CPIT (InfoSec) Sample Questions 1. When there is a breach of ...
CPIT (InfoSec) Sample Questions 1. When there is a breach of ...
CPIT (InfoSec) Sample Questions 1. When there is a breach of ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
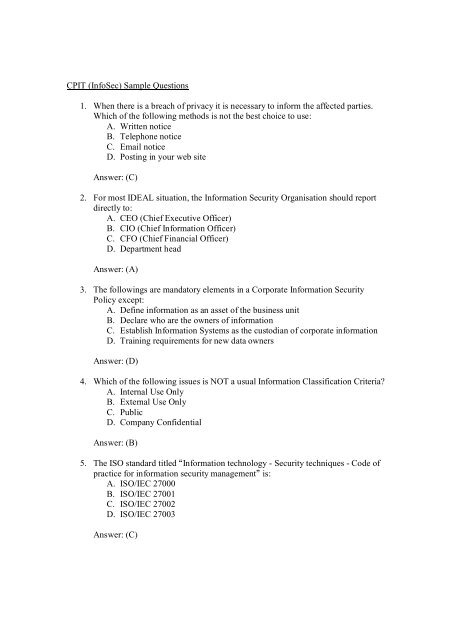
<strong>CPIT</strong> (<strong>InfoSec</strong>) <strong>Sample</strong> <strong>Questions</strong><br />
<strong>1.</strong> <strong>When</strong> <strong>there</strong> <strong>is</strong> a <strong>breach</strong> <strong>of</strong> privacy it <strong>is</strong> necessary to inform the affected parties.<br />
Which <strong>of</strong> the following methods <strong>is</strong> not the best choice to use:<br />
A. Written notice<br />
B. Telephone notice<br />
C. Email notice<br />
D. Posting in your web site<br />
Answer: (C)<br />
2. For most IDEAL situation, the Information Security Organ<strong>is</strong>ation should report<br />
directly to:<br />
A. CEO (Chief Executive Officer)<br />
B. CIO (Chief Information Officer)<br />
C. CFO (Chief Financial Officer)<br />
D. Department head<br />
Answer: (A)<br />
3. The followings are mandatory elements in a Corporate Information Security<br />
Policy except:<br />
A. Define information as an asset <strong>of</strong> the business unit<br />
B. Declare who are the owners <strong>of</strong> information<br />
C. Establ<strong>is</strong>h Information Systems as the custodian <strong>of</strong> corporate information<br />
D. Training requirements for new data owners<br />
Answer: (D)<br />
4. Which <strong>of</strong> the following <strong>is</strong>sues <strong>is</strong> NOT a usual Information Classification Criteria?<br />
A. Internal Use Only<br />
B. External Use Only<br />
C. Public<br />
D. Company Confidential<br />
Answer: (B)<br />
5. The ISO standard titled Information technology - Security techniques - Code <strong>of</strong><br />
practice for information security management <strong>is</strong>:<br />
A. ISO/IEC 27000<br />
B. ISO/IEC 27001<br />
C. ISO/IEC 27002<br />
D. ISO/IEC 27003<br />
Answer: (C)
6. Which <strong>of</strong> the following core principles <strong>of</strong> information security pertains to the<br />
request that Data cannot be modified without proper authorization?<br />
A. Integrity<br />
B. Confidentiality<br />
C. Non-repudiation<br />
D. Data Protection<br />
Answer: (A)<br />
7. To perform a successful information system security audit, the following areas <strong>of</strong><br />
computer activity should be monitored on a regular bas<strong>is</strong> except:<br />
A. Virus Scanning<br />
B. User Access Control<br />
C. System Activities<br />
D. Audit Trail<br />
Answer: (A)<br />
8. Which <strong>of</strong> the following steps <strong>is</strong> usually mandatory in the information system<br />
security audit process?<br />
A. Provide a system performance report<br />
B. Provide an audit report<br />
C. Provide a ROI (Return on Investment) report<br />
D. Provide a security report<br />
Answer: (B)<br />
9. Computer "security" <strong>is</strong> a conceptual idea attained by the use <strong>of</strong> three processes,<br />
but not including which <strong>of</strong> the followings?<br />
A. Prevention<br />
B. Dectection<br />
C. Backup<br />
D. Response<br />
Answer: (C)<br />
10. In the case <strong>of</strong> computer security audit on network vulnerabilities, the followings<br />
are the three main areas <strong>of</strong> control except:<br />
A. Interception Controls<br />
B. Availability Controls<br />
C. Access / entry point Controls<br />
D. Encryption Controls<br />
Answer: (D)
1<strong>1.</strong> During the BCP process, which <strong>of</strong> the following parties <strong>is</strong> responsible for granting<br />
final approval and providing ongoing support?<br />
A. Functional Business Units<br />
B. BCP Committee<br />
C. Chief Information Officer<br />
D. Executive Management<br />
Answer: (D)<br />
12. Which <strong>of</strong> the following <strong>is</strong> the top priority <strong>of</strong> d<strong>is</strong>aster response?<br />
A. Ensuring all personnel safety<br />
B. Protecting all data<br />
C. Resuming all business functions<br />
D. Protecting all networking equipment<br />
Answer: (A)<br />
13. Which <strong>of</strong> the following areas <strong>of</strong> enterpr<strong>is</strong>e requires business continuity plan?<br />
A. Marketing area <strong>of</strong> the enterpr<strong>is</strong>e.<br />
B. Operating area <strong>of</strong> the enterpr<strong>is</strong>e<br />
C. Financial area <strong>of</strong> the enterpr<strong>is</strong>e<br />
D. All area <strong>of</strong> the enterpr<strong>is</strong>e<br />
Answer: (D)<br />
14. Which <strong>of</strong> the following <strong>is</strong> NOT identified by a Business Impact Analys<strong>is</strong>?<br />
A. The name <strong>of</strong> individuals to be contacted during a d<strong>is</strong>asters<br />
B. Areas that would suffer the greatest financial or operational loss in<br />
d<strong>is</strong>asters<br />
C. The outage time that can be tolerated as a result <strong>of</strong> d<strong>is</strong>asters<br />
D. Systems critical to the survival <strong>of</strong> the enterpr<strong>is</strong>e<br />
Answer: (C)<br />
15. Which <strong>of</strong> the following <strong>is</strong> a hot-site facility?<br />
A. A site with pre-installed computers, ra<strong>is</strong>ed floor, air conditioning,<br />
telecommunications and networking equipment, and UPS<br />
B. A site with ready made work space with telecommunication equipment,<br />
LANs, PCs, and terminals for work groups.<br />
C. A site in which space <strong>is</strong> reserved with pre-installed wiring and ra<strong>is</strong>ed<br />
floors<br />
D. A site with ra<strong>is</strong>ed floors, air conditioning, telecommunications and<br />
networking equipment and UPS<br />
Answer: (A)
16. Which one <strong>of</strong> the following represents transference <strong>of</strong> r<strong>is</strong>k?<br />
A. Reduce the probability <strong>of</strong> a r<strong>is</strong>k occurring<br />
B. Lower the impact <strong>of</strong> a r<strong>is</strong>k if materialized<br />
C. Purchase insurance coverage for the r<strong>is</strong>k<br />
D. Eliminate the threat completely<br />
Answer: (C)<br />
17. The annualized rate <strong>of</strong> occurrence (ARO) <strong>is</strong> a value that represents:<br />
A. The estimated frequency <strong>of</strong> a specific threat taking place within a one-year<br />
time frame<br />
B. The estimated loss in dollar amount resulting from a specific threat within<br />
a one-year time frame<br />
C. The estimated costs in dollar amount incurred in protection from a specific<br />
threat within a one-year time frame<br />
D. The estimated probability <strong>of</strong> a specific threat taking place within a oneyear<br />
time frame<br />
Answer: (A)<br />
18. An action to determine the sequence <strong>of</strong> events <strong>is</strong> known as:<br />
A. Sequential Analys<strong>is</strong><br />
B. Timeline Analys<strong>is</strong><br />
C. Event Analys<strong>is</strong><br />
D. Priority Analys<strong>is</strong><br />
Answer: (B)<br />
19. All <strong>of</strong> the followings are layers described in TCP/IP model except:<br />
A. Application Layer<br />
B. Internet Layer<br />
C. Link Layer<br />
D. Physical Layer<br />
Answer: (D)<br />
20. All <strong>of</strong> the following are valid form <strong>of</strong> announcement used in the computer<br />
security incident response management except:<br />
A. Testimony<br />
B. Adv<strong>is</strong>ory<br />
C. Alert<br />
D. Heads-up Note<br />
Answer: (A)