>Hong</strong> <strong>Kong</strong> only) US$11<br />
(within Asia) and US$12 (outside Asia) plus US$5<br />
handling charge per order. Printed in <strong>Hong</strong> <strong>Kong</strong>.<br />
Postage paid in <strong>Hong</strong> <strong>Kong</strong>. For subscription enquiries,<br />
change of address or delivery services, please<br />
(852) 2559-2015<br />
contact our circulation department by: fax (852)<br />
2559-2015, e-mail customer_service@cw.com.hk or by mail.<br />
Computerworld <strong>Hong</strong> <strong>Kong</strong> is on sale in bookshops in <strong>Hong</strong> <strong>Kong</strong> at<br />
HK$40 per issue.<br />
Questex Media Group LLC<br />
275 Grove Street, Newton, MA 02466, Tel: +1 617 219 8300<br />
PRESIDENT & CHIEF EXECUTIVE OFFICER Kerry C. Gumas<br />
EXECUTIVE V.P. & CHIEF FINANCIAL OFFICER Tom Caridi<br />
EXECUTIVE VICE PRESIDENT<br />
Robert S. Ingraham<br />
EXECUTIVE VICE PRESIDENT<br />
Tony D’Avino<br />
EXECUTIVE VICE PRESIDENT<br />
Jon Leibowitz<br />
EXECUTIVE V.P. CORPORATE DEVELOPMENT Claudia Flowers<br />
VICE PRESIDENT, DIG<strong>IT</strong>AL MEDIA<br />
Seth Nichols<br />
Printed by:<br />
DG3 Asia Limited<br />
9th Floor, Haking (Tung Shing) Industrial Building<br />
34 Lee Chung Street , Chai Wan, <strong>Hong</strong> <strong>Kong</strong><br />
Tel: 852 2965 6777<br />
www.dg3.com/<br />
Average Circulation: 9,579<br />
www.cw.com.hk<br />
4 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
NEWS<br />
newsbites<br />
IBM rolls out 256-core Unix<br />
server<br />
IBM has rolled out its 256-core Power<br />
795 server—its biggest Unix server to<br />
date—for large enterprises, which customers<br />
are expected to use for consolidation<br />
projects. IBM also launched several<br />
low-end Power7-based servers, each<br />
with one or two processors. All the new<br />
systems are offered with Linux or IBM’s<br />
AIX or i operating systems (i is the new<br />
name for IBM’s i5/OS).<br />
Dell sees Asia rollout of<br />
Android tablet in 2011<br />
Dell is likely to bring its Streak tablet<br />
to Asia-Pacific markets early next year,<br />
said Steve Felice, president of Dell’s<br />
small and medium business unit. Already<br />
on sale in the US and Europe, the Streak<br />
sports a 5-inch touchscreen display,<br />
runs Google’s Android OS, and has a<br />
1GHz Qualcomm SnapDragon processor.<br />
The tablet can connect to Wi-Fi and 3G<br />
<strong>net</strong>works, which allows the Streak to be<br />
used as a phone.<br />
40 Windows apps have critical<br />
bugs<br />
Some 40 different Windows applications<br />
contain a critical flaw that attackers<br />
can use to hijack PCs and infect them<br />
with malware, according to security<br />
researcher HD Moore. Moore is chief<br />
security officer of Rapid7 and creator<br />
of the open-source Metasploit pe<strong>net</strong>ration<br />
testing toolkit. He said the bug was<br />
patched by Apple in its iTunes software<br />
for Windows four months ago, but<br />
remains in more than three dozen other<br />
Windows programs.<br />
global<br />
Intel to buy McAfee for US$7.68 billion<br />
Intel said recently it plans to acquire<br />
security vendor McAfee<br />
in a cash deal valued at about<br />
US$7.68 billion and aimed at enhancing<br />
the chip maker’s mobile strategy.<br />
Both boards of directors have approved<br />
the deal, and McAfee is expected<br />
to become a subsidiary within<br />
Intel’s Software and Services Group.<br />
Intel said that the current approach to<br />
security doesn’t address the full range<br />
of Inter<strong>net</strong>-connected devices, including<br />
TVs, cars, medical devices and ATM<br />
machines. “Hardware-enhanced security”<br />
will be needed to counter increasingly<br />
sophisticated threats, said Renée<br />
James, Intel senior vice president, and<br />
general manager of the group.<br />
McAfee CEO Dave DeWalt wrote<br />
in a blog post that the “current cybersecurity<br />
model isn’t extensible<br />
across the proliferating spectrum of<br />
devices.”<br />
“The industry needed a paradigm<br />
shift, incremental improvements can’t<br />
bridge the opportunity gap,” DeWalt<br />
wrote. “There is no better partner that<br />
we could have found than Intel.”<br />
The deal is expected to close after<br />
McAfee shareholder approval and<br />
regulatory clearances. Intel said the<br />
acquisition will have on a GAAP<br />
basis a slightly dilutive effect on its<br />
earnings in the first year of operations<br />
and a flat effect in the second<br />
year. 3<br />
global<br />
Microsoft: Mac-Windows compatible in Office 2011<br />
Microsoft has announced that<br />
the next version of Office<br />
for the Mac will include a<br />
pair of key features that debuted in the<br />
Windows edition of Office 2010 earlier<br />
this year.<br />
Office for Mac 2011, which is slated<br />
for an October launch, will offer “Sparklines,”<br />
cell-sized Excel charts, and inapp<br />
image editing tools, two features<br />
that first appeared in Office 2010, the<br />
more popular Windows edition that hit<br />
the retail market last May.<br />
Microsoft touted the new features as<br />
part of its attempt to boost compatibility<br />
between the Mac and Windows versions<br />
of the suite.<br />
“What we’ve been able to do in Office<br />
for Mac 2011 is to bring a lot of<br />
power to bear to produce a professionallooking<br />
document that’s still compatible<br />
with Office for Windows,” said Kurt<br />
Schmucker, an evangelist with Microsoft’s<br />
Mac team, in a video the group<br />
released last month.<br />
Sparklines, which Computerworld US<br />
reviewer Preston Gralla called the “most<br />
useful” among the changes to Excel 2010<br />
on Windows, lets users drop bite-sized<br />
charts or graphs into individual cells.<br />
Microsoft pitched Sparklines and improvements<br />
to Excel’s PivotTables as<br />
compatibility wins for Mac users who<br />
need to share spreadsheet documents<br />
with co-workers running the Windows<br />
version of Office. 3<br />
6 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
HP Virtualized Storage Technologies Fight <strong>IT</strong> Sprawl<br />
HP Converged Infrastructure enables integration of existing silos of <strong>IT</strong> resources<br />
with unified management to deliver a virtualized, highly-automated technology environment<br />
Titania Leung<br />
Sprawl of technology silos has<br />
brought <strong>IT</strong> infrastructures to the<br />
breaking point by increasing complexity,<br />
which drives up operational costs<br />
and stifles <strong>innovation</strong>. Today, <strong>IT</strong> organizations<br />
spend up to 70 percent of their<br />
budgets on operations and maintenance<br />
leaving only 30 percent for business <strong>innovation</strong>.<br />
But HP Converged Infrastructure delivers<br />
the blueprint for building the data center of<br />
the future that eliminates costly and rigid<br />
<strong>IT</strong> silos, simplifies the management of the<br />
environment, and drives integration and<br />
automation across every area of the data<br />
center.<br />
Traditionally, client virtualization requires<br />
the complex integration of storage, servers,<br />
<strong>net</strong>working and management software. To<br />
address this challenge, HP is offering the<br />
first client virtualization reference architecture<br />
built for a Converged Infrastructure.<br />
This comprehensive hardware and software<br />
architecture scales to support thousands<br />
of virtual desktops in a simple,<br />
modular design that is pre-sized and pretested.<br />
The reference architecture delivers<br />
three times the productivity for <strong>IT</strong> administrators.<br />
Virtualization and deduplication<br />
“HP StorageWorks technologies play a<br />
critical role in the Converged Infrastructure<br />
by enabling clients to virtualize and cre-<br />
www.cw.com.hk<br />
ate a Virtual Resource Pool that<br />
is instantly accessible for meeting<br />
changing business needs,” says<br />
Titania Leung, Product Manager,<br />
StorageWorks Division, HP <strong>Hong</strong><br />
<strong>Kong</strong>.<br />
Data duplication is on a sharp<br />
upswing in today’s <strong>IT</strong> environment,<br />
with identical records often<br />
duplicated dozens of times. “HP<br />
StoreOnce deduplication software<br />
can be deployed at multiple<br />
points in a converged infrastructure,”<br />
says Leung. “It reduces the<br />
amount of times data must be deduplicated<br />
and enables clients to<br />
more efficiently control data growth. HP<br />
StoreOnce is new in all HP StorageWorks<br />
D2D backup systems. HP D2D solutions<br />
easily combine with HP Data Protector<br />
backup and recovery software, providing<br />
simplified data protection at a 70 percent<br />
lower total cost of ownership compared to<br />
other solutions.”<br />
HP StorageWorks P4800<br />
BladeSystem SAN solution<br />
Faster deployment with a pretested<br />
and performance-tuned configuration<br />
designed for multiple client virtualization<br />
software implementations,<br />
including Microsoft Hyper-V with Citrix<br />
XenDesktop and VMWare View.<br />
Optimized system performance by<br />
balancing the workload across blades<br />
and disk drives to avoid storage bottlenecks<br />
that occur when too many<br />
users log into the <strong>net</strong>work at the same<br />
time.<br />
Increased productivity by distributing<br />
storage resources across multiple<br />
sites to ensure better business continuity.<br />
As a result, end-users have access<br />
to data during failure conditions<br />
such as power outages and human<br />
errors.<br />
Reduced <strong>net</strong>working costs and simplified<br />
management with HP’s Virtual<br />
Connect technology. Integrating the<br />
P4800 into the HP BladeSystem enclosure<br />
eliminates external storage<br />
switches and cables, reducing the<br />
need for <strong>IT</strong> expertise to manage traditional<br />
SAN-based offerings.<br />
Storage strategies<br />
“HP’s P4800 BladeSystem SAN is a core<br />
component of a new HP Converged Infrastructure<br />
reference architecture for client<br />
virtualization,” says Leung. “It supports<br />
1,600 users at 50 percent less cost and requires<br />
60 percent less space than traditional<br />
client virtualization implementations.”<br />
“The LAN-based system can be easily<br />
added on to existing systems,” says Fred<br />
Sheu, Director, Alliances and Solutions, HP<br />
Enterprise Business, <strong>Hong</strong> <strong>Kong</strong>. It provides<br />
scalable, shared storage for a converged<br />
server, storage and <strong>net</strong>working environment.<br />
Built from HP BladeSystem technology,<br />
the new P4800 delivers 63 terabytes<br />
(TB) of storage capacity with four storage<br />
blades connected to 140 disk drives.<br />
Clustering islands of storage<br />
Another new component of HP’s storage<br />
portfolio is the new HP StorageWorks Enterprise<br />
Virtual Array Cluster (EVA Cluster) that<br />
eliminates disparate “islands” of storage. As<br />
a result, clients can consolidate up to 600<br />
percent more storage than a single EVA array,<br />
which reduces complexity, improves capacity<br />
utilization and lowers management costs. The<br />
solution uses a modular approach and works<br />
with existing heterogeneous systems.<br />
“HP EVA Cluster consists of multiple EVAs<br />
to create a virtual pool of capacity containing<br />
up to 2 PB of data and nearly 2,000 drives,”<br />
says Leung.<br />
HP StorageWorks EVA Cluster<br />
Improved continuity with transparent<br />
failover software that maintains<br />
application and availability between<br />
arrays to ensure uninterrupted access<br />
to data.<br />
Simplified operations with HP Command<br />
View, which enables clients to<br />
unify and centralize management of<br />
heterogeneous storage products.<br />
Optimized capacity and availability<br />
with a common set of advanced storage<br />
features, including thin provisioning<br />
to maximize storage utilization, as<br />
well as <strong>net</strong>work-based replication for<br />
failover to remote sites.<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 7<br />
Brought to you by HP
VIEWPOINT c h a r l e s m o k<br />
In search of social media gurus<br />
Every now and then, a hot new job title emerges. The<br />
latest is “social media director.”<br />
But the most curious thing about the nature of this<br />
job is that corporations usually don’t really know what social<br />
media are, or what they mean to them, let alone knowing how<br />
to hire the right person for the job. Or then again, this may not<br />
be such a rare thing in the corporate world.<br />
Yes, companies big and small are ‘embracing’ social media.<br />
But the way firms are adopting the new media doesn’t seem<br />
too different from ten years or so ago, when they felt compelled<br />
to set up corporate Web sites (which inevitably turned<br />
into brochureware) just because they “had to have them.”<br />
Your online corporate image should<br />
have little to do with what you want to<br />
sell them today or the next day, but what<br />
the online public sees in your brand<br />
Some companies or institutions even thought that social<br />
media mean Facebook. Even our HKSAR Chief Executive’s<br />
Office recently put out an ad for Facebook administrators—<br />
yet another classic case of hiring someone to execute something<br />
before, not after, the organization knows what that<br />
something is, or have set up a strategy of engagement. Lured<br />
by generous government salary-levels, hundreds of self-proclaimed<br />
Facebook gurus applied to our social media-naive<br />
bureaucrats.<br />
Social media shouldn’t be just marketing driven<br />
For those companies who are adopting social media now,<br />
most are using them for sales, marketing and promotion. Naturally,<br />
companies with consumer-oriented products and services<br />
are early adopters, because they have a genuine need to<br />
connect with their buyers and customers in a way that is much<br />
cheaper than placing advertisements in print, TV or outdoor<br />
display. They learn about search engine optimization, and marketing<br />
departments sometimes organize “bloggers parties” to<br />
try to locate and engage online opinion leaders.<br />
These are just the basics. What about deeper consideration<br />
and planning on issues like branding, corporate communica-<br />
tions, image building, even risk management Never forget<br />
that social media is a double-edged sword: you don’t have to<br />
do anything for it to come back and haunt you in ways you<br />
never thought of. For example, any disgruntled customer or<br />
nosy bystander can upload a YouTube video with a negative<br />
experience related to your company. By tomorrow morning it<br />
may have “gone viral” and hit headlines, giving you problems<br />
in both new and old media.<br />
So my advice is: think long term. Instead of focusing on<br />
short-term promotional campaigns, think about building your<br />
online corporate image in the social media space.<br />
Of course, that means a lot more than setting up a Facebook<br />
page and trying to get as many people to “like” it as you can.<br />
Your online corporate image should have little to do with what<br />
you want to sell them today or the next day, but what the online<br />
public sees in your brand. This is important not only because<br />
they may be buying your products and services tomorrow, but<br />
because they may turn out to be your best allies and defenders<br />
if things turn sour online for your company or brand—especially<br />
when those “things” are out of your control.<br />
Define your social media image<br />
Engage your current and future customers in improving your<br />
products and services, and even more importantly, making<br />
your brand and image a likeable one in the online space. In<br />
today’s online world, this may mean more than the quality of<br />
what you sell, but the values you represent, and the benefits<br />
you are seen to provide to society. This philosophy may make<br />
even those who may not become your customers regard your<br />
brand in a positive light.<br />
How to take the first step Instead of<br />
simply hiring someone for the mundane<br />
work of placing and answering messages<br />
on Facebook, think carefully about<br />
your objectives—why and how—and<br />
who your target audiences should be,<br />
before deciding on a course of action.<br />
This leads me to think, instead of hiring<br />
their own social media directors before<br />
knowing what social media actually is<br />
or can do, corporations are likely better<br />
off consulting a social media doctor<br />
first, for a body check. Now, if only<br />
these good doctors were easy to find!3<br />
Charles Mok<br />
has been in the<br />
<strong>IT</strong> industry for<br />
almost 20 years,<br />
and is active in a<br />
number of advisory<br />
committees and<br />
statutory bodies.<br />
8 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 9
BIZPEOPLE<br />
Networks scrutiny is the only<br />
real security<br />
Dr Prescott Winter previously served as CIO and CTO of the USA’s National<br />
Security Agency and brings almost three decades of combined experience in<br />
the public sector to new role as CTO, Public Sector, ArcSight. Winter’s brief<br />
is to drive strategic product initiatives and industry relationships concerning<br />
public sector cybersecurity requirements in the US and internationally, as well<br />
as facilitate collaboration between the public and private sector on the ever<br />
changing global cyberthreat landscape<br />
By Stefan Hammond<br />
Prescott Winter from ArcSight<br />
CWHK: <strong>IT</strong> leaders in <strong>Hong</strong> <strong>Kong</strong> know<br />
they must maintain good security, but<br />
may not know how to best go about it.<br />
In general terms, what advice do you<br />
have<br />
Prescott Winter: There are two main<br />
areas I want to touch on for private<br />
companies, although when you get to<br />
government agencies there are some<br />
other ingredients in the mix. But for<br />
most SMBs and enterprises, there are<br />
two main principles.<br />
Firstly, the environment is much more<br />
threatening now than it has been in the<br />
past. There are many factors in information<br />
systems today that make it harder to<br />
protect what you’ve got. Wireless communications:<br />
iPhones and BlackBerrys<br />
attached to your computing environment.<br />
So if you still have the idea of a<br />
“perimeter defense line,” you’ve already<br />
got people pole-vaulting over the top of<br />
the “fence.”<br />
There are also reasons you want to<br />
share information: you have partners<br />
and other allies in whatever you’re<br />
working on. And you want them in and<br />
out of your <strong>net</strong>work, as the information<br />
is there for them to use. Because of this,<br />
there are vulnerabilities that can never<br />
be 100% erased, so you’re always at risk<br />
of intrusion. You cannot wall yourself<br />
off—you must assume that the other<br />
guys are going to get in, and in fact are<br />
probably already in.<br />
CWHK: Which metrics affect this<br />
equation<br />
PW: The bigger the corporation, the<br />
more strategic the information, and<br />
the more likely someone else wants a<br />
unique piece of strategic information.<br />
You’re likelier to have more persistent,<br />
well schooled attackers. So for a small<br />
company, that’s less of an issue than it is<br />
for a larger company, and definitely less<br />
than for a government entity.<br />
But a small company that is developing<br />
intellectual property or being very<br />
creative in how it develops markets, anything<br />
with potential for growth or importance,<br />
is automatically a more interesting<br />
target for somebody using that same basic<br />
strategy—they’ve got the goods, and<br />
someone wants that IP. The better they<br />
are, the more power they have, the more<br />
unique they are, the better a target they<br />
are.<br />
If you’re a bank and you’re concerned<br />
about cybertheft and you do a really good<br />
job of buttoning up your bank, the odds<br />
are good that the criminals will look for<br />
a bank that’s not so well protected. But<br />
if you have strategic, unique informa-<br />
tion, then there’s only one place for the<br />
adversaries to come in and get it, and<br />
that’s inside your walls. So you should<br />
assume that you have well organized,<br />
well resourced adversaries who have the<br />
patience and the time to get inside your<br />
walls. Your strategic approach should<br />
be that they’re going to get in, and when<br />
they do, and then determine who’s in<br />
there, what they’re doing, how bad it is,<br />
and what you have to do to fix it before<br />
the damage exceeds levels that you’ve<br />
defined as excessive.<br />
I think the perimeter defense mindset<br />
is passé. If you think that you can erect<br />
firewalls and intrusion detection systems<br />
and somehow get by on that, you’re going<br />
to be disappointed in the end. Sooner<br />
rather than later, in all likelihood.<br />
CWHK: So what should businesses do to<br />
protect themselves<br />
PW: Change your mindset and look at<br />
different ways to approach the problem.<br />
This is the first thing I talk about at the<br />
government-level: understand what<br />
we’re dealing with here, because if they<br />
don’t get that right, then most of other<br />
things I would suggest are irrelevant.<br />
It isn’t going to get any better. For example,<br />
in 2006 the Pentagon had six million<br />
hits annually: the DOD (US Depart-<br />
10 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
ment of Defense) is probably the biggest<br />
enterprise <strong>net</strong>work system out there. It’s<br />
also the most heavily attacked, as far as<br />
we know. In 2008, that six million had<br />
grown to about 350-360 million. And a<br />
recent article had a senior Pentagon official<br />
commenting that we’re now up to<br />
six million hits a day. So the amount of<br />
increase in hostile activity is extremely<br />
rapid.<br />
CWHK: Once you realize that you need<br />
to change your perimeter mindset, what<br />
do you do<br />
PW: The prescription is straightforward.<br />
Flashy terms like “cyberwar” and<br />
“cyberdefense” are dramatic, but what<br />
works is like the basic blocking-andtackling<br />
that wins games in American<br />
football, or the passing and ball control<br />
that wins soccer games.<br />
The fundamental issue is to know<br />
what’s going on in your <strong>net</strong>works, and<br />
that starts with careful instrumentation<br />
of your systems and a careful approach<br />
to managing identity and access. There<br />
are lots of good techniques to accomplish<br />
this, but the point is you need to<br />
know who’s in your <strong>net</strong>works, and what<br />
they’re doing—meaning which computer<br />
systems they’re using to get access to<br />
which pieces of information. Again, you<br />
acquire this with careful instrumentation<br />
that gives you a clear and manageable<br />
form.<br />
A good place to start is with a set of<br />
20 recommended controls by the SANS<br />
Institute (http://www.sans.org/criticalsecurity-controls/interactive.php),<br />
which<br />
is a Stateside nonprofit organization that<br />
works with many of the best experts. The<br />
idea is to begin to learn what’s going on<br />
in your <strong>net</strong>work, and start to establish<br />
definable standards for <strong>net</strong>work hygiene<br />
and management. You need basic instrumentation<br />
in place and get these devices<br />
to generate logs that record every<br />
time someone logs on, every time a file<br />
is opened or closed, every time a message<br />
is sent, every time a ping comes<br />
in and bangs into one of your perimeter<br />
systems—every event that occurs in<br />
your <strong>net</strong>work space generates a record,<br />
a fingerprint. Some are big noisy fingerprints<br />
and some are tiny fingerprints but<br />
you want to gather them all, use a process<br />
that filters out the less useful ones<br />
and correlates the more useful ones, and<br />
correlates the more useful ones, and tells<br />
If you still have the idea of a “perimeter defense line,”<br />
you’ve already got people pole-vaulting over the top of<br />
the “fence”<br />
you what’s going on.<br />
CWHK: It sounds like identity management<br />
is a critical part of this ecosystem<br />
you’re describing.<br />
PW: That’s exactly the right word: ecosystem.<br />
And identity management is absolutely<br />
fundamental.<br />
Even enterprises that have significant<br />
resources to do this well, and use<br />
systems like Active Directory or an<br />
equivalent, with considerable skill,<br />
still in many cases don’t aggregate and<br />
correlate all the pieces of information<br />
that the system generates. Your IAM<br />
(Identity Access Management) system<br />
should tell you who all your users are,<br />
and the relevant authorities, privileges<br />
and responsibilities are for each user.<br />
So if I have someone at a bank who’s<br />
on the financial analysis side, and he<br />
suddenly turns up looking at the HR<br />
records, someone needs to be looking<br />
at this quickly. Conversely, if I’ve got<br />
someone on the HR side, and he’s looking<br />
at the financial data and moving<br />
money around, that’s a bad mismatch<br />
for the job description.<br />
To control people’s use of data, you<br />
must control the attributes of the people.<br />
The starting point is to use any one of<br />
several good commercial systems that<br />
instrument the identities of the users in<br />
your system, and to ensure that you have<br />
an adequate level of detail to define their<br />
attributes and their privileges.<br />
The same principles apply to the information.<br />
If you have a firm with different<br />
classes of information, some of<br />
them are more important for the long<br />
term future of your organization than<br />
others. And some of your users have<br />
higher levels of access, which makes<br />
them high-risk users, as they have access<br />
to lots of things. Your system administrators<br />
are people who you quite<br />
frankly have to monitor more carefully,<br />
not because you necessarily distrust<br />
those people, but because abuse of that<br />
special use of access privileges would<br />
be a disaster, as the system administrator<br />
has the “keys” to get into anything<br />
in your computer environment.<br />
CWHK: Yes, just look at the case of Terry<br />
Childs in San Francisco.<br />
PW: Absolutely. You must be mindful of<br />
those individuals with special privileges.<br />
So if you don’t have the assets to look<br />
at every individual in your organization,<br />
at least develop a careful taxonomy and<br />
priority scheme, to show you which individuals<br />
have the elevated privileges that<br />
require the most control, because those<br />
are the ones who can cause you the most<br />
damage if they break loose. 3<br />
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 11
CHINAWATCH<br />
Chinese outsourcer seeks US workers with IQ of 125 and up<br />
Bleum sets IQ threshold<br />
By Patrick Thibodeau, Computerworld (US)<br />
A<br />
Chinese <strong>IT</strong> outsourcing company<br />
that has started hiring new<br />
US computer science graduates<br />
to work in Shanghai requires prospective<br />
job candidates to demonstrate an IQ of<br />
125 or above on a test it administers to<br />
sort out job applicants.<br />
In doing so, Bleum Inc is following a<br />
hiring practice it applies to college recruits<br />
in China. But a new Chinese college<br />
graduate must score an IQ of 140 on<br />
the company’s test.<br />
An IQ test is the first screen for any US<br />
or Chinese applicant.<br />
The lower IQ threshold for new US<br />
graduates reflects the fact that the pool<br />
of US talent available to the company is<br />
smaller than the pool of Chinese talent,<br />
Bleum said.<br />
In China, Bleum receives thousands of<br />
applications weekly,<br />
said CEO Eric Rongley.<br />
Rongley is a US<br />
citizen who founded<br />
Bleum in 2001; his<br />
career prior to that<br />
included stints working<br />
in offshore development<br />
in India and<br />
later in China.<br />
The company employs<br />
about 1,000 and<br />
hires about 1% or less<br />
of the people who apply<br />
for jobs there. “It<br />
is much harder to get<br />
into Bleum than it is<br />
to Harvard,” Rongley<br />
said.<br />
Shanghai-based<br />
Bleum has been recruiting<br />
new computer<br />
engineering graduates in the Atlanta,<br />
Chicago and Denver areas. If a student<br />
meets the minimum requirement on an<br />
IQ test, he then take a skills test, similar<br />
to the hiring process Bleum follows in<br />
China.<br />
IQ tests not exact science<br />
Bleum has already hired its first US<br />
recruits—a group of five people who left<br />
for Shanghai this month, said Rongley.<br />
They will work in China for a year and<br />
then return to the US to work.<br />
Many employers do measure intelligence<br />
to cull candidates from pools of<br />
applicants, but they typically call the exams<br />
aptitude tests, said Dennis Garlick,<br />
a post-doctoral researcher at the University<br />
of California, Los Angeles.<br />
An IQ of 140 is extremely high, representing<br />
about the top 1% of the population,<br />
said Garlick. But he said that even<br />
though some studies have shown a correlation<br />
between IQ and job performance,<br />
IQ is a “crude assessment tool” when it<br />
comes to sorting out job applicants.<br />
IQ tests tend be inaccurate at the upper<br />
end of the scale as the questions become<br />
more complex and it becomes “debatable<br />
what is a correct answer,” he said.<br />
IQ is also an indirect measure of job<br />
performance; a high IQ doesn’t necessarily<br />
mean a worker will achieve a certain<br />
level in job performance, “because<br />
an IQ test measures abstract reasoning in<br />
a general context, and on-the-job performance<br />
requires abstract reasoning in a<br />
specific context,” said Garlick.<br />
But for a person who does score high<br />
on an IQ test, “you can reasonably say<br />
that the person is likely to be able to<br />
understand typical abstract concepts as<br />
they are applied in business, understand<br />
instructions, follow them, and then generalize<br />
them in a new situation,” said<br />
Garlick.<br />
Mark Finocchario, national director<br />
for recruiting at the Eliassen Group, said<br />
that his <strong>IT</strong> staffing and recruiting firm<br />
in Wakefield, USA, administers technical<br />
skill tests, but not IQ tests, for some<br />
clients. The importance of the skill tests<br />
varies depending on the client. Most clients<br />
view the skill tests as academic and<br />
rely mostly his firm’s assessment of a<br />
candidate’s experience. “Experience is<br />
huge,” he said.<br />
For its own employees, Eliassen uses<br />
what it calls an EQ test, which measures<br />
how an employee may operate in<br />
continued on page 22 4<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
12 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
Sponsored Feature<br />
Total Solution for Ultra Productivity with High Image Quality<br />
Enterprise users can grow their business<br />
with business they already have.<br />
They can transform the monthly bills and<br />
statements they currently produce into<br />
something special with Xerox 650/1300 TM<br />
Continuous Feed Printer. Better imaging<br />
and output quality create better, more effective<br />
communications. It is an easy and<br />
cost-effective way to increase sales and<br />
revenue and accelerate payment and collection<br />
for a wide range of industries.<br />
Evolving and Growing your Business via Transformation<br />
Transactional, TransPromo and<br />
direct mail<br />
Xerox 650/1300 Continuous Feed<br />
Printer makes it easy to quickly produce<br />
high-volume, time-critical applications.<br />
• Boost response rates by adding highquality<br />
data-driven graphics to bills<br />
and statements.<br />
• Save print costs and reduce postal<br />
fees by transforming standard transactional<br />
documents into TransPromo<br />
communications. Turn those communications<br />
into cost-effective sales<br />
tools by adding personalized graphics,<br />
promotional offers and marketing<br />
content.<br />
• Implement cost-effective marketing<br />
campaigns for your customers with<br />
targeted and customized direct mail<br />
pieces leveraging new and exciting<br />
media.<br />
1<br />
Input from roll<br />
2<br />
Box-fed<br />
3<br />
Pinfed or pinless feed<br />
4<br />
Fine particle toner<br />
7<br />
Onboard controller<br />
10<br />
Internal stacker<br />
5<br />
Xerographic LED imaging<br />
8<br />
Graphic user interface (GUI)<br />
11<br />
Output to inline finishing<br />
6<br />
Flash-fusing module<br />
9<br />
Developer housing<br />
Quality<br />
• 1200 x 600 dpi resolution and<br />
ImageSmooth Technology deliver<br />
distinctive image quality (exceptional<br />
halftones and solid area density) and<br />
high quality at maximum speed.<br />
• Fine particle toner with xerographic<br />
LED imaging, are more consistent and<br />
precise in size for better edge acuity<br />
(especially for small font – e.g. traditional<br />
Chinese).<br />
Reliability<br />
• Xerox on-board controller enables<br />
native IPDS printing, ensuring fast<br />
process to print for your production<br />
volumes. Ultra high speed: 74,000<br />
duplex A4 image per hour.<br />
www.cw.com.hk<br />
Innovative Technology behind the System<br />
The system is backed by state-of-the-art printing technology —dry toner,<br />
xerographic imaging and flash-fusing technology.<br />
• Non-contact Flash-Fusing Technology<br />
– reduce paper shrinkage and<br />
retains proper paper moisture levels,<br />
improving performance and reliability<br />
of in-line, near-line, and offline postprocessing<br />
devices like mail inserters<br />
or book binding equipment with the<br />
flat output sheets.<br />
• The four kilo toner can be changed on<br />
the fly to boost your productivity and<br />
uptime.<br />
Flash emission<br />
Flash lamp<br />
Flexibility<br />
• Print on wide range of paper stocks,<br />
both pinless and pinfed, of varying<br />
weights and thicknesses.<br />
• Wide print web enables flexible imposition<br />
so you can use media more effi-<br />
- Self mailers<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 23<br />
ciently, save costs, and reduce waste<br />
• Wide variety of applications, add value<br />
and deliver better results for more<br />
business opportunities<br />
- Transactional Promotional<br />
applications<br />
- Emerging Applications - e.g. RFID<br />
logistics tracking application<br />
- Plastic Cards<br />
- Peel off labels and tags<br />
Form<br />
Reflector<br />
Toner
COVERSTORY<br />
Why can’t <strong>Hong</strong> <strong>Kong</strong><br />
lead the region in <strong>IT</strong><br />
<strong>innovation</strong><br />
<strong>Hong</strong> <strong>Kong</strong> is touted as a “<strong>hub</strong>” for everything from wine to<br />
logistics—what about <strong>IT</strong> <strong>innovation</strong> By Stefan Hammond<br />
Bottom Line<br />
• Public and private sectors,<br />
education and even<br />
parenting—all come into<br />
play<br />
• <strong>Hong</strong> <strong>Kong</strong>’s infrastructure<br />
is a major strength, but<br />
more needs to be added to<br />
the mix<br />
• The OGCIO provides<br />
facilities and incentives,<br />
but is it enough<br />
The light bulb goes on and an idea<br />
fires in the brain of a young, techsavvy<br />
<strong>Hong</strong> <strong>Kong</strong>er. Suddenly, the<br />
catalyst is clear—and a new ICT-development<br />
begins to take shape. But where does<br />
the youngster find the resources to make<br />
his or her dream come true<br />
<strong>Hong</strong> <strong>Kong</strong> remains world-class. Our<br />
infrastructure offers Inter<strong>net</strong> and mobile telephony<br />
that most countries outside Scandinavia<br />
can’t touch. Mobile phone pe<strong>net</strong>ration<br />
is well in excess of 100%, and many of<br />
those phones handle 3G and data as well.<br />
The rule of law means that contracts signed<br />
here guarantee ownership, including that of<br />
intellectual property. With a chip-enabled<br />
<strong>Hong</strong> <strong>Kong</strong> ID card you can pop through<br />
our excellent e-channels in less than a min-<br />
ute—a legal, recorded entry without the aid<br />
of an immigration officer. While most of<br />
Asia fumbles with high-tech, <strong>Hong</strong> <strong>Kong</strong><br />
remains an island of evolution.<br />
But to find documentation of our successes,<br />
you need to read Teresa Leung’s<br />
excellent IndustryProfile articles in the pages<br />
of Computerworld <strong>Hong</strong> <strong>Kong</strong>. Most of<br />
our young stars in the <strong>IT</strong> sector are typical<br />
<strong>Hong</strong> <strong>Kong</strong> businessmen and businesswomen:<br />
working as SMBs, but often far<br />
surpassing their modest means. Together,<br />
they form a mosaic of <strong>IT</strong> success. But do<br />
they form a “<strong>hub</strong>”<br />
Forget “the new Silicon Valley”<br />
I spent many years in the San Francisco<br />
Bay/Silicon Valley area. Even pre-Inter<strong>net</strong>,<br />
the place was tech-centric like no other. Every<br />
so often someone will declare that Bangalore<br />
or Beijing or Cyberjaya will become<br />
14 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
“the new Silicon Valley,” but in my view, it<br />
will never happen. The creation of Google,<br />
Yahoo and Napster came about because of<br />
the unique inquisitiveness and creativity<br />
of university students, usually at Stanford,<br />
and invariably to serve their own interests.<br />
Zuckerberg of Facebook fame is unusual<br />
only in that he came from the East Coast.<br />
That doesn’t mean other areas aren’t viable.<br />
Innovation will occur, unique business<br />
models will be built, and existing models<br />
leveraged. The key is to localize, focus on<br />
niche markets and operate within a nurturing<br />
environment. The concept of “incubation”<br />
is a good one, but it needs venture<br />
capital to keep it alive.<br />
But what else needs to be done I asked a<br />
number of <strong>Hong</strong> <strong>Kong</strong>’s movers-and-shakers<br />
in the <strong>IT</strong> world if <strong>Hong</strong> <strong>Kong</strong> could be<br />
an <strong>IT</strong> <strong>innovation</strong> <strong>hub</strong>, and what would be<br />
needed to make it so.<br />
Natural strength<br />
Joe Locandro, director of group <strong>IT</strong> for<br />
CLP, believes there are four main areas of<br />
built-in advantages. “In the digital world,<br />
we will have more future consumers,” said<br />
Locandro. “<strong>Hong</strong> <strong>Kong</strong> has high inter<strong>net</strong><br />
pe<strong>net</strong>ration, and a lot of <strong>Hong</strong> <strong>Kong</strong> services<br />
are done via the Net. Our high broadband<br />
pe<strong>net</strong>ration on a per capita basis gives<br />
us ability to innovate using the Inter<strong>net</strong>.”<br />
Secondly, he said, “<strong>Hong</strong> <strong>Kong</strong> has one<br />
of the highest mobile pe<strong>net</strong>ration rates in<br />
the world. If future tech is going the mobile<br />
route, we have natural strength there.”<br />
Thirdly, “<strong>Hong</strong> <strong>Kong</strong> as part of China<br />
has a quality brand—what’s invented here<br />
can be deployed in China through CEPA,<br />
said Locandro. “That’s another natural advantage.”<br />
Finally, Locandro pointed to the international<br />
rule of law in <strong>Hong</strong> <strong>Kong</strong>, “CEPA<br />
allows us to deploy innovative technology<br />
on a favored-trading status,” he said.<br />
continued on page 16 4<br />
Science Park: <strong>Hong</strong> <strong>Kong</strong>’s incubator<br />
By Teresa Leung<br />
As real estate is expensive in <strong>Hong</strong> <strong>Kong</strong>, the government has set up<br />
a statutory body—the <strong>Hong</strong> <strong>Kong</strong> Science and Technology Parks<br />
(HKSTPC)—to provide infrastructure and services to enable <strong>Hong</strong> <strong>Kong</strong><br />
to become a world-class <strong>hub</strong> on its chosen technologies, says the HKSTPC<br />
Web site.<br />
The science park offers facilities and support services such as an IC (integrated<br />
circuit) design center, an IC development support center, a materials<br />
analysis laboratory, a wireless communications test laboratory, an intellectual<br />
property servicing center, a solar energy technology support center, and a<br />
biotech center.<br />
To help local tech startups with huge potentials but having limited resources,<br />
the science park has run a three-year incubation program since 1992. Now the<br />
program has two streams—technology and design. The cumulative number of<br />
tech graduate companies as of 2010 is estimated to reach 215, according to<br />
the park’s Web site.<br />
Inside technology, <strong>IT</strong> and telecoms is one of the areas, with the other four<br />
being<br />
biotechnology, electronics, green technology, and precision engineering. In<br />
the year 2009-2010, there are 86 incubatees in the technology stream of the<br />
program.<br />
All incubatees are provided with ready-to-use offices, which are available<br />
for up to 12 months rent-free and for a further two years or three years at a<br />
reduced rental. These startups can also use free services including professional<br />
reception services, meeting rooms, pantry, and a full range of office equipment<br />
and telecommunications facilities. The incubatees also have access to a<br />
range of assistance programs including those related to management, technical<br />
know-how, promotion and development, and business matching.<br />
“The <strong>Hong</strong> <strong>Kong</strong> Science and Technology Parks Corporation (HKSTPC) was<br />
established in May 2001 to offer one-stop infrastructural support services to<br />
technology-based companies and activities, including the nurturing of technology-based<br />
start-up companies through its incubation program,” said the<br />
OGCIO in a statement. “The first two phases of <strong>Hong</strong> <strong>Kong</strong> Science Park were<br />
completed in 2004 and 2008 at the cost of HK$2.9 billion and HK$3.8 billion<br />
respectively. The five clusters developed in the <strong>Hong</strong> <strong>Kong</strong> Science Park are<br />
information technology and telecommunications, electronics, biotechnology,<br />
precision engineering and green technology (including renewable energy and<br />
environmental technologies).”<br />
Future progress was “decided earlier this year to proceed with the development<br />
of <strong>Hong</strong> <strong>Kong</strong> Science Park Phase 3 at an estimated development cost<br />
of HK$4.9 billion,” said the OGCIO, adding that construction will commence in<br />
mid 2011 and “the first batch of buildings in Phase 3 will be ready in late 2013<br />
while the whole phase will be completed in 2016.”<br />
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 15
COVERSTORY<br />
4 continued from page 15<br />
Driving forces<br />
“I call these favorable factors some of<br />
the necessary ingredients,” said Locandro.<br />
“But to complete this recipe, you must add<br />
<strong>innovation</strong> culture and government support.”<br />
Locandro explained that the HKSAR<br />
government “has <strong>IT</strong> <strong>innovation</strong> as one of<br />
its six pillars, and funds earmarked for <strong>innovation</strong><br />
through the HKPC, and an additional<br />
benefit would be to use tax incentives<br />
to encourage corporations to invest in commercially<br />
deployable innovative technology.<br />
“<br />
Locandro added that another area the<br />
government could consider is “specific<br />
technology export-grants for <strong>Hong</strong> <strong>Kong</strong><br />
companies to deploy in China or other parts<br />
of Asia for long-term economic gain.”<br />
“A linkage between the academic and<br />
private sectors is desirable [and] further<br />
strengthening those relationships would be<br />
an advantage,” Locandro said. “We want<br />
talent development which means we need<br />
to harness the entrepreneurial spirit of HKers<br />
with <strong>IT</strong> skills at a young age. It’s in the<br />
DNA, so combining that entrepreneurial<br />
spirit with a hunger for <strong>IT</strong> at a college or<br />
even high-school level is something I’d like<br />
to see.”<br />
Locandro urged organizations like the<br />
HK branches of the American, Australian<br />
and British Chambers of Commerce, as<br />
well as the <strong>Hong</strong> <strong>Kong</strong> Computer Society,<br />
to help facilitate this process. “There’s a lot<br />
of opportunity for <strong>innovation</strong> in the<br />
SMB segment,” he said.<br />
Web <strong>innovation</strong><br />
platforms<br />
Locandro mentioned a US<br />
company whose Website,<br />
brightidea.com, is a “platform<br />
that allows <strong>innovation</strong>.<br />
We use it internally<br />
Public sector support<br />
One of the HKSAR’s perennial strengths<br />
is that public and private sectors dovetail.<br />
Some say that the <strong>Hong</strong> <strong>Kong</strong> government<br />
doesn’t impede the progress of the public<br />
sector, but most agree that a “laissez-faire”<br />
approach has proven essential to <strong>Hong</strong><br />
<strong>Kong</strong>’s economic rise over the decades.<br />
We do have governmental tech assisto<br />
generate ideas, and have our own <strong>IT</strong><br />
<strong>innovation</strong> center where we show internal<br />
business and companies within <strong>Hong</strong> <strong>Kong</strong><br />
our new ideas, such as digital-pen technology.”<br />
But Locandro is determined that CLP<br />
evolve beyond Web platforms and new<br />
products. “Innovation is one of our five <strong>IT</strong><br />
core values,” he said, “our <strong>IT</strong> employees<br />
are encouraged to demonstrate <strong>innovation</strong>.<br />
We also want to use tech to improve our<br />
work/life balance—it’s part of our <strong>IT</strong> human<br />
capital management strategy: career<br />
development.”<br />
“Together with China’s scale and <strong>Hong</strong><br />
<strong>Kong</strong>’s entrepreneurial spirit, <strong>Hong</strong> <strong>Kong</strong><br />
can compete on an <strong>innovation</strong> value proposition.<br />
It’s about combining the ingredients<br />
with the mindset and the talent. And although<br />
results won’t appear overnight but<br />
the medium to long term results should be<br />
sustainable.”<br />
Innovative <strong>IT</strong> usage<br />
“The strength of HK people in everyday<br />
usage of <strong>IT</strong>,” said Agnes Mak, former head<br />
of the <strong>Hong</strong> <strong>Kong</strong> Computer Society and<br />
executive director of <strong>IT</strong> consultancy<br />
i Principle. But she cautioned that using <strong>IT</strong><br />
doesn’t mean you can develop tech products—”a<br />
lot of people think they are <strong>IT</strong> professionals,<br />
but just because you can drive a<br />
car, doesn’t mean you can design it.”<br />
“<strong>Hong</strong> <strong>Kong</strong>’s <strong>IT</strong> users are good at understanding<br />
and using applications in everyday<br />
systems, like paying bills or even<br />
income tax at ATMs—that’s innovative<br />
use of <strong>IT</strong>,” said Mak. This <strong>innovation</strong><br />
has been part of <strong>Hong</strong> <strong>Kong</strong> culture<br />
for some time, but it doesn’t<br />
mean <strong>Hong</strong> <strong>Kong</strong> is strong in<br />
R&D.”<br />
Mak from i Principle: You<br />
need fundamental training<br />
to create <strong>innovation</strong> as an<br />
end-product<br />
Educational and parental help<br />
“In <strong>Hong</strong> <strong>Kong</strong>, students don’t learn only<br />
from teachers, but [also] have the Inter<strong>net</strong>,”<br />
said Mak. “Still, they need their parents and<br />
other mentors to make sure they’re getting<br />
the correct information.”<br />
Mak pointed out that “the way of teaching<br />
is changing now—before the dotcom<br />
boom, a lot of students wanted to get into<br />
<strong>IT</strong>, but after the dotcom bust, parents discouraged<br />
<strong>IT</strong> study. <strong>Hong</strong> <strong>Kong</strong>ers are too<br />
short-sighted: we must look at an individual’s<br />
skills and not only the latest view of the<br />
job market. You need fundamental training<br />
to create <strong>innovation</strong> as an end-product.”<br />
Building an <strong>innovation</strong> culture<br />
“Innovation is boosted by exposure to<br />
different cultures, and the Inter<strong>net</strong> helps<br />
here,” said Mak. “But you can’t force <strong>innovation</strong>,<br />
you have to look at the education<br />
system: quality of teachers and curriculum.<br />
Rote learning does not lead to <strong>innovation</strong>—<br />
if you find potential within a student, you<br />
give them exposure in the areas that interest<br />
them.”<br />
But Mak insisted that parental guidance<br />
is an important part of encouraging creativity<br />
in the technology realm and elsewhere.<br />
“Innovation can be encouraged through the<br />
parents’ mindset,” said Mak. “Parents must<br />
take responsibility.”<br />
Mak echoed Locandro’s view that <strong>Hong</strong><br />
<strong>Kong</strong>’s strong <strong>IT</strong> infrastructure is an essential<br />
element. “World-class <strong>IT</strong> used daily,<br />
this is our strength—we should continue to<br />
encourage this,” she said.<br />
16 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
CLP’s Locandro: For <strong>Hong</strong> <strong>Kong</strong>, <strong>innovation</strong><br />
should bring shareholder value<br />
Rote learning does not lead to <strong>innovation</strong>—if you find<br />
potential within a student, you give them exposure in<br />
the areas that interest them<br />
— Agnes Mak, i Principle<br />
tance—the OGCIO, which oversees government<br />
assistance for <strong>IT</strong> projects. “<strong>Hong</strong><br />
<strong>Kong</strong> is committed to developing itself into<br />
a <strong>hub</strong> for <strong>innovation</strong>, cooperation and trade<br />
in information & communications technology<br />
(ICT). ‘Promoting Advanced Technology<br />
and Innovation’ and ‘Developing <strong>Hong</strong><br />
<strong>Kong</strong> as a <strong>hub</strong> for technological cooperation<br />
and trade’ are two of the key action<br />
areas in the Digital 21 Strategy,” said the<br />
OGCIO in a statement. And the tech sector<br />
also receives overall government support,<br />
continued the OGCIO: “In June 2009, the<br />
identification of the Innovation and Technology<br />
sector as one of the six economic<br />
pillars where <strong>Hong</strong> <strong>Kong</strong> has good potential<br />
for further development as the priority<br />
areas by the Task Force on Economic Challenges<br />
commissioned by the Chief Executive<br />
helped further increase the momentum<br />
of <strong>Hong</strong> <strong>Kong</strong> developing into an <strong>innovation</strong><br />
and technology <strong>hub</strong>.”<br />
But Samson Tam, Legislative Councilor<br />
for <strong>IT</strong>, has doubts about the government’s<br />
commitment to our tech sector. “In<br />
2007, Digital 21 clearly stated that one of<br />
the <strong>Hong</strong> <strong>Kong</strong>’s missions is to be a <strong>hub</strong><br />
for technological cooperation and trade,”<br />
said Tam, “and it was also mentioned in<br />
the CE’s Policy Address that <strong>Hong</strong> <strong>Kong</strong><br />
must move towards becoming a knowledge<br />
economy. In the past two years, the<br />
HKSAR government has started the engine<br />
by establishing the Create <strong>Hong</strong> <strong>Kong</strong> and<br />
the HK$300 million CreateSmart Initiative,<br />
setting up an R&D Cash Rebate Scheme<br />
and also providing subsidy for Inter<strong>net</strong> access<br />
charges for students in need.”<br />
“However,” cautioned Tam, “there’re no<br />
outstanding results in the ICT <strong>innovation</strong> in<br />
the past five years compared to neighborhood<br />
countries, and <strong>Hong</strong> <strong>Kong</strong> may even<br />
be falling behind.”<br />
Are we falling behind<br />
Agnes Mak, who in her role with the<br />
HKCS ensured <strong>Hong</strong> <strong>Kong</strong> firms were<br />
represented at APICTA (The Asia Pacific<br />
ICT Awards, http://www.apicta.com/) has<br />
seen changes during the ten years of API-<br />
CTA’s existence. “<strong>Hong</strong> <strong>Kong</strong> is still in<br />
the forefront, and years ago it was always<br />
<strong>Hong</strong> <strong>Kong</strong>/Singapore/Australia [winning<br />
awards at APICTA],” she said, “but now<br />
other ASEAN countries, with their creative<br />
students and overall confidence, are catching<br />
up. Even from Sri Lanka and Pakistan,<br />
we’re seeing strong entries nowadays.<br />
Their presentations are strong.”<br />
The OGCIO is also worried about <strong>Hong</strong><br />
<strong>Kong</strong>’s ability to maintain its competitive<br />
edge. “Under the Digital 21 Strategy Advisory<br />
Committee, the Government in 2009<br />
set up a Task Force on Industry Facilitation<br />
which comprises mainly of industry members<br />
to advise on relevant strategies and initiatives”<br />
said the OGCIO. “The Task Force<br />
identified difficulties and barriers facing<br />
<strong>Hong</strong> <strong>Kong</strong>, and analyzed <strong>Hong</strong> <strong>Kong</strong>’s<br />
unique strengths and the opportunities that<br />
arise from them.”<br />
The investigative task force concluded<br />
that “the major difficulty encountered by<br />
the local ICT industry was the relatively<br />
small size of the local market.” But they<br />
also identified other barriers:<br />
• Difficulties in fund raising and inadequate<br />
awareness on Government<br />
funding schemes for some SMEs<br />
• Hard to attract multi-national companies<br />
to develop ICT products and<br />
services in <strong>Hong</strong> <strong>Kong</strong><br />
• Home-grown companies are too<br />
small to compete with large ones<br />
and keen competition from other<br />
economies<br />
• Difficulties in export such as the<br />
lack of global sales channels in<br />
SMEs and the lack of success cases<br />
of exportable software package<br />
• Risks of joint-ventures with other<br />
economies<br />
• High labor cost and decline in enrollments<br />
of undergraduates in engineering<br />
and ICT<br />
Although the last point directly echoes<br />
one of Mak’s concerns about <strong>Hong</strong> <strong>Kong</strong><br />
education, the governmental task force<br />
found some positive directions as well.<br />
<strong>Hong</strong> <strong>Kong</strong>’s strengths and<br />
opportunities<br />
“The Task Force’s analysis reveals that<br />
although the local ICT market is relatively<br />
continued on page 18 4<br />
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 17
COVERSTORY<br />
4 continued from page 17<br />
small in size, there are significant opportunities<br />
in regional and global markets. In<br />
particular the fast development of China<br />
has led to rapid growth both in demand for<br />
ICT products and services, and in capabilities<br />
which could be used to serve global<br />
customers.”<br />
The OGCIO added that as “an international<br />
trading <strong>hub</strong> with good financial facilities<br />
and having an ICT industry with<br />
good understanding of international market<br />
and business practice, <strong>Hong</strong> <strong>Kong</strong> is well<br />
positioned to facilitate the internationalization<br />
of the mainland software sector. <strong>Hong</strong><br />
<strong>Kong</strong>’s know-how, <strong>innovation</strong> and technology<br />
can add value to mainland ICT sectors<br />
and assist them to be marketed internationally.<br />
Equally, <strong>Hong</strong> <strong>Kong</strong> can add value to<br />
technology developed in third markets, so<br />
that it can be effectively deployed on the<br />
mainland and regionally.”<br />
In addition to Science Park (see sidebar,<br />
page 15), <strong>Hong</strong> <strong>Kong</strong> provides other<br />
facilities and incentives. Although Cyberport<br />
is primarily a private-sector facility,<br />
“the IncuTrain Centre of Cyberport helps<br />
commercialize creative ideas and incubate<br />
start-ups,” said the OGCIO. “The program<br />
provides incubatees with not only<br />
technological knowledge and techniques<br />
indispensable to the pursuit of a successful<br />
business in a knowledge-based highlycompetitive<br />
industry, but also all-round<br />
business support services, such as arrangement<br />
of business matching meetings to<br />
connect incubates with potential investors,<br />
participation opportunities in overseas and<br />
local trade shows and exhibitions to showcase<br />
incubatees’ products and services,<br />
media exposure opportunities to disseminate<br />
successful incubatees experience.”<br />
The OGCIO added that “as of July 2010,<br />
the total number of incubatees that have<br />
been admitted is 110, among them, 56 incubatees<br />
are going through the incubation<br />
program, and 40 have already successfully<br />
graduated.” In addition, said the OGCIO,<br />
“Cyberport initiated the Creative Micro<br />
Fund (CCMF) pilot scheme in 2009 to provide<br />
a seed fund to innovative projects or<br />
business concepts in digital entertainment,<br />
digital content and digital lifestyle.” So far,<br />
five grantees have been awarded funding<br />
sponsorship.<br />
Running to stay in place<br />
In the world of technology, you have to<br />
run fast just to stay in place, and Samson<br />
Tam argues that <strong>Hong</strong> <strong>Kong</strong> isn’t running<br />
fast enough. “There are three main reasons<br />
why <strong>Hong</strong> <strong>Kong</strong> is falling behind in<br />
this run,” said Tam. “Firstly, the Steering<br />
Committee on Innovation and Technology<br />
was not functioning well and hence<br />
no proper technology policy is established<br />
to take care of all aspects such as professional<br />
training, land and taxation incentive,<br />
investment and funding, etc. Hence, there<br />
are no synchronization among different<br />
departments.”<br />
“Secondly, the HK$500 million <strong>innovation</strong><br />
funding is not [being] effectively used.<br />
The application of such funding is too conservative<br />
and [with] no obvious strategy in<br />
using the funding, the end results are not<br />
significant,” he said.<br />
“Last but not least,” said Tam, “there<br />
are many difficulties for the ICT industry<br />
to get into China even [with] CEPA since<br />
the [HKSAR] government didn’t put [appropriate]<br />
actions in helping the industry to<br />
further develop in China.”<br />
The way forward<br />
Clearly, the tech landscape in <strong>Hong</strong><br />
<strong>Kong</strong> is convoluted and strategies are<br />
contentious. The OGCIO declares that<br />
“the government will continue its efforts<br />
in collaboration with the industry and<br />
academia to formulate and undertake initiatives<br />
to promote <strong>Hong</strong> <strong>Kong</strong> as a <strong>hub</strong><br />
for <strong>innovation</strong>, cooperation and trade in<br />
Legco’s Tam: The government should take to<br />
increase public awareness of the important<br />
role technology plays in moving <strong>Hong</strong> <strong>Kong</strong><br />
forward as an energetic knowledge economy<br />
ICT.” Their intentions are positive and<br />
proactive, and our current GCIO has<br />
proven his commitment to <strong>Hong</strong> <strong>Kong</strong><br />
technology.<br />
But Tam is more granular when he declares<br />
it’s “time to catch up: I believe that<br />
<strong>Hong</strong> <strong>Kong</strong> [can] be the <strong>hub</strong> for technological<br />
cooperation and trade in two tactics:<br />
first of all, setting up a Science and Technology<br />
Bureau to execute their technology<br />
policies. Moreover, the government should<br />
take to increase public awareness of the<br />
important role technology plays in moving<br />
<strong>Hong</strong> <strong>Kong</strong> forward as an energetic knowledge<br />
economy.”<br />
“Promoting the open <strong>innovation</strong> concept<br />
in <strong>Hong</strong> <strong>Kong</strong>—especially by using<br />
the Inter<strong>net</strong>,” said Tam, “would allow us<br />
to enhance regional cooperation and also<br />
achieve better cooperation in Shenzhen/<br />
<strong>Hong</strong> <strong>Kong</strong> <strong>innovation</strong> circles. Also, cooperation<br />
between Shenzhen/<strong>Hong</strong> <strong>Kong</strong><br />
and Guangdong/<strong>Hong</strong> <strong>Kong</strong> are important<br />
keys for <strong>Hong</strong> <strong>Kong</strong> to be the <strong>hub</strong> of technological<br />
cooperation and trade. It is worth<br />
[the effort] for the HKSAR government to<br />
work towards establishing <strong>Hong</strong> <strong>Kong</strong> as<br />
an <strong>innovation</strong> <strong>hub</strong> and hence moving <strong>Hong</strong><br />
<strong>Kong</strong> forward to be a knowledge-based<br />
economy.” 3<br />
18 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
Lower total cost<br />
boost productivity.<br />
Double utilization<br />
enhance SLAs.<br />
Back up frequently<br />
keep applications running.<br />
Cut power consumption<br />
manage data growth.<br />
Shrink your footprint<br />
grow your business.<br />
on.<br />
on.<br />
on.<br />
Thanks to AND, you’ll never have to settle for OR again.<br />
With solutions from NetApp, you can both increase storage efficiency and improve business<br />
performance. To get storage efficiency without compromise, visit <strong>net</strong>app.com/and.<br />
© 2010 NetApp. All rights reserved. Specifications are subject to change without notice. NetApp, the NetApp logo, and Go further, faster are trademarks or registered trademarks of<br />
NetApp, Inc. in the United States and/or other countries. All other brands or products are trademarks or registered trademarks of their respective holders and should be treated as such.<br />
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 19
Canon’s vision<br />
for greening the enterprise<br />
Canon’s commitment: social harmony, user convenience,<br />
environmental protection<br />
When businesses acquire multifunction<br />
machines for printing<br />
and digital communication,<br />
they now want a lot more than just efficient<br />
technology. Corporate stakeholders<br />
including governments, large customers<br />
and employees, are now emphasizing the<br />
need for a sense of social responsibility.<br />
Users demand that suppliers of major<br />
business tools such as multi-function<br />
printing machines share the same belief<br />
in social values. Canon is deeply committed<br />
to the concept of corporate social<br />
responsibility.<br />
Corporate Philosophy: Kyosei<br />
Canon’s corporate philosophy is “Kyosei”<br />
which refers to all people, regardless<br />
of race, religion or culture, harmoniously<br />
living and working together into the future.<br />
Based on the philosophy of Kyosei, Canon<br />
makes every effort to create technology to<br />
benefit future society for the prosperity of<br />
the world and the happiness of humankind.<br />
At the same time, towards the fulfillment of<br />
their social responsibilities, Canon promote<br />
both enriched lifestyles and the global environmental<br />
while also carrying out social<br />
contribution activities.<br />
First Step to Green Strategy<br />
Canon is now implementing a new product<br />
strategy, introducing MFDs that are pioneering<br />
higher levels of environmental friendliness<br />
and corporate social responsibility.<br />
a) Eco Friendly Materials<br />
eco-friendly materials in construction. They<br />
employ certain components fabricated with<br />
100% recycled plastic materials from retired<br />
products.<br />
Canon’s innovative green technologies<br />
include bio-based plastic materials, and a<br />
plant-derived compound that replaces certain<br />
petroleum-based plastic parts.<br />
Other components that will be recycled<br />
include the drum, and the toner cartridges<br />
through recycle program.<br />
This green technology is being progressively<br />
applied to all Canon machines, part<br />
of a new green production strategy that will<br />
in future enable 100% of the company’s<br />
multi-function machines to be recycled or<br />
otherwise safely disposed of with minimal<br />
environmental burden.<br />
b) CO 2 emissions down 30%<br />
Canon has lowered the lifecycle CO 2<br />
emissions of the imageRUNNER AD-<br />
VANCE series of machines by a total of<br />
30% compared with conventional models.<br />
It achieved this large reduction in the carbon<br />
footprint of its machines by focusing on<br />
each state of the product life cycle, including<br />
manufacturing, user operations, and logistics,<br />
and then analyzing the energy use<br />
at each stage and systematically improving<br />
the design to reduce it.<br />
c) Power consumption is only 1W<br />
or less<br />
Canon’s factories going green<br />
Canon’s R&D, design and<br />
manufacturing sites are<br />
implementing green policies<br />
throughout their operations. For<br />
example, Canon is reducing its CO 2<br />
emissions by developing energysaving<br />
production technologies and<br />
installing energy-saving facilities.<br />
Another practical step is the<br />
reduction of packaging materials<br />
used to deliver MFDs, components<br />
and consumables, to reduce waste<br />
and make consignments lighter,<br />
thus saving CO 2 during shipment.<br />
Canon also exceeds the toughest<br />
global standards set by the<br />
European RoHS standard, which<br />
requires the restriction of six<br />
specified hazardous substances.<br />
Canon currently restricts the use of<br />
no less than 24 such substances in<br />
its products.<br />
The imageRUNNER ADVANCE Series is<br />
designed for both high energy efficiency and<br />
extraordinary performance. A new kind of im-<br />
The new imageRUNNER ADVANCE serieage<br />
fixing unit with “On-demand” fixing ensures<br />
Canon imageRUNNER ADVANCE SERIES<br />
20<br />
introduced<br />
Computerworld<br />
in 2010<br />
<strong>Hong</strong><br />
feature<br />
<strong>Kong</strong><br />
the<br />
September<br />
use of<br />
2010<br />
better reliability than with conventional rollers,<br />
www.cw.com.hk
Brought to you by Canon<br />
and this technology, combined with a new<br />
toner called pQ, significantly reduces overall<br />
energy consumption by minimizing heat and<br />
power requirements. A rapid warm-up time<br />
– only 38 seconds from power-on – encourages<br />
users to turn the machine off when not<br />
in use. When devices are in sleep mode,<br />
power consumption is only 1W or less.<br />
d) Reduce Noise Level<br />
Various noise-reduction measures and<br />
control features are also implemented in<br />
the configuration of the imageRUNNER<br />
ADVANCE C5051 & C5045 to ensure minimum<br />
noise levels during both operation and<br />
standby mode.<br />
Another Big Step for Efficiency<br />
a) Scan directly to Powerpoint format<br />
One of the ways that Canon helps the<br />
green office is by enabling better management<br />
of electronic documents, which reduces<br />
the need to constantly print out paper<br />
copies.<br />
Industries such as finance, education and<br />
construction that use a lot of PowerPoint<br />
slides expend hundreds of hours patiently<br />
keying text and placing graphics in the<br />
PowerPoint format. The imageRUNNER<br />
ADVANCE automates most of that work.<br />
For example, any color or black-and-white<br />
material can be scanned and automatically<br />
converted to the latest PowerPoint Format<br />
(pptx), saving users a huge amount of time.<br />
Canon is the official digital imaging partner<br />
of Microsoft Office 2010. So Canon MFDs<br />
can have native connection to Microsoft<br />
SharePoint 2010, which enables electronic<br />
documents to be easily shared, especially<br />
through the Web or by email. This also enables<br />
many users operations to be executed<br />
without printing out paper copies.<br />
b) Automatic form-to-database<br />
scanning<br />
A unique service provided by Canon enables<br />
imageRUNNER ADVANCE users to<br />
scan large numbers of forms such as invoices,<br />
and<br />
www.cw.com.hk<br />
have the machine perform OCR and<br />
Enriching user experience & cutting the environmental burden<br />
Passing on a healthy environment to the next generation.<br />
We can reduce burden on the environment by developing environmental<br />
technology and promoting recyceling.<br />
Canon plans to reduce the environmental burden of document processing, but<br />
skeptics may wonder if the company can do that without sacrificing the things<br />
that make users’ lives comfortable and convenient. Canon believes that doing<br />
both is the key to a sustainable society.<br />
Canon has a symbol (see above) that expresses this dual strategy. In the<br />
symbol, one arrow indicates that ‘Enrichment’ should increase, which means<br />
a more convenient and efficient lifestyle that enriches our lives with innovative<br />
technology. A second arrow indicates that the ‘Environmental burden’ should<br />
decrease, because Canon intends to pass on a healthy environmental to the next<br />
generation. Canon can reduce the burden on the environment by developing<br />
environmental technologies and promoting recycling.<br />
“At Canon, we are not just machine vendors but <strong>net</strong>worked communication<br />
specialists,” said Daniel Chung, Senior Marketing Manager, Business Imaging<br />
Solution Marketing Division. “We seek a close partnership with our users to help<br />
them leverage machines such as the imageRUNNER ADVANCE to improve the<br />
processing, management and security of their electronic documents. We help<br />
them minimize the need to print out paper copies, increase scanning efficiency<br />
and systematically reducing the environmental footprint of the whole reprographic,<br />
document management, and communication processes.”<br />
transfer any selected data to the appropriate<br />
fields in a corporate database, with no<br />
re-keying of data. Large companies receive<br />
hundreds of thousands of similar forms and<br />
about 85% of forms are currently re-keyed.<br />
Canon consultants can create a template for<br />
a specific form that enables it to be scanned<br />
to a database without any manual work. This<br />
process greatly increases efficiency when<br />
thousands of forms are processed.<br />
c) Security and access control for<br />
documents.<br />
For more details, please visit:<br />
www.canon.com.hk/en/business/home<br />
A more<br />
convenient and<br />
efficient lifestyle.<br />
Enrichment<br />
our lives with<br />
innovative<br />
technology.<br />
Canon MFDs can provide comprehensive<br />
security and access control for electronic<br />
documents. Many companies limit access<br />
by printing out paper copies for authorized<br />
users, but Canon’s system of controlling<br />
access to the electronic storage on its <strong>net</strong>worked<br />
MFDs eliminates the need for such<br />
paper printout.<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 21
CHINAWATCH<br />
4 continued from page 12<br />
a stressful environment, as well as their<br />
sense of social responsibility to the team,<br />
said Finocchario. The EQ test “provides<br />
a measuring stick on how someone will<br />
adjust,” he said.<br />
Rongley believes that higher-IQ <strong>IT</strong><br />
workers are more productive. “The point<br />
is not that they are typing faster, but they<br />
are finding a faster solution to the technical<br />
problem,” said Rongley.<br />
North American customers<br />
Moreover, unlike many of the larger<br />
<strong>IT</strong> offshore development companies,<br />
Bleum is focused on long-term engagements<br />
with its clients, not on one-time<br />
projects. Over time, it hopes to hire 100<br />
to 500 US workers to help support North<br />
American customers.<br />
China’s technology labor force is<br />
largely young; the massive government<br />
ramp-up in science and engineering education<br />
is a recent development, and the<br />
labor force doesn’t yet have a broad pool<br />
of people with deep experience in technical<br />
disciplines. By seeking high-IQ<br />
employees, “we’re compensating for the<br />
experience gap,” said Rongley.<br />
He also said that the number of students<br />
seeking computer science degrees,<br />
which has dipped in the US, is on the rise<br />
in China.<br />
“China has a much larger talent pool<br />
than India does, and it has much less demand<br />
for that talent,” said Rongley, who<br />
added that the number of new computer<br />
science graduates each year is about<br />
300,000.<br />
India dominates the offshore outsourcing<br />
industry, helped by the fact that it has<br />
a large English-speaking population. The<br />
largest Indian <strong>IT</strong> vendors have in excess<br />
of 100,000 employees.<br />
The impact of China’s larger talent<br />
pool may be evident in an international<br />
coding contest conducted annually by<br />
TopCoder Inc, a Glastonbury, USA.-<br />
based software development service.<br />
Baidu sues Chinese security company<br />
The search engine giant is suing Chinese company 360 for unfair competition<br />
By Michael Kan, IDG News Service (Beijing Bureau)<br />
Last year, about 4,200 people took<br />
part in this coding competition, which<br />
includes events such as algorithmwriting<br />
contests. Of the 70 finalists,<br />
20 were from China, 10 from Russia<br />
and two from the US. The top winner<br />
was Chinese. The contest is sponsored<br />
in part by the National Security<br />
Agency.<br />
Bleum has a policy of requiring its employees<br />
to speak English, and many of its<br />
hires have already been through Englishlanguage<br />
programs widely taught in the<br />
schools. The company uses a system of<br />
levels for marking capability with English,<br />
with the highest level reserved for<br />
those who achieve accent neutralization,<br />
said Rongley.<br />
“In China, for a long time now, anyone<br />
from eighth grade and above is being<br />
taught English,” said Rongley. However,<br />
what those students don’t have is an opportunity<br />
to practice, he noted, adding,<br />
“We create the environment for them to<br />
practice all the time.” 3<br />
Baidu, operator of China’s largest<br />
search engine, is suing domestic<br />
security vendor 360 for unfair<br />
competition alleging a version of 360’s<br />
security software flags both Baidu Toolbar<br />
and Baidu Address Bar as malware.<br />
The software tells users the plugins<br />
must be removed, Baidu said. The suit,<br />
which was filed late last month, demands<br />
that 360 cease with its unfair practices.<br />
Baidu is also suing the company for 10<br />
million renminbi (US$1.4 million) and is<br />
requesting that 360 issue public apologies<br />
on its websites as well as on several<br />
major news sites in China.<br />
Baidu declined to comment, but confirmed<br />
that the suit was accepted by Beijing<br />
Second Intermediate People’s Court.<br />
360, a major software security provider<br />
in China, responded to Baidu’s claims<br />
in a statement last month. The company<br />
highlighted how search engines are sites<br />
for “swindling” and that they provide avenues<br />
for online threats to reach users.<br />
“In providing search results, Baidu has<br />
made no obligation toward protecting its<br />
users. Baidu is not a security company,”<br />
360 said.<br />
Whether or not Baidu’s toolbars were<br />
flagged as malware is decided by user<br />
vote, the company added. “Baidu should<br />
check to see if these two software programs<br />
are operating correctly,” 360 said.<br />
This is not the first time that 360 has<br />
faced a lawsuit for unfair competition.<br />
In the past, it has also seen trouble with<br />
Yahoo China and other domestic companies.<br />
360 was founded by Zhou <strong>Hong</strong>yi, who<br />
was originally the general manager of Yahoo<br />
China. Following his departure, Yahoo<br />
China sued Zhou’s new company in 2006,<br />
alleging that 360’s security software was<br />
identifying Yahoo Toolbar as malware.<br />
Yahoo China later won the case.<br />
“This is a very old battleground,”<br />
said Mark Natkin, managing director of<br />
Beijing-based Marbridge Consulting.<br />
“You will see a plethora of suits between<br />
different companies, not just in the antivirus<br />
malware field, but also in types of<br />
toolbars. If you install one company’s<br />
toolbar, it will disable the other company’s<br />
toolbar.” 3<br />
22 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 13
CAREERWATCH n i h a r i k a c h at u r v e d i<br />
Contractors offer answers to growth challenge<br />
Companies and individuals ponder mindset shift as<br />
contracting offers flexible expansion options<br />
By Niharika Chaturvedi<br />
The recovering economy in Asia<br />
has signaled a greater flow<br />
of investment into the region<br />
with multinationals and regional firms<br />
growing their presence and the supporting<br />
infrastructure to support the<br />
expansion.<br />
More often than not, an organization’s<br />
strategy to set up its new team<br />
includes hiring permanent resources,<br />
as well as outsourcing specific operations<br />
to various <strong>IT</strong> services companies<br />
and independent contractors.<br />
A contractor is a specialist in a specific<br />
area who is hired for a fixed term<br />
to complete an allocated task. Because<br />
these people are professionals in their<br />
area of expertise, they are typically<br />
paid a premium salary.<br />
An individual specializing in a technical<br />
field has two career choices—to<br />
take on the managerial career route, or<br />
to become an expert individual contributor.<br />
Contracting is a very popular<br />
career path in western countries such as<br />
Europe, USA, UK, Australia and New<br />
Zealand. This is due to the flexibility it<br />
provides to an individual’s lifestyle—<br />
contracting professionals often make<br />
use of the breaks in-between contracts<br />
to pursue hobbies or travel plans.<br />
Open mind<br />
A majority of <strong>IT</strong> professionals generally<br />
have a high preference for specializing<br />
in a niche area while moving<br />
on from one organization to another.<br />
This allows them an opportunity to<br />
gain exposure to new<br />
environments, technologies<br />
and projects<br />
which contribute to<br />
their knowledge and<br />
expertise. Based on<br />
the types of projects<br />
they are exposed to,<br />
they are often able to<br />
increase their rates<br />
after garnering adequate<br />
experience in<br />
various areas of expertise.<br />
From an organizational<br />
perspective,<br />
there are many benefits<br />
of hiring talents<br />
on contract:<br />
• Completing a sixmonth<br />
task in three<br />
months by employing<br />
an expert provides<br />
a more costeffective<br />
solution<br />
to an organization.<br />
• Having a pool of contractors offers<br />
more flexibility in maintaining the<br />
work-force balance in times of<br />
downturn.<br />
• Contracting offers an initial insight<br />
into new markets which will help in<br />
making manpower decisions in countries<br />
with stricter labor laws.<br />
• Headcount issues can be easily managed<br />
by hiring talents on contract<br />
and passing on the responsibility of<br />
HR administration to professional<br />
Chaturvedi from Robert Walters: Consider Asian contractors<br />
organizations instead.<br />
• Organizations have the flexibility to<br />
transfer resources from one project to<br />
another based on appropriate skillssets<br />
required for different projects.<br />
Contracting in Asia<br />
Before the global <strong>IT</strong> revolution, the<br />
working culture in Asia was skewed<br />
towards job longevity and stability,<br />
thus resulting in the contracting option<br />
continued on page 26 4<br />
24 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 25
CAREERWATCH<br />
4 continued from page 24<br />
being a less popular method of hiring<br />
or working in Asia. In comparison with<br />
current dynamics revolving from what<br />
was once the famous Japanese working<br />
style of “one company, one career, one<br />
life” in older times, to current software<br />
engineers in India following a “one<br />
year, one company” lifestyle, Asia has<br />
seen a complete turnaround.<br />
Contracting offers a middle-path<br />
solution for the budding software professional<br />
who is hungry for exposure<br />
to new projects, more attractive compensation<br />
packages and new environments,<br />
as well as the employer on the<br />
lookout for expert talents to take on<br />
high–profile projects without having to<br />
commit to progressive career growth<br />
or an investment in long-term permanent<br />
headcount.<br />
The challenge in Asia, however,<br />
seems to come from both sides.<br />
Employers in the banking world are<br />
attracted to Asia in terms of its lower<br />
labor costs and are thus not encouraged<br />
to pay a premium to hire a contractor.<br />
As a result, many organizations are not<br />
entirely open to adopting the contracting<br />
resource option as it brings about<br />
the uncertainty of income and employment<br />
beyond the contractual period.<br />
A person who is employed on a contract<br />
might constantly be on the lookout<br />
for his/her next assignment and/<br />
or a permanent job. In fact, there is a<br />
high percentage of people preferring to<br />
switch jobs approximately every couple<br />
of years given the current buoyant<br />
job market facing a limited supply of<br />
skilled labor.<br />
Contracting in Asia has the potential<br />
to mature into two different models.<br />
1) Alternate long-term hiring: Many<br />
global hiring organizations find it a<br />
challenge to obtain headcount approvals<br />
for permanent positions in offshore<br />
locations, in comparison with positions<br />
of six-month to one-year contracts.<br />
Thus, candidates are sometimes hired<br />
as a solution to bypass the headcount<br />
approval process and then gradually<br />
given the option to convert to a permanent<br />
headcount in the event of good<br />
performance and/or strong business<br />
case to justify the existing role.<br />
1) Expertise-based hiring: A fixedterm<br />
contract hire comprises of hiring<br />
an expert to complete an integral part<br />
of the project, or sometimes to run a<br />
very strategic and high visibility project.<br />
The expertise developed in this<br />
case can often lead to a premium being<br />
charged.<br />
There are various other reasons for<br />
hiring on contract; however, from a job<br />
seeker’s perspective, this is an option<br />
with opportunities galore as the market<br />
gradually matures with time.<br />
Contracting is here to stay, regardless<br />
if it is a challenging or booming<br />
market. There are definitely more options<br />
out there in the job market when<br />
one keeps an open mind to consider<br />
contract work. Here are more reasons<br />
why the job seeker should say “yes” to<br />
contracting:<br />
• It opens the door to a new industry or<br />
a new profile.<br />
• It is a stopgap arrangement for those<br />
in-between jobs.<br />
• It helps to increase your cash-inhand<br />
by clubbing in the bonus as a<br />
guaranteed income.<br />
• It gives you the opportunity to try out<br />
a role before deciding to move longterm<br />
into a similar position, without<br />
having to commit to your employer.<br />
• You gain exposure to new technologies<br />
and projects across the industry<br />
in a much shorter time span.<br />
• You are provided with the opportunity<br />
to list additional knowledge and<br />
value to your CV with every new<br />
project undertaken.<br />
• You are provided with the opportunity<br />
to prove yourself in a large MNC<br />
environment and get recognized for<br />
better roles.<br />
• There is a lower risk of losing your<br />
job since the cost of hiring a contractor<br />
is relatively lower in comparison<br />
with a permanent headcount and<br />
Many Asian organizations are not entirely open to<br />
adopting the contracting resource option as it brings<br />
about the uncertainty of income and employment<br />
beyond the contractual period<br />
organizations are thus less likely to<br />
hire and fire.<br />
• You have the opportunity to experience<br />
salary increments from one<br />
contract to another instead of having<br />
to wait for annual increments.<br />
• From a lifestyle perspective, it provides<br />
you with more freedom to plan<br />
longer holidays in-between contracts<br />
or to invest your time in trainings<br />
and courses to upgrade yourself and<br />
gain more skills.<br />
In short, contracting definitely provides<br />
you with a more flexible lifestyle<br />
while broadening the limits and horizons<br />
for a professional, well-rounded<br />
and exponential career path. 3<br />
Niharika Chaturvedi is senior consultant<br />
(<strong>IT</strong> Banking Contract division) at<br />
Robert Walters Singapore.<br />
26 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 27
“Video is our next voice !!”<br />
Business Video is far more than<br />
just video conferencing.<br />
Macroview had showcased a<br />
variety of latest ICT technologies<br />
with real-life application<br />
examples in both the Retail Asia Expo in<br />
June and Finance Tech Forum in July.<br />
Although the visitors to these two<br />
events were from very different<br />
business nature, we observed that<br />
many of them were interested in and<br />
actually had the need to integrate and<br />
apply high quality, real-time and<br />
interactive video elements into their<br />
business operations.<br />
Retailers can now use interactive HD<br />
video displays to attract consumers to<br />
their shops from anywhere in the mall<br />
or even simply from a nearby bus<br />
station, and to pass on product or<br />
marketing information in the most<br />
visual and vibrant way. Bankers can<br />
make use of similar video platforms to<br />
deliver the most direct and interactive<br />
services to their clients at bank<br />
branches – improving customer<br />
experience while saving on service<br />
costs. Video-based banking services<br />
may include financial-advisor-ondemand,<br />
interactive video and<br />
context-based financial data displays,<br />
centralized product update and<br />
training to branch staff after office<br />
hours, etc. The era of BUSINESS VIDEO<br />
has arrived.<br />
Business Video is far more than<br />
just video conferencing - Business<br />
Video encompasses TelePresence,<br />
Unified Communications, Enterprise<br />
Social Video, Digital Signage,<br />
Enterprise TV, Video Surveillance, etc.<br />
With the help of a carefullydesigned<br />
intelligent IP infrastructure,<br />
HD video contents can be securely and<br />
promptly delivered through an<br />
enterprise <strong>net</strong>work. When the video<br />
elements merge with the business<br />
logics, they help create very visual and<br />
extraordinary business angles for<br />
decision makers.<br />
Success will be limited if you treat<br />
Business Video only as a technology.<br />
Macroview is the magician that can<br />
help integrate latest video technologies,<br />
secured wired and wireless<br />
Sales &<br />
Marketing<br />
- Telepresence with<br />
partners<br />
- HD signage at POS<br />
- Consumer behavioral<br />
video analytics<br />
- Remote expert<br />
consultation<br />
Logistics &<br />
Security<br />
- Warehouse surveillance<br />
- Goods/vehicle<br />
movement tracking<br />
- Item tallying<br />
Macroview showcased<br />
the latest Business<br />
Video solutions to<br />
financial institutions in<br />
the Finance Tech<br />
Forum.<br />
<strong>net</strong>working<br />
solutions with The “Connected Bus Shelter” in<br />
business<br />
Retail Asia Expo demonstrated the<br />
real-time, interactive video displays<br />
processes to<br />
for retailers and shopping malls to<br />
provide true<br />
address social <strong>net</strong>working needs.<br />
Business<br />
Video turnkey<br />
solutions for enterprise clients. We do<br />
believe the importance of Video is rising in<br />
the business world and expanding across<br />
all desktop and mobility platforms<br />
including the PC, telephony and mobile<br />
devices.<br />
HR &<br />
Training<br />
- Remote Interview<br />
- Staff counseling<br />
- Interactive video<br />
training for remote<br />
offices<br />
“Video is our next voice !!”<br />
Finance &<br />
Accouting<br />
- Analysis of revenue<br />
against no. of shop<br />
visitors<br />
- Executive<br />
telepresence<br />
- Briefing to press<br />
and financial analysts<br />
LUCAS (Integration Layer)<br />
R&D &<br />
Engineering<br />
- Design and prototype<br />
illustrations<br />
- Video and<br />
UC collaboration<br />
- Sharing ideas via<br />
HD video social<br />
<strong>net</strong>working<br />
The essence of Business Video is not<br />
just on the high video quality, but also<br />
on how well the video elements<br />
integrate with business functions to<br />
practically enhance business communications<br />
and provide users with<br />
meaningful business analyses and<br />
management. A critical success factor is<br />
the “interactive” capability for support<br />
of real-time multi-way dialogues.<br />
TelePresence<br />
Unified<br />
Communications<br />
R<br />
Social Video<br />
Video Surveillance<br />
and Analytics<br />
Video Messaging<br />
IP Infrastructure<br />
Enterprise TV<br />
Digital Signage<br />
28 Computerworld <strong>Hong</strong> <strong>Kong</strong> September The 2010 architecture of Business Video<br />
www.cw.com.hk
Advertorial<br />
Macroview deploys Cisco OTV<br />
to enable Workload Mobility<br />
across Data Centres<br />
Overlay<br />
Transport<br />
– A solution that is independent of the infrastructure<br />
technology and services, flexible over various interconnect<br />
facilities<br />
– Transporting services for layer 2 and layer 3 Ether<strong>net</strong><br />
and IP traffic<br />
With the introduction of Cisco OTV, we<br />
are now able to extend VMWare VMotion<br />
across long distances, providing customers<br />
with resource flexibility and workload<br />
portability that span across geographically<br />
dispersed data centres.”<br />
Virtualization<br />
C<br />
isco Overlay Transport Virtualization<br />
(OTV) is a built-in solution<br />
on the preeminent data center<br />
switches, the Cisco NEXUS 7000 Series<br />
Switches. OTV can be thought of as<br />
MAC-address routing, in which<br />
destinations are MAC addresses, and<br />
the next hops are IP addresses. The<br />
convenience brought by OTV will not<br />
sacrifice the scalability, resiliency,<br />
multipathing, and failure-isolation<br />
characteristics of a Layer 3 connection.<br />
– Provides virtual connections,<br />
connections that are in turn virtualized and<br />
partitioned into VPNS, VRFs, VLANs and Bridge<br />
Domain instances<br />
Macroview is a pioneer in using Cisco<br />
OTV to enable workload mobility across<br />
data centres for clients in <strong>Hong</strong> <strong>Kong</strong>.<br />
“Moving workloads between data<br />
centres has typically involved complex<br />
and time-consuming <strong>net</strong>work design<br />
and configurations. In most of our<br />
previous implementations for clients,<br />
VMWare VMotion feature is normally<br />
deployed within a single data centre.<br />
“This represents a significant advancement<br />
for the implementation of virtualized data<br />
centre by simplifying and accelerating<br />
long-distance workload migrations.” said<br />
P.H Tang, CTO of Macroview Telecom.<br />
About Macroview<br />
Macroview Telecom is a professional<br />
system integrator providing<br />
Inter<strong>net</strong>working solutions for<br />
enterprise IP <strong>net</strong>work infrastructures,<br />
DWDM optical <strong>net</strong>works,<br />
Data Centres, IP unified communications,<br />
carrier backbones, business<br />
videos, <strong>net</strong>work security and<br />
<strong>net</strong>work management. We have<br />
been operating since 1991 and now<br />
have offices and technical support<br />
centers in <strong>Hong</strong> <strong>Kong</strong>, Guangzhou,<br />
Shanghai, Beijing, Dongguan,<br />
Shenzhen and Macau.<br />
To get more information, please<br />
visit www.macroview.com<br />
Cisco OTV enabling VMotion across data centers<br />
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 29
Advertorial<br />
Meeting the complex needs for a<br />
secure and adequately controlled<br />
ICT environment<br />
Keep your mission critical applications<br />
running and achieve <strong>IT</strong> agility<br />
According to the circular issued<br />
by Securities and Futures<br />
Commission (SFC) in March<br />
2010, all licensed corporations in the<br />
banking and securities industry shall<br />
establish policies and procedures to<br />
ensure the integrity, security, availability,<br />
reliability and thoroughness of all<br />
information, including documentation<br />
and electronically stored data, relevant<br />
to the firm’s business operations.<br />
Almost all enterprises require a secure<br />
and adequately controlled ICT environment<br />
for their ICT operations and<br />
information management systems<br />
Throughout the years when<br />
Macroview designs <strong>net</strong>work solutions<br />
for different customer requirements<br />
and <strong>net</strong>working scenarios, we observe<br />
that, not only financial service institutions,<br />
but almost all other enterprises<br />
require their ICT operation and<br />
information<br />
management systems to meet the<br />
firm’s needs of a secure and adequately<br />
controlled ICT environment.<br />
To cope with this widespread<br />
security concern, Macroview helps<br />
customers deploy the F5 BIG-IP<br />
Application Security Manager (ASM) as<br />
one of the recommended practices.<br />
ASM provides auto-adaptive approach<br />
to application delivery security, where<br />
the security policy is automatically<br />
updated based on observed traffic<br />
patterns. ASM also comes with<br />
detailed security reporting capabilities.<br />
Macroview recommends clients to<br />
perform incident response, threat<br />
analysis, event correlation and compliance<br />
audits<br />
Apart from the delivery of security<br />
policy, Macroview recommends clients<br />
to perform incident response, threat<br />
analysis, event correlation and<br />
compliance audits. In this case, the<br />
Splunk software becomes an essential<br />
solution that meets such stringent need<br />
of advanced <strong>net</strong>work security operation<br />
and management.<br />
“F5 and Splunk have partnered to<br />
deliver an advanced security reporting<br />
and analysis tool to assist ASM users” said<br />
Linda Hui, the Manager Director of F5<br />
Network <strong>Hong</strong> <strong>Kong</strong> and Taiwan. “This<br />
brings even more value to users of F5’s<br />
Application Security Management<br />
solution, and enables them to meet the<br />
complex needs of incident responses,<br />
threat analyses or compliance audits.”<br />
Splunk allow users to drill down on<br />
security incidents and to build ad-hoc<br />
reports for auditing and compliance<br />
easily<br />
C<br />
M<br />
Y<br />
CM<br />
MY<br />
CY<br />
CMY<br />
K<br />
“Splunk have developed an App to<br />
manage F5 ASM, Firepass and APM devices<br />
by providing out-of-the-box reports and<br />
dashboards. On top of this, Splunk allow<br />
users to drill down on security incidents<br />
and to build ad-hoc reports for auditing<br />
and compliance easily. ” said Robert Lau,<br />
Vice President, Asia Pacific and Japan,<br />
Splunk.<br />
Pre-defined searches, reports and dashboards make it quick to get started and you can customize<br />
Splunk for F5 to meet the specific needs of your agile <strong>IT</strong> environment.<br />
Macroview designs and provides<br />
integrated solutions of Splunk and F5 ASM<br />
to clients with professional services to<br />
meet their unique business environment -<br />
making customers’ ICT operation and<br />
information management systems more<br />
secured and effective.<br />
30 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
<strong>Hong</strong> <strong>Kong</strong>’s Source of <strong>IT</strong> Insight<br />
www.cw.com.hk<br />
technews<br />
techguide<br />
techfeature<br />
industryevent<br />
biznews<br />
viewpoint<br />
bizpeople<br />
analystwatch<br />
industryprofile<br />
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 43
Locking down the data lifecycle<br />
Fuji Xerox bolsters security controls at all stages of data lifecycle to<br />
secure possible information leaks from multi-functional devices<br />
Today, virtually every business organization<br />
has its own copier or a<br />
multi-functional device (MFD) with<br />
all-in-one copy, print, scan and fax functions.<br />
Modern MFDs offer tremendous productivity<br />
advantages. It is fast, convenient<br />
and extremely versatile. Most office workers<br />
will not be able to survive if the printers<br />
/ copiers / MFDs broken down in their<br />
departments.<br />
All kinds of documents are processed and<br />
important information is duplicated, stored<br />
or transmitted through these devices every<br />
day. However, without the correct safeguards<br />
in place, that efficiency can come<br />
at a high price.<br />
“If confidential data is leaked, the business<br />
is at risk, reputations can be ruined<br />
and, in extreme cases, companies can<br />
even close,” said Henry Kwok, General<br />
Manager of Marketing at Fuji Xerox (<strong>Hong</strong><br />
<strong>Kong</strong>) Limited, “That means enterprises<br />
cannot afford to take risks with information<br />
security when it comes to their hardware<br />
devices.”<br />
Hard disk risk<br />
Security risks start when data is written<br />
to the hard disks of MFDs. Without proper<br />
control, these can be accessed relatively<br />
easily by un-authorized users. The risks<br />
continue through the end-of-life, when the<br />
hard disks of defunct MFDs retain valuable,<br />
confidential information.<br />
Such a case happened in April 2010,<br />
when two copiers were acquired from a<br />
used machine broker. They were originally<br />
installed in the Sex Crimes Unit and Narcotics<br />
Unit of New York Police Department<br />
(NYPD). Confidential information from past<br />
investigations was extracted from the machines’<br />
hard disk drives, using a forensic<br />
software program available free on the in-<br />
In Fuji Xerox’s case, all data temporarily stored<br />
in the system hard disk is deleted after the print<br />
jobs are completed.<br />
One of the copiers contained 249,000<br />
copies and 42,000 prints, and it was also<br />
used as a fax machine. Tens of thousands<br />
of documents were extracted from the device,<br />
including detailed domestic violence<br />
complaints and a list of wanted Buffalo sex<br />
offenders. The other copier has a list of targets<br />
from the Operation Impact Drug raid<br />
three years ago on it.<br />
Copy machine truths<br />
and prescription information on the hard<br />
disk.<br />
The news stunned the public about potential<br />
hazards of copying machines. The<br />
lesson is clear. Securing information on<br />
the hard disk, and removing it when the<br />
machine has reached the end of its useful<br />
life are the keys to keeping a tight grip on<br />
enterprise information.<br />
According to Kwok of Fuji Xerox, there<br />
are four types of information security threats<br />
encountered by the MFDs. They include:<br />
1. Leakage of document data and security<br />
audit log data from the system<br />
hard disk<br />
2. Document data, security audit logs<br />
and controller software setting data<br />
are accessed, read, used or altered<br />
from control panel or web browser<br />
without authorization<br />
3. Document data, print jobs from PC<br />
clients, security audit log data, and<br />
controller software setting data on<br />
the internal <strong>net</strong>work are intercepted<br />
or altered<br />
4. Un-authorised access to the internal<br />
<strong>net</strong>work via fax modems from public<br />
telephone lines<br />
To deal with the potential threat of leakage<br />
of document data from hard disk, companies<br />
can look for MFDs with capability to<br />
overwrite stored data or encrypt data in the<br />
hard disks.<br />
Security answers<br />
If companies are afraid of data in the<br />
MFDs being accessed without authorization,<br />
features such as security audit log,<br />
user authentication and system administrator<br />
security management should help.<br />
To prevent data being intercepted on internal<br />
<strong>net</strong>work when MFDs process printed<br />
job from PC clients, companies can encrypt<br />
The news was covered by CBS in prime<br />
time. The CBS report also revealed a shocking<br />
truth: almost every digital copier made<br />
since 2002 contains a hard disk storing an<br />
image of every document copied, scanned,<br />
or emailed by the machine. Unless users<br />
deliberately scrub the hard disk clean, the<br />
records will always remain.<br />
The CBS reporters acquired two more<br />
copying machines from the same broker.<br />
One used by a construction company,<br />
which still had a list of employees’ names<br />
and social security numbers, the other had<br />
been used by a New York insurance com-<br />
ter<strong>net</strong>.<br />
pany which had people’s medical records <strong>net</strong>work data using protocol such as SSL,<br />
32 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
Brought to you by Fuji Xerox<br />
IPSec and S/MIME. And they can also setup<br />
<strong>net</strong>work security management system,<br />
using, for example, SNMPv3.<br />
Finally, to prevent unauthorized access<br />
of data through fax modem, companies can<br />
look for MFDs with fax flow security feature.<br />
4 types of information security threats encountered by MFDs<br />
Enterprises cannot afford to<br />
take risks with information<br />
security when it comes to<br />
their hardware devices<br />
All in all, to deal with the potential security<br />
hazards, companies should be carefully<br />
when choosing their MFDs. Apart from<br />
price and functionalities, they should also<br />
check the security features of the machines,<br />
before making purchases. For example,<br />
whether temporarily stored or stored data<br />
in the machine can be overwritten. Or, how<br />
to deal with used machines<br />
Policy enforcement<br />
In Fuji Xerox’s case, Kwok said, “all data<br />
temporarily stored in the system hard disk<br />
is deleted after the print jobs are completed.<br />
If customers need to store the relevant<br />
data in the hard disk, they are required to<br />
set the duration of data storage according<br />
to their existing data processing policy and<br />
hard disk volume.”<br />
Fuji Xerox also has stringent disposal<br />
Fuji Xerox Tsuen Wan Recycling Centre. All<br />
used copiers / printers / MFDs are re-packed,<br />
containerised and transferred to the FX ecomanufacturing<br />
plant for separation into up to 70<br />
types of raw materials for recycling.<br />
www.cw.com.hk<br />
and recycling processes of MFD hard disk<br />
Industry standard leadership<br />
in place to ensure customer data protection.<br />
Since 2004, Fuji Xerox has been certified<br />
When a MFD reaches the end of its to the ISO 15408 standard. “Fuji Xerox’s<br />
life, it will be shipped to the Fuji Xerox Eco- full range of MFD products are equipped<br />
Manufacturing Co., Ltd. in Thailand where it with the advanced data storage function<br />
is taken to pieces for secure disposal. to ensure the information security,” said<br />
Material is recycled and returned to the Kwok.<br />
industrial manufacturing cycle. The plant Today, Fuji Xerox is the only MFD manufacturer<br />
has helped Fuji Xerox achieve its goal of<br />
to pass the EAL3 (Evaluation As-<br />
reaching zero-landfill with recycling rates of surance Level 3) which encompasses the<br />
99.8%.<br />
following seven security function targets on<br />
By the end of August, Fuji Xerox will the entire device:<br />
launch two other professional services, including:<br />
1. Document data and security audit log<br />
1) dismantling the hard disk from are encrypted before being stored in<br />
the MFD and returning it to the customer the system hard disk<br />
for self-handling, and 2) implementing international<br />
2. Temporarily stored or stored data<br />
standard “3D Procedures” – ‘De-<br />
can be overwritten<br />
gauss’, ‘Destroy’ and ‘Disposal’ of the hard 3. Security audit log alters device maldisk<br />
in front of the customer.<br />
function and configuration, and user<br />
This should prevent embarrassing events, operation data for incidence follow up<br />
such as the case of NYPD, from happening 4. System only allow the authorised<br />
after a MFD reach the end system administrator to log in to set<br />
of its useful life, and bring the security function<br />
peace of mind to companies<br />
5. System can set the individual user<br />
using MFDs.<br />
right<br />
In fact, security of MFD 6. System supports multiple encrypted<br />
is getting more and more communication protocol, such as<br />
attention nowadays. SSL/TLS, IPSec, SNMP and S/MIME<br />
There is an international 7. System can prevent hackers from<br />
standard to measure accessing the internal <strong>net</strong>work via<br />
whether a MFD is secured MFD from public telephone line,<br />
enough. It is ISO 15408 and accessing data in the MFD hard<br />
standard (also known as disk<br />
Common Criteria Certificate)<br />
Moreover, the controller software, which<br />
for Information Technology Security controls the whole MFD, has also been<br />
Evaluation, offered by International Standards<br />
certified to the ISO 15408 standard. All of<br />
Organization. There are seven these are designed to bring the peace of<br />
Evaluation Assurance Levels (EAL). mind to the customers.<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 33
SECUR<strong>IT</strong>YWATCH<br />
Microsoft still mum on programs prone to DLL hijacking attacks<br />
Redmond offers automated tool to simplify attack blocking setup<br />
By Gregg Keizer, Computerworld (US)<br />
Microsoft on August 31 again<br />
abstained from naming<br />
which of its Windows programs,<br />
if any, contain bugs that could<br />
lead to widespread “DLL load hijacking”<br />
attacks. The company also published an<br />
automated tool to make it easier for users<br />
to block attacks exploiting vulnerabilities<br />
in a host of Windows applications.<br />
The DLL load hijacking vulnerabilities<br />
exist in many Windows applications<br />
because the programs don’t call code libraries—dubbed<br />
“dynamic-link library,”<br />
or “DLL”—using the full pathname, but<br />
instead use only the filename. Criminals<br />
can exploit that by tricking the application<br />
into loading a malicious file with the<br />
same name as the required DLL. The result:<br />
Hackers can hijack the PC and plant<br />
malware on the machine.<br />
“Microsoft plans to address those of<br />
our products affected by this issue in the<br />
most appropriate way for customers,”<br />
said Jerry Bryant, a group manager with<br />
the Microsoft Security Response Center,<br />
in a Tuesday entry on that team’s blog.<br />
“This will primarily be in the form of<br />
security updates or defense-in-depth updates.”<br />
Although Microsoft again declined to<br />
call out its vulnerable software, outside<br />
researchers have identified as potential<br />
targets a number of its high-profile apps,<br />
including Word 2007, PowerPoint 2007<br />
and 2010, Address Book and Windows<br />
Contact, and Windows Live Mail.<br />
Other vendors’ software may also<br />
be at risk, including Mozilla’s Firefox,<br />
Google’s Chrome, and Adobe’s Photoshop.<br />
Bloggers try to help<br />
In another blog, Jonathan Ness, an<br />
engineer with MSRC, and Maarten Van<br />
Horenbeeck, an MSRC program manager,<br />
described how customers can deploy<br />
and use a tool the company first offered<br />
Aug. 23.<br />
That tool blocks the loading of DLLs<br />
from remote directories, such as those on<br />
USB drives, Web sites and an organization’s<br />
<strong>net</strong>work, and is aimed at enterprise<br />
<strong>IT</strong> personnel.<br />
Not surprisingly, Microsoft acknowledged<br />
that users have asked for more help<br />
with the tool. Shortly after its release, <strong>IT</strong><br />
professionals complained that the tool<br />
was confusing and asked colleagues for<br />
advice on how to configure it.<br />
To simplify things, Microsoft has<br />
posted a “Fix It” tool on its support site<br />
that automatically blocks any DLLs from<br />
loading from WebDAV or SMB (Server<br />
Message Block) shares, two of the most<br />
likely attack vectors. Users must still<br />
download and install the original tool,<br />
however.<br />
Ness and Van Horenbeeck also downplayed<br />
the threat to some extent, saying<br />
that DLL load hijacking bugs cannot be<br />
exploited via “drive-by” attacks, where a<br />
user’s PC is infected as soon as he or she<br />
browses to a malicious site.<br />
“A victim would need to browse to a<br />
malicious WebDAV server or a malicious<br />
SMB server and double-click a<br />
file in the Windows Explorer window<br />
that the malicious server displays,” they<br />
said.<br />
Microsoft has known of the issue since<br />
at least August 2009, when researchers<br />
with the University of California Davis<br />
notified the company of their work.<br />
There’s evidence, however, of reports as<br />
far back as 2000, and attacks exploiting<br />
the flaw the following year, when the<br />
Nimda worm leveraged the bug in Office<br />
2000.<br />
HD Moore, chief security officer at<br />
Rapid7 and the creator of the Metasploit<br />
pe<strong>net</strong>ration testing toolkit, was the<br />
first to reveal the potential attacks when,<br />
on Aug 19, he said he’d found 40 vulnerable<br />
Windows applications. Moore<br />
was followed by other researchers who<br />
claimed different numbers of at-risk programs,<br />
ranging from more than 200 to<br />
fewer than 30.<br />
Others are working on a fix. “We’re<br />
testing our own Firefox-specific fixes<br />
and plan to get them out to users soon,”<br />
Mozilla’s security team said in an e-mail<br />
reply to questions last week.<br />
Even so, Microsoft said patches may<br />
be long in coming to some users. “We<br />
recognize that it may take quite a bit of<br />
time for all affected applications to be<br />
updated and for some, an update may not<br />
be possible,” Bryant admitted. 3<br />
34 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
Nov 11, 2010<br />
Sheraton <strong>Hong</strong> <strong>Kong</strong><br />
Call for Sponsorship<br />
Cloud computing challenges faced by <strong>IT</strong> management<br />
If you have solutions that will help CIO/CEO/CFO change these challenges into<br />
opportunities, please join as sponsor and get in touch with your target audience.<br />
For sponsorship opportunities, please contact<br />
Connie Yip Account Director Tel: 2589 1373 Email: cyip@questexasia.com<br />
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 35
CIOs back in the fray as<br />
Asian <strong>IT</strong> recovers<br />
Top <strong>Hong</strong> <strong>Kong</strong> CIOs and <strong>IT</strong> heads discuss “CIO Opportunities<br />
in the New Economy” By Ross Milburn<br />
Another high-energy Computerworld<br />
<strong>Hong</strong> <strong>Kong</strong> TalkTech<br />
discussion started with globalization<br />
and the acknowledgement that<br />
Asia is leading the economic recovery.<br />
“Customers previously executed regional<br />
projects in <strong>Hong</strong> <strong>Kong</strong> or greater China<br />
[and] are now increasing their scope,”<br />
said Tony Fung, executive, Global Technology<br />
Services, IBM Global Technology<br />
Services, IBM China/<strong>Hong</strong> <strong>Kong</strong>.<br />
“They might combine <strong>Hong</strong> <strong>Kong</strong>, Japan<br />
and seven or eight Asian countries—<br />
or even global projects that align the US,<br />
European and Asian branches of an organization.”<br />
Others agreed with this global theme.<br />
“In the past, many FedEx <strong>IT</strong> initiatives<br />
were initiated at headquarters and implemented<br />
here in the regions with little input<br />
from the regional teams,” said Alison<br />
Dack, VP for <strong>IT</strong> and CIO, Asia Pacific,<br />
FedEx Express.<br />
“Now there is heightened awareness<br />
to engage early on and work more seam-<br />
lessly and collaboratively,” said Dack.<br />
“This process of understanding needs,<br />
challenges and solutions empowers our<br />
Asia-Pacific <strong>IT</strong> team to contribute to a<br />
better global solution and to actively participate<br />
in the delivery cycle. In addition,<br />
collaboration also ensures we continue<br />
to develop relevant <strong>IT</strong>-enabled valueadded<br />
solutions that customers demand<br />
for their business.”<br />
Globalization a must<br />
“A few years ago, our company selected<br />
a very US-centric CRM solution for<br />
global implementation and it was abandoned<br />
last year as a disaster,” said Byron<br />
Hou, <strong>IT</strong> director, Asia Pacific, Cushman<br />
& Wakefield. “Now every regional business<br />
head is on a committee, and the<br />
worldwide offices are able to contribute<br />
and be responsible for a global CRM solution<br />
together.”<br />
Apparently regional development is not<br />
the sole answer. “Five years ago, we used<br />
to create regional project teams to execute<br />
My users keep asking why <strong>IT</strong> can’t develop<br />
applications like iPhone or Facebook, which don’t<br />
require training<br />
—Andrew Ling, Bossini<br />
projects,” said Edison Sam, assistant VP<br />
& head of <strong>IT</strong>, New York Life Insurance<br />
Worldwide. “We would aim to achieve<br />
80% standardization with 20% variation to<br />
suit local users. It didn’t work.”<br />
“With five countries [involved], the<br />
projects took two to three times longer and<br />
cost more, said Sam. “Now we collaborate<br />
globally on more than half our projects to<br />
achieve as much consensus as possible,<br />
36 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
ut we have abandoned rigid standardization.<br />
One country will implement the project<br />
first and the others are encouraged to<br />
follow in their own time with appropriate<br />
customization of platform and other requirements.”<br />
Fickle users<br />
Keeping users happy is still top priority<br />
and it’s not getting any easier. “Users<br />
tend to change requirements due to<br />
changing conditions,” said Helen Wong,<br />
chief, Finance Systems Development,<br />
Hospital Authority. “You ‘spec’ it out<br />
clearly, but the market changes and they<br />
want something different. Small changes<br />
are OK, but big changes are difficult and<br />
the CEO wants to know why it cost so<br />
much.”<br />
Most CIOs agreed that business analysts<br />
must liaise between <strong>IT</strong> and users. “For any<br />
project, we need business analysts, otherwise<br />
it’s difficult to capture the necessary<br />
information,” said Arthur Wong, head of<br />
Inter<strong>net</strong> Banking Department, Information<br />
Technology Development Department,<br />
Chong Hing Bank. “Especially when users<br />
don’t always know what they want.<br />
The lack of analyst skills could extend the<br />
delivery time.”<br />
IBM’s Fung: Customers previously executed<br />
regional projects in <strong>Hong</strong> <strong>Kong</strong> or greater<br />
China [and] are now increasing their scope<br />
But smooth-talking business analysts<br />
can’t always keep users happy. “We set<br />
up Project Management and Business<br />
Analysis departments last year, said Sam.<br />
“But company culture doesn’t change<br />
overnight. Users don’t understand the<br />
benefits and also must understand that<br />
while they can make late changes, proper<br />
change management procedures with impact<br />
analyst must be in place.”<br />
Skills shortage<br />
The ongoing <strong>IT</strong> skills shortage is another<br />
worry. “The market is bouncing back, but<br />
it’s difficult to find people with the right<br />
skills for each project,” said Ken<strong>net</strong>h Yiu,<br />
manager, Integrated Technology Services,<br />
IBM Global Technology Services, IBM<br />
China/<strong>Hong</strong> <strong>Kong</strong>. “Staff are moving<br />
around looking for security, especially in<br />
China, <strong>Hong</strong> <strong>Kong</strong> and Macau.”<br />
Andrew Ling, director of <strong>IT</strong> and supply<br />
chain, Bossini, said: “It comes down<br />
to standardization. If you shop for servers<br />
and SANs from different vendors, you<br />
may get incompatibility, so it may be easier<br />
with a single vendor—and you’ll get a better<br />
deal.”<br />
But the single-vendor-theory has its<br />
downside. “My company adopted a single<br />
vendor policy for hardware and software,<br />
but I have a hard time getting the vendor’s<br />
attention,” said Wong from Chong Hing.<br />
“When I requested proposals from multiple<br />
vendors, I got a lot more response<br />
and aggressive price-cuts, sometimes up<br />
to 50-60%. I also found that vendor competition<br />
resulted in better solutions.”<br />
The outsourcing conundrum<br />
Although most CIOs do some outsourcing,<br />
caution is essential. “Outsourcing technology<br />
can mean a lot of things,” said Yiu<br />
from IBM. “Full outsourcing was common,<br />
but now the trend is for flexible sourcing,<br />
with different selected vendors for specific<br />
needs.”<br />
Helen Wong agreed. “Flexible sourcing<br />
The Hospital Authority’s Wong: Small<br />
changes are OK, but big changes are<br />
difficult and the CEO wants to know why it<br />
cost so much<br />
provides more choice, flexibility and costeffectiveness,<br />
and you also have more bargaining<br />
power.”<br />
User-friendly interfaces<br />
CIOs agreed that most applications<br />
are not user-friendly enough. “I bought<br />
an iPhone for my wife,” said Ling, “and<br />
was surprised to see my daughters, aged<br />
two and four years, using it without any<br />
training. My users keep asking why <strong>IT</strong><br />
can’t develop user-friendly applications<br />
like iPhone or Facebook, which don’t<br />
require training and minimize operation<br />
mistakes.”<br />
“We need a fundamental rethink in the<br />
design process, because the traditional way<br />
of developing applications results in boring<br />
interfaces which cause user errors in spite<br />
of operator training, and require multiple<br />
sign-ons,” said the Bossini director. “I’ve<br />
started an initiative on usability architecture,<br />
which includes collecting user feedback<br />
during the design process.”<br />
Do we need school reform “The current<br />
education system in <strong>Hong</strong> <strong>Kong</strong> is<br />
almost killing off usability,” said Arthur<br />
Wong. “It’s like getting blood from a stone<br />
and we need another training method for<br />
creativity.” 3<br />
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 37
The kaleidoscope of post-financial<br />
crisis <strong>IT</strong> management<br />
The pluses and minuses of<br />
swimming at low tide<br />
By Carol Ko<br />
<strong>Hong</strong> <strong>Kong</strong> Housing Authority’s Chu: For<br />
some of the <strong>IT</strong> systems that we plan to<br />
implement, we’ll sometimes host discussions<br />
with our tenants<br />
The financial crisis has eased—or<br />
so it seems. With the chips back<br />
on the table, where have costconscious<br />
CIOs been placing their bets<br />
These and other matters were discussed<br />
by Asia-Pacific CIOs and senior<br />
<strong>IT</strong> executives in a recent roundtable<br />
co-organized by Computerworld <strong>Hong</strong><br />
<strong>Kong</strong> and IBM <strong>Hong</strong> <strong>Kong</strong>. As CIOs<br />
felt each others’ pulses, they concluded<br />
an overall upswing of technology initiatives<br />
and investments, as well as surprises<br />
and shocks during infrastructure<br />
overhaul projects.<br />
Through the financial crisis, investment<br />
bank JP Morgan has publicly stated<br />
that it will continue to invest in new<br />
technology solutions. Through the financial<br />
crisis, the global Banking Firm JP<br />
Morgan has stated that it will continue to<br />
invest in new technology solutions. “We<br />
were presented with a great opportunity<br />
to work more closely with our vendors<br />
to invest smartly,” said Martin Laing, JP<br />
Morgan’s head of <strong>IT</strong>, risk and security<br />
management, Asia Pacific. “We scaled<br />
back some projects, but we continued to<br />
invest as a whole.”<br />
Retail bank China Construction Bank<br />
(Asia) recently replaced its 15-year-old<br />
core banking system. “We work very<br />
hard on negotiating prices with the vendors,”<br />
said Michael Leung, senior vice<br />
president & CIO, CCB (Asia), <strong>IT</strong> and<br />
corporate services. “During the market<br />
downturn in the past years we had huge<br />
bargaining power to get the best deals<br />
because we’re one of the few that were<br />
actually buying. At times we were able<br />
to tell our vendors: ‘Look, give us [the<br />
<strong>IT</strong> products] for free. You can make<br />
money just from the services’,” Leung<br />
said jokingly.<br />
“<strong>IT</strong> investment has been quite steady<br />
[in the government sector] for the last 5<br />
years despite the economic downturn recently”<br />
said Raymond Chu, head of <strong>IT</strong>,<br />
<strong>Hong</strong> <strong>Kong</strong> Housing Authority (HA),<br />
the government body that manages public<br />
housing. However, Chu pointed out<br />
that there had been “a unanimous slowdown<br />
in terms of <strong>IT</strong> investment” in the<br />
private sector.<br />
This year, said Chu, the HA has been<br />
“seriously” looking to adopt cloud computing,<br />
such as desktop virtualization<br />
and private cloud deployment in the testing<br />
and development environment.<br />
The citizens’ roundtable<br />
These days, the <strong>IT</strong> staff working at the<br />
HA are finding themselves interfacing<br />
more with the business—both internal<br />
users and public housing tenants. Chu<br />
said, “For some of the <strong>IT</strong> systems that<br />
we plan to implement, we’ll sometimes<br />
host discussions with our tenants and<br />
other stakeholders: we go to the field and<br />
ask what they want in terms of Inter<strong>net</strong><br />
services, for instance.”<br />
“These discussions have been useful,<br />
added Chu. “If you’re considering what <strong>IT</strong><br />
services to offer to the public [while] ‘in<br />
an ivory tower,’ you tend to believe everything<br />
is good for the tenants. But then our<br />
customers may say ‘I don’t want that’—<br />
38 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
it’s important to strike a balance between<br />
perceived and actual customer needs.”<br />
Legacy system replacement<br />
The Housing Authority has replaced all<br />
the legacy systems, and is in the middle<br />
of implementing SAP projects including<br />
the finance and procurement modules.<br />
“Looking forward, we’re also looking to<br />
expand our data warehouse—the existing<br />
data warehouse was built five years<br />
back,” Chu said.<br />
Swiss Reinsurance is an insurance<br />
company that enable insurance companies<br />
financially to subscribe to more<br />
greater risks, in turn achieving a more<br />
balanced portfolio. “Our challenge is to<br />
globalize our systems, some of which belong<br />
to the second or third generation,”<br />
said Patrick Raths, director of <strong>IT</strong>, Swiss<br />
Reinsurance Company. Raths said his<br />
team was centralizing all the company’s<br />
data centers back in Switzerland, as all<br />
the global and core business applications<br />
were supplied by its Swiss headquarters.<br />
CCB’s Leung: There are many frequenttravelers<br />
between <strong>Hong</strong> <strong>Kong</strong> and mainland<br />
China. If you have RMB funding sources, you<br />
can then settle these payments in RMB—<br />
that’s the way to go<br />
Supermarket coupons<br />
Leung explained that his bank “bravely<br />
survived” a massive core banking replacement<br />
project, largely through careful<br />
planning and execution, but also partly<br />
through the “deployment” of supermarket<br />
coupons. “We had to explain to those<br />
customers who were affected by some<br />
inevitable system outages during the conversion<br />
period and, where necessary, sent<br />
them a coupon to compensate for the inconvenience<br />
they experienced.”<br />
Leung said. “At the same time, we also<br />
used up some of these coupons for our<br />
staff, who had to work round-the-clock<br />
several days in a row; some actually<br />
camped in the office.”<br />
On several occasions during and after the cut-over<br />
period, I was left thinking “Look, what else could better<br />
give us a few hours of breathing space than perhaps a<br />
complete, total power failure in <strong>Hong</strong> <strong>Kong</strong>”<br />
—Michael Leung, CCB (Asia)<br />
Leung added: “On several occasions<br />
during and after the cut-over period, I<br />
was left thinking ‘Look, what else could<br />
better give us a few hours of breathing<br />
space than perhaps a complete, total<br />
power failure in <strong>Hong</strong> <strong>Kong</strong>’ That<br />
would be what we needed.”<br />
“This was no joke. Do it a [core<br />
banking replacement] once in your <strong>IT</strong><br />
career and that’s more than enough,”<br />
he said.<br />
Eyeing/entering China<br />
In <strong>Hong</strong> <strong>Kong</strong>, both local and multinational<br />
companies have been actively expanding<br />
their market reach in China. Sauce<br />
maker Lee Kum Kee is marketing its<br />
sauces to Wenzhou, a coastal city in China<br />
famous for exporting chefs to restaurants<br />
in Europe and the US, according to David<br />
Lau, director of <strong>IT</strong> at Lee Kum Kee.<br />
Over two years ago, CCB (Asia) installed<br />
a dedicated manager to look after<br />
business collaboration with mainland<br />
entities, and has been preparing for the<br />
dawn of RMB businesses. “Already today,<br />
and more in the near future, we in<br />
<strong>Hong</strong> <strong>Kong</strong> will be doing much more<br />
RMB businesses, such as purchasing<br />
goods and services using dual-currency<br />
credit cards, paying utility bills across<br />
the border and settling trade transaction<br />
with mainland partners in RMB,” said<br />
Leung. “There are many frequent-travelers<br />
between <strong>Hong</strong> <strong>Kong</strong> and mainland<br />
China. If you have RMB funding sources,<br />
you can then settle these payments in<br />
RMB—that’s the way to go.”<br />
But entrance to the China market has<br />
not been barrier-free—the Chinese government<br />
has put in place certain “restrictive”<br />
policies in this rabbit-carrot chase.<br />
“China’s foreign exchange policies are<br />
still restrictive,” said Rory Yu, head of<br />
technology management division, technology<br />
management division, information<br />
technology department, Bank of<br />
China <strong>Hong</strong> <strong>Kong</strong>. “Even if you reach<br />
the market, there is no way to invest. So<br />
we’re treating <strong>Hong</strong> <strong>Kong</strong> as a springboard.”<br />
“As our parent company FHC (Fubon<br />
Financial Holding Co) is expanding its<br />
business into mainland China, current<br />
regulations only allow an indirect route<br />
through its <strong>Hong</strong> <strong>Kong</strong> subsidiary,” said<br />
Sunny Chang, senior VP, head of <strong>IT</strong> &<br />
operations, Fubon Bank (<strong>Hong</strong> <strong>Kong</strong>).<br />
Chang said FHC is already investing in<br />
Xiamen and other tier-two Chinese cities<br />
which he considered “promising and<br />
profitable.” 3<br />
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 39
The time has come for<br />
real-time apps<br />
The new customer: the case for predicting and exceeding expectations<br />
By Ross Milburn<br />
In <strong>Hong</strong> <strong>Kong</strong> during August, a group<br />
of CIOs participated in a roundtable<br />
discussion on “The new customer:<br />
the case for predicting and exceeding<br />
expectations,” sponsored by TIBCO<br />
Software. Below is a summary of their<br />
main discussion, which was moderated<br />
by Chee Sing Chan, group editor, Computerworld<br />
<strong>Hong</strong> <strong>Kong</strong>.<br />
Today’s enterprises have lots of data,<br />
but extracting value from it is a continuing<br />
challenge. “Our data relating<br />
to clients and company fundamentals<br />
comprises an enormous amount of business<br />
intelligence that can predict the future<br />
behavior of markets under various<br />
economic and market conditions,” said<br />
T Rajah, CIO, CLSA.<br />
Use of real-time data is<br />
growing fast<br />
Nevertheless, versions of real-time<br />
technology are in widespread use. “Op-<br />
of the Australian market has up to 30%<br />
churn in power consumers. That means<br />
we may have to add 30% new customers<br />
a year just to keep the same customer<br />
base and it takes a lot of analytics to determine<br />
the best portfolio of customers<br />
to optimize the business results.”<br />
Airline passengers have a big need<br />
for real-time data. “One US airline carrier<br />
has a real-time system that enables<br />
it to automatically reroute, compensate<br />
and notify passengers when their connecting<br />
flights are delayed,” said Ram<br />
Menon, Chief Marketing Officer & Executive<br />
VP, Worldwide Product Strategy,<br />
TIBCO. “Thousands of events occur<br />
simultaneously—whether it is an airport<br />
curfew, weather delay, or baggage<br />
transaction—and all these events have<br />
the potential to impact other parts of an<br />
airline’s operation to drive up complexity.<br />
With real-time enterprise computing<br />
an organization can gain a dual benefit:<br />
opportunity seized and crisis averted.”<br />
“The average person is inundated with<br />
over 2,000 outbound marketing intererational<br />
reliability is a basic te<strong>net</strong> of<br />
electricity supply,” said Joe Locandro,<br />
director, Group <strong>IT</strong>, CLP Holdings. “A<br />
small voltage dip in <strong>Hong</strong> <strong>Kong</strong> can<br />
mean many people trapped in lifts, waiting<br />
to be freed by the Fire Services Dept.<br />
To avoid this, we monitor our whole system<br />
for wear and tear in real-time, from<br />
power plants, to substations, down to the<br />
feeder substation, and then analyze the<br />
data so that we can do predictive rather<br />
than scheduled maintenance. We also<br />
monitor weather conditions in detail, to<br />
predict the hottest peaks when consumers<br />
crank up their air conditioners and<br />
we have to meet the real time demand- as<br />
lagging supply is not an option.”<br />
“In Australia, we supply a real-time<br />
energy market, bidding every five minutes<br />
to determine our energy dispatch,”<br />
continued Locandro. “That means analyzing<br />
our own load profile, as well as<br />
the demand curve. Another challenge<br />
40 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
CLSA’s Rajah: Our data relating to clients<br />
and company fundamentals comprises an<br />
enormous amount of business intelligence<br />
ruptions a day: in response a US retailer<br />
studied customer responses to an alternative<br />
approach—real-time marketing<br />
campaigns. And what they found is that<br />
“relevant” offers made to customers<br />
based on real-time information such as<br />
a life event, a recent purchase, or a location-based<br />
transaction resulted in a respectable<br />
customer response rate,” said<br />
Menon. “Seemingly insignificant events<br />
in isolation are meaningless, however,<br />
with the ability to perform sophisticated<br />
real-time correlations, a big picture can<br />
be inferred and turned into a relevant offer<br />
embedded in the stream of life.”<br />
Managing customer expectations is<br />
also vital. “In bad weather it’s better if<br />
we contact the customer by SMS three<br />
hours before the flight and tell them they<br />
can’t fly and we’ve rebooked them on<br />
another flight,” said Tomasz Smaczny,<br />
director & CIO, Cathay Pacific Airways.<br />
“The customer doesn’t have to turn up<br />
and waste their time.”<br />
<strong>IT</strong> can be used to monitor any work<br />
and sometimes make radical improvements.<br />
“By monitoring our trading, we<br />
are very aware that 70% of our trading<br />
volume can be executed is during the last<br />
10 minutes of the day, and we can organize<br />
to benefit from that awareness,”<br />
added Rajah.<br />
The government also wants to share<br />
useful information. “After a traffic accident,<br />
we need to pass information to<br />
the police to deal with it, and also to the<br />
public, so drivers can reroute to avoid<br />
it,” said Jeremy Godfrey, GCIO, Office<br />
of the Government CIO. “We have<br />
a project to create a real-time repository<br />
of transport information. It will initially<br />
be for internal purposes, but we hope to<br />
provide public access, so that third parties<br />
can make the information available<br />
on platforms such as mobile phones and<br />
GPS-based route planning systems.”<br />
Privacy means op-in versus<br />
opt-out<br />
Godfrey wondered whether privacy<br />
concerns would impact real-time marketing.<br />
“In the last few weeks, there has<br />
been significant public concern about<br />
whether people have given genuinely<br />
informed consent for use of personal<br />
data in marketing,” said Godfrey. “You<br />
got a 6% response to your SMS, but that<br />
means 94% did not respond: do you<br />
know how many of them would be upset<br />
if they knew that their real-time location<br />
was being monitored and used for marketing<br />
purposes”<br />
Customers are not sheep, however,<br />
and it is necessary to pay attention to<br />
individual preferences, as the moderator<br />
pointed out. “When my wife filed her tax<br />
online and the tax office knew all about<br />
her previous employers, she was taken<br />
aback that they had such a large file on<br />
her,” said Chee Sing Chan, group editor,<br />
Computerworld <strong>Hong</strong> <strong>Kong</strong>. “I suppose<br />
some people will find real-time messages<br />
brilliant and others will not.”<br />
Speaking the customer’s language<br />
would seem important—but apparently<br />
we can’t all do it. “Do you know what<br />
really irritates me” asked Patrick Slesinger,<br />
director & CIO, Wallem Group.<br />
“The fact that I’m a gweilo, yet I receive<br />
Chinese text on my phone and Chinese<br />
telephone calls at home. I would prefer<br />
PCCW to make it known that there is a<br />
gweilo on this number!”<br />
If customer satisfaction is the goal,<br />
opt-in versus opt-out could be a sensitive<br />
issue in future. “When I sign up to download<br />
various software, one of the things<br />
I am resigned to doing is to un-subscribe<br />
from the promotional emails I get, which<br />
is part of my modus operandi,” said<br />
Roland Tesmer, head of <strong>IT</strong> Strategy &<br />
Planning, HK Jockey Club. “In contrast,<br />
when using the Telebet service at the<br />
Jockey Club, you have to elect to receive<br />
SMSs on the opt-in system.”<br />
Of course, the reason why people<br />
opt-in or-out comes back to relevance<br />
and utility of the information. “Imagine<br />
you are driving towards a traffic<br />
jam and you receive an SMS: ‘Go by<br />
another route,’—that information is<br />
really useful,” said Steve Siu, CIO,<br />
continued on page 42 4<br />
Godfrey from OGCIO: Recently there has<br />
been public concern in <strong>Hong</strong> <strong>Kong</strong> about use<br />
of personal data in marketing<br />
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 41
OOCL/Cargosmart. “It all depends on<br />
whether the information is useful to<br />
you.”<br />
4 continued from page 41 execution systems,” said David Brickler,<br />
managing director & CIO, <strong>IT</strong> Dept,<br />
Mizuho Securities Asia. “With high volume<br />
transactions in banking, with milliseconds<br />
between trading volume the<br />
latency issues mean your servers need to<br />
be on top of the exchange and you have<br />
to transact in memory.”<br />
“Algorithmic trading makes a distinct<br />
change in that the level in the application<br />
or programming stack where the decision<br />
making takes place is changed dramatically,”<br />
continued Brickler. “In algorithmic<br />
trading, a high-level person wants to<br />
roll out a trade with huge volume. Then<br />
ChinaTrust Commercial Bank’s Chang:<br />
The integration layer is the least disruptive<br />
architecture to move forward, but it’s a very<br />
difficult technology to manage<br />
The value of relevance and utility was<br />
quickly seconded by another professional.<br />
“I agree that, when you receive<br />
and SMS, it is the issue of relevance that<br />
makes you love or hate the information,”<br />
said Ruu-Tian Chang, CIM executive<br />
president, <strong>IT</strong>, ChinaTrust Commercial<br />
Bank. “When the bank uses real-time<br />
information to tell us that our ATM<br />
withdrawal is exceptionally high or at an<br />
unusual location, we all welcome the information.<br />
When it is used for sales, it’s<br />
probably the relevance that makes it acceptable.”<br />
How to program algorithms<br />
and objects<br />
Real-time technology doesn’t come<br />
free—more programmers will have to<br />
accept the challenge of working in the<br />
memory space. “We have built a federated<br />
structure across <strong>Hong</strong> <strong>Kong</strong> and Asia<br />
for consolidating information from lots<br />
of platforms, business intelligence and<br />
In 2004 we started to break our enterprise object<br />
model implemented in Smalltalk object database and<br />
we leveraged TIBCO to create a distributed object<br />
mode<br />
—Steve Siu, OOCL/Cargosmart<br />
the algorithm takes over and the decisionmaking<br />
process is totally transparent to<br />
the trader, who doesn’t care about it. The<br />
decision-making cranks away in the background<br />
and it is not just trades, but decisions<br />
such as the need to cope with the exchange<br />
opening and closing, because that’s<br />
when 80% of the business is done.”<br />
Real-time applications apparently<br />
call for a revamp of the object model<br />
underlying services. “In 2000 we expanded<br />
the scope of our transaction system<br />
into marketing and pricing,” said<br />
Siu. “In 2004 we started to break our<br />
enterprise object model implemented in<br />
Smalltalk object database and we leveraged<br />
TIBCO to create a distributed object<br />
model.”<br />
“We discovered the power of the<br />
enterprise message bus and started<br />
adding additional applications that depended<br />
on the complex event processing<br />
environment,” continued Siu. “The<br />
massive data needed provides a large<br />
challenge. We abstracted the attributes<br />
needed for different objects in a given<br />
domain in the memory space with<br />
more detail extract from database on<br />
demand basis because of the rule base<br />
advantage in complex event processing<br />
platform. The memory space is a new<br />
game, with no standard structure for<br />
handling today, but it provides power<br />
we can leverage.”<br />
An added bonus of real-time apps<br />
could be a big clean-up of the services<br />
repertoire. “The integration layer is very<br />
important. If you can develop architecture<br />
for one banking system and provide<br />
it to 17 countries, the synergy is pretty<br />
easy to understand,” said Chang. “But<br />
the integration layer is also important<br />
for cleaning up the past. Our bank was<br />
a latecomer to regionalization, but as we<br />
went through transaction renovation, introducing<br />
the trading system and banking<br />
system, the integration layer brought<br />
all the different legacy systems and standards<br />
to light.”<br />
“[The] integration layer is the least<br />
disruptive architecture to move forward,<br />
but it’s a very difficult technology to<br />
manage,” continued Chang. “When you<br />
buy TIBCO or Microsoft software, you<br />
are forced to obsolete old versions and<br />
there’s always an end-of-service policy.<br />
When we build SOA services in-house,<br />
we keep a bunch of old services, but now<br />
we have to clean up and move only valuable<br />
services to our mature future repertoire.”<br />
3<br />
42 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
BOCI partners with TIBCO<br />
to reach new heights.<br />
© 2010, TIBCO Software Inc. All rights reserved.<br />
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 31
TECHGUIDE<br />
IBM rolls out new zEnterprise mainframe server<br />
and auxiliary products<br />
Big iron from Big Blue features 96 microprocessors clocking in at 5.2GHz<br />
By Stefan Hammond in Jiangzhajie, Hunan Province<br />
In the center of the world’s most important<br />
21st century country, one of<br />
the world’s premier tech-vendors<br />
last month outlined the benefits of their<br />
latest mainframe computer.<br />
As IBM’s Dr Guraraj Rao put it in a<br />
keynote speech, “Given the workloads<br />
we have to process and keep secure in<br />
our data wards, if we did not have mainframes,<br />
we would have to invent them.”<br />
In this spirit, IBM announced a series<br />
of new products based around the 96-microprocessor-powered<br />
zEnterprise 196<br />
mainframe server, their zEnterprise BladeCenter<br />
Extension unit and their Unified<br />
Resource Manager software which<br />
integrates multiple platform resources as<br />
a single virtualized system and provides<br />
unified management for zEnterprise,<br />
said IBM in a statement.<br />
Moore’s Law and heavy R&D<br />
Ray Jones (IBM’s VP Worldwide,<br />
zSeries Software) said that “Moore’s<br />
Law is obsolete due to heat-dissipation,<br />
so Intel has added more cores, [which<br />
drives] down clock-speeds as silicon<br />
must be devoted to management. The<br />
mainframe model is quite different—<br />
they have more cache to maximize hitrates.”<br />
Other mainframe benefits cited<br />
by Jones include the microprocessor being<br />
“built into the mainframe. We call it<br />
‘fit-for-purpose’: workloads work best if<br />
they’re designed [into the system].”<br />
Dan O’Connell, VP, Mainframe Platform,<br />
IBM Growth Marketing Unit, said<br />
that the new System z, is a “new generation/new<br />
class [of machine] that’s getting<br />
a lot of attention in the marketplace. It’s a<br />
machine created with a lot of client-input.<br />
According to O’Connell, the new device<br />
is “the most scalable server, [and]<br />
now has the world’s fastest processor at<br />
5.2 GHz.” He added that IBM had invested<br />
over US$1 billion with each generation<br />
in the System z line.<br />
O’Connell said that client-input from<br />
finance users was invaluable, as many<br />
financial services are either considering<br />
or implementing core banking transformation.<br />
He added that HSBC in HK was<br />
the first order placed for this new zEnterprise<br />
in the region, and that his firm’s<br />
regional efforts were headquartered in<br />
Shanghai, as “China is the largest growing<br />
market—we’re targeting areas that<br />
are growing.<br />
“System z has had an 18% CAGR<br />
since 2003,” he said, citing internal data<br />
based on MIPS. “No matter how fast you<br />
grow, we can scale.”<br />
O’Connell added that China’s banks<br />
are “some of our biggest and most important<br />
clients,” and that another “sector<br />
is tax: state and local.”<br />
Data center panic<br />
Dr Guraraj Rao, IBM Fellow, systems<br />
chief engineer, systems hardware development,<br />
IBM Systems &Technology<br />
Group, declared that today’s data centers<br />
have huge challenges. “When we<br />
do CIO surveys, they complain about<br />
dedicated resources,” he said, “and 70%<br />
of CIO budgets are used to fix existing<br />
problems, not moving forward.”<br />
Rao pointed to the new add-ons in the<br />
system: the BladeCenter extension, and<br />
especially the Unified Resource Manager,<br />
which he described as “the glue that<br />
holds it all together.”<br />
IBM’s Jones: As far as we know, a System z<br />
mainframe has never been hacked<br />
Critical software<br />
“We see that mainframes handle data<br />
very well,” said Ray Jones, VP, System z<br />
software sales, IBM Software Group. “If<br />
users move these processes off the mainframe,<br />
they find it works more slowly.”<br />
Jones explained that a new OS—z/OS<br />
1.12—was needed to run the new hardware,<br />
and the total creation involved the<br />
collaboration of over 12,000 IBM engineers,<br />
including 5,000 on the software<br />
side.<br />
“The new OS improves performance<br />
40% to allow customers to manage their<br />
batch-windows,” said Jones. “Next year,<br />
Tivoli and 1.13 will make more improvements<br />
to the batch paradigm across the<br />
data center.”<br />
Jones also highlighted a feature of<br />
mainframes which is rarely highlighted,<br />
security. “As far as we know, a System z<br />
mainframe has never been hacked, partly<br />
as we hire some of the world’s toughest<br />
hackers,” he said. “Once they get out of<br />
prison, literally, we invite them to hack<br />
our systems. Mainframe security extends<br />
from elliptical keys in the microprocessor<br />
for mobile devices out to the end of<br />
the <strong>net</strong>work.” 3<br />
44 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
Awards<br />
2 0 1 0<br />
中 小 企 資 訊 世 界 大 獎<br />
立 即 投 票<br />
一<br />
人<br />
一<br />
票<br />
齊<br />
來<br />
參<br />
與<br />
www.cw.com.hk<br />
www.smb.com.hk/smbawards/2010/index.html<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 45
INDUSTRYPROFILE<br />
<strong>Hong</strong> <strong>Kong</strong> firm k-matrix targets<br />
online marketing benchmarks<br />
Social media marketing is the way to go, says Edmund Lee,<br />
CEO of k-matrix By Teresa Leung<br />
Lee from k-matrix: We have already collected<br />
1.2 billion documents<br />
CWHK: Why digital marketing intelligence<br />
Edmund Lee: We’d seen a lot of aggregated<br />
online data from forums, blogs<br />
and CGM (consumer-generated media)<br />
since the 2004-2005 timeframe. At that<br />
time, US-based developers already had<br />
products for analyzing such data, so we<br />
considered creating a product (k-matrix<br />
CI) for analyzing data related to <strong>Hong</strong><br />
<strong>Kong</strong>. The aim is to help businesses develop<br />
effective marketing and branding<br />
strategies and campaigns.<br />
We spent less than two years on R&D<br />
before releasing the first version of this<br />
product in 2006. Now we have released<br />
the third edition capable of natural language<br />
processing, and text-mining.<br />
Besides keywords, we look at how frequently<br />
keywords appear and the position<br />
in which they appear. Based on<br />
further context analysis, we label a post<br />
positive or negative.<br />
CWHK: How many founders are there<br />
EL: There are four of us. Now we have<br />
16 people in <strong>Hong</strong> <strong>Kong</strong> and around five<br />
in Shenzhen.<br />
CWHK: Do you have many competitors<br />
EL: We have only a few rivals. One of<br />
them is a Singapore-based company that<br />
doesn’t do much localization, while the<br />
others are mainland-based. However,<br />
many others that do online marketing intelligence<br />
collect their data manually.<br />
CWHK: How do you differentiate yourself<br />
EL: Our data-mining approach starts<br />
with text and data collection from influential<br />
local media. We cover 90 percent<br />
of <strong>Hong</strong> <strong>Kong</strong> media and popular forums<br />
such as Yahoo <strong>Hong</strong> <strong>Kong</strong> news,<br />
Uwant, discuss.com, and hkgolden.com.<br />
This way we can provide past data immediately<br />
and allow a more complete<br />
analysis for our customers. Our rivals<br />
lack historical data because their data<br />
collection is project-based.<br />
In the future, we plan to discover unknown<br />
terms. Now we are working with<br />
<strong>Hong</strong> <strong>Kong</strong> Poly U to develop a system<br />
that searches for the most-mentioned<br />
terms not yet known to us. In addition,<br />
we will look into tools that helps measure<br />
effectiveness of cross-channel campaigns<br />
[that use channels like] EDM<br />
(electronic direct marketing) and Facebook.<br />
CWHK: Is your service on an SaaS model<br />
EL: Yes. Since we have 1.2 billion documents<br />
we can’t offer it on-premise. Customers<br />
pay monthly charges and service<br />
fees for reports.<br />
CWHK: Who are your target customers<br />
EL: We target SMBs, but the early<br />
adopters are primarily enterprises. Most<br />
of the users are involved in sales of consumer<br />
goods, corporation communications<br />
departments of large firms, and<br />
companies or business units that do PR<br />
and marketing.<br />
We also have presence in the nonprofit/social<br />
service sectors. Some of our<br />
paying customers include Caritas, which<br />
looks for young drug takers online, and<br />
Samaritans, which searches online for<br />
people who might commit suicide.<br />
CWHK: Geographically where are most<br />
of your clients from<br />
EL: <strong>Hong</strong> <strong>Kong</strong>. We have a small number<br />
of clients from the mainland and Taiwan.<br />
The China market can accommodate<br />
several companies like ours because<br />
of its size.<br />
Businesses don’t want to use a service<br />
from the same company serving their<br />
competitors. The major challenges include<br />
localization, a colossal collection<br />
of data, and channel partnership.<br />
CWHK: Tell me more about your partnership<br />
with <strong>Hong</strong> <strong>Kong</strong>-based Admomo.<br />
EL: While Admomo’s forte is online ad<br />
spending data, we focus on sentiment.<br />
We combine our strength and provide<br />
measurement of the effectiveness of<br />
marketing and branding exercises.<br />
CWHK: What’s your next milestone, and<br />
how do you plan to achieve it<br />
EL: Many businesses want to spend<br />
on social media marketing but without<br />
benchmarks. We hope to provide<br />
benchmarks for them to measure campaign<br />
success. We are also in talks with<br />
a VC—aiming to expand overseas by<br />
helping foreign firms tap the mainland<br />
market. 3<br />
46 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
http://www.questexevents.<strong>net</strong>/dcshk<br />
Diamond Sponsor<br />
Platinum Sponsor<br />
Hitachi Data Systems<br />
Delegate Bag Sponsor<br />
Luncheon Sponsor<br />
Gold Sponsor<br />
O r a n g e B u s i n e s s S e r v i c e s v i s u a l i d e n t i t y - a p r i l 2 0 0 6<br />
Hitachi Data Systems<br />
Coffee Break Sponsor<br />
Exhibition Sponsor<br />
Prize Sponsor<br />
Research Partner<br />
Supporting Organizations<br />
Official Media<br />
For enquiries, please contact Connie Yip Tel: 2589 1373 Email: cyip@questexasia.com
conference / seminar / forum / round table / user guides<br />
Finding a target audience for your products<br />
Proudly presents<br />
Events<br />
User Guides<br />
Grasp the chance and contact us now.<br />
Event Manager Joyce Chung Account Director Connie Yip<br />
Tel: 2589 1360 jchung@questexasia.com Tel: 2589 1373 cyip@questexasia.com<br />
48 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
For enquiries, please call Connie Yip at 9407 5454.<br />
E-mail: cyip@questexasia.com<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
R<br />
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 49
BACKPAGE r o b e r t c l a r k<br />
China: from tech laggard to green superpower<br />
Despite a lack of <strong>innovation</strong>, China’s scale will<br />
eventually lead the world in, among other things,<br />
clean energy<br />
China’s economy has passed Japan’s to become the<br />
world’s second largest. Some economists think it may<br />
overtake the US as early as 2027, although (as usual)<br />
other economists disagree.<br />
It’s quite a milestone. Inevitably China will overtake the US<br />
on size alone. The interesting question is whether it will lead the<br />
world in <strong>innovation</strong> and not just in scale.<br />
Exports rule<br />
If I had to choose an <strong>IT</strong> firm that best represented China’s<br />
economy, it wouldn’t be a home-grown champion like Huawei.<br />
Rather, it would be like an export manufacturer like Foxconn,<br />
which has built immense scale out of leveraging China’s low<br />
wages and good infrastructure.<br />
Yes, Foxconn is Taiwan-owned, but that underlines the fact<br />
that China’s export economy is driven by non-mainland companies.<br />
Like China itself, Foxconn is suffering blowback from<br />
its mercenary approach to labor management. And most of all,<br />
Foxconn is an assembly manufacturer that makes money in the<br />
Chinese way, at the low-end of the value chain.<br />
The US, at the other end, is China’s benchmark. It’s tempting<br />
to compare the US to Microsoft—which has minted fortunes out<br />
of its hammerlock on strategic products—or the clever, highminded<br />
Googlers.<br />
But if I had to name one company, it would be IBM—thanks<br />
to its size, longevity and ability to reinvent itself. Big Blue got its<br />
first big break with the 1905 US census and went onto dominate<br />
timeshare, mainframes and PCs and now services. Its strength is<br />
its ability to execute profitably and build a system of <strong>innovation</strong>.<br />
That’s what China lacks. Old China may have given the world<br />
the compass, printing and gunpowder, but there isn’t a single<br />
idea from modern China that has been adopted elsewhere.<br />
Brand equity<br />
One obvious marker is brands. By the mid-1970s, 30 years after<br />
the end of World War II, the Japanese economic miracle had<br />
created global brands such as Sony, Yamaha and Toyota.<br />
Three decades after China began opening its economy, it can<br />
claim Lenovo (thanks to the purchase of IBM’s PC business)<br />
and Hai’er. Neither is exactly a household name, and in both<br />
cases their market share outside China is insignificant.<br />
China’s <strong>IT</strong> leaders are firms such as Huawei (which builds<br />
standards-based products at lower prices), Baidu (which has<br />
its own search technology but a business model cut-and-pasted<br />
from Google) look-alike aggregators like Netease and Sina, and<br />
quasi-monopolies like China Mobile. There are also gaps, like<br />
the absence of large enterprise software firms.<br />
Innovation gap<br />
The problem is China’s authoritarian, top-down political system,<br />
which weighs heavily on <strong>innovation</strong>. The government interferes<br />
directly in industry and splashes a good deal of cash trying to<br />
pick winners. Private firms are unable to borrow cash from stateowned<br />
banks unless they develop connections to key officials.<br />
China produces 350,000 engineers, but most of these are unemployable<br />
in world-class companies. The best go abroad if<br />
they can and most stay there.<br />
The education system promotes math but discourages critical<br />
thinking. The culture disdains those who have failed. The political<br />
system penalizes the kind of free expression and spontaneity<br />
that fueled the creation of Silicon Valley. In addition to all of<br />
the above, the low level of trust deters collaboration between<br />
complementary teams.<br />
The future: green tech<br />
Yet despite all this, China is set to become the world’s leading<br />
center for green technologies. China already runs the world’s<br />
biggest wind power deployments and, according to the Pew<br />
Charitable Trusts, last year invested US$34.6 billion in clean<br />
energy, nearly double the US total of $16.8 billion. The World<br />
Economic Forum expects the global clean energy market will<br />
reach $450 billion annually by 2012 and<br />
$600 billion by 2020.<br />
With that kind of scale, and in the face<br />
of fragmented efforts by the rest of the<br />
world, China has the ability to design,<br />
test and commercialize clean technologies<br />
that will be in demand within its<br />
own economy and across the developing<br />
world.<br />
Which goes back to my original analogy.<br />
The best economies, like the best<br />
businesses, need only execute better than<br />
their rivals. 3<br />
Robert Clark is<br />
a <strong>Hong</strong> <strong>Kong</strong>based<br />
technology<br />
journalist.<br />
rclark@electricspeech.com<br />
C<br />
M<br />
Y<br />
CM<br />
MY<br />
CY<br />
CMY<br />
K<br />
50 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk
www.cw.com.hk<br />
September 2010 Computerworld <strong>Hong</strong> <strong>Kong</strong> 51
52 Computerworld <strong>Hong</strong> <strong>Kong</strong> September 2010 www.cw.com.hk