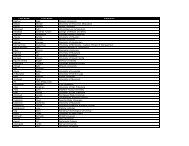
Chen et al./Introduction: Business Intelligence ResearchPapers in this Special IssueThe idea for this special issue began in May 2009, whenDetmar Straub, the Edi<strong>to</strong>r-in-Chief of MIS Quarterly, solicitedsuggestions for special issues <strong>from</strong> the edi<strong>to</strong>rial boardmembers. We submitted the special issue proposal on BusinessIntelligence Research in August 2009, with the call-forpapersapproved <strong>and</strong> distributed at the 30 th Annual InternationalConference on Information Systems (ICIS) in Decemberof that year. Submissions <strong>to</strong> this special issue needed <strong>to</strong>relate <strong>to</strong> MIS Quarterly’s mission with strong managerial,organizational, <strong>and</strong> societal relevance <strong>and</strong> <strong>impact</strong>. In addition<strong>to</strong> the Design Science approach (Hevner et al. 2004; March &S<strong>to</strong>rey 2008), rigorous <strong>and</strong> relevant BI-related research usingmanagement science (modeling, optimization), informationeconomics, <strong>and</strong> organizational <strong>and</strong> behavioral methodologies(case studies, surveys) was also welcomed. A <strong>to</strong>tal of 62manuscripts was received by Oc<strong>to</strong>ber 2010. In the following20 months, six of the manuscripts went through three or fourreview rounds <strong>and</strong> were then accepted for this issue.The six papers address various aspects of the BI&A researchframework presented in this introduction paper (see Table 7).All six papers are based on BI&A 1.0, with three also basedon BI&A 2.0. The first three papers by Chau <strong>and</strong> Xu, Park etal., <strong>and</strong> Lau et al. focus on BI&A 2.0 with applications on e-commerce <strong>and</strong> market <strong>intelligence</strong> using text, web, <strong>and</strong> network<strong>analytics</strong>. In the next two papers, both Hu et al. <strong>and</strong>Abbasi et al. work in the category of BI&A 1.0 with a focuson security, but Hu et al. use network <strong>analytics</strong> whereasAbbasi et al. emphasize security analysis <strong>and</strong> <strong>data</strong> <strong>analytics</strong>.Finally, Sahoo et al. also work in BI&A 1.0, with direct application<strong>to</strong> e-commerce <strong>and</strong> market <strong>intelligence</strong> using web <strong>and</strong><strong>data</strong> <strong>analytics</strong>.In “Business Intelligence in Blogs: Underst<strong>and</strong>ing ConsumerInteractions <strong>and</strong> Communities,” Michael Chau <strong>and</strong> JenniferXu recognized the potential “gold mine” of blog content for<strong>business</strong> <strong>intelligence</strong> <strong>and</strong> developed a framework forgathering <strong>business</strong> <strong>intelligence</strong> by au<strong>to</strong>matically collecting<strong>and</strong> analyzing blog content <strong>and</strong> bloggers’ interaction networks.A system developed using this framework wasapplied <strong>to</strong> two case studies, which revealed novel patterns inblogger interactions <strong>and</strong> communities.Sung-Hyuk Park, Soon-Young Huh, Wonseok Oh, <strong>and</strong> SangPil Han in their paper, “A Social Network-Based InferenceModel for Validating Cus<strong>to</strong>mer Profile Data,” argue that <strong>business</strong><strong>intelligence</strong> systems are of limited value when they dealwith inaccurate <strong>and</strong> unreliable <strong>data</strong>. The authors proposed asocial network-driven inference framework <strong>to</strong> determine theaccuracy <strong>and</strong> reliability of self-reported cus<strong>to</strong>mer profiles.The framework utilizes the individuals’ social circles <strong>and</strong>communication patterns within their circles. To construct thespecific inference <strong>and</strong> validation model, a combination ofmethods was used, including query processing, statisticalinference, social network analysis, <strong>and</strong> user profiling. Theauthors analyzed over 20 million actual mobile call transactions<strong>and</strong> their proposed social network-based inferencemodel consistently outperformed the alternative approaches.In “Web 2.0 Environmental Scanning <strong>and</strong> Adaptive DecisionSupport for Business Mergers <strong>and</strong> Acquisitions,” RaymondLau, Stephen Liao, K. F. Wong, <strong>and</strong> Dickson Chiu analyzedcompany mergers <strong>and</strong> acquisitions (M&A). Online environmentalscanning with Web 2.0 provides <strong>to</strong>p executives withopportunities <strong>to</strong> tap in<strong>to</strong> collective web <strong>intelligence</strong> <strong>to</strong> developbetter insights about the socio-cultural <strong>and</strong> political-economicfac<strong>to</strong>rs that cross-border M&As face. Grounded on Porter’sfive forces model, this research designed a due diligencescorecard model that leverages collective web <strong>intelligence</strong> <strong>to</strong>enhance M&A decision making. The authors also developedan adaptive <strong>business</strong> <strong>intelligence</strong> (BI) 2.0 system, which theyapplied <strong>to</strong> Chinese companies’ cross-border M&A activities.In their paper, “Network-Based Modeling <strong>and</strong> Analysis ofSystemic Risk in Banking Systems,” Daning Hu, J. LeonZhao, Zhimin Hua, <strong>and</strong> Michael Wong analyzed systemic riskin banking systems by treating banks as a network linked withfinancial relationships, leading <strong>to</strong> a network approach <strong>to</strong> riskmanagement (NARM). NARM analyzes systemic risk attributed<strong>to</strong> each individual bank via simulation based on realworld<strong>data</strong> <strong>from</strong> the Federal Deposit Insurance Corporation.NARM offers a new means for predicting contagious bankfailures <strong>and</strong> determining capital injection priorities at theindividual bank level in the wake of financial crisis. A simulationstudy showed that, under significant market shocks, theinterbank payment links became more influential than thecorrelated bank portfolio links in determining an individualbank’s survival.In their paper, “MetaFraud: A Meta-Learning Framework forDetecting Financial Fraud,” Ahmed Abbasi, Conan Albrecht,Anthony Vance, <strong>and</strong> James Hansen employed a designscience approach <strong>to</strong> develop MetaFraud, a meta-learningframework for enhanced financial fraud detection. A seriesof experiments was conducted on thous<strong>and</strong>s of legitimate <strong>and</strong>fraudulent firms <strong>to</strong> demonstrate the effectiveness of the frameworkover existing benchmark methods. The research resultshave implications for compliance officers, inves<strong>to</strong>rs, auditfirms, <strong>and</strong> regula<strong>to</strong>rs.The paper by Nachiketa Sahoo, Param Vir Singh, <strong>and</strong> TridasMukhopadhyay, “A Hidden Markov Model for CollaborativeFiltering,” reports on the analysis of making personalizedrecommendations when user preferences are changing. The20 MIS Quarterly Vol. 36No. 4/December 2012
Chen et al./Introduction: Business Intelligence ResearchTable 7. Summary of Special Issue Papers Within the BI&A Research FrameworkAuthors <strong>and</strong> Titles Evolutions Applications Data Analytics/ Research ImpactsChau <strong>and</strong> Xu, “BusinessIntelligence in Blogs: Underst<strong>and</strong>ingConsumer Interactions<strong>and</strong> Communities”Park et al., “A SocialNetwork-Based InferenceModel for ValidatingCus<strong>to</strong>mer Profile Data”Lau et al., “Web 2.0Environmental Scanning <strong>and</strong>Adaptive Decision Supportfor Business Mergers <strong>and</strong>Acquisitions”Hu et al., “Network-BasedModeling <strong>and</strong> Analysis ofSystemic Risk in BankingSystems”Abbasi et al., “MetaFraud: AMeta-Learning Frameworkfor Detecting FinancialFraud”Sahoo et al., “A HiddenMarkov Model for CollaborativeFiltering”BI&A 2.0 onsocial media& network<strong>analytics</strong>BI&A 1.0 &2.0 on socialnetworkanalysis <strong>and</strong>statisticalanalysisBI&A 1.0 <strong>and</strong>2.0 onscorecards<strong>and</strong> web<strong>analytics</strong>BI&A 1.0 onstatisticalanalysisBI&A 1.0 on<strong>data</strong> mining<strong>and</strong> metalearningBI&A 1.0 onstatisticalanalysisMarket <strong>intelligence</strong>on consumers <strong>and</strong>communitiesMarket <strong>intelligence</strong>in predicting cus<strong>to</strong>mers’profilesMarket <strong>intelligence</strong>on environmentalscanningSystemic riskanalysis <strong>and</strong>management inbanking systemsFraud detectionRecommender systemswith changinguser preferencesUser-generatedcontent extracted<strong>from</strong> blogsSelf-reported userprofiles <strong>and</strong> mobilecall recordsBusiness informationextracted <strong>from</strong>Internet <strong>and</strong>proprietary financialinformationU.S. banking informationextracted <strong>from</strong>FDIC <strong>and</strong> FederalReserve WireNetworkFinancial ratios, <strong>and</strong>organizational <strong>and</strong>industrial-level contextfeaturesBlog reading <strong>data</strong>,Netflix prize <strong>data</strong> set,<strong>and</strong> Last.fm <strong>data</strong>• Text <strong>and</strong> network<strong>analytics</strong>• Community detection• Network visualization• Network <strong>analytics</strong>• Anomaly detection• Predictive <strong>analytics</strong>• Text <strong>and</strong> web <strong>analytics</strong>• Sentiment <strong>and</strong> affectanalysis• Relation mining• Network <strong>and</strong> <strong>data</strong><strong>analytics</strong>• Descriptive <strong>and</strong>predictive modeling• Discrete event simulation• Data <strong>analytics</strong>• Classification &generalization• Adaptive learning• Data <strong>and</strong> web <strong>analytics</strong>• Statistical dynamic model• Collaborative filteringIncreased sales<strong>and</strong> cus<strong>to</strong>mersatisfactionPersonalizedrecommendation<strong>and</strong> increasedcus<strong>to</strong>mersatisfactionStrategic decisionmaking inmergers <strong>and</strong>acquisitionsMoni<strong>to</strong>ring <strong>and</strong>mitigating ofcontagious bankfailuresFinancial frauddetectionPersonalizedrecommendationsauthors proposed a hidden Markov model based on collaborativefiltering <strong>to</strong> predict user preferences <strong>and</strong> make the mostappropriate personalized recommendations for the predictedpreference. The authors employed real world <strong>data</strong> sets <strong>and</strong>simulations <strong>to</strong> show that, when user preferences are changing,there is an advantage <strong>to</strong> using the proposed algorithm overexisting ones.Summary <strong>and</strong> ConclusionsThrough BI&A 1.0 initiatives, <strong>business</strong>es <strong>and</strong> organizations<strong>from</strong> all sec<strong>to</strong>rs began <strong>to</strong> gain critical insights <strong>from</strong> thestructured <strong>data</strong> collected through various enterprise systems<strong>and</strong> analyzed by commercial relational <strong>data</strong>base managementsystems. Over the past several years, web <strong>intelligence</strong>, web<strong>analytics</strong>, web 2.0, <strong>and</strong> the ability <strong>to</strong> mine unstructured usergeneratedcontents have ushered in a new <strong>and</strong> exciting era ofBI&A 2.0 research, leading <strong>to</strong> unprecedented <strong>intelligence</strong> onconsumer opinion, cus<strong>to</strong>mer needs, <strong>and</strong> recognizing new<strong>business</strong> opportunities. Now, in this era of Big Data, evenwhile BI&A 2.0 is still maturing, we find ourselves poised atthe brink of BI&A 3.0, with all the attendant uncertainty thatnew <strong>and</strong> potentially revolutionary technologies bring.This MIS Quarterly Special Issue on Business IntelligenceResearch is intended <strong>to</strong> serve, in part, as a platform <strong>and</strong>conversation guide for examining how the IS discipline canbetter serve the needs of <strong>business</strong> decision makers in light ofmaturing <strong>and</strong> emerging BI&A technologies, ubiqui<strong>to</strong>us BigData, <strong>and</strong> the predicted shortages of <strong>data</strong>-savvy managers <strong>and</strong>of <strong>business</strong> professionals with deep analytical skills. Howcan academic IS programs continue <strong>to</strong> meet the needs of theirtraditional students, while also reaching the working ITprofessional in need of new analytical skills? A new visionfor IS may be needed <strong>to</strong> address this <strong>and</strong> other questions.By highlighting several applications such as e-commerce,market <strong>intelligence</strong>, e-government, healthcare, <strong>and</strong> security,<strong>and</strong> by mapping important facets of the current BI&Aknowledge l<strong>and</strong>scape, we hope <strong>to</strong> contribute <strong>to</strong> future sourcesof knowledge <strong>and</strong> <strong>to</strong> augment current discussions on theimportance of (relevant) academic research.MIS Quarterly Vol. 36 No. 4/December 2012 21