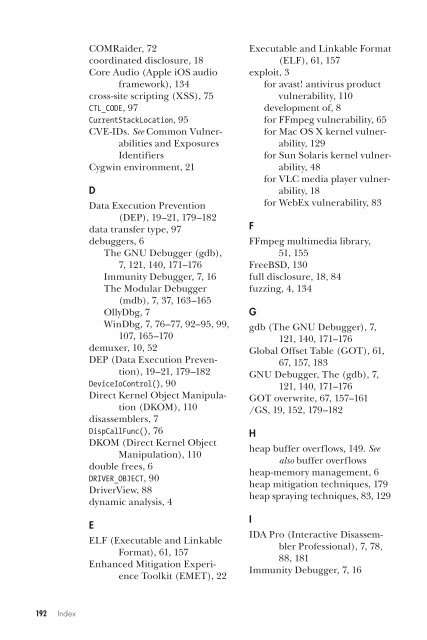
COMRaider, 72coordinated disclosure, 18Core Audio (Apple iOS audioframework), 134cross-site scripting (XSS), 75CTL_CODE, 97CurrentStackLocation, 95CVE-IDs. See Common Vulnerabilitiesand ExposuresIdentifiersCygwin environment, 21DData Execution Prevention(DEP), 19–21, 179–182data transfer type, 97debuggers, 6The GNU Debugger (gdb),7, 121, 140, 171–176Immunity Debugger, 7, 16The Modular Debugger(mdb), 7, 37, 163–165OllyDbg, 7WinDbg, 7, 76–77, 92–95, 99,107, 165–170demuxer, 10, 52DEP (Data Execution Prevention),19–21, 179–182DeviceIoControl(), 90Direct Kernel Object Manipulation(DKOM), 110disassemblers, 7DispCallFunc(), 76DKOM (Direct Kernel ObjectManipulation), 110double frees, 6DRIVER_OBJECT, 90DriverView, 88dynamic analysis, 4EELF (Executable and LinkableFormat), 61, 157Enhanced Mitigation ExperienceToolkit (EMET), 22Executable and Linkable Format(ELF), 61, 157exploit, 3for avast! antivirus productvulnerability, 110development of, 8for FFmpeg vulnerability, 65for Mac OS X kernel vulnerability,129for Sun Solaris kernel vulnerability,48for VLC media player vulnerability,18for WebEx vulnerability, 83FFFmpeg multimedia library,51, 155FreeBSD, 130full disclosure, 18, 84fuzzing, 4, 134Ggdb (The GNU Debugger), 7,121, 140, 171–176Global Offset Table (GOT), 61,67, 157, 183GNU Debugger, The (gdb), 7,121, 140, 171–176GOT overwrite, 67, 157–161/GS, 19, 152, 179–182Hheap buffer overflows, 149. Seealso buffer overflowsheap-memory management, 6heap mitigation techniques, 179heap spraying techniques, 83, 129IIDA Pro (Interactive DisassemblerProfessional), 7, 78,88, 181Immunity Debugger, 7, 16192 Index
input/output controls (IOCTL),26, 88, 113ioctl(), 115instruction alignment, 146instruction pointer, 7, 150Intel, 7, 149Interactive Disassembler Professional(IDA Pro), 7, 78,88, 181Internet Explorer, 71IoCreateDevice(), 88IOCTL (input/output controls),26, 88, 113ioctl(), 115I/O request packet (IRP), 95_IO_STACK_LOCATION, 96iPhone, 133IRP (I/O request packet), 95IRP_MJ_DEVICE_CONTROL, 90Jjmp reg technique, 18, 19Kkernel debugging, 7, 37, 88, 121,167, 173Kernel Debug Kit, 174kernel driver, 87kernel panic, 32, 37–38, 120, 165kernel space, 39, 102KeSetEvent(), 107LLinuxDebian, 157, 183debugging the Mac OS Xkernel with, 121, 173and exploit mitigation techniques,180, 183fuzzing the iPhone with, 134gdb, debugger for, 7Red Hat, 173stack buffer overflowsunder, 151Ubuntu, 56, 63, 151little-endian, 17, 143LookingGlass, 21MMac OS X, 7, 113, 173mdb (The Modular Debugger),7, 37, 163–165mediaserverd, 134memcpy(), 101, 142memory corruption, 6, 140,149, 157memory errors, 6memory leak, 129, 140METHOD_BUFFERED, 99MindshaRE, 76mmap(), 44MobileSafari, 133Modular Debugger, The (mdb),7, 37, 163–165Most Significant Bit (MSB), 156movie header atom, 144movsx, 5MSB (Most Significant Bit), 156Nnon-maskable interrupt(NMI), 122NULL pointer dereference, 6,32, 51, 153–154Oobjdump, 63, 161, 184OS X, 7, 113, 173Pparser, 9PLT (Procedure Linkage Table),158–160privilege escalation, 110, 129Procedure Linkage Table (PLT),158–160program counter, 7, 150Python, 74QQuickTime (File Format Specification),144Index 193
- Page 6 and 7:
A Bug Hunter’s Diary. Copyright
- Page 10 and 11:
Chapter 3: Escape from the WWW Zone
- Page 12 and 13:
B.2 The Windows Debugger (WinDbg) .
- Page 15 and 16:
IntroductionWelcome to A Bug Hunter
- Page 17 and 18:
1Bug HuntingBug hunting is the proc
- Page 19 and 20:
After I’ve found a bug, I want to
- Page 21 and 22:
Table 1-1: Debuggers Used in This B
- Page 23:
2Back to the ’90sSunday, October
- Page 26 and 27:
16361637 /* clear the SEQ table */1
- Page 28 and 29:
If a TiVo file is loaded by VLC, th
- Page 30 and 31:
Get the →vulnerableWindows versio
- Page 32 and 33:
EIP = 41414141 . . . Mission EIP co
- Page 34 and 35:
NoteTo configure Process Explorer t
- Page 36 and 37:
See the following excerpt from the
- Page 38 and 39:
3. Immunity Debugger is a great Win
- Page 40 and 41:
NoteInput/output controls (IOCTLs)
- Page 42 and 43:
msgbb_datapdatabb_rptrdb_basedatabu
- Page 44 and 45:
8180 /*8181 * Null terminate the st
- Page 46 and 47:
26736 /*26737 * SIOC[GS]TUNPARAM ap
- Page 48 and 49:
19165 * are also rejected as they i
- Page 50 and 51:
01 #include 02 #include 03 #include
- Page 52 and 53:
fffffe8000f7e4b0 unix:die+da ()ffff
- Page 54 and 55:
zero pagenot mappedzero pageis mapp
- Page 56 and 57:
gaining full control over EIP/RIP a
- Page 58 and 59:
112 return 1;113 }114115 printf ("O
- Page 60 and 61:
solaris$ isainfo -b64I then compile
- Page 62 and 63:
ip_output+0x10()ip_wput+0x37()putne
- Page 64 and 65:
Notes1. The source code of OpenSola
- Page 66 and 67:
4.1 Vulnerability DiscoveryTo find
- Page 68 and 69:
167 if (current_track + 1 > fourxm-
- Page 71 and 72:
Step 1: Find a Sample 4X Movie File
- Page 73 and 74:
Next, I modified the values of trac
- Page 75 and 76:
Table 4-2: List of the Assembler In
- Page 77 and 78:
63 #elif defined (HAVE_MEMALIGN)64
- Page 79 and 80:
linux$ gdb -q ./ffmpeg_g(gdb) run -
- Page 81 and 82:
(UINT_MAX / sizeof(AudioTrack) - 1)
- Page 83 and 84:
7ebe000-b7ec0000 r--p 0015c000 08:0
- Page 85 and 86:
5Browse and You’re OwnedSunday, A
- Page 87 and 88:
{SWI.ClassId_q.ClassId clsid = new
- Page 89 and 90:
27 except KeyboardInterrupt:28 prin
- Page 91 and 92:
Figure 5-4: Defining a breakpoint a
- Page 93 and 94:
Figure 5-7: User-controlled argumen
- Page 95 and 96:
Next, I tried to retrieve the size
- Page 97 and 98:
05 06 arg = String(232, "A") + Stri
- Page 99:
iDefense VCPnotifiedVulnerability d
- Page 102 and 103:
6.1 Vulnerability DiscoveryI used t
- Page 104 and 105:
Step 3: Check the Device Security S
- Page 106 and 107:
Below, the elements of the MajorFun
- Page 108 and 109:
At address .text:00010748, a pointe
- Page 110 and 111:
[..][..]//// Current stack location
- Page 112 and 113:
The transfer type is specified usin
- Page 114 and 115:
If the requested IOCTL code matches
- Page 116 and 117:
Figure 6-5: Graph view of the vulne
- Page 118 and 119:
.text:00010DBA push 1 ; _DWORD.text
- Page 120 and 121:
99 // .text:00010DEF cmp dword ptr
- Page 122 and 123:
nt!RtlpBreakWithStatusInstruction:8
- Page 124 and 125:
After I gained control over EIP, I
- Page 127 and 128:
7A Bug Older Than 4.4BSDSaturday, M
- Page 129 and 130:
Here are some examples:Source code
- Page 131 and 132:
1094 return (ENXIO);1095 if (t != t
- Page 133 and 134:
4. The assumed address of l_open()
- Page 135 and 136:
osx$ cat /Library/Logs/panic.logSat
- Page 137 and 138:
Back on the Linux host, I started t
- Page 139 and 140:
0x35574c, the value is used to calc
- Page 141 and 142:
48 define search_memloc49 set $max_
- Page 143 and 144:
As the debugger output shows, the E
- Page 145:
ApplenotifiedApple asks formore det
- Page 148 and 149:
I performed the following steps whe
- Page 150 and 151:
I then began fuzzing files of the A
- Page 152 and 153:
Figure 8-1: Playing the unmodifiedA
- Page 154 and 155:
• Line 40 copies the current proc
- Page 156 and 157: As the debugger output shows, media
- Page 158 and 159: The manipulated byte (0xff) that ca
- Page 160 and 161: (gdb) x/12x 0x1301bfc0x1301bfc: 0x0
- Page 162 and 163: ApplenotifiedApple confirmsthe vuln
- Page 164 and 165: Every function of a process that is
- Page 166 and 167: eip 0x43434343 0x43434343eflags 0x1
- Page 168 and 169: The access violation is caused when
- Page 170 and 171: is less than 12. If it is, the stri
- Page 172 and 173: The program in Listing A-4 calls th
- Page 174 and 175: 0x080483f3 : mov DWORD PTR [esp+0x4
- Page 177 and 178: BDebuggingThis appendix contains in
- Page 179 and 180: Information CommandsCommandDescript
- Page 181 and 182: Information CommandsCommandrkbu add
- Page 183 and 184: Figure B-3: Configuration settings
- Page 185 and 186: Figure B-6: Attaching the kernel de
- Page 187 and 188: Other CommandsCommandset disassembl
- Page 189 and 190: linux# pwd/home/tk/gdb-292/srclinux
- Page 191: Notes1. See the Solaris Modular Deb
- Page 194 and 195: The many mitigation techniques coul
- Page 196 and 197: Figure C-1: DEP and ASLR status sho
- Page 198 and 199: 08 p[0] = 0x41414141;09 printf (“
- Page 200 and 201: ConclusionIn case of a buffer overf
- Page 202 and 203: zonecfg:wwwzone> set autoboot=truez
- Page 204 and 205: Notes1. See Rob King, “New Leopar
- Page 208 and 209: Rreadelf, 161RELRO, 67-69, 183-186r
- Page 210: A Bug Hunter’s Diary is set in Ne