IS0/<strong>IEC</strong><strong>18028</strong>-1:2006(E)12 Identify the Information Security RisksAs reflected earlier, the majority of organizations today are dependent on the use of information systems andnetworks to support their business operations. Further, in many cases there is a definite business requirementfor the use of network connections between the information systems at each organization's location, and toother locations both within and outside the organization, including to/from the general public. When aconnection is made to another network, considerable care should be taken to ensure that the connectingorganization is not exposed to additional risks (from potential threats exploiting vulnerabilities). These riskscould, for example, result from the connection itself or from network connections at the other end.Some of these risks may be related to ensuring adherence to relevant legislation and regulation. (Particularattention should be given to privacy and data protection legislation. Several countries have legislation placingcontrols on the collection, processing and transmission of personal data, i.e. data that can be related to aspecific person or persons. Depending on the respective national legislation, such controls may impose dutieson those collecting, processing and disseminating personal information through networks and may evenrestrict the ability to transfer that data to certain other countries, yielding additional important securityconcerns. Less obvious examples of data that may be subject to such legislation are some hardware and IPaddresses.)The types of risk reflected in this clause relate to concerns about unauthorized access to information,unauthorized sending of information, the introduction of malicious code, denial of receipt or origin, denial ofservice connection, and unavailability of information and service. Thus the types of security risk that anorganization might face relate to loss of:— confidentiality of information and code (in networks and in systems connected to networks),— integrity of information and code (in networks and in systems connected to networks),— availability of information and network services (and systems connected to networks),— non-repudiation of network transactions (commitments),— accountability of network transactions,— authenticity of information (as well of course of network users and administrators),— reliability of information and code (in networks and in systems connected to networks),— ability to control unauthorized use and exploitation of network resources, including in the contexts oforganization policy (e.g. selling bandwidth or using bandwidth for own benefits) and responsibilities inrelation to legislation and regulation (e.g. storing child pornography).Not all of the types of security risk will apply to every location, or to every organization. However, the relevanttypes of security risk should be identified so that potential control areas can be identified (and eventuallycontrols selected, designed, implemented and maintained).22 ©<strong>ISO</strong>/<strong>IEC</strong> 2006 - All rights reserved
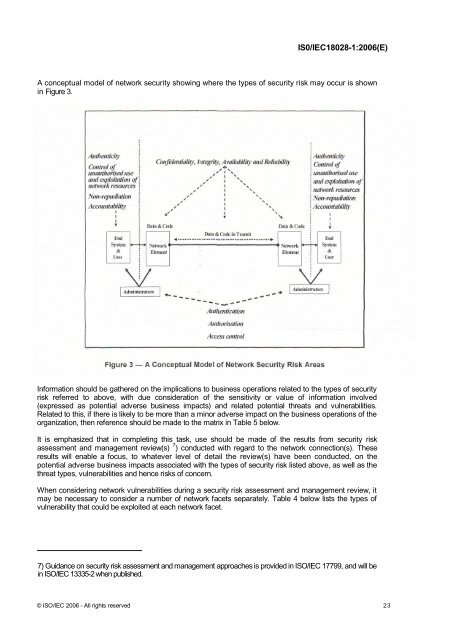
IS0/<strong>IEC</strong><strong>18028</strong>-1:2006(E)A conceptual model of network security showing where the types of security risk may occur is shownin Figure 3.Information should be gathered on the implications to business operations related to the types of securityrisk referred to above, with due consideration of the sensitivity or value of information involved(expressed as potential adverse business impacts) and related potential threats and vulnerabilities.Related to this, if there is likely to be more than a minor adverse impact on the business operations of theorganization, then reference should be made to the matrix in Table 5 below.It is emphasized that in completing this task, use should be made of the results from security riskassessment and management review(s) 7 ) conducted with regard to the network connection(s). Theseresults will enable a focus, to whatever level of detail the review(s) have been conducted, on thepotential adverse business impacts associated with the types of security risk listed above, as well as thethreat types, vulnerabilities and hence risks of concern.When considering network vulnerabilities during a security risk assessment and management review, itmay be necessary to consider a number of network facets separately. Table 4 below lists the types ofvulnerability that could be exploited at each network facet.7) Guidance on security risk assessment and management approaches is provided in <strong>ISO</strong>/<strong>IEC</strong> 17799, and will bein <strong>ISO</strong>/<strong>IEC</strong> 13335-2 when published.© <strong>ISO</strong>/<strong>IEC</strong> 2006 - All rights reserved 23