JP 3-26, Counterterrorism - Defense Technical Information Center
JP 3-26, Counterterrorism - Defense Technical Information Center
JP 3-26, Counterterrorism - Defense Technical Information Center
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
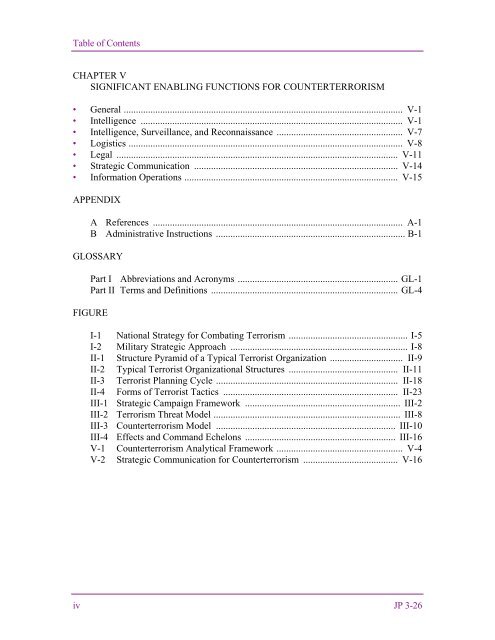
Table of ContentsCHAPTER VSIGNIFICANT ENABLING FUNCTIONS FOR COUNTERTERRORISM• General ................................................................................................................... V-1• Intelligence ............................................................................................................ V-1• Intelligence, Surveillance, and Reconnaissance .................................................... V-7• Logistics ................................................................................................................. V-8• Legal .................................................................................................................... V-11• Strategic Communication .................................................................................... V-14• <strong>Information</strong> Operations ........................................................................................ V-15APPENDIXA References ....................................................................................................... A-1B Administrative Instructions .............................................................................. B-1GLOSSARYPart I Abbreviations and Acronyms .................................................................. GL-1Part II Terms and Definitions ............................................................................. GL-4FIGUREI-1 National Strategy for Combating Terrorism ................................................. I-5I-2 Military Strategic Approach ......................................................................... I-8II-1 Structure Pyramid of a Typical Terrorist Organization .............................. II-9II-2 Typical Terrorist Organizational Structures ............................................. II-11II-3 Terrorist Planning Cycle ........................................................................... II-18II-4 Forms of Terrorist Tactics ........................................................................ II-23III-1 Strategic Campaign Framework ................................................................ III-2III-2 Terrorism Threat Model ............................................................................. III-8III-3 <strong>Counterterrorism</strong> Model .......................................................................... III-10III-4 Effects and Command Echelons .............................................................. III-16V-1 <strong>Counterterrorism</strong> Analytical Framework .................................................... V-4V-2 Strategic Communication for <strong>Counterterrorism</strong> ....................................... V-16iv <strong>JP</strong> 3-<strong>26</strong>