SRA 221 - Penn State Altoona
SRA 221 - Penn State Altoona
SRA 221 - Penn State Altoona
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
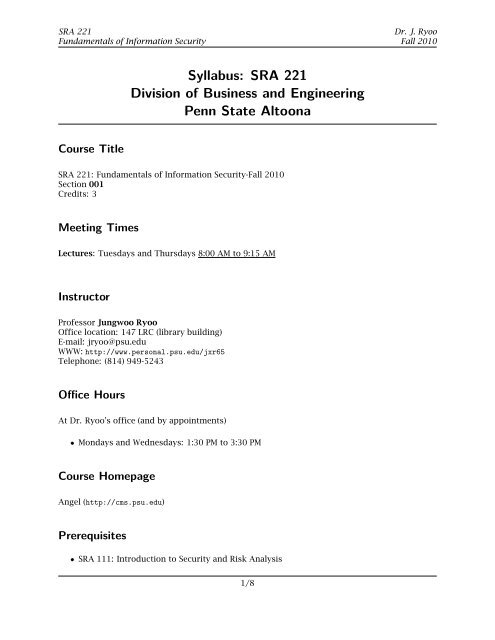
<strong>SRA</strong> <strong>221</strong><br />
Fundamentals of Information Security<br />
Dr. J. Ryoo<br />
Fall 2010<br />
Syllabus: <strong>SRA</strong> <strong>221</strong><br />
Division of Business and Engineering<br />
<strong>Penn</strong> <strong>State</strong> <strong>Altoona</strong><br />
Course Title<br />
<strong>SRA</strong> <strong>221</strong>: Fundamentals of Information Security-Fall 2010<br />
Section 001<br />
Credits: 3<br />
Meeting Times<br />
Lectures: Tuesdays and Thursdays 8:00 AM to 9:15 AM<br />
Instructor<br />
Professor Jungwoo Ryoo<br />
Office location: 147 LRC (library building)<br />
E-mail: jryoo@psu.edu<br />
WWW: http://www.personal.psu.edu/jxr65<br />
Telephone: (814) 949-5243<br />
Office Hours<br />
At Dr. Ryoo's office (and by appointments)<br />
• Mondays and Wednesdays: 1:30 PM to 3:30 PM<br />
Course Homepage<br />
Angel (http://cms.psu.edu)<br />
Prerequisites<br />
• <strong>SRA</strong> 111: Introduction to Security and Risk Analysis<br />
1/8
<strong>SRA</strong> <strong>221</strong><br />
Fundamentals of Information Security<br />
Dr. J. Ryoo<br />
Fall 2010<br />
• IST 110: Information, People, and Technology<br />
• CMPSC 101: Introduction to C++ Programming<br />
Required Texts<br />
Raymond R. Panko, Corporate Computer and Network Security, Prentice Hall, 2009 (ISBN: 0-13-<br />
185475-5).<br />
Course Description<br />
<strong>SRA</strong> <strong>221</strong> provides an overview of information security including security architecture, access control,<br />
and secure Internet applications. This course is required for all <strong>SRA</strong> majors and covers the<br />
following topics:<br />
• Security Fundamentals,<br />
• Basics of Cryptography,<br />
• Firewall Technologies,<br />
• Virtual Private Networks (VPNs),<br />
• Authentication,<br />
• Access Control,<br />
• Privacy and Identity Protection<br />
• Intrusion Detection, and<br />
• Software Security.<br />
with a focus on the relationship to e-business and the digital global economy.<br />
The aforementioned topics will be presented with relevant hands-on learning modules to promote<br />
deeper understanding. In addition, students will be given a term project in which they can<br />
synthesize the concepts and skills obtained during lecture sessions.<br />
2/8
<strong>SRA</strong> <strong>221</strong><br />
Fundamentals of Information Security<br />
Course Objectives<br />
Dr. J. Ryoo<br />
Fall 2010<br />
In this course, students should learn:<br />
• The fundamental concepts and issues of information security,<br />
• The mainstream information security technologies,<br />
• How real world enterprises are attacked, and<br />
• How to defend an organization against well known cyber attacks.<br />
Topics<br />
• Module 1: Security Fundamentals<br />
• Module 2: Access Control<br />
• Module 3: Firewall Technologies<br />
• Module 4: Basics of Cryptography<br />
• Module 5: Virtual Private Networks (VPNs)<br />
• Module 6: Authentication<br />
• Module 7: Privacy and Identity Protection<br />
• Module 8: Intrusion Detection<br />
• Module 9: Software Security<br />
3/8
<strong>SRA</strong> <strong>221</strong><br />
Fundamentals of Information Security<br />
Tentative Schedule<br />
Dr. J. Ryoo<br />
Fall 2010<br />
Date Week Session Lecture Topics Chapter Homework Due<br />
8/23/2010 1 1 Security Fundamentals 1<br />
8/25/2010 1 2 Security Fundamentals 1 Photo, Team Info., Bio.<br />
8/30/2010 2 3 Planning 2<br />
9/1/2010 2 4 Access Control 5 Team Contract<br />
9/6/2010 3 5 Access Control 5<br />
9/8/2010 3 6 Access Control 5 Research Proposal<br />
9/13/2010 4 7 Firewalls 6<br />
9/15/2010 4 8 Firewalls 6<br />
9/20/2010 5 9 Firewalls 6 Extra Credit<br />
9/22/2010 5 10 Exam Prep 6<br />
9/27/2010 6 11 Midterm Exam One<br />
9/29/2010 6 12 The Elements of Cryptography 3 Project Report One<br />
10/4/2010 7 13 The Elements of Cryptography 3<br />
10/6/2010 7 14 The Elements of Cryptography 3<br />
10/11/2010 8 15 Second Life N/A<br />
10/13/2010 8 16 Second Life N/A<br />
10/18/2010 9 17 Second Life N/A<br />
10/20/2010 9 18 Second Life N/A<br />
10/25/2010 10 19 Cryptographic System Standards 4<br />
10/27/2010 10 20 Cryptographic System Standards 4<br />
11/1/2010 11 21 Exam Prep 4 Project Report Two<br />
11/3/2010 11 22 Midterm Exam Two<br />
11/8/2010 12 23 Application Security 8<br />
11/10/2010 12 24 Application Security 8<br />
11/15/2010 13 25 Application Security 8<br />
11/17/2010 13 26 Intrusion Detection Systems N/A<br />
11/22/2010 14 N/A Thanksgiving N/A<br />
11/24/2010 14 N/A Thanksgiving N/A<br />
11/29/2010 15 29 Intrusion Detection Systems N/A<br />
12/1/2010 15 30 Intrusion Detection Systems N/A<br />
12/6/2010 16 31 Term Project Presentations 9<br />
12/8/2010 16 32 Term Project Presentations 9 Final Project Report<br />
Grading Policy<br />
Grade Distribution<br />
• Labs: 10%<br />
• Homework Assignments: 10%<br />
• Term Project 10%<br />
• Midterm I: 20%<br />
• Midterm II: 20%<br />
• Final: 30%<br />
• In-class presentations: 2% extra credit<br />
4/8
<strong>SRA</strong> <strong>221</strong><br />
Fundamentals of Information Security<br />
Dr. J. Ryoo<br />
Fall 2010<br />
There will also be pop quizzes throughout the semester. Their results will be used as extra<br />
credit (3%) to boost your overall grade.<br />
Grading Scale<br />
A: 93% to 100%<br />
A-: 90% to 92.9%<br />
B+: 87% to 89.9%<br />
B: 83% to 86.9%<br />
B-: 80% to 82.9%<br />
C+: 77% to 79.9%<br />
C: 70% to 76.9%<br />
D: 60% to 69.9%<br />
F: less than 60%<br />
Course Format<br />
In a real-life work environment, problem solving and troubleshooting skills are a must. Even<br />
more important is an ability to gain new knowledge and apply it in the process. The format of<br />
this class is deliberately designed to help students acquire these skills throughout the semester.<br />
At the beginning of each class, students will be given a coherent set of problems and learning<br />
objectives relevant to these problems (5 minutes). All the information necessary to solve the<br />
problems will be provided during the lecture (45 minutes). Students then work on a quiz and<br />
hands-on exercise (25 minutes) based on the problems posed earlier in the class.<br />
Term Project<br />
Throughout the semester each student will participate in a group project. A group will consist of<br />
three students. The nature of the project is either (1) scholarly research or (2) Community<br />
Service Learning (CSL).<br />
Students participating in research project groups will be guided and advised by me at each<br />
important juncture of their research project and will be taught basic academic research skills. A<br />
set of candidate topics will be available. A research group may pursue a topic of its own choice<br />
with a prior permission from me.<br />
Below is a summary of the tentative project schedule and deliverables at each milestone.<br />
• Proposals and references (Due on September 8th)<br />
– Research groups: consult Research Proposal Preparation Guideline on Angel.<br />
• Project Report Part One (Due on September 29th)<br />
Consult the Project Report document on Angel.<br />
– Research Group Project Report: include group members, your research topic, copies of<br />
scholarly journal articles, and 5 page partially finished term paper (not including the<br />
references) of your proposed paper.<br />
5/8
<strong>SRA</strong> <strong>221</strong><br />
Fundamentals of Information Security<br />
Dr. J. Ryoo<br />
Fall 2010<br />
• Project Report Two (Due on November 1st)<br />
Consult the Status Report document on Angel.<br />
– Research Group Project Report Two: include group members, your research topic, a 10<br />
page updated term paper, and a list of tasks yet to be accomplished.<br />
• Submission of presentation materials (Due on December 1st)<br />
PowerPoint slides, videos, and exam questions must be turned in on time. Follow<br />
guidelines on Angel.<br />
• Research presentations:<br />
– Place: classroom<br />
• Submission of the Final Project Report (3000 words excluding the references) (Due on<br />
December 8th).<br />
• Publications The authors of the papers of excellent quality will have a chance to present<br />
their work in one of the following conferences:<br />
– International Conference on Business, Economics, and Information Technology<br />
(ICBEIT) 2011 Guam, March, 2011.<br />
∗ http://www.aa.psu.edu/icbeit/<br />
– <strong>Penn</strong> <strong>State</strong> <strong>Altoona</strong> Annual Undergraduate Research Fair, April 2011.<br />
∗ http://www.aa.psu.edu/honors/URF.htm<br />
– <strong>Penn</strong> <strong>State</strong> Behrend-Sigma Xi: Undergraduate Research and Creative Accomplishment<br />
Conference, April, 2011.<br />
∗ http://www.erie.psu.edu/research/<br />
Important Dates<br />
• September 1: Add/Drop deadline<br />
• September 27: Midterm exam I<br />
• November 3: Midterm exam II<br />
• December 10: Last day to withdraw from the class<br />
• December : Final exam<br />
Attendance<br />
Students are expected to attend every class unless there are health or other justifiable reasons.<br />
Make-up Examinations<br />
Students are required to make every effort to take all examinations at their scheduled times. If a<br />
student will have to be absent for any University-approved and documented reasons at the time<br />
of midterm or final examinations, he or she must contact the instructor well in advance of the<br />
examinations (at least one day prior to the examination) to make special arrangements. Note<br />
that make-up exams are given on the following Friday (of the originally scheduled exam) at<br />
4:00 PM.<br />
6/8
<strong>SRA</strong> <strong>221</strong><br />
Fundamentals of Information Security<br />
Classroom Etiquette<br />
Dr. J. Ryoo<br />
Fall 2010<br />
In general, students are expected to behave in a way that does not hinder other students'<br />
learning. For example, students are expected to turn off their cell phones before each class. Do<br />
not bring your cell phone on the midterm and final exam days.<br />
Assignment Submission and Deadline Policies<br />
Homework assignments must be submitted by the designated due date. Students are<br />
recommended to type their homework and to use electronic submission (Angel). A drop box will<br />
be created for each assignment. Handwritten homework will not be considered if not legible. In<br />
case of electronic submission, printed copies are still expected to be handed in before class on<br />
the due date. Assignments are assessed a ten percent per-day late penalty, up to a maximum of<br />
four days. Unless the problem is apocalyptic, don't give execuses. Students with legitimate<br />
reasons who contact the professor before the deadline may apply for an extension.<br />
Communication Policies<br />
The instructor prefers E-mails to phone calls. Dr. Ryoo checks his E-mail regularly. Therefore,<br />
sending an E-mail is the best way to contact him.<br />
<strong>Penn</strong> <strong>State</strong> University’s Academic Integrity Policy<br />
Academic Integrity Definition and Expectations: Academic integrity is the pursuit of scholarly<br />
activity in an open, honest and responsible manner. Academic integrity is a basic guiding<br />
principle for all academic activity at The <strong>Penn</strong>sylvania <strong>State</strong> University, and all members of the<br />
University community are expected to act in accordance with this principle. Consistent with this<br />
expectation, the University's Code of Conduct states that all students should act with personal<br />
integrity, respect other students' dignity, rights and property, and help create and maintain an<br />
environment in which all can succeed through the fruits of their efforts.<br />
Academic integrity includes a commitment not to engage in or tolerate acts of falsification,<br />
misrepresentation or deception. Such acts of dishonesty violate the fundamental ethical<br />
principles of the University community and compromise the worth of work completed by others.<br />
(Policies and Rules for Students, Section 49-20.)<br />
Consequences of academic dishonesty: The instructor may assign an academic sanction<br />
ranging from a warning, to failure on an assignment or in the course, or to removal from the<br />
course. (Note that a failure in a course may affect a student's status in a program and/or in the<br />
University.) The instructor reports each academic sanction to the Office of Judicial Affairs, which<br />
keeps a record. Students can appeal academic sanctions to the Committee on Academic Integrity<br />
through the Office of Academic Affairs. In more serious cases of academic dishonesty, the<br />
Office of Judicial Affairs may apply disciplinary sanctions in addition to the academic sanctions.<br />
These may range from a warning to probation, suspension or expulsion from the University. An<br />
XF grade is a formal University disciplinary sanction that indicates on the student's academic<br />
transcript that failure in a course was due to a serious act of academic dishonesty. (Policies and<br />
Rules for Students, Section 49-20, and Academic Integrity Procedure G-9.)<br />
7/8
<strong>SRA</strong> <strong>221</strong><br />
Fundamentals of Information Security<br />
Dr. J. Ryoo<br />
Fall 2010<br />
While students can help each other (no more than two people in a group) with their homework<br />
assignments, they are still expected to do their own work individually. Copying<br />
someone else's work is not permitted at all. Note that the instructor checks similarities to<br />
ensure the originality of the work.<br />
<strong>State</strong>ment on Accessibility<br />
If you have a documented disability which requires classroom accommodations, please notify<br />
the instructor. All students with disabilities are required to register with Office for Disability<br />
Services on campus for the provisions of appropriate accommodations. Disability Services is<br />
located in the Health and Wellness Center, 814-949-5540.<br />
The content of this syllabus is subject to change during the semester on a daily basis. The<br />
changes will be announced in class and the details of the revisions will be reflected on the<br />
course homepage.<br />
8/8