Group 1 Failures in Data Security Management
Group 1 Failures in Data Security Management
Group 1 Failures in Data Security Management
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>Group</strong> 1<br />
<strong>Failures</strong> <strong>in</strong> <strong>Data</strong> <strong>Security</strong> <strong>Management</strong>
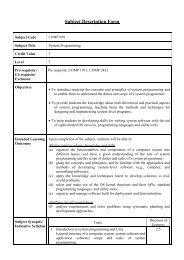
Introduction<br />
<strong>Data</strong> <strong>Security</strong> helps ensur<strong>in</strong>g privacy, and<br />
protect<strong>in</strong>g personal data. In this century,<br />
although data is very important to the<br />
bus<strong>in</strong>ess of corporate, they did not put the<br />
data security <strong>in</strong> high priority, and the<br />
budget was also very little. <strong>Data</strong> security<br />
breaches were happened so often <strong>in</strong><br />
those corporate.
Corporate background<br />
• Lowe’s<br />
<br />
US-based cha<strong>in</strong> of retail home improvement and appliance stores<br />
In 2007, Ranked 48 on the FORTUNE® 500<br />
• TCI (Teledata Communications Inc.)<br />
<br />
The leader <strong>in</strong> affordable browser-based loan orig<strong>in</strong>ation software<br />
and background check software for small and mid-sized bus<strong>in</strong>esses<br />
• Bank of America<br />
<br />
The largest bank by assets and second largest commercial bank by<br />
deposits and market capitalization <strong>in</strong> US<br />
• ChoicePo<strong>in</strong>t<br />
<br />
Date aggregation company <strong>in</strong> US
Problem of the four<br />
companies<br />
• Lowe’s – Hardware Issue<br />
Lack of Internet security<br />
Network open to anyone<br />
No Laptop access control<br />
• TCI – Human Issue<br />
Employee lack of ethical knowledge and<br />
responsibility<br />
<strong>Security</strong> policy and procedure
Problem of the four<br />
companies<br />
• Bank of America – <strong>Data</strong> security issue<br />
Valuable data without protection<br />
Customer data without encryption<br />
• Choice Po<strong>in</strong>t – Technology issue<br />
Unreliable safeguards<br />
No customer data check<strong>in</strong>g
Preventive<br />
Measurement<br />
• <strong>Security</strong> Policy - Acceptable use policy (AUP)<br />
guidel<strong>in</strong>e <strong>in</strong> details to enhance employees’<br />
ethical knowledge<br />
rules to restrict users or employees<br />
allowable to use or access the local network<br />
and Internet<br />
approved by CIO and signed up by all<br />
employees<br />
def<strong>in</strong>itely not allowed to use<br />
client’s password
Preventive<br />
Measurement<br />
• Secur<strong>in</strong>g the Wireless Network and WiFiequipped<br />
device<br />
publish a Coverage Map of the Wireless<br />
Network<br />
access track<strong>in</strong>g <strong>in</strong> handl<strong>in</strong>g a security <strong>in</strong>cident<br />
protect the entire WiFi network<br />
perform regular check<strong>in</strong>g of log records<br />
prevent the crim<strong>in</strong>al to the network
<strong>Security</strong> Measurement<br />
• <strong>Data</strong> Encryption System<br />
<br />
<br />
<br />
<br />
protect its data and to prevent the crime<br />
happened <strong>in</strong> the data loose<br />
make data unreadable to unspecific party<br />
key must be kept secure<br />
prevent data aga<strong>in</strong>st the threat of<br />
lost or stolen
<strong>Security</strong> Measurement<br />
• <strong>Security</strong> Audit<br />
check<strong>in</strong>g process of security measure<br />
f<strong>in</strong>d out current environment is securely<br />
protected<br />
exam<strong>in</strong>e and analyze safeguards<br />
failure to fulfill the security audit <strong>in</strong> Choice<br />
Po<strong>in</strong>t<br />
failure to f<strong>in</strong>d out unreliable<br />
safeguards
<strong>Data</strong> <strong>Security</strong><br />
<strong>Management</strong><br />
• consideration of the preventive and<br />
security measurements<br />
• work out the solution<br />
• prevent the unexpected crime<br />
• protect valuable customer data<br />
• responsibility of each employee <strong>in</strong> the<br />
organization
Latest Development –<br />
Lowe’s<br />
Lowe’s<br />
• Standard methods<br />
• Secure Sockets Layer<br />
• Verisign digital security certificate
Latest Development - TCI<br />
TCI<br />
• IP address restrictions<br />
• Time restrictions.<br />
• Limit user access by function.<br />
• <strong>Data</strong> encryption.
Latest Development -<br />
ChoicePo<strong>in</strong>t<br />
A.Inventory and Limit Access to Sensitive<br />
Consumer Information<br />
B.B. Credential Customers, Employees, and<br />
Vendors<br />
C. Establish Corporate Accountability<br />
D. Execute Policies, Procedures and<br />
Guidel<strong>in</strong>es<br />
E. Self Regulate Through Audit and<br />
Compliance
Latest Development -<br />
ChoicePo<strong>in</strong>t<br />
F. Implement Technology Solutions<br />
G. Tra<strong>in</strong> and Educate Associates<br />
H. Enhance Internal and External Outreach<br />
Program<br />
I. Transparency with Consumers
Latest Development -<br />
Bank of America<br />
• Credit Protection Plus<br />
• Photo <strong>Security</strong><br />
• Safety Tips<br />
• Demos and Guides