IT-Security Evaluation Criteria
IT-Security Evaluation Criteria
IT-Security Evaluation Criteria
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
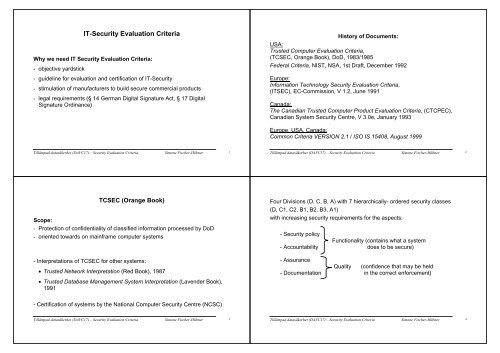
<strong>IT</strong>-<strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong><br />
Why we need <strong>IT</strong> <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong>:<br />
- objective yardstick<br />
- guideline for evaluation and certification of <strong>IT</strong>-<strong>Security</strong><br />
- stimulation of manufacturers to build secure commercial products<br />
- legal requirements (§ 14 German Digital Signature Act, § 17 Digital<br />
Signature Ordinance)<br />
History of Documents:<br />
USA:<br />
Trusted Computer <strong>Evaluation</strong> <strong>Criteria</strong>,<br />
(TCSEC, Orange Book), DoD, 1983/1985<br />
Federal <strong>Criteria</strong>, NIST, NSA, 1st Draft, December 1992<br />
Europe:<br />
Information Technology <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong>,<br />
(<strong>IT</strong>SEC), EC-Commission, V 1.2, June 1991<br />
Canada:<br />
The Canadian Trusted Computer Product <strong>Evaluation</strong> <strong>Criteria</strong>, (CTCPEC),<br />
Canadian System <strong>Security</strong> Centre, V 3.0e, January 1993<br />
Europe, USA, Canada:<br />
Common <strong>Criteria</strong> VERSION 2.1 / ISO IS 15408, August 1999<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 1<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 2<br />
TCSEC (Orange Book)<br />
Scope:<br />
- Protection of confidentiality of classified information processed by DoD<br />
- oriented towards on mainframe computer systems<br />
- Interpretations of TCSEC for other systems:<br />
• Trusted Network Interpretation (Red Book), 1987<br />
• Trusted Database Management System Interpretation (Lavender Book),<br />
1991<br />
Four Divisions (D, C, B, A) with 7 hierarchically- ordered security classes<br />
(D, C1, C2, B1, B2, B3, A1)<br />
with increasing security requirements for the aspects:<br />
- <strong>Security</strong> policy<br />
Functionality (contains what a system<br />
- Accountability does to be secure)<br />
- Assurance<br />
Quality (confidence that may be held<br />
- Documentation in the correct enforcement)<br />
- Certification of systems by the National Computer <strong>Security</strong> Centre (NCSC)<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 3<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 4
Summary of TCSEC- <strong>Security</strong> Classes:<br />
Division C: Discretionary Protection:<br />
Division D/ Class D: Minimal Protection:<br />
- unrated, no security characteristics required<br />
Class C1: Discretionary <strong>Security</strong> Protection:<br />
- for cooperating users processing at the same level of security<br />
- discretionary access controls (DAC): users can protect their own data and<br />
keep other users from accidentally reading or destroying their data<br />
- identification and authentication<br />
- penetration testing<br />
-<br />
Example: MVS/RACF<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 5<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 6<br />
C2: Controlled Access Protection:<br />
Features of C1 +:<br />
- more finely grained DAC:<br />
protection must be implementable at the degree of a single user<br />
- auditing<br />
- object reuse<br />
Examples: VAX VMS, MVS/ACF, Windows NT<br />
Division B: Mandatory Protection<br />
Class B1: Labelled <strong>Security</strong> Protection:<br />
Features of C2 +:<br />
- informal statement of security model<br />
- security labelling<br />
- mandatory access control (MAC) policy of the Bell LaPadula model<br />
- thorough analysis and testing of design documentation,<br />
source code, object code,<br />
- removal of security related flaws<br />
Examples: Trusted Solaris CMW 1.1, Trusted Oracle 7, Unix System V/MLS<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 7<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 8
Class B2: Structured Protection:<br />
Features of B1 +:<br />
- formal security model<br />
- descriptive top-level specification (DTLS)<br />
- DAC and MAC enforcement shall be applied to all subjects and objects (also<br />
devices)<br />
- covert channel analysis<br />
- TCB must be structured into protection critical and non-protection critical<br />
elements (TCB: security-relevant portions of a system)<br />
- authentication mechanisms are strengthened<br />
- more thorough testing and code review<br />
- system is “relatively resistant to penetration”<br />
- separate operator and administrator functions<br />
-<br />
Example: Honeywell Multics<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 9<br />
Class B3: <strong>Security</strong> Domains:<br />
Features of B2 +:<br />
- TCB satisfies the reference monitor concept<br />
- TCB is structured to exclude code not essential to security policy<br />
enforcement<br />
- auditing mechanisms signal security-related events<br />
- system recovery procedures<br />
- the system is highly resistant to penetration<br />
- convincing argument shall be given that DTLS is consistent with the model<br />
- system is “highly resistant to penetration”<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 10<br />
Division A: Verified Protection<br />
Class A1: Verified Design:<br />
Systems in A1 are functionally equivalent to those in B3,<br />
but Class A1 requires a formally verified system design<br />
Formal Model<br />
Formal Top-Level<br />
Specification<br />
Implementation<br />
demonstration using formal or informal techniques<br />
consistency informally shown<br />
<strong>IT</strong>SEC<br />
Harmonisation and extension of existing national criteria:<br />
- UK Systems <strong>Security</strong> Confidence Levels, CESG 1989<br />
- UK DTI Commercial Computer <strong>Security</strong> Centre<br />
<strong>Evaluation</strong> Manual/ Functionality Manual 1989<br />
- German <strong>IT</strong>-<strong>Security</strong> <strong>Criteria</strong>, ZSI (now BSI) 1989<br />
- French "Blue-White-Red Book", SCSSI 1989<br />
Aim:<br />
- compatible basis for certification by national certification bodies<br />
- mutual recognition of evaluation results<br />
Example: Honeywell Scomp<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 11<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 12
Main differences to TCSEC:<br />
- <strong>Security</strong> in <strong>IT</strong>SEC is defined as:<br />
• Confidentiality<br />
• Integrity<br />
• Availability<br />
- <strong>IT</strong>SEC separates/decouples functionality and quality/assurance<br />
requirements<br />
- <strong>IT</strong>SEC is aimed at the evaluation of both products and systems (Target of<br />
<strong>Evaluation</strong> - TOE)<br />
Product: hardware/software package that can be incorporated into<br />
a variety of systems<br />
System: specific <strong>IT</strong> installation with a particular purpose and known<br />
operational environment<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 13<br />
Functionality:<br />
Sponsors of evaluation define security functionality either by<br />
a.) predefined example functionality classes (Annex A):<br />
F-C1<br />
F-C2<br />
F-B1<br />
F-B2<br />
F-B3<br />
F-IN:<br />
F-AV:<br />
F-DI:<br />
F-DC:<br />
F-DX:<br />
hierarchically ordered confidentiality classes,<br />
correspond closely to the functionality<br />
requirements of TCSEC classes C1 to B3<br />
Integrity of Data/ Programs<br />
System Availability<br />
Integrity of Data during Data Exchange<br />
Confidentiality of Data during Data Exchange<br />
Confidentiality and Integrity of information to be exchanged in networks<br />
(possible combinations of functionality classes: one or none of F-C1, F-C2, F-B1, F-B2,<br />
F-B3 and a subset of {F-IN, F-AV, F-DI, F-DC, F-DX})<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 14<br />
b.) Specifying individual functionality claims<br />
It is recommended to use the following generic headings:<br />
- Identification & Authentication<br />
- Access Control<br />
- Accountability<br />
- Object Reuse<br />
- Audit<br />
- Accuracy<br />
- Reliability of Service<br />
- Data Exchange<br />
Quality/Assurance:<br />
Confidence in the<br />
- correctness of the implementation<br />
- effectiveness of the security functions and mechanisms<br />
Correctness:<br />
7 (hierarchically ordered) evaluation levels are defined representing ascending<br />
levels of the confidence in the correctness of a TOE:<br />
E0 E1 E2 E3 E4 E5 E6<br />
no confidence highest confidence<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 15<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 16
Effectiveness:<br />
- assesses suitability of the functionality, binding of the functionality, ease of<br />
use<br />
- deals with the strength of the security enforcing mechanism, assesses the<br />
ability to withstand direct attacks<br />
- If an exploitable vulnerability exists: Overall evaluation level = E0<br />
Correspondence between <strong>IT</strong>SEC and TCSEC:<br />
<strong>IT</strong>SEC: TCSEC:<br />
EO D<br />
F-C1, E1 C1<br />
F-C2, E2 C2<br />
F-B1, E3 B1<br />
F-B2, E4 B2<br />
F-B3, E5 B3<br />
F-B3, E6 A1<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 17<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 18<br />
Common <strong>Criteria</strong> (CC):<br />
http://csrc.nist.gov/cc/<br />
Objectives:<br />
- Harmonised criteria widely useful within the international community<br />
- World-wide mutual recognition of evaluation results<br />
- International standard (ISO IS 15408)<br />
CC Structure:<br />
Part 1: Introduction and General Model<br />
Part 2: <strong>Security</strong> Functional Requirements<br />
Part 3: <strong>Security</strong> Assurance Requirements<br />
CC Project Sponsoring Organisations:<br />
National <strong>Security</strong> agencies of<br />
- Canada<br />
- Germany<br />
- France<br />
- The Netherlands<br />
- UK<br />
- USA (NSA, NIST)<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 19<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 20
Organisation and Construction of <strong>Security</strong> Requirements:<br />
Classb Family k Component Packages<br />
Component<br />
…. Protection Profile<br />
Component Possible<br />
Input sources<br />
for PP<br />
Classa Familiy j Component<br />
Package:<br />
Reusable set of either functional or assurance components (e.g, EALs )<br />
<strong>Security</strong> Target (ST):<br />
Set of security requirements used as a basis for evaluation of an identified<br />
TOE<br />
Family i Component<br />
Component<br />
…,<br />
Component <strong>Security</strong> Target<br />
Possible<br />
Component Optional extended input sources<br />
…… (non-CC) <strong>Security</strong> for ST<br />
Component Requirements<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 21<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 22<br />
Protection Profile (PP):<br />
Implementation-independent, reusable set of security-requirements for a<br />
category of TOEs that meet specific consumer needs<br />
Example PPs:<br />
- Commercial security profile<br />
- Profiles to replicated TCSEC C2 and B1 requirements<br />
- A role based access control (RBAC) profile<br />
- Smart card profiles<br />
- Firewall profiles<br />
CC registry system for approved PPs<br />
Functional <strong>Security</strong> Requirements (Part 2):<br />
Classes of <strong>Security</strong> Functional Requirements:<br />
• FAU (<strong>Security</strong> Audit)<br />
• FCO (Communication/Non-Repudiation)<br />
• FCS (Cryptographic Support)<br />
• FDP (User Data Protection)<br />
• FIA (Identification and Authentication)<br />
• FMT (<strong>Security</strong> Management)<br />
• FPR (Privacy)<br />
• FPT (Protection of the TOE <strong>Security</strong> Functions)<br />
• FRU (Resource Utilisation)<br />
• FTA (TOE Access)<br />
• FTP (Trusted path/channels).<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 23<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 24
Example: Class-Family-Component Hierarchy:<br />
Class Family Components<br />
Identification and Authentication Authentication Failure<br />
Authentication Failures Handling<br />
FIA FIA_AFL FIA_AFL.1<br />
……<br />
User Authentication Timing of Authentication<br />
FIA_UAU FIA_UAU.1<br />
…..<br />
Re-Authenticating<br />
FIA_UAU.6<br />
Protected Authentication Feedback<br />
FIA_UAU.7<br />
Assurance Requirements (Part 3):<br />
Classes of assurance components (covering the correctness and<br />
effectiveness:<br />
• ACM (Configuration Management)<br />
• ADO (Delivery and Operation)<br />
• ADV (Development)<br />
• AGD (Guidance Documentation)<br />
• ALC (Life-Cycle Support)<br />
• ATE (Tests)<br />
• AVA (Vulnerability Assessment)<br />
User Identification Timing of Identification<br />
FIA_UID FIA_UID.1<br />
……<br />
….. ……. ……<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 25<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 26<br />
Useful combinations of assurance components are combined into seven<br />
<strong>Evaluation</strong> Assurance Levels (EALs):<br />
EAL1 – functionally tested (new)<br />
EAL2 – structurally tested (like C1 – E1)<br />
EAL3 – methodically tested and checked (like C2 – E2)<br />
EAL4 – methodically designed, tested, and reviewed (like B1 – E3)<br />
EAL5 – semiformally designed and tested (like B2 – E4)<br />
EAL6 – semiformally verified design and tested (like B3 – E5)<br />
EAL7 – formally verified design and tested (like A1 – E6)<br />
Shortcomings<br />
• Costs of evaluation (10% - 40%) of developing costs<br />
• Time delay until an evaluation is completed<br />
• Cost of re-evaluating new versions of an evaluated product<br />
• Certificates only apply to a particular version and a particular configuration of<br />
a product<br />
• <strong>Criteria</strong> have been biased on protecting system owners and operators, no<br />
satisfactory protection of usees<br />
• CC are too voluminous and complex<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 27<br />
Tillämpad datasäkerhet (DAVC17) – <strong>Security</strong> <strong>Evaluation</strong> <strong>Criteria</strong> Simone Fischer-Hübner 28