Chen et al./Introduction: Business Intelligence Researchsecurity, domestic counter-terrorism, protecting critical infrastructure(including cyberspace), defending against catastrophicterrorism, <strong>and</strong> emergency preparedness <strong>and</strong> response.Facing the critical missions of international security <strong>and</strong>various <strong>data</strong> <strong>and</strong> technical challenges, the need <strong>to</strong> develop thescience of “security informatics” was recognized, with itsmain objective being thedevelopment of advanced information technologies,systems, algorithms, <strong>and</strong> <strong>data</strong>bases for securityrelatedapplications, through an integrated technological,organizational, <strong>and</strong> policy-based approach(Chen 2006, p. 7).BI&A has much <strong>to</strong> contribute <strong>to</strong> the emerging field of securityinformatics.Security issues are a major concern for most organizations.According <strong>to</strong> the research firm International Data Corporation,large companies are expected <strong>to</strong> spend $32.8 billion incomputer security in 2012, <strong>and</strong> small- <strong>and</strong> medium-sizecompanies will spend more on security than on other ITpurchases over the next three years (Perlroth <strong>and</strong> Rusli 2012).In academia, several security-related disciplines such ascomputer security, computational criminology, <strong>and</strong> terrorisminformatics are also flourishing (Brantingham 2011; Chen etal. 2008).Intelligence, security, <strong>and</strong> public safety agencies are gatheringlarge amounts of <strong>data</strong> <strong>from</strong> multiple sources, <strong>from</strong> criminalrecords of terrorism incidents, <strong>and</strong> <strong>from</strong> cyber security threats<strong>to</strong> multilingual open-source <strong>intelligence</strong>. Companies of differentsizes are facing the daunting task of defending againstcybersecurity threats <strong>and</strong> protecting their intellectual assets<strong>and</strong> infrastructure. Processing <strong>and</strong> analyzing security-related<strong>data</strong>, however, is increasingly difficult. A significant challengein security IT research is the information s<strong>to</strong>vepipe <strong>and</strong>overload resulting <strong>from</strong> diverse <strong>data</strong> sources, multiple <strong>data</strong>formats, <strong>and</strong> large <strong>data</strong> volumes. Current research on technologiesfor cybersecurity, counter-terrorism, <strong>and</strong> crimefightingapplications lacks a consistent framework foraddressing these <strong>data</strong> challenges. Selected BI&A technologiessuch as criminal association rule mining <strong>and</strong> clustering,criminal network analysis, spatial-temporal analysis <strong>and</strong>visualization, multilingual text <strong>analytics</strong>, sentiment <strong>and</strong> affectanalysis, <strong>and</strong> cyber attacks analysis <strong>and</strong> attribution should beconsidered for security informatics research.The University of Arizona’s COPLINK <strong>and</strong> Dark Webresearch programs offer significant examples of crime <strong>data</strong>mining <strong>and</strong> terrorism informatics within the IS community(Chen 2006, 2012). The COPLINK information sharing <strong>and</strong>crime <strong>data</strong> mining system, initially developed with funding<strong>from</strong> NSF <strong>and</strong> the Department of Justice, is currently in useby more than 4,500 police agencies in the United States <strong>and</strong>by 25 NATO countries, <strong>and</strong> was acquired by IBM in 2011.The Dark Web research, funded by NSF <strong>and</strong> the Departmen<strong>to</strong>f Defense (DOD), has generated one of the largest knownacademic terrorism research <strong>data</strong>bases (about 20 terabytes ofterrorist web sites <strong>and</strong> social media content) <strong>and</strong> generatedadvanced multilingual social media <strong>analytics</strong> techniques.Recognizing the challenges presented by the volume <strong>and</strong>complexity of defense-related <strong>big</strong> <strong>data</strong>, the U.S. DefenseAdvanced Research Project Agency (DARPA) within DODinitiated the XDATA program in 2012 <strong>to</strong> help develop computationaltechniques <strong>and</strong> software <strong>to</strong>ols for processing <strong>and</strong>analyzing the vast amount of mission-oriented information fordefense activities. XDATA aims <strong>to</strong> address the need forscalable algorithms for processing <strong>and</strong> visualization ofimperfect <strong>and</strong> incomplete <strong>data</strong>. The program engages appliedmathematics, computer science, <strong>and</strong> <strong>data</strong> visualization communities<strong>to</strong> develop <strong>big</strong> <strong>data</strong> <strong>analytics</strong> <strong>and</strong> usability solutionsfor warfighters. 7 BI&A researchers could contribute significantlyin this area.Table 2 summarizes these promising BI&A applications, <strong>data</strong>characteristics, <strong>analytics</strong> techniques, <strong>and</strong> potential <strong>impact</strong>s.BI&A Research Framework:Foundational Technologies <strong>and</strong>Emerging Research in AnalyticsThe opportunities with the abovementioned emerging <strong>and</strong>high-<strong>impact</strong> applications have generated a great deal ofexcitement within both the BI&A industry <strong>and</strong> the researchcommunity. Whereas industry focuses on scalable <strong>and</strong> integratedsystems <strong>and</strong> implementations for applications in differen<strong>to</strong>rganizations, the academic community needs <strong>to</strong>continue <strong>to</strong> advance the key technologies in <strong>analytics</strong>.Emerging <strong>analytics</strong> research opportunities can be classifiedin<strong>to</strong> five critical technical areas—(<strong>big</strong>) <strong>data</strong> <strong>analytics</strong>, text<strong>analytics</strong>, web <strong>analytics</strong>, network <strong>analytics</strong>, <strong>and</strong> mobile<strong>analytics</strong>—all of which can contribute <strong>to</strong> <strong>to</strong> BI&A 1.0, 2.0,<strong>and</strong> 3.0. The classification of these five <strong>to</strong>pic areas is intended7 “DARPA Calls for Advances in ‘Big Data” <strong>to</strong> Help the Warfighter,” March29, 2012 (http://www.darpa.mil/NewsEvents/Releases/2012/03/29.aspx;accessed August 5, 2012).8 MIS Quarterly Vol. 36No. 4/December 2012
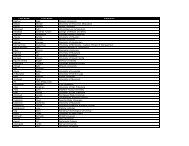
Chen et al./Introduction: Business Intelligence ResearchTable 2. BI&A Applications: From Big Data <strong>to</strong> Big ImpactApplicationsE-Commerce <strong>and</strong>Market Intelligence• Recommendersystems• Social mediamoni<strong>to</strong>ring <strong>and</strong>analysis• Crowd-sourcingsystems• Social <strong>and</strong> virtualgamesE-Government <strong>and</strong>Politics 2.0• Ubiqui<strong>to</strong>usgovernment services• Equal access <strong>and</strong>public services• Citizen engagement<strong>and</strong> participation• Political campaign<strong>and</strong> e-pollingScience &Technology• S&T innovation• Hypothesis testing• KnowledgediscoverySmart Health <strong>and</strong>Wellbeing• Human <strong>and</strong> plantgenomics• Healthcaredecision support• Patient communityanalysisSecurity <strong>and</strong>Public Safety• Crime analysis• Computationalcriminology• Terrorisminformatics• Open-source<strong>intelligence</strong>• Cyber securityDataAnalytics• Search <strong>and</strong> userlogs• Cus<strong>to</strong>mer transactionrecords• Cus<strong>to</strong>mergeneratedcontentCharacteristics:Structured webbased,usergeneratedcontent,rich network information,unstructuredinformal cus<strong>to</strong>meropinions• Association rulemining• Database segmentation<strong>and</strong>clustering• Anomaly detection• Graph mining• Social networkanalysis• Text <strong>and</strong> web<strong>analytics</strong>• Sentiment <strong>and</strong>affect analysis• Government information<strong>and</strong> services• Rules <strong>and</strong> regulations• Citizen feedback <strong>and</strong>commentsCharacteristics:Fragmented informationsources <strong>and</strong>legacy systems, richtextual content,unstructured informalcitizen conversations• Information integration• Content <strong>and</strong> text<strong>analytics</strong>• Government informationsemantic services<strong>and</strong> on<strong>to</strong>logies• Social media moni<strong>to</strong>ring<strong>and</strong> analysis• Social networkanalysis• Sentiment <strong>and</strong> affectanalysis• S&T instruments<strong>and</strong> systemgenerated<strong>data</strong>• Sensor <strong>and</strong>network contentCharacteristics:High-throughputinstrument-based<strong>data</strong> collection, finegrainedmultiplemodality<strong>and</strong> largescalerecords, S&Tspecific <strong>data</strong> formats• S&T baseddomain-specificmathematical <strong>and</strong>analytical models• Genomics <strong>and</strong>sequence <strong>data</strong>• Electronic healthrecords (EHR)• Health <strong>and</strong> patientsocial mediaCharacteristics:Disparate but highlylinked content,person-specificcontent, HIPAA, IRB<strong>and</strong> ethics issues• Genomics <strong>and</strong>sequence analysis<strong>and</strong> visualization• EHR associationmining <strong>and</strong>clustering• Health socialmedia moni<strong>to</strong>ring<strong>and</strong> analysis• Health text<strong>analytics</strong>• Health on<strong>to</strong>logies• Patient networkanalysis• Adverse drugside-effectanalysis• Privacy-preserving<strong>data</strong> mining• Criminal records• Crime maps• Criminal networks• News <strong>and</strong> webcontents• Terrorism incident<strong>data</strong>bases• Viruses, cyberattacks, <strong>and</strong>botnetsCharacteristics:Personal identityinformation, incomplete<strong>and</strong> deceptivecontent, rich group<strong>and</strong> network information,multilingualcontent• Criminalassociation rulemining <strong>and</strong>clustering• Criminal networkanalysis• Spatial-temporalanalysis <strong>and</strong>visualization• Multilingual text<strong>analytics</strong>• Sentiment <strong>and</strong>affect analysis• Cyber attacksanalysis <strong>and</strong>attributionImpactsLong-tail marketing,targeted <strong>and</strong> personalizedrecommendation,increased sale<strong>and</strong> cus<strong>to</strong>mersatisfactionTransforming governments,empoweringcitizens, improvingtransparency, participation,<strong>and</strong> equalityS&T advances,scientific <strong>impact</strong>Improved healthcarequality, improvedlong-term care,patient empowermentImproved publicsafety <strong>and</strong> securityMIS Quarterly Vol. 36 No. 4/December 2012 9