Government Security News
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
(ISC)² announces U.S. <strong>Government</strong> Information <strong>Security</strong><br />
Leadership Award winners<br />
(ISC)2 has recognized leaders in advancing<br />
the government’s cyber security<br />
mission with its annual U.S.<br />
<strong>Government</strong> Information <strong>Security</strong><br />
Leadership Awards (GISLA).<br />
At the May 14 event, the<br />
nonprofit organization of certified<br />
information and software security<br />
professionals announced individual<br />
and team winners in seven<br />
categories during a gathering of<br />
government information security<br />
executives at the GISLA Gala in<br />
Washington, D.C.<br />
These top leaders are<br />
working to mature the government’s<br />
cyber world, encourage<br />
others in professionalism and<br />
training, streamline operations<br />
and share ways to fight emerging<br />
threats. The honorees represent<br />
the best in the industry,<br />
across all levels within the U.S.<br />
government community, according<br />
to Dan Waddell, CISSP,<br />
CAP, PMP, (ISC)² director of<br />
U.S. <strong>Government</strong> Affairs.<br />
“Competition is tough every<br />
year, but this year seemed<br />
especially challenging,” Waddell<br />
said. “The finalists’ scores were<br />
often separated by a very thin<br />
margin, which really speaks to<br />
their commitment to excellence and<br />
dedication to advancing the security<br />
posture of government.”<br />
The (ISC)²’s 2015 Global Information<br />
<strong>Security</strong> Workforce<br />
Study shows the gap between the<br />
need of qualified information security<br />
professionals and the supply is<br />
negatively impacting government<br />
security readiness and existing<br />
workers’ morale. “This year’s GISLA<br />
recipients are those who have persisted—and<br />
prevailed—in the midst<br />
of significant obstacles in the areas<br />
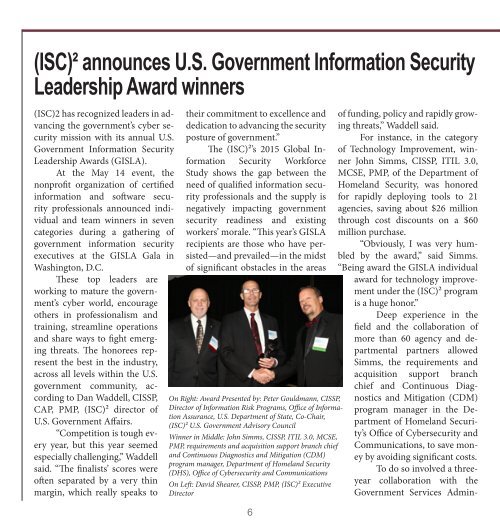
On Right: Award Presented by: Peter Gouldmann, CISSP,<br />
Director of Information Risk Programs, Office of Information<br />
Assurance, U.S. Department of State, Co-Chair,<br />
(ISC)² U.S. <strong>Government</strong> Advisory Council<br />
Winner in Middle: John Simms, CISSP, ITIL 3.0, MCSE,<br />
PMP, requirements and acquisition support branch chief<br />
and Continuous Diagnostics and Mitigation (CDM)<br />
program manager, Department of Homeland <strong>Security</strong><br />
(DHS), Office of Cybersecurity and Communications<br />
On Left: David Shearer, CISSP, PMP, (ISC)² Executive<br />
Director<br />
6<br />
istration and others. “It really took<br />
a monumental effort to plan, coordinate,<br />
and orchestrate activities<br />
necessary to get to where we are today<br />
and to see that we, indeed, are<br />
achieving financial cost savings,”<br />
said Simms, who has worked in information<br />
technology for 25 years<br />
and in information security for 15<br />
years.<br />
His innovative approach to<br />
rapidly deploy nearly $60M of CDM<br />
tools to 21 agencies was a productonly<br />
delivery order focused on agencies<br />
that could immediately benefit<br />
from additional tools. While saving<br />
taxpayer dollars and protecting<br />
federal networks, he also ensured<br />
that the agencies acquired critical<br />
capabilities to meet emerging, government-wide<br />
cyber threats. “We’ve<br />
received substantial savings, most in<br />
the form of savings on product delivery<br />
orders.”<br />
Going forward, Simms anticipated<br />
the tools now in place will be<br />
used for continuous monitoring and<br />
will be leveraged as the preferred<br />
approach for federal civilian government.<br />
Within each group, tasks<br />
and processes required to solicit solutions<br />
have been streamlined for<br />
each agency. The impact, he said, is<br />
expected to continue, with followup<br />
orders also including a high percentage<br />
of product discounts based<br />
of funding, policy and rapidly growing<br />
threats,” Waddell said.<br />
For instance, in the category<br />
of Technology Improvement, winner<br />
John Simms, CISSP, ITIL 3.0,<br />
MCSE, PMP, of the Department of<br />
Homeland <strong>Security</strong>, was honored<br />
for rapidly deploying tools to 21<br />
agencies, saving about $26 million<br />
through cost discounts on a $60<br />
million purchase.<br />
“Obviously, I was very humbled<br />
by the award,” said Simms.<br />
“Being award the GISLA individual<br />
award for technology improvement<br />
under the (ISC)² program<br />
is a huge honor.”<br />
Deep experience in the<br />
field and the collaboration of<br />
more than 60 agency and departmental<br />
partners allowed<br />
Simms, the requirements and<br />
acquisition support branch<br />
chief and Continuous Diagnostics<br />
and Mitigation (CDM)<br />
program manager in the Department<br />
of Homeland <strong>Security</strong>’s<br />
Office of Cybersecurity and<br />
Communications, to save money<br />
by avoiding significant costs.<br />
To do so involved a threeyear<br />
collaboration with the<br />
upon IT schedule 70 list prices.<br />
security and course development is<br />
odology enhancements to any gov-<br />
<strong>Government</strong> Services Admin- More on page 8<br />
Other 2015 GISLA recipients are:<br />
Community Awareness: 81<br />
Cyber Protection Team (CPT)<br />
As the U.S. Marine’s first National<br />
Cyber Protection Team, 81<br />
Cyber Protection Team quickly<br />
became the most sophisticated incident<br />
response element in the Department<br />
of Defense (DoD). 81<br />
CPT created innovative approaches<br />
to building an advanced defensive<br />
cyberspace capability in training,<br />
technology employment, methodologies<br />
and mission planning.<br />
Using both proprietary and commercial<br />
technology, the team built<br />
one of the most modern and effective<br />
defensive cyber programs for<br />
the DoD, including a CPT toolkit<br />
that has become the standard for all<br />
CPTs in the department<br />
81 CPT produced experts<br />
capable of conducting incident response,<br />
vulnerability analysis and<br />
mitigation, and procedure/meth-<br />
ernment organization. As a result,<br />
7<br />
81 CPT has shaped the way that the<br />
U.S. Cyber Command implements<br />
CPTs and has set the standard for<br />
other DoD teams.<br />
Workforce Improvement: Michael<br />
C. Redman, CISSP, CISM, CCNA,<br />
CompTIA Network+, CompTIA<br />
<strong>Security</strong>+, CompTIA A+, Comp-<br />
TIA Linux+, MCP, MCSA, senior<br />
information assurance manager<br />
and chief, Policy and Accreditation<br />
Branch<br />
Redman identified a training<br />
gap for DoD cybersecurity professionals<br />
and delivered in-house<br />
training courses to more than 300<br />
personnel using training materials<br />
that he created. With the knowledge<br />
transfer to students at their level of<br />
learning, 93 percent achieved a pass<br />
rate on certifications such as CISSP,<br />
CISM, <strong>Security</strong>+ and Linux+. His<br />
holistic approach to information