Using Data Analysis to Detect Fraud - IIA Dallas Chapter
Using Data Analysis to Detect Fraud - IIA Dallas Chapter
Using Data Analysis to Detect Fraud - IIA Dallas Chapter
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
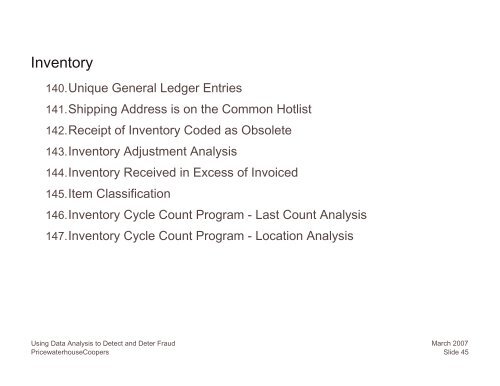
Inven<strong>to</strong>ry140.Unique General Ledger Entries141.Shipping Address is on the Common Hotlist142.Receipt of Inven<strong>to</strong>ry Coded as Obsolete143.Inven<strong>to</strong>ry Adjustment <strong>Analysis</strong>144.Inven<strong>to</strong>ry Received in Excess of Invoiced145.Item Classification146.Inven<strong>to</strong>ry Cycle Count Program - Last Count <strong>Analysis</strong>147.Inven<strong>to</strong>ry Cycle Count Program - Location <strong>Analysis</strong><strong>Using</strong> <strong>Data</strong> <strong>Analysis</strong> <strong>to</strong> <strong>Detect</strong> and Deter <strong>Fraud</strong>PricewaterhouseCoopersMarch 2007Slide 45